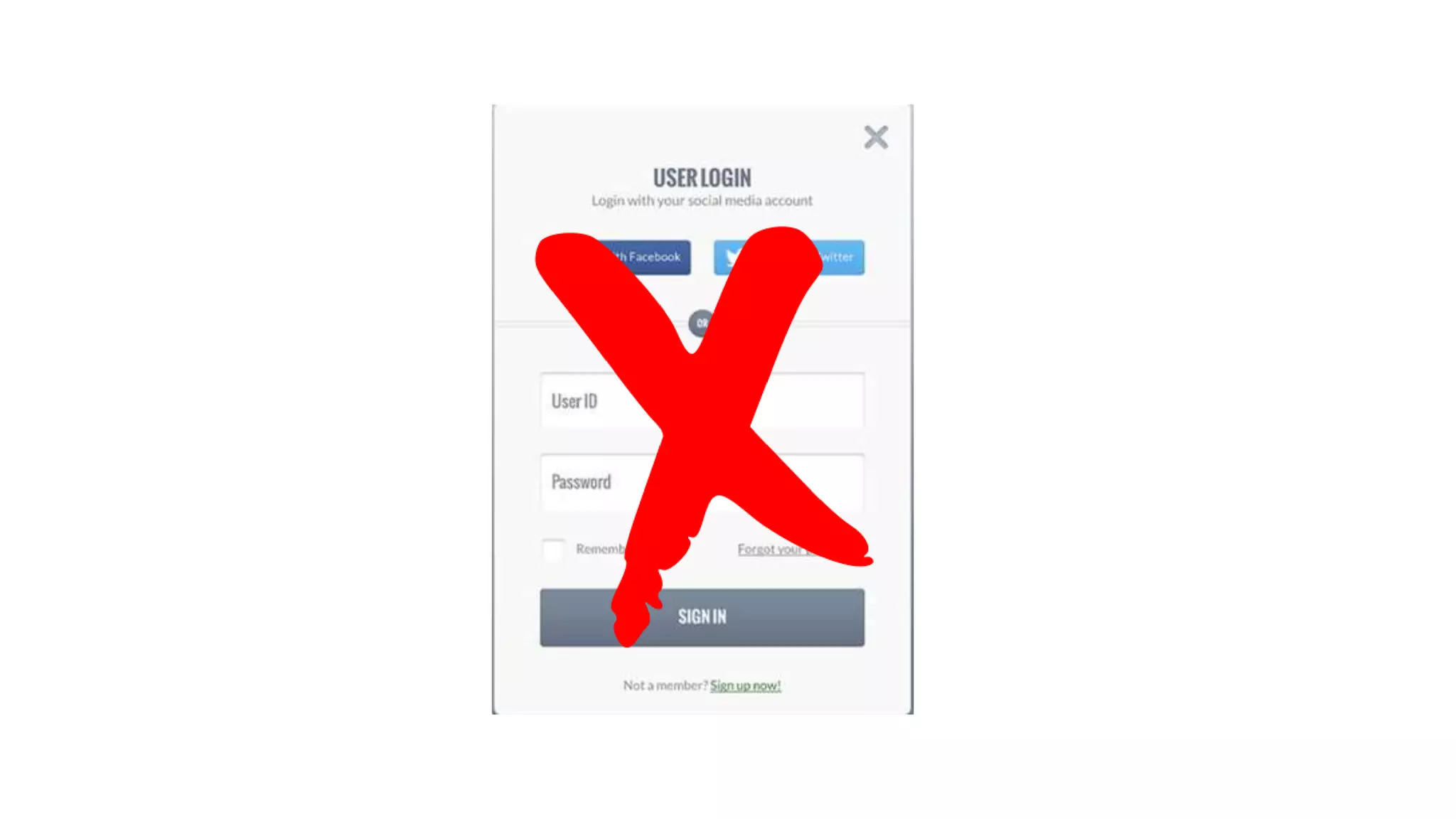
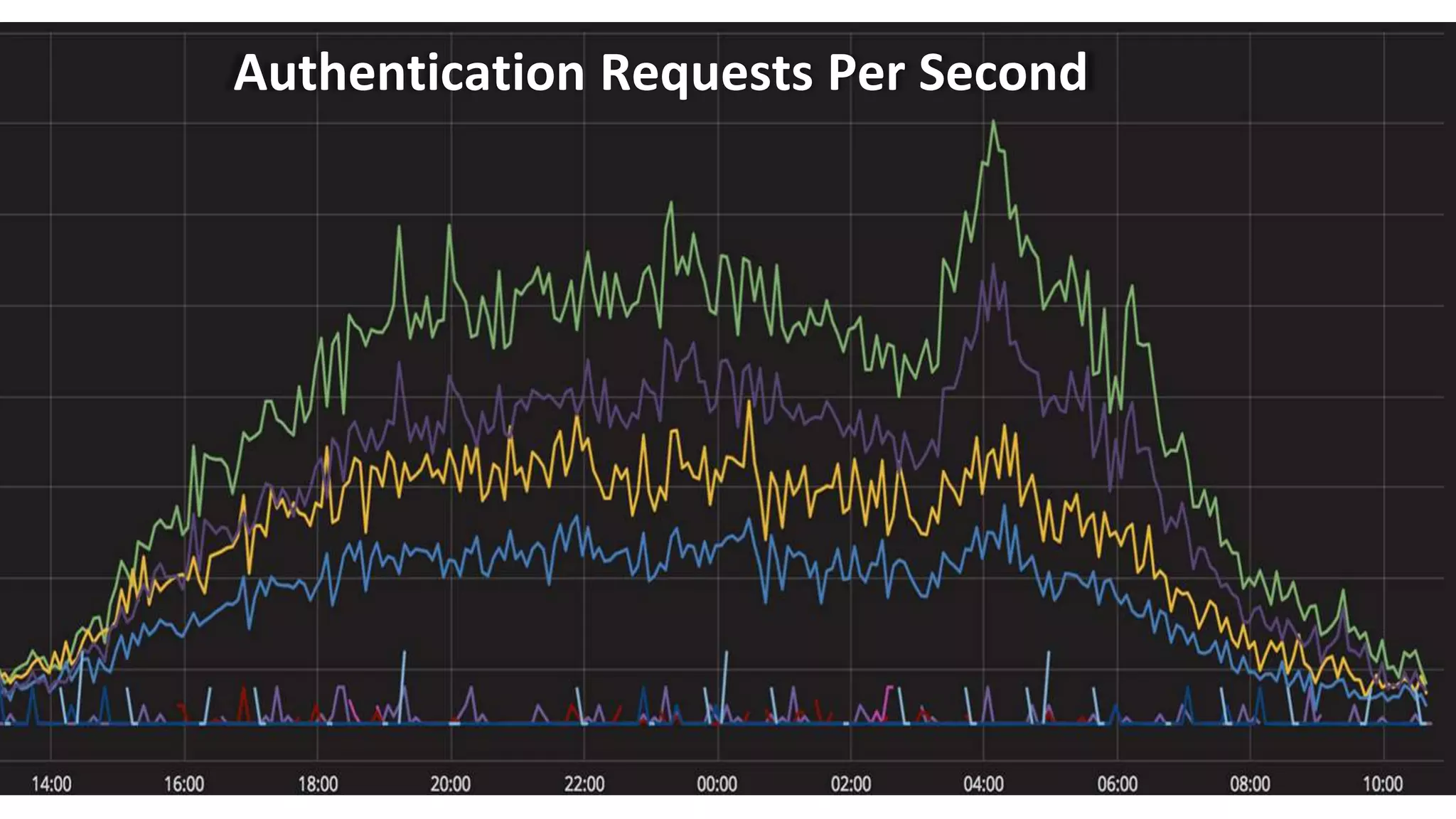
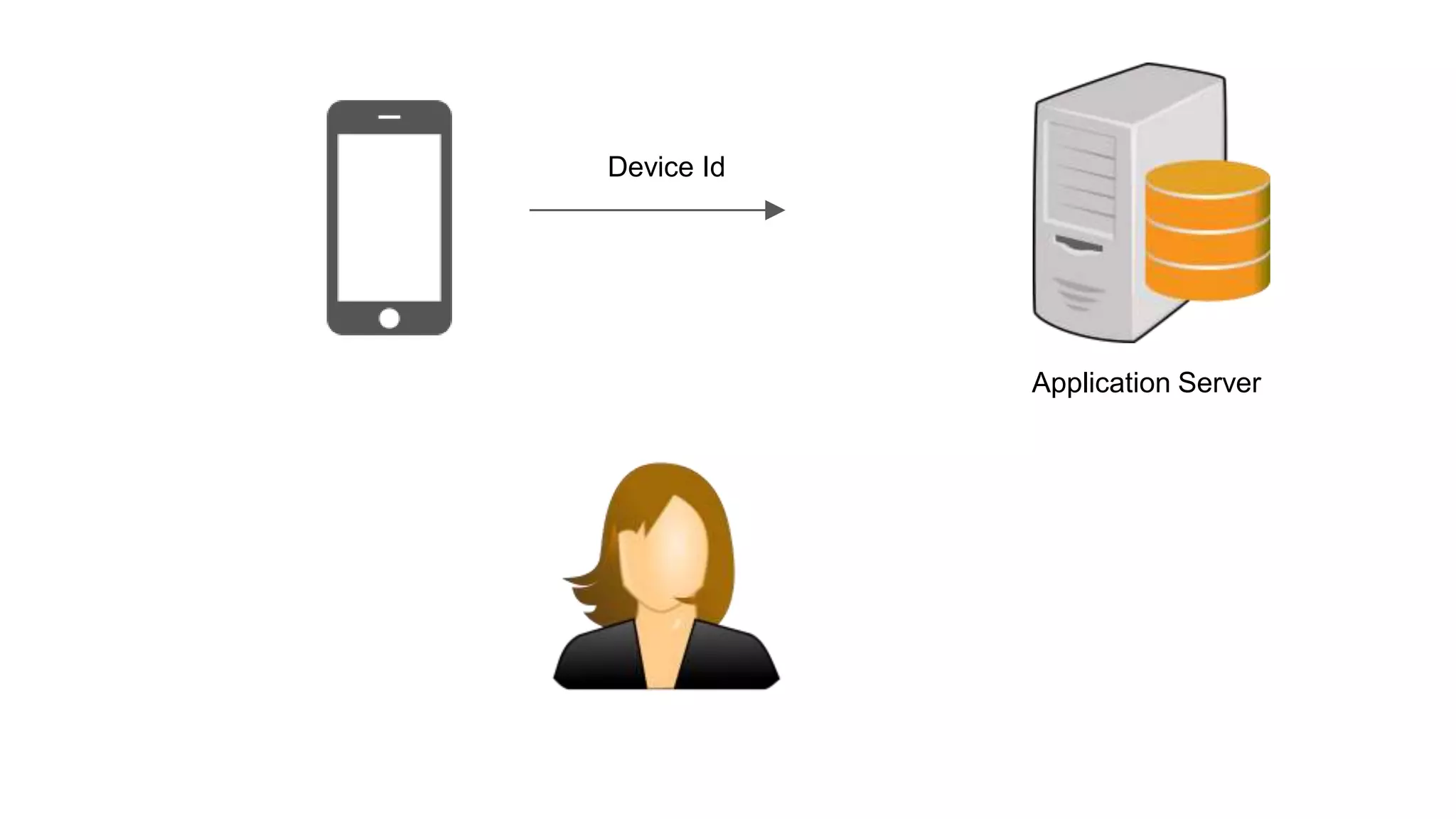
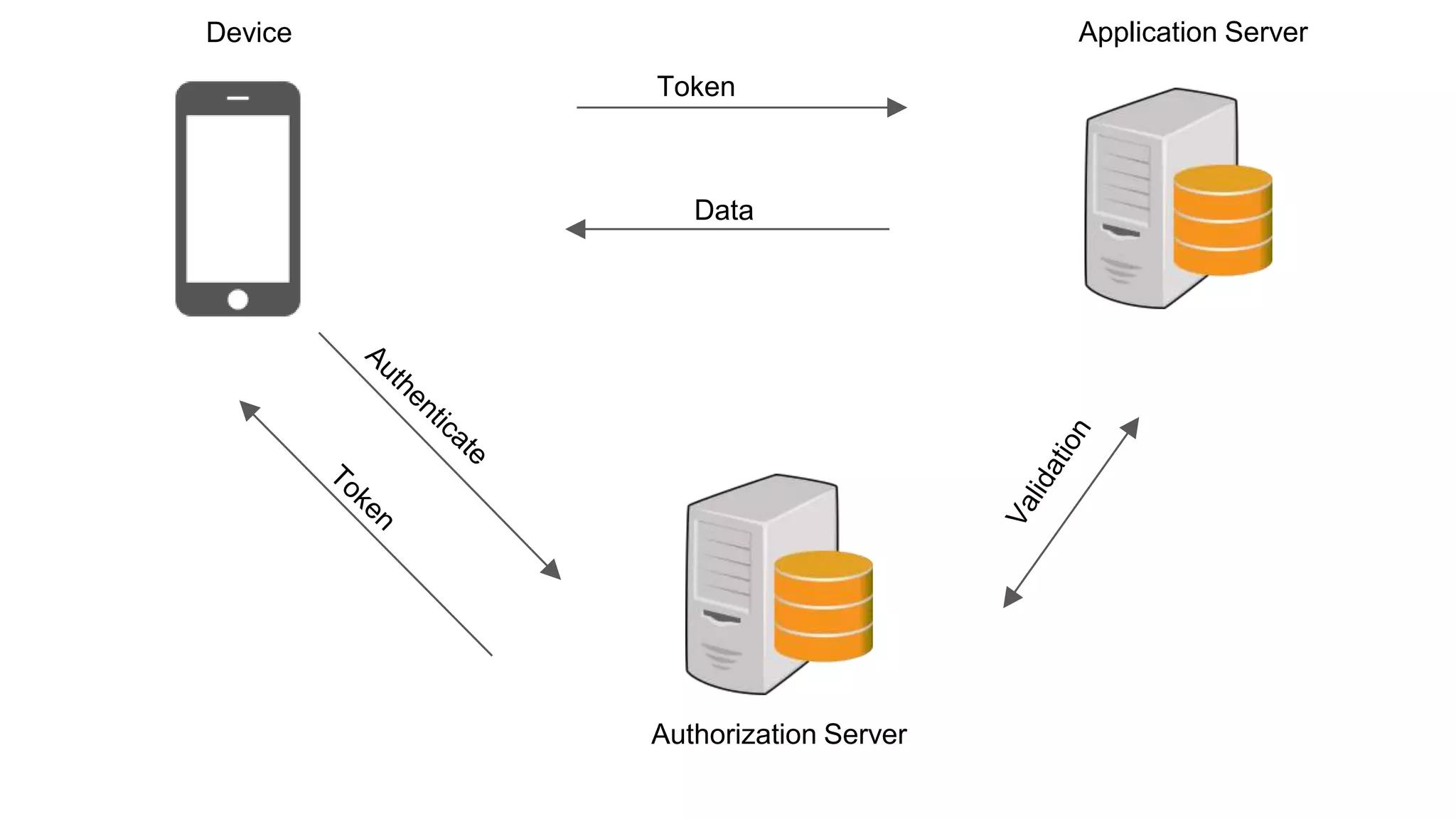
