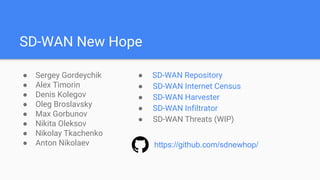
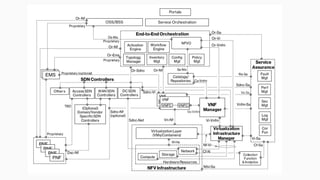
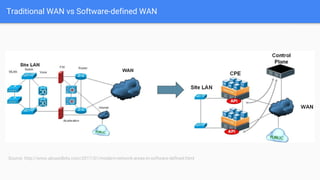
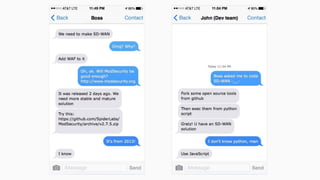
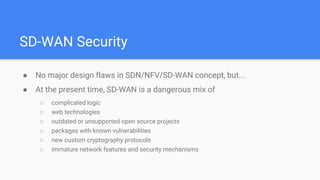
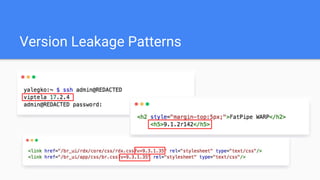
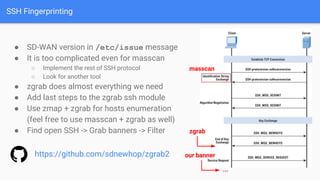
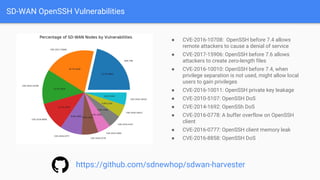
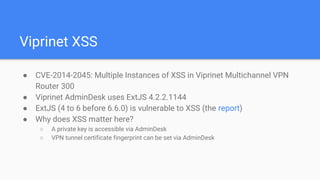
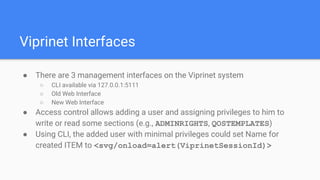
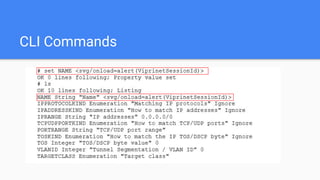
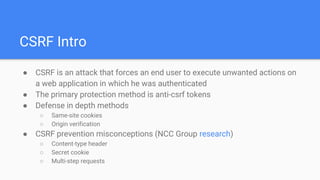
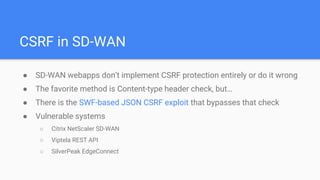
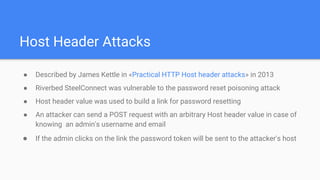
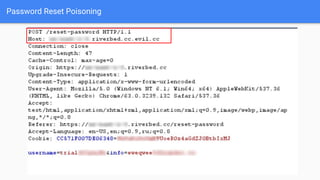
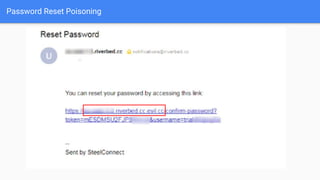
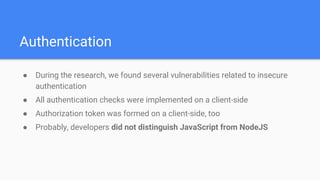
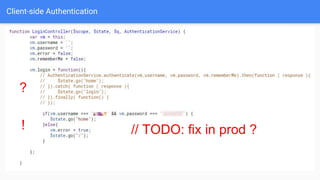
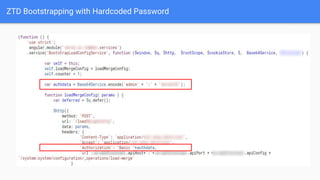
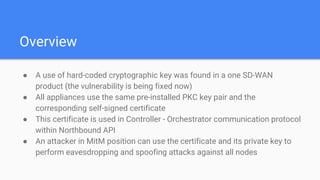
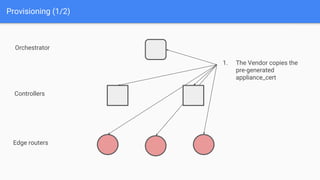
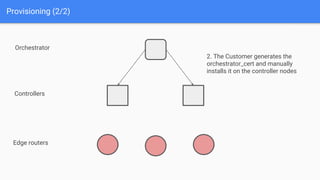
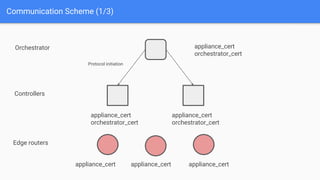
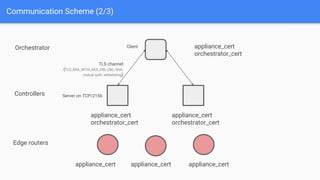
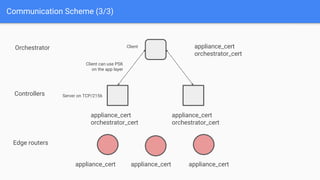
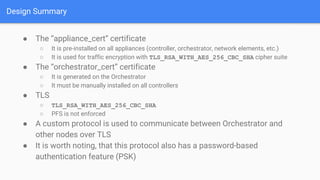
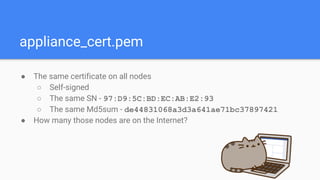
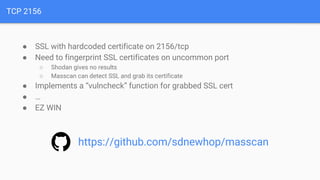
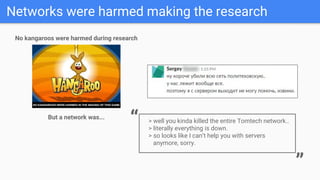
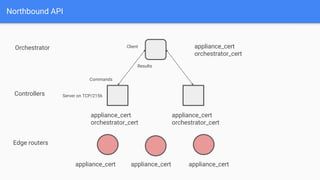
