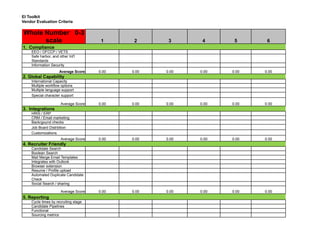