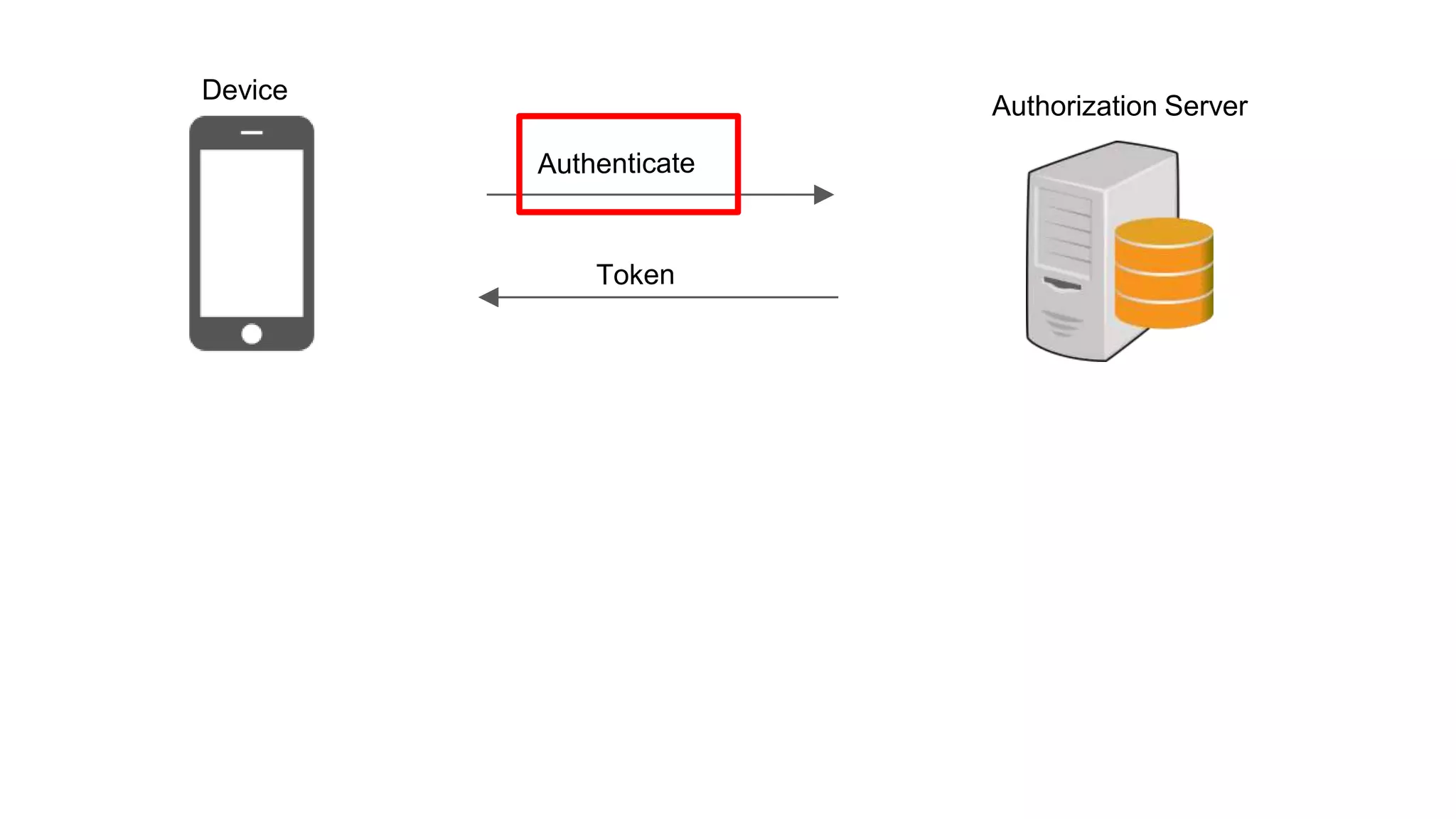
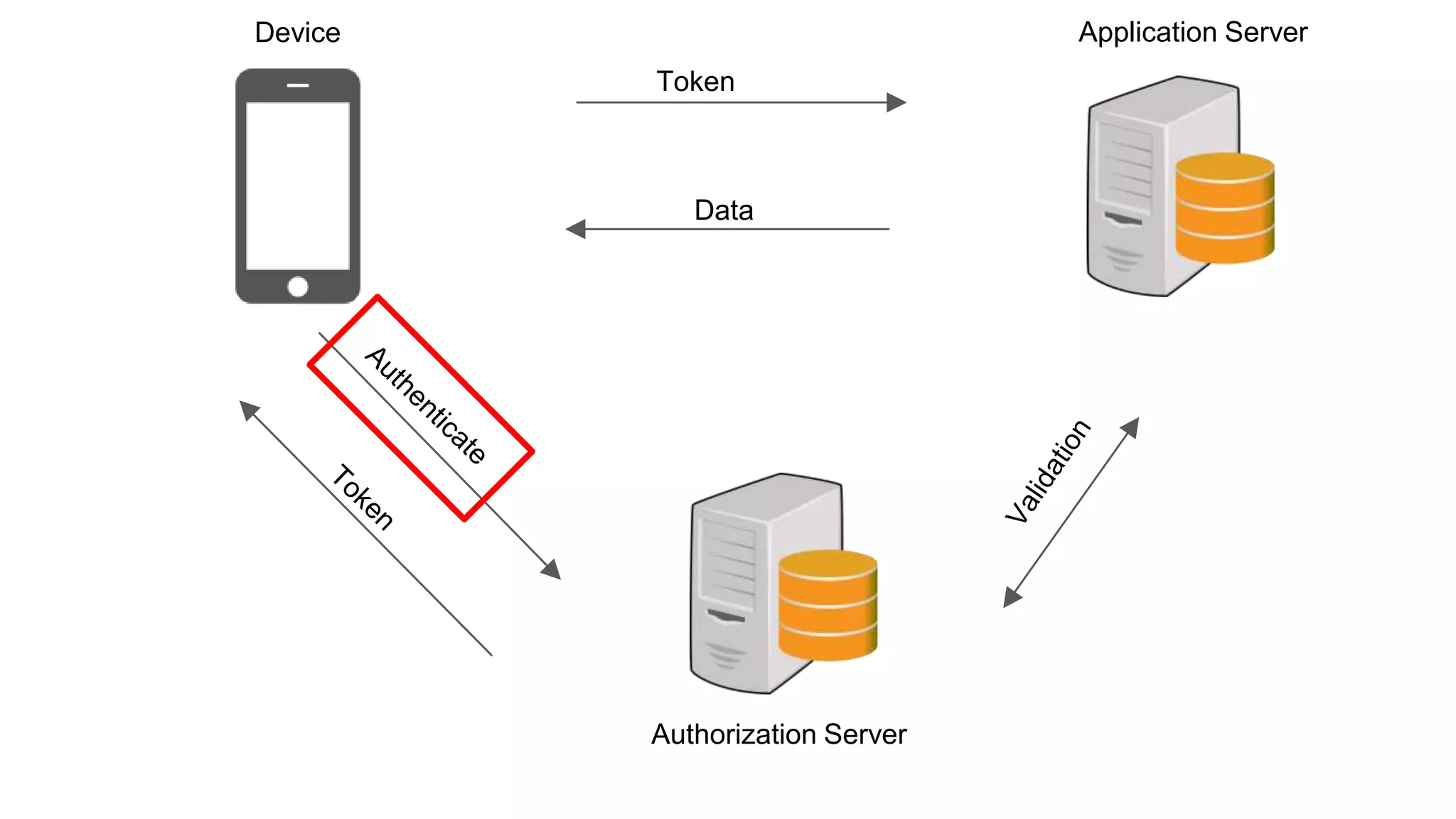
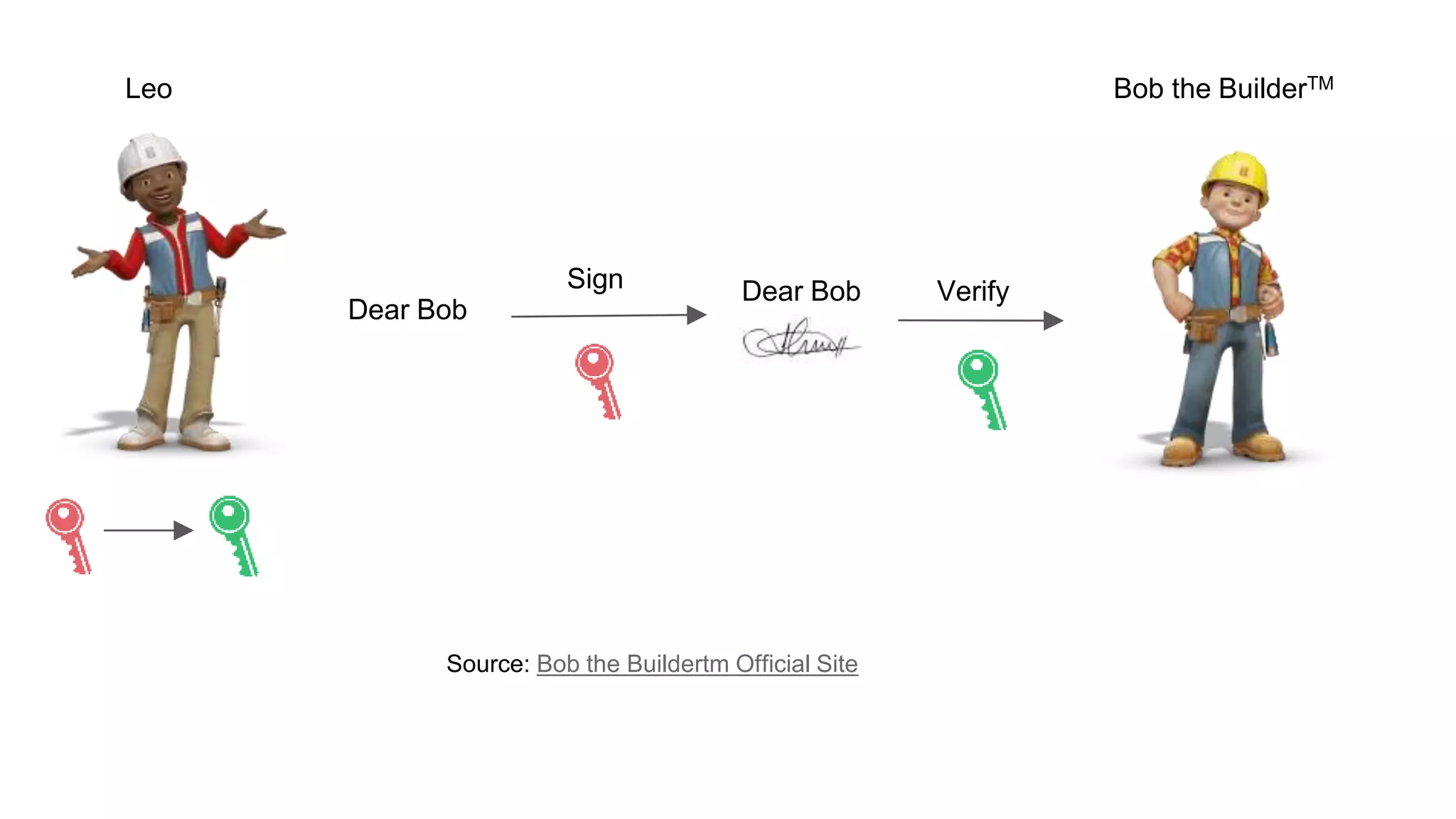
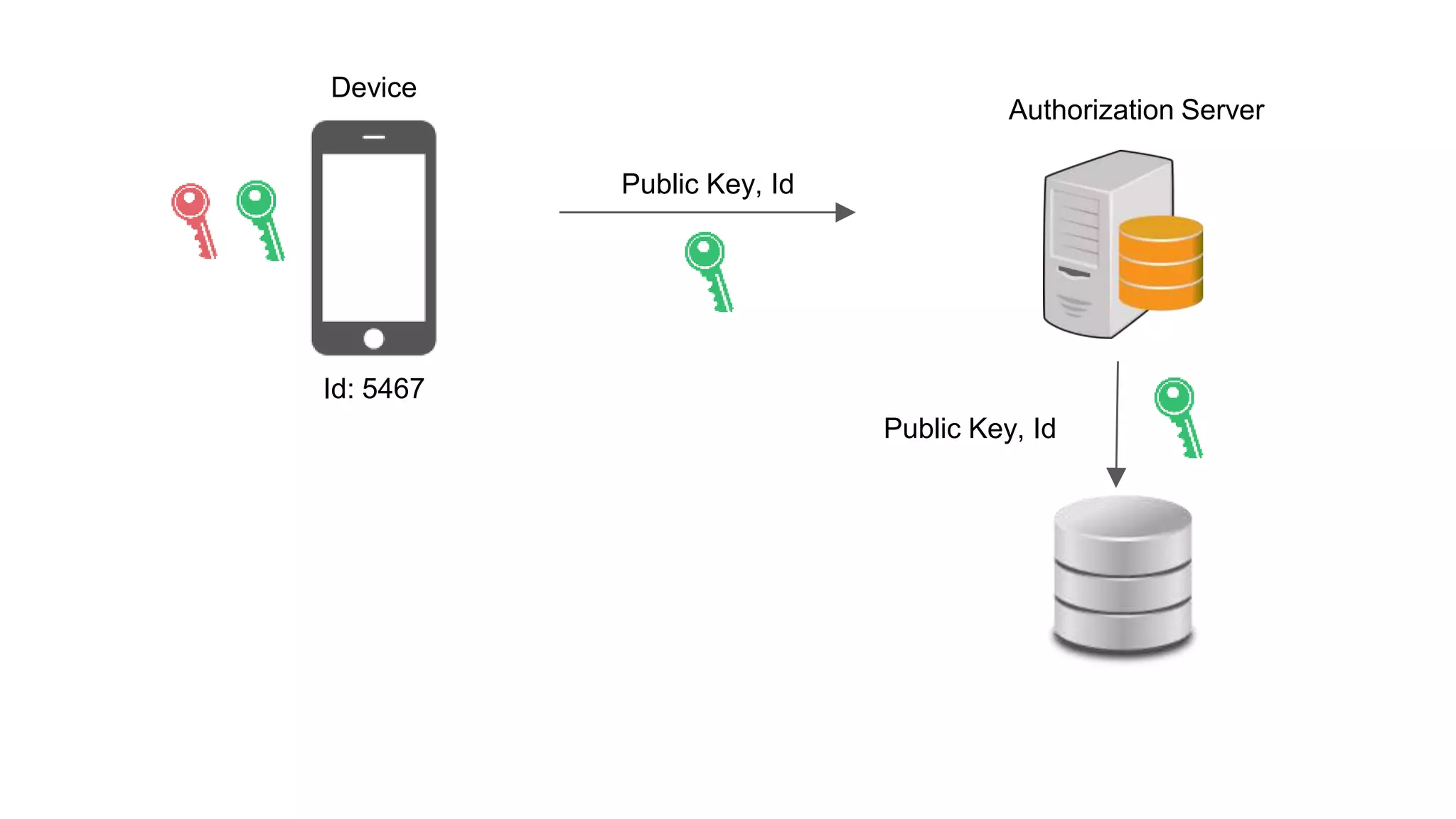
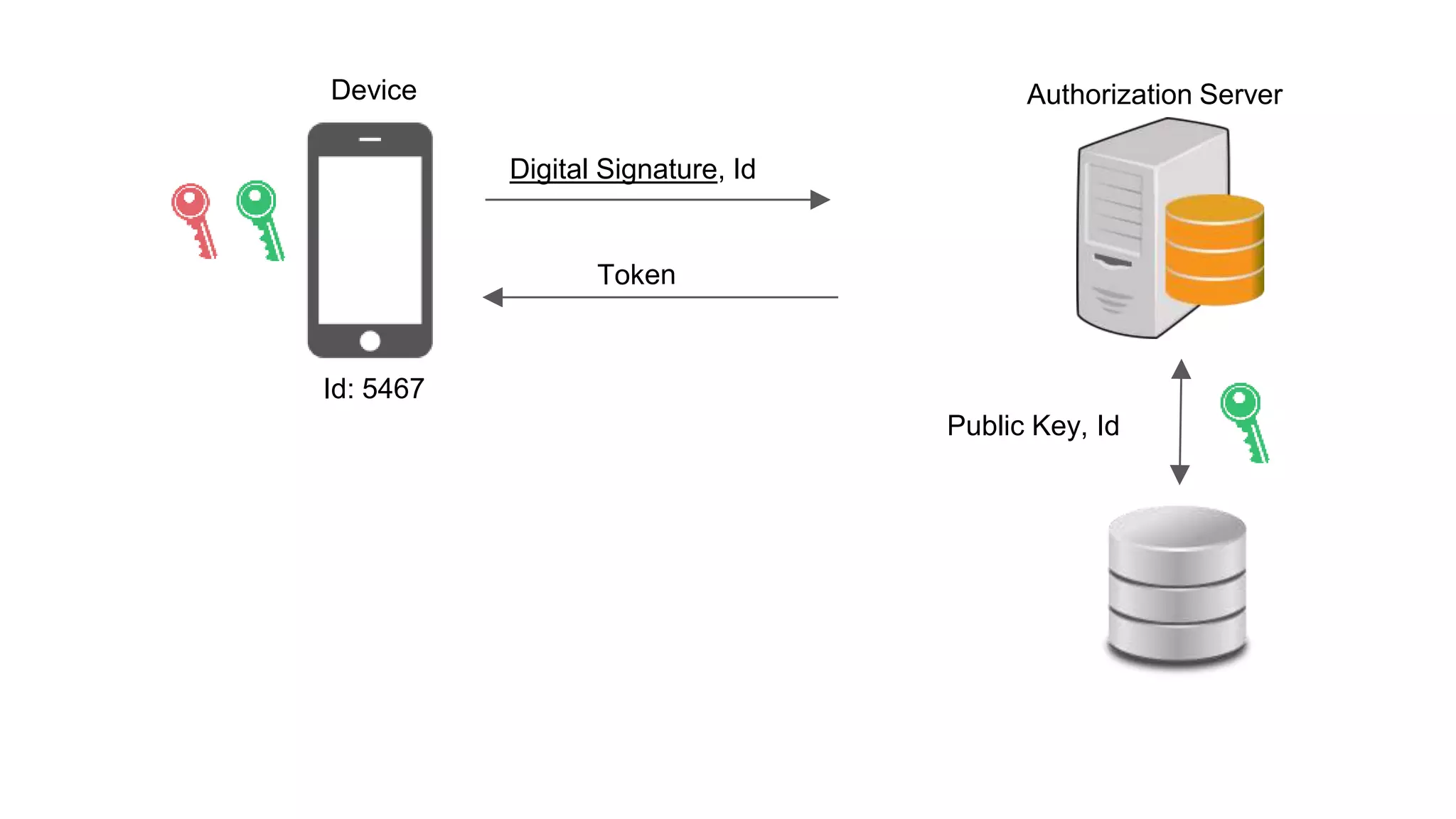
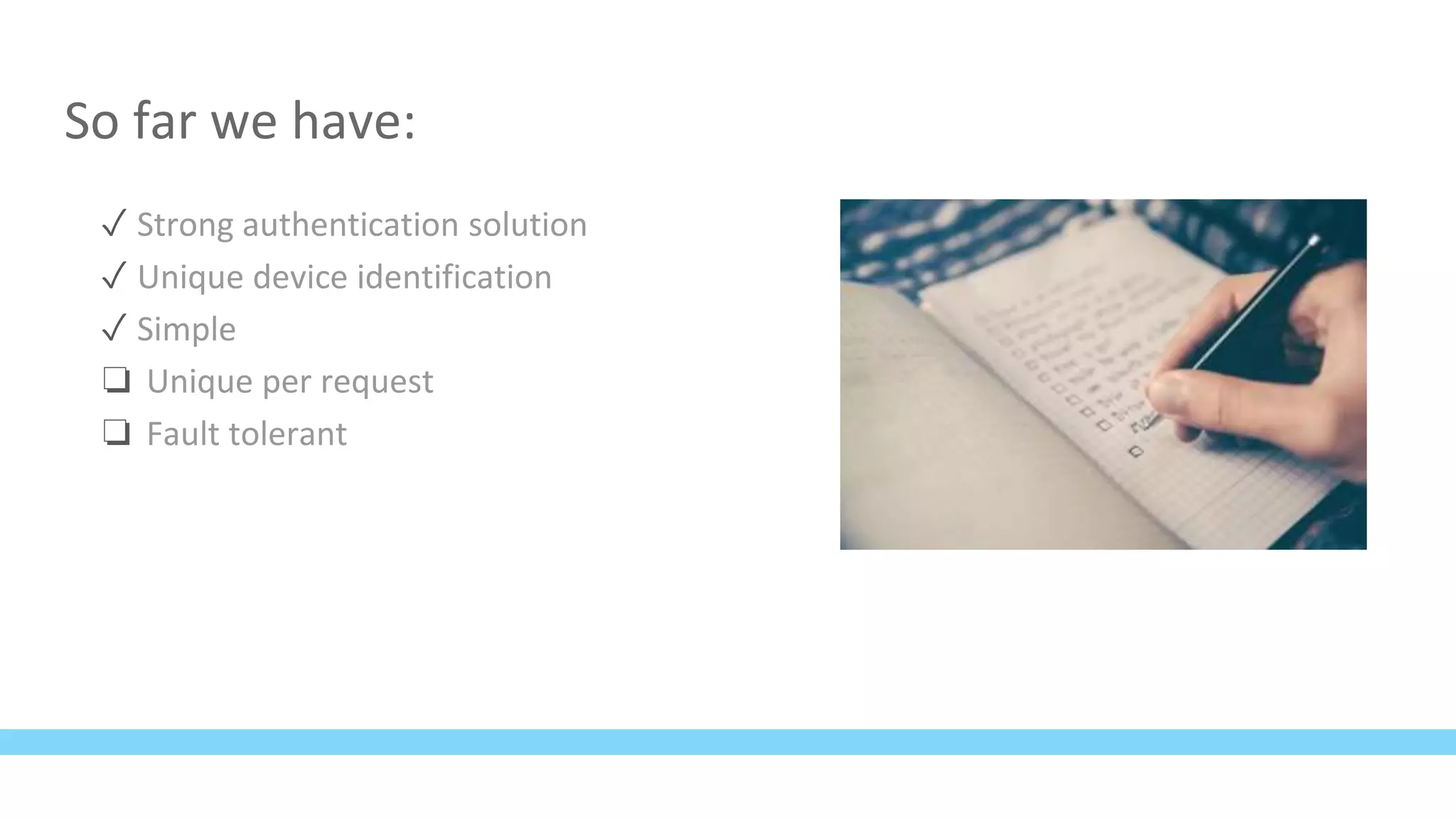
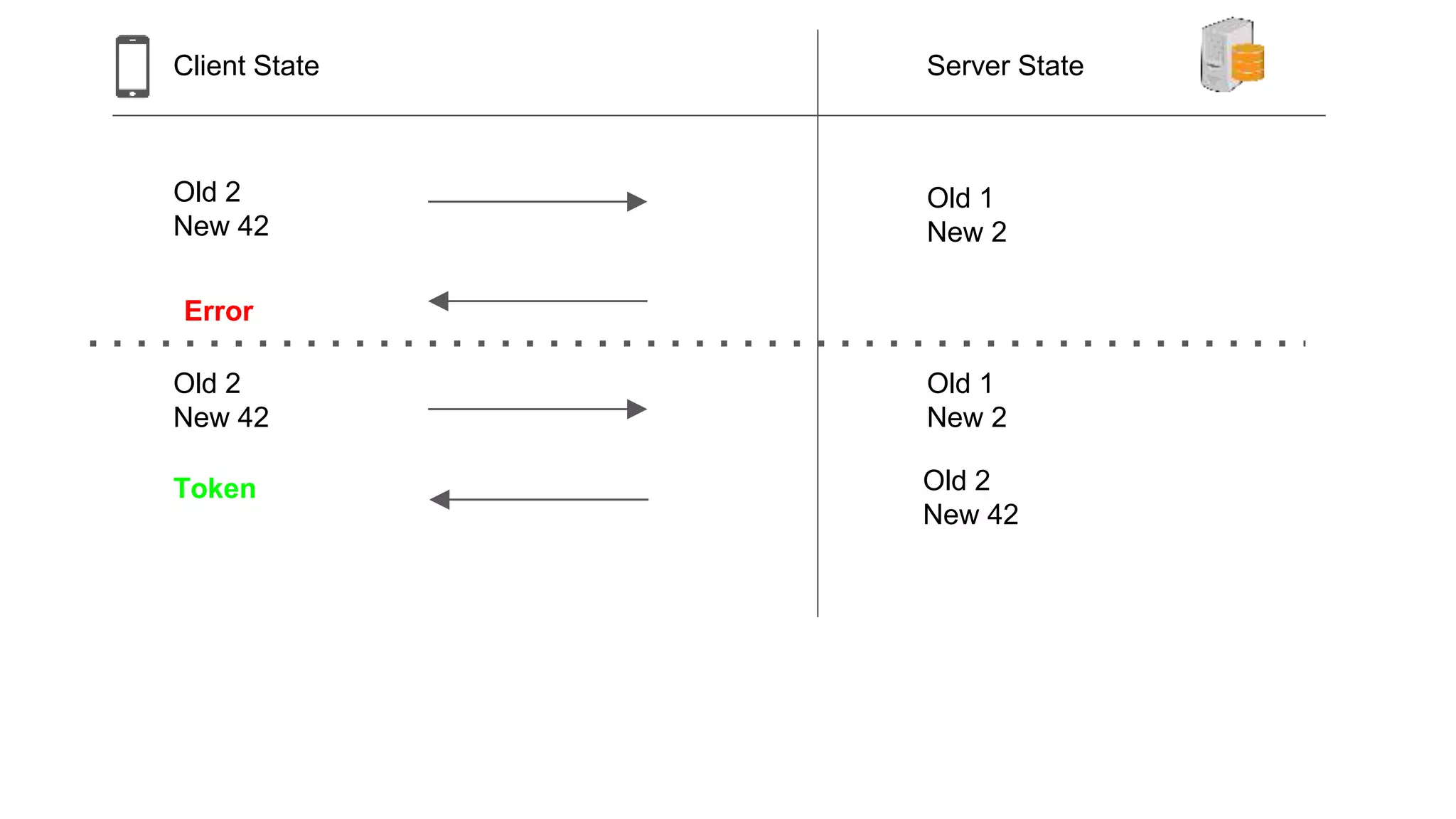
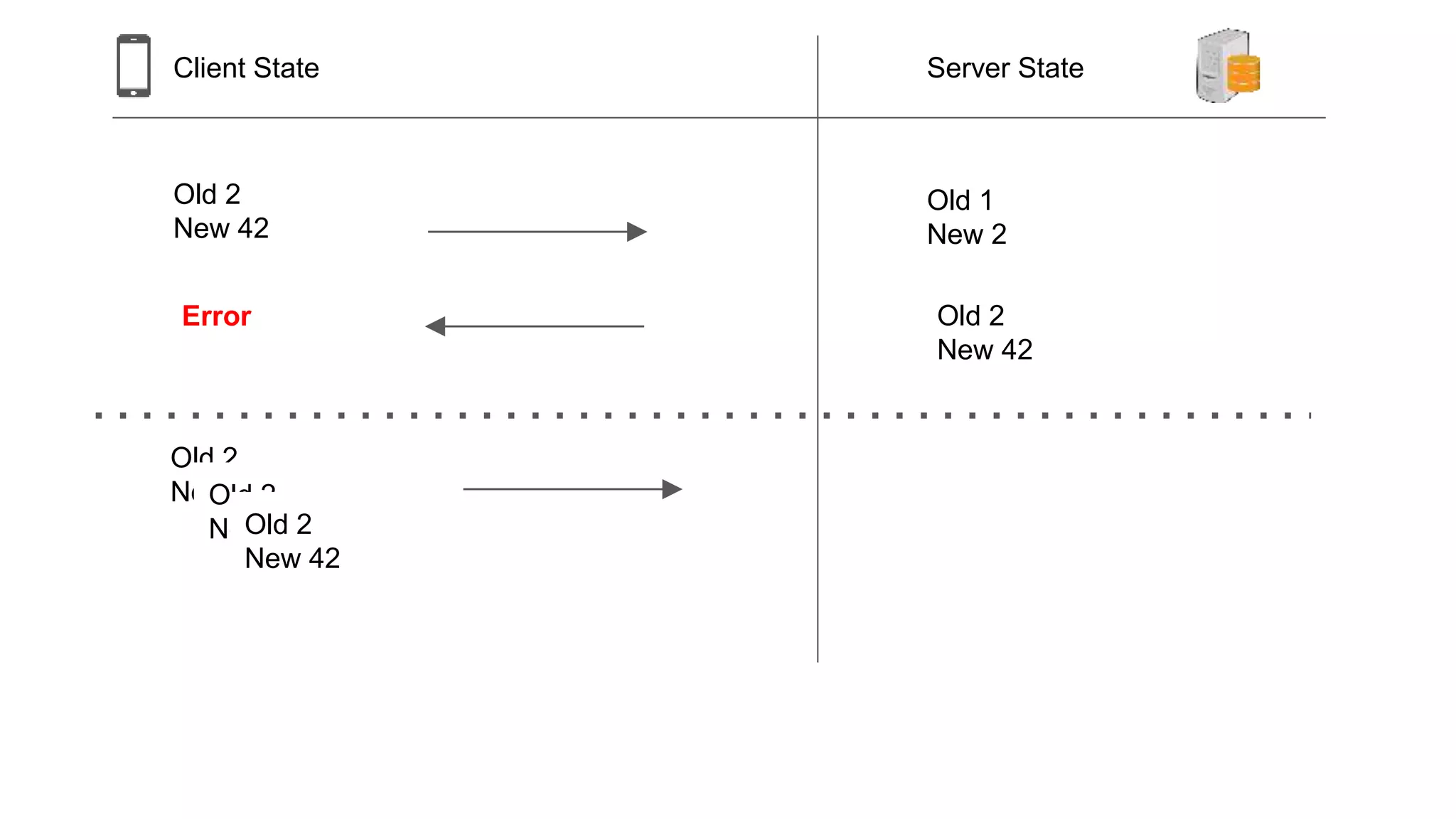
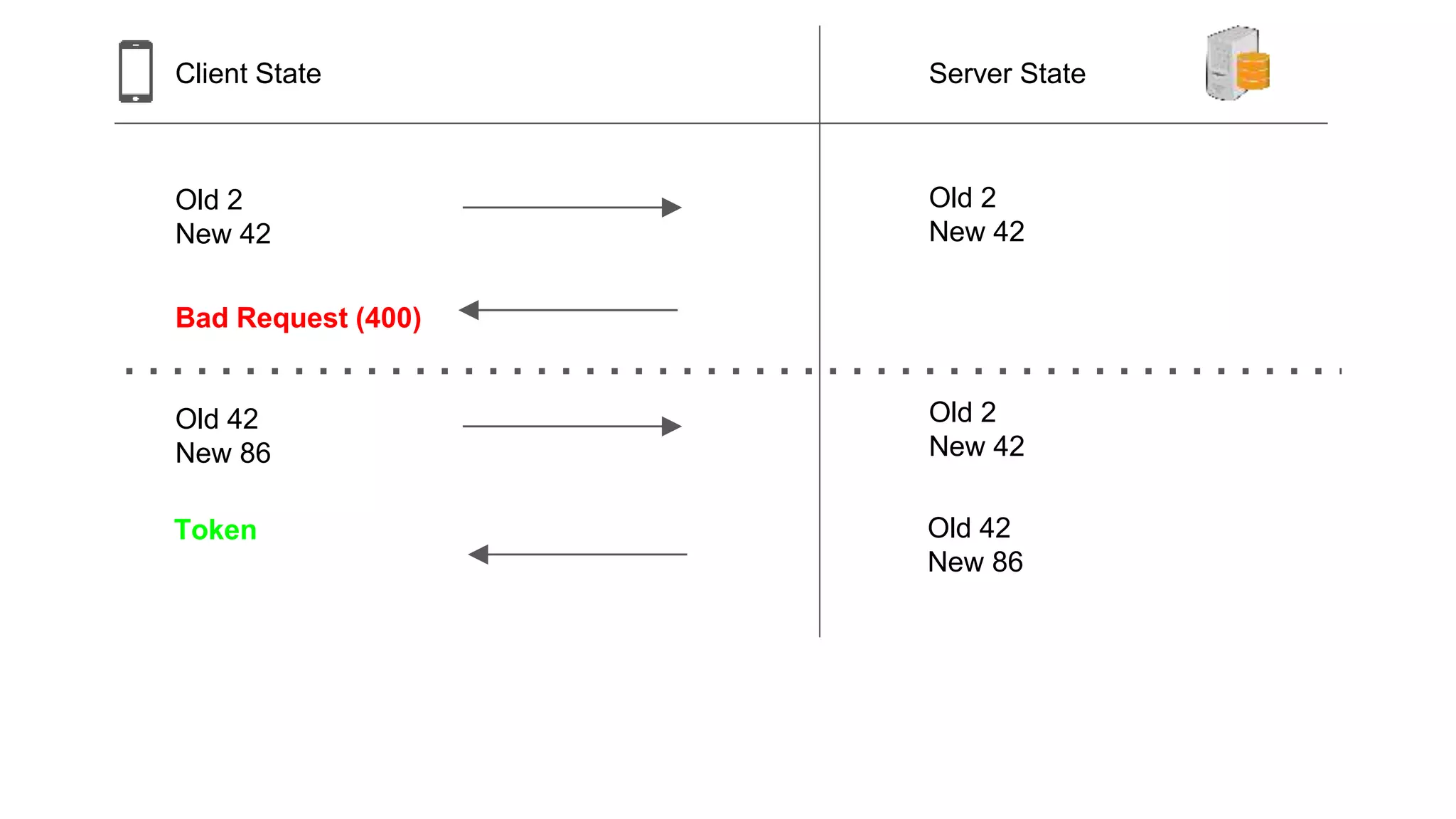
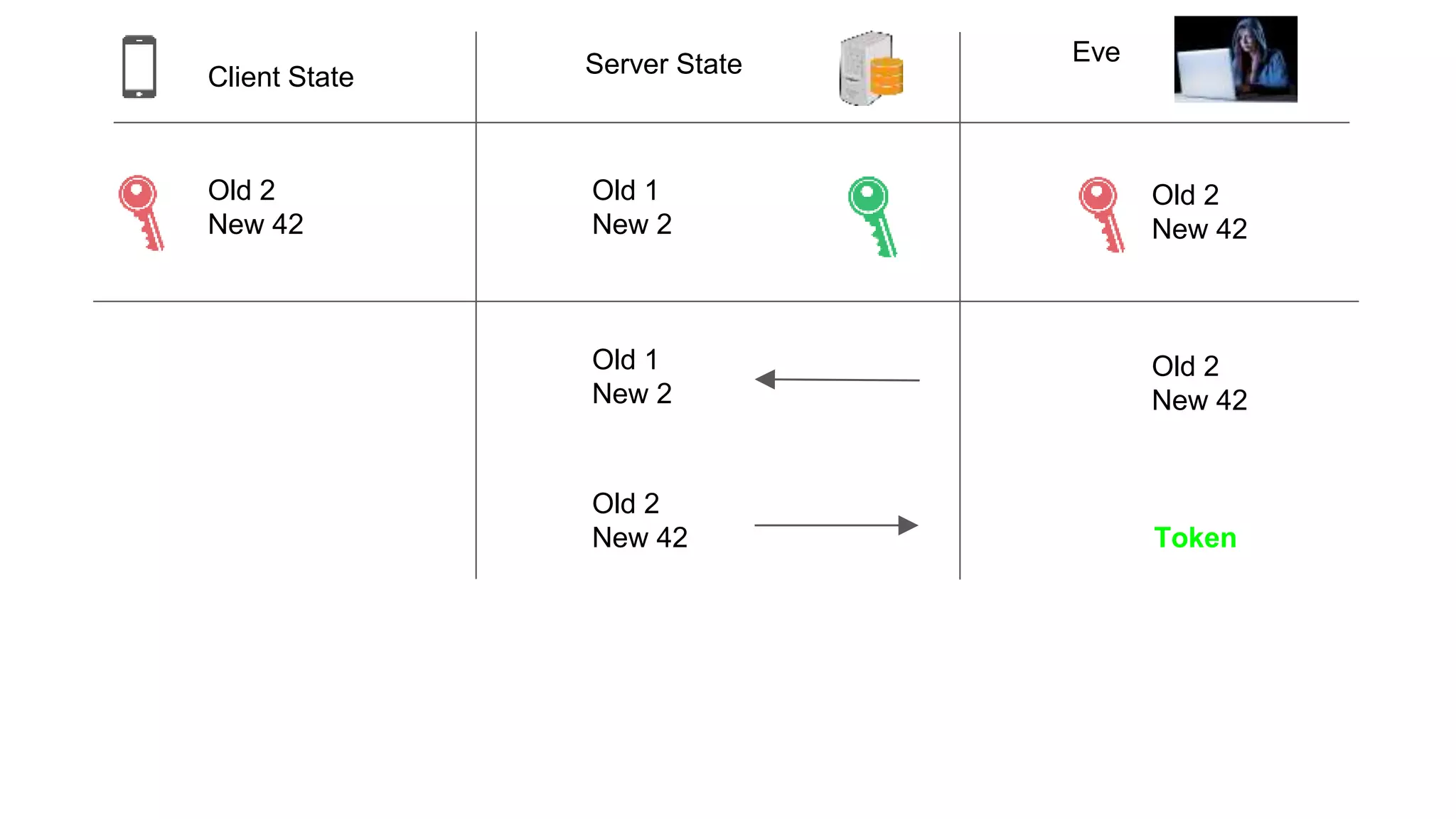
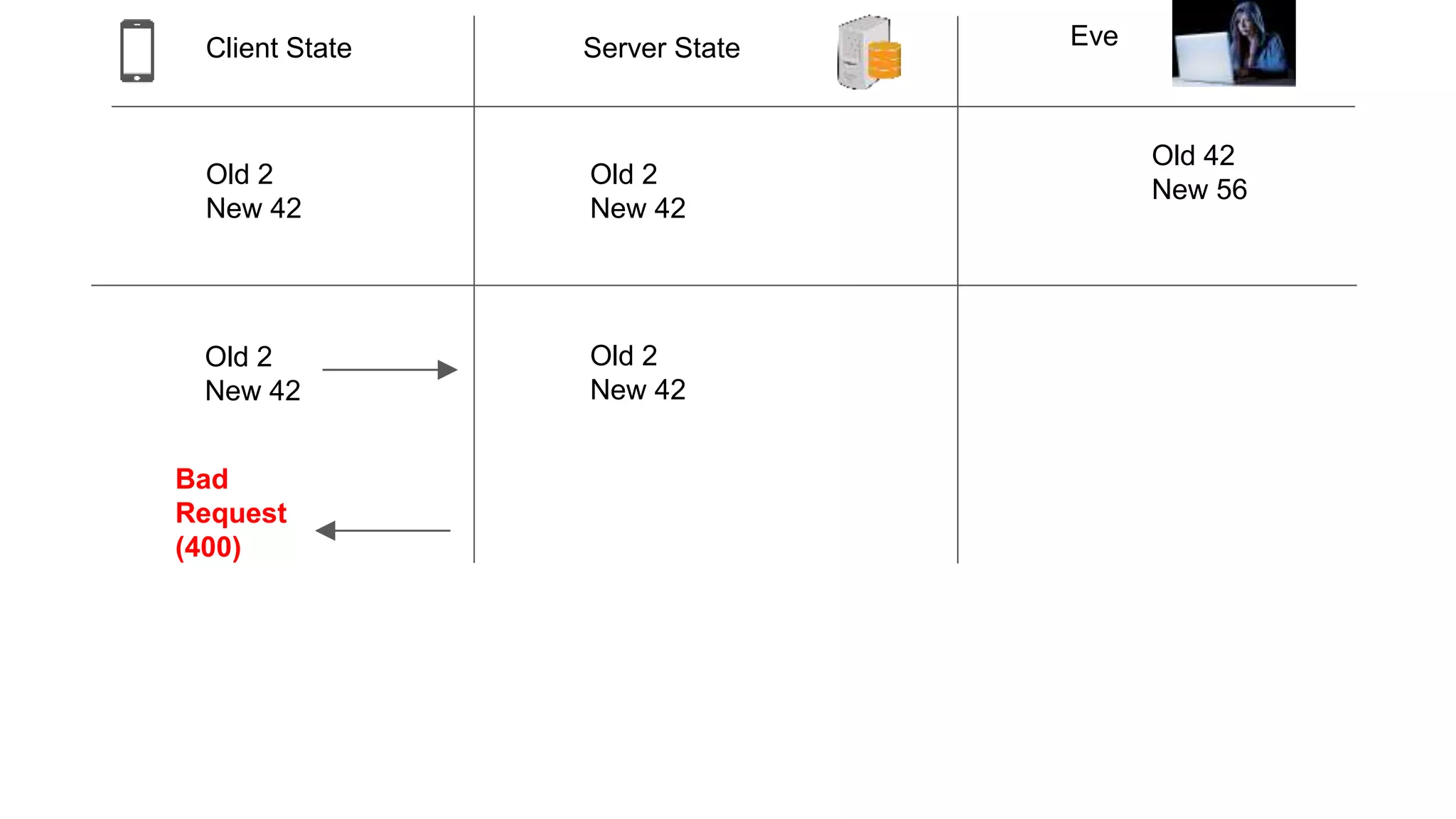
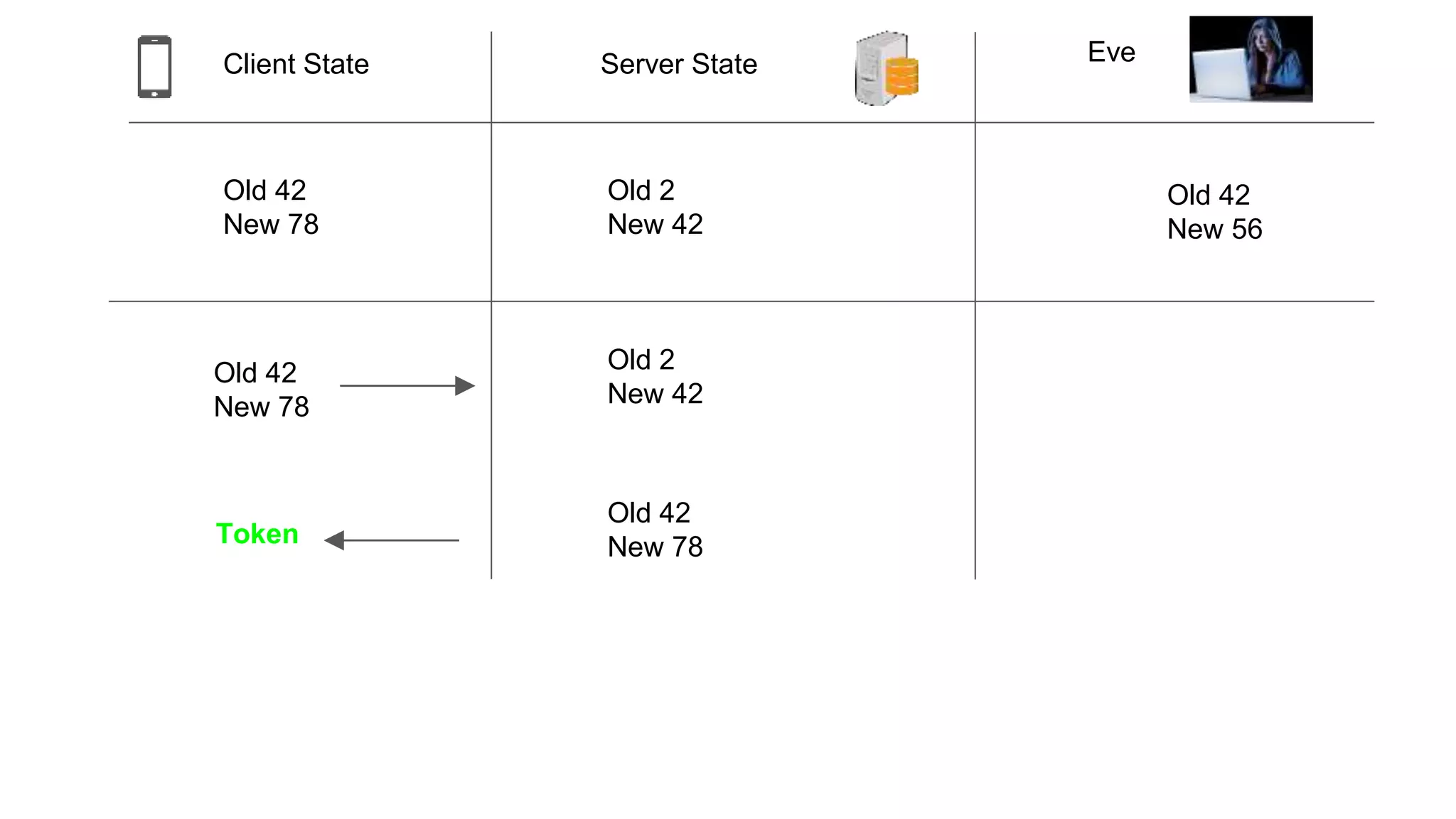
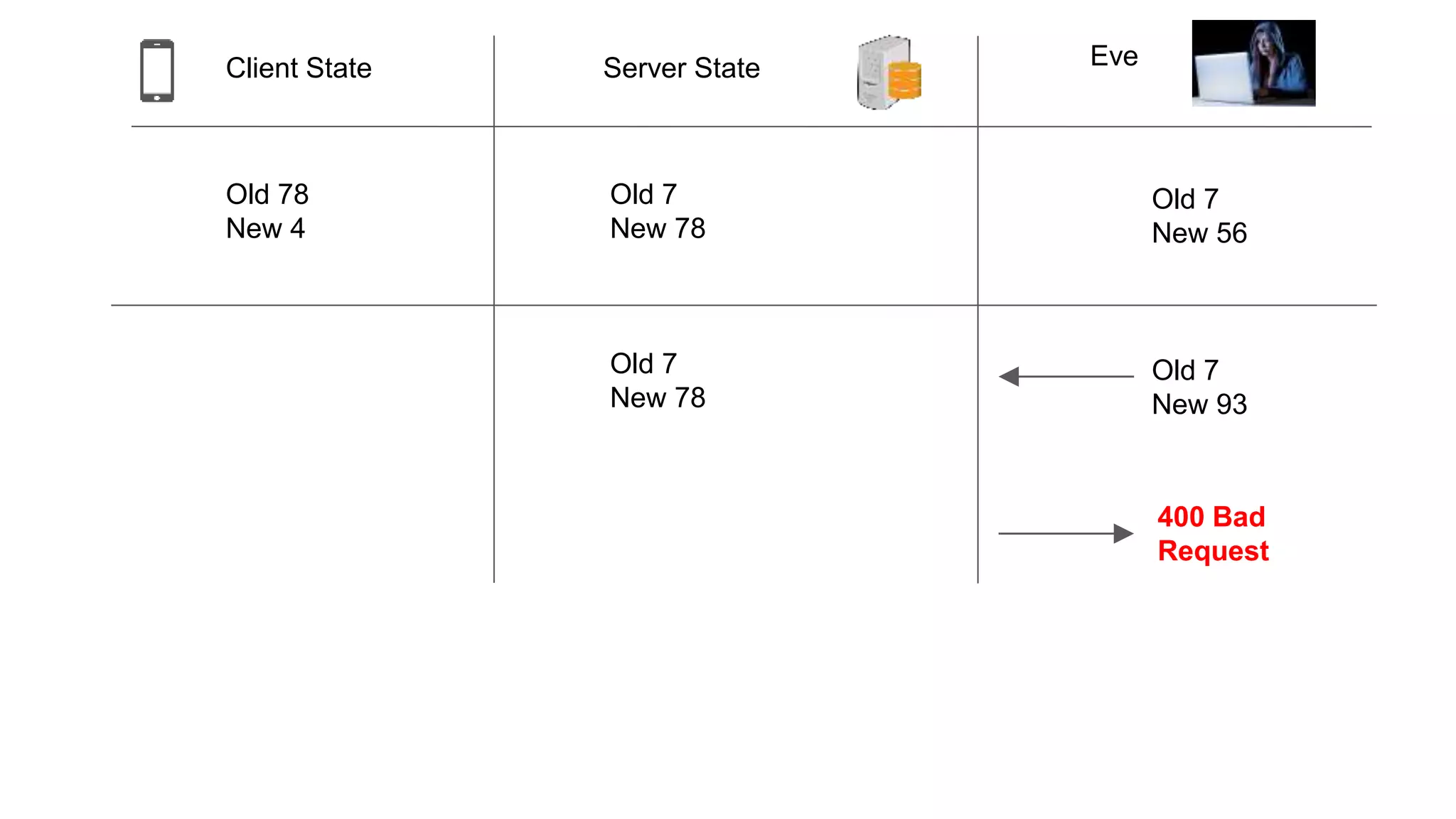
This document summarizes a presentation about authenticating devices without traditional authentication. It describes using digital signatures and one-time passwords to uniquely identify devices based on cryptographic keys. The presentation covers OpenID, digital signatures, one-time passwords, and demonstrates authenticating an API request without passwords. Edge cases like network failures and compromised devices are also addressed. Requirements for the authentication method are that it provides strong authentication, unique device identification, simplicity, unique requests, and fault tolerance.