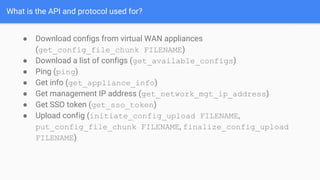
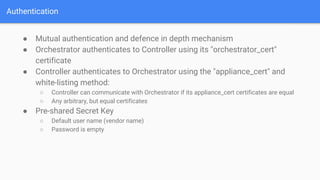
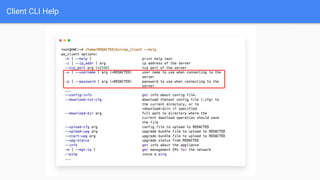
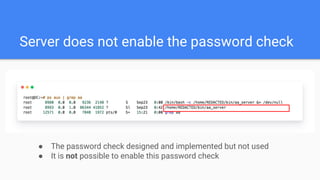
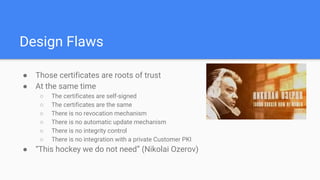
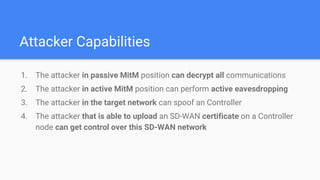
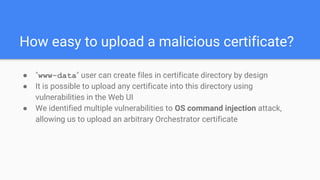
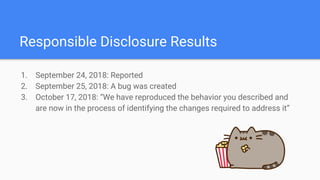
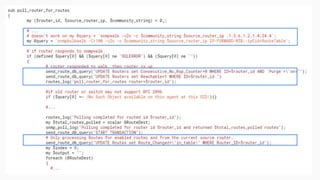
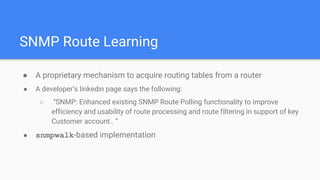
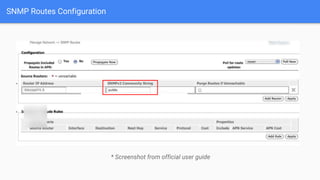
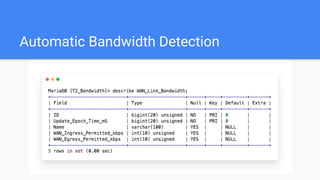
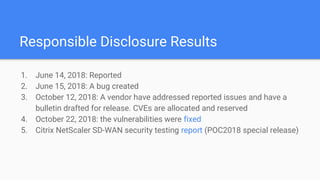
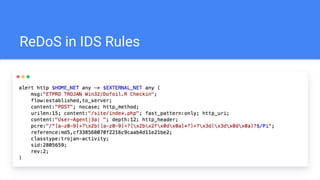
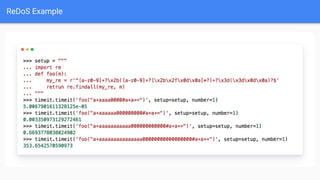
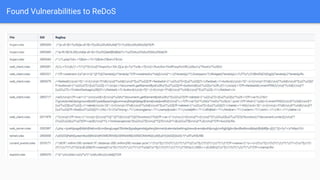
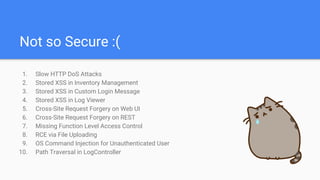
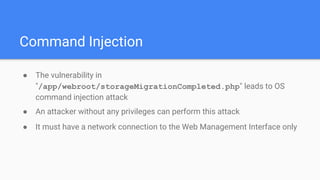
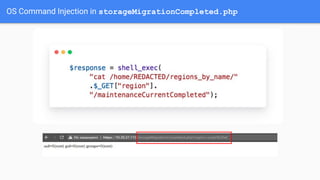
The document discusses the security vulnerabilities of Software-Defined Wide Area Networks (SD-WAN), highlighting issues such as insecure authentication, cross-site scripting, and SQL injection. It also presents an SD-WAN internet census that identifies version leakage patterns and common vulnerabilities encountered during testing. Additionally, the presenters emphasize the need for improved security mechanisms and responsible disclosure practices in the SD-WAN landscape.