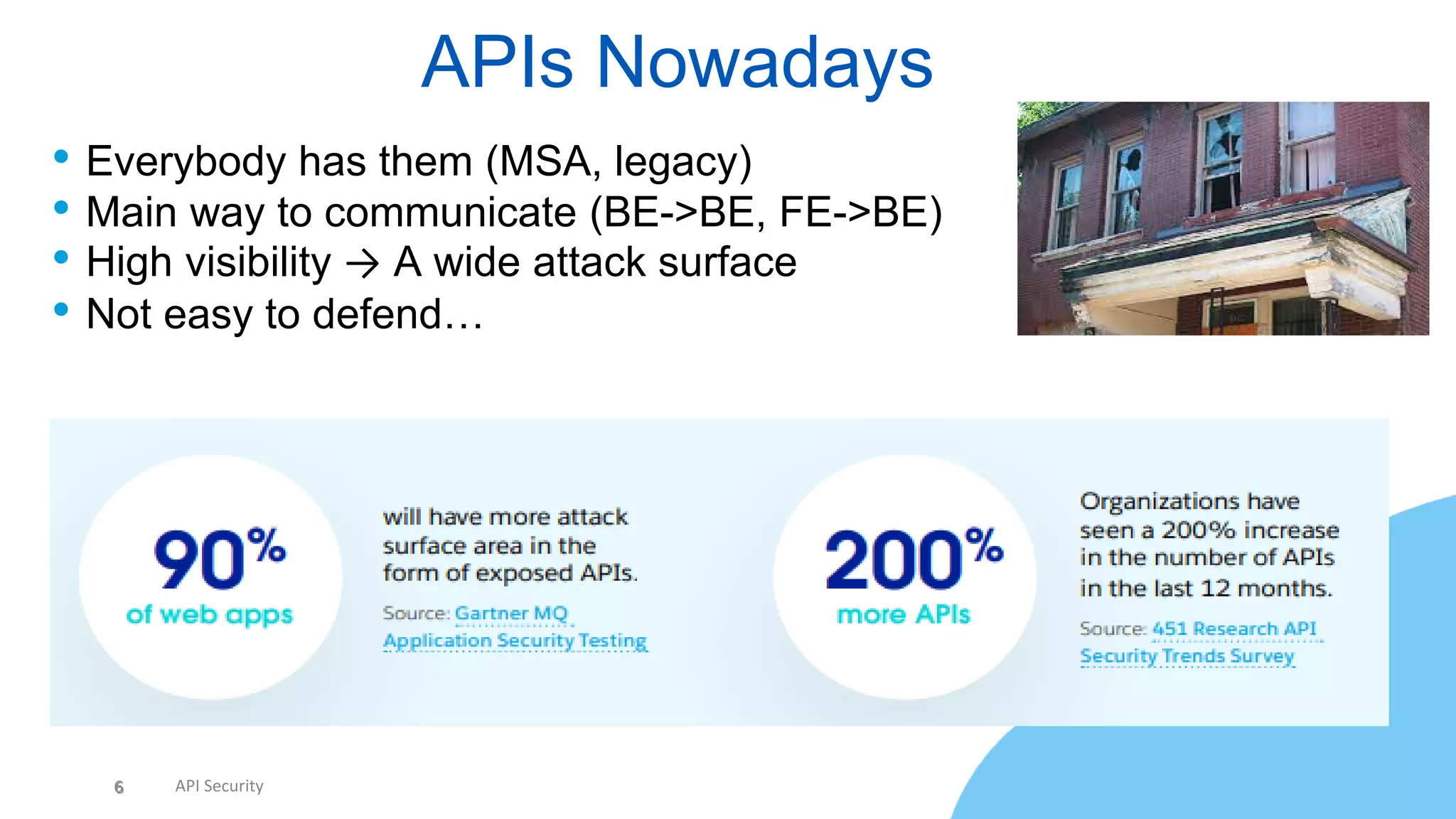
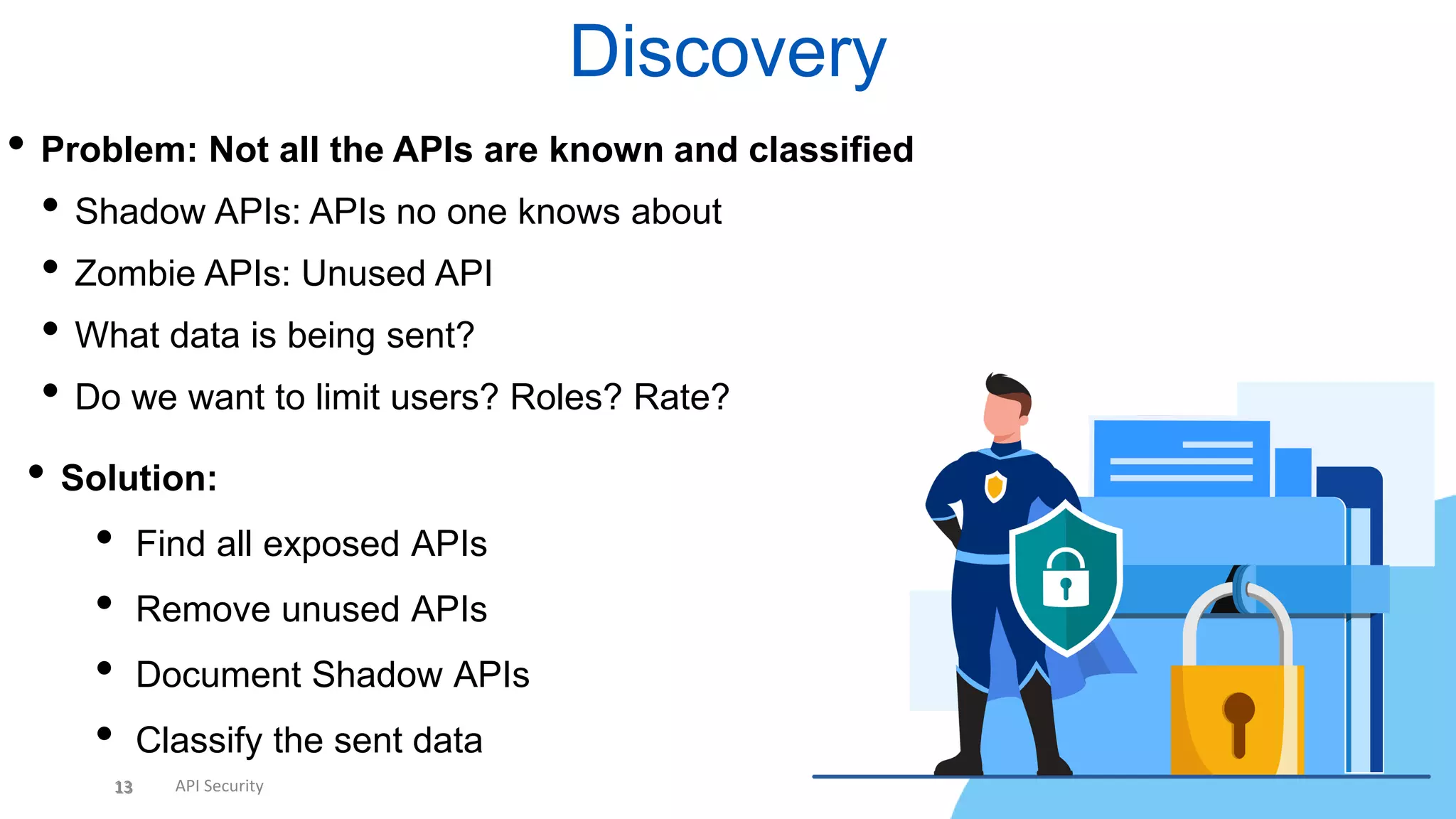
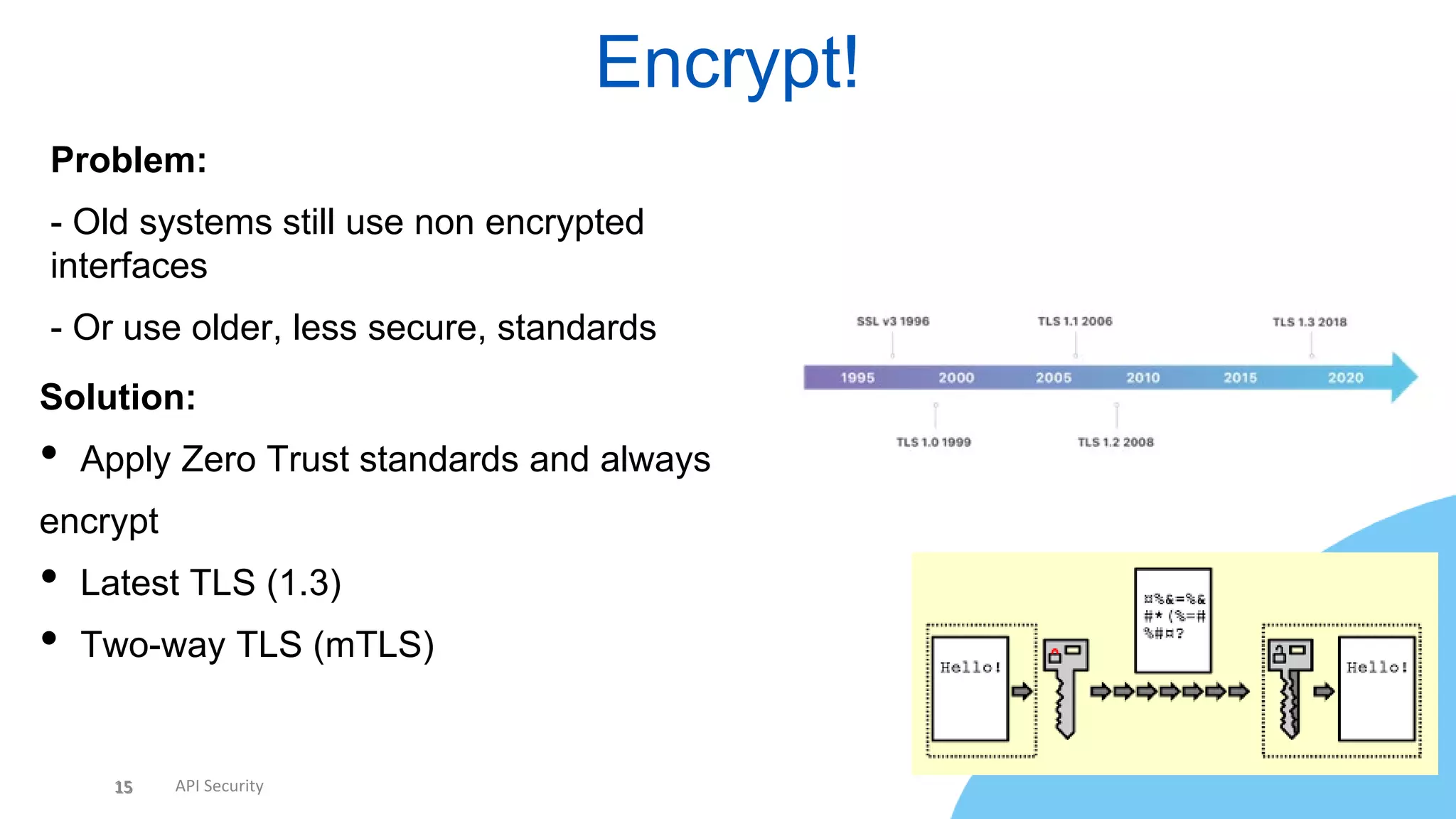
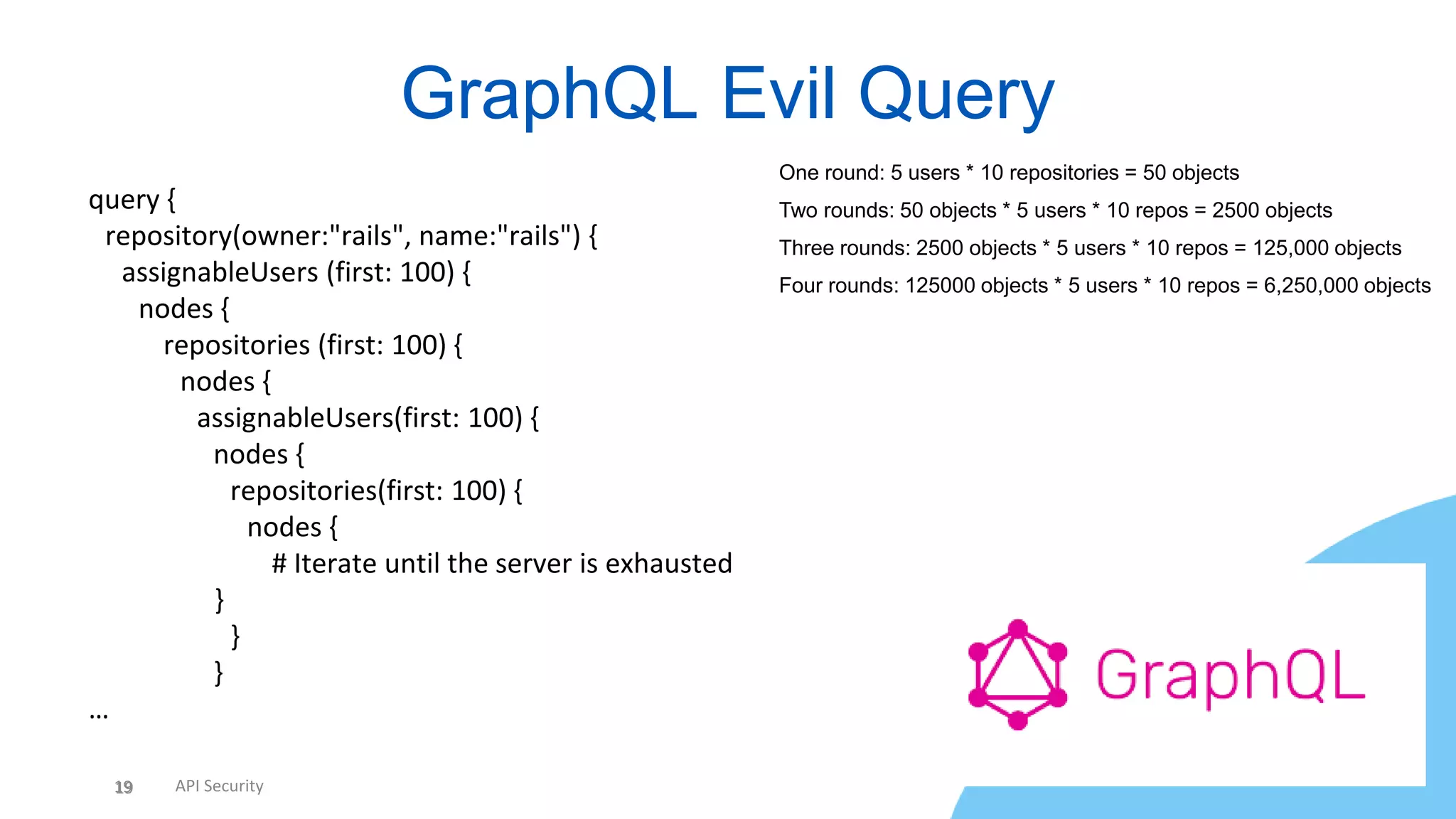
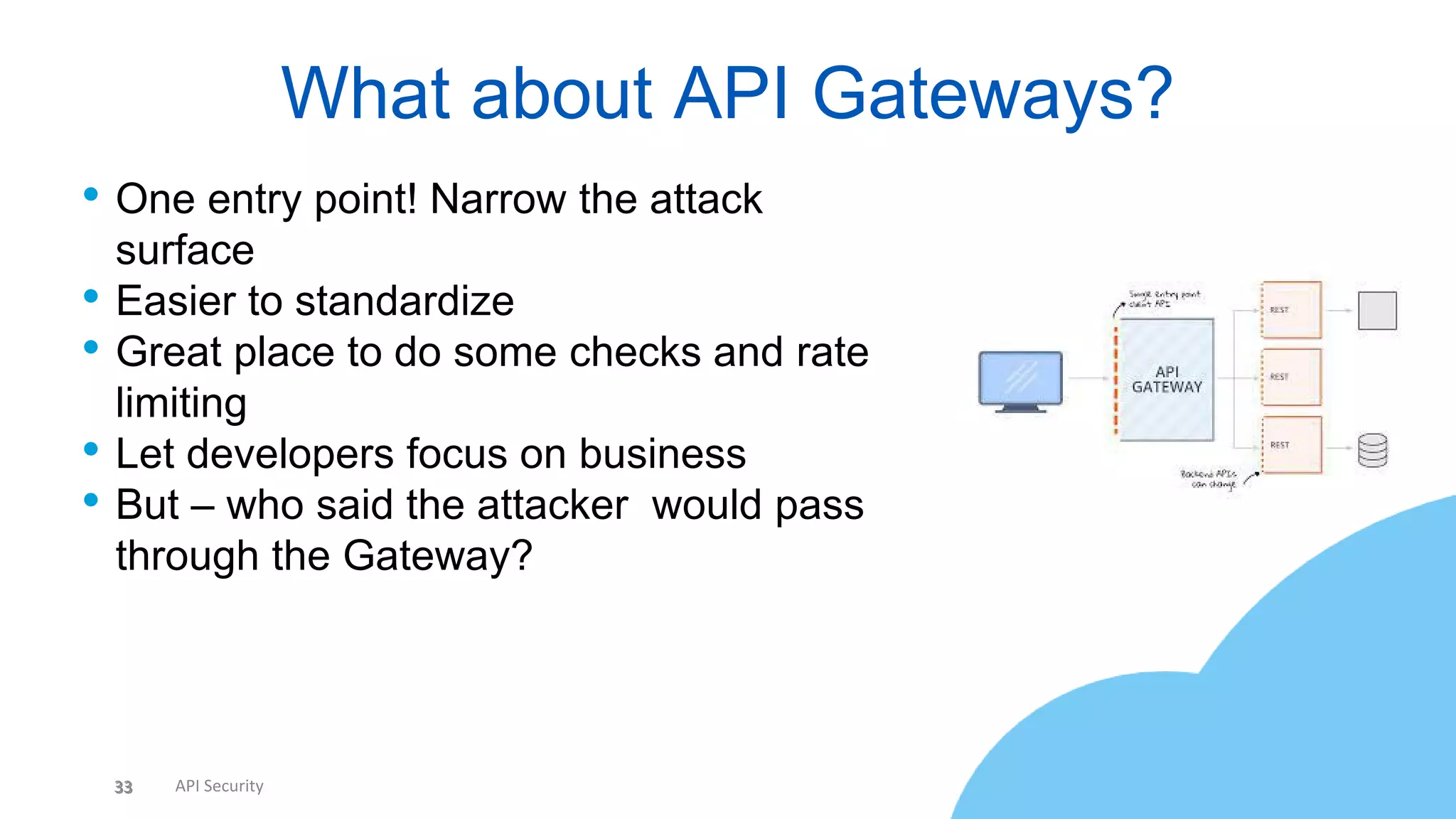
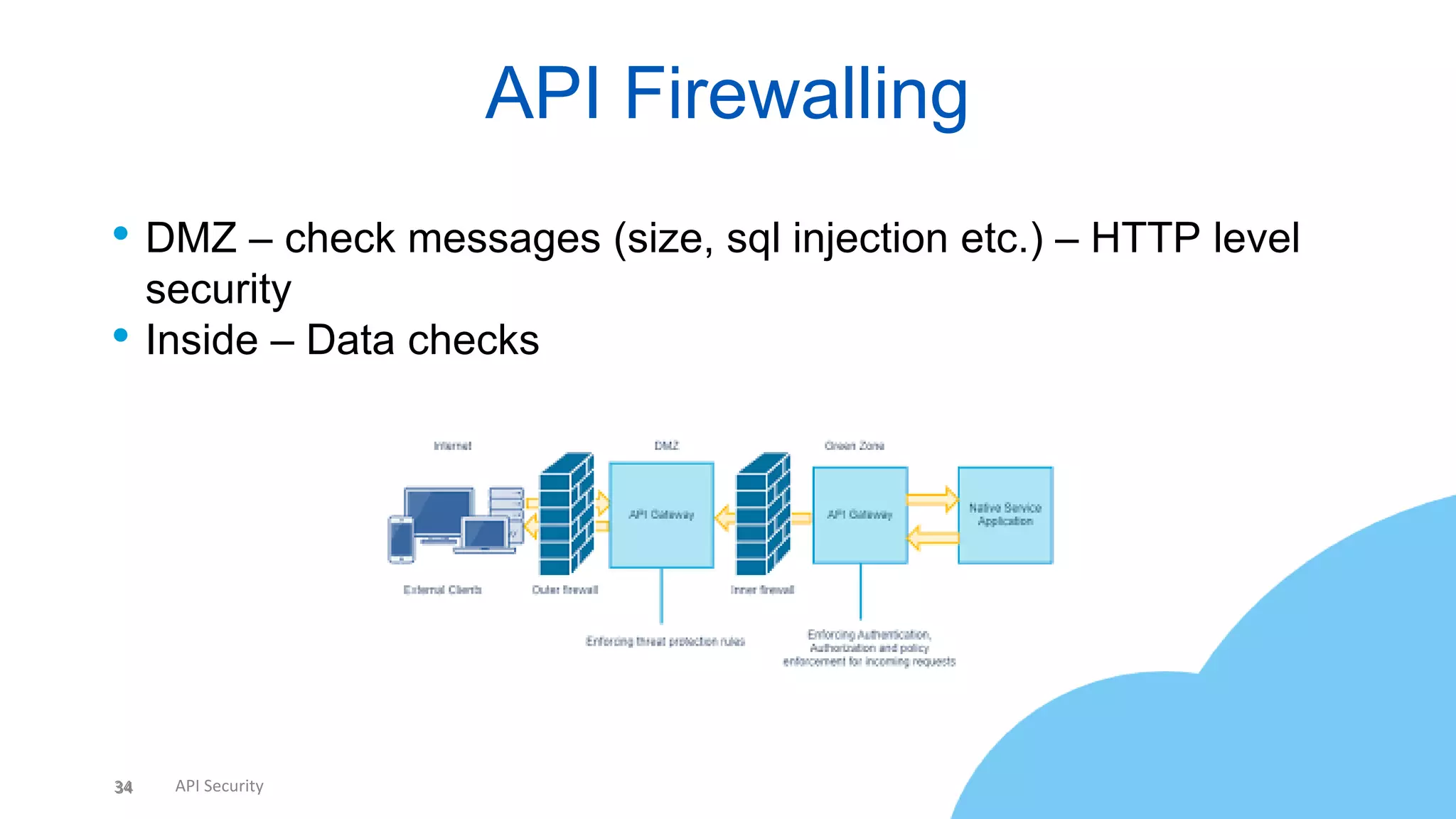
The document discusses API security, highlighting the importance of securing APIs due to their widespread usage and vulnerability to attacks. It covers common security risks, recommended measures for protection, and emphasizes the need for standardization, encryption, and continuous monitoring. Key takeaways include narrowing the attack surface, implementing proper defenses, and staying updated on threats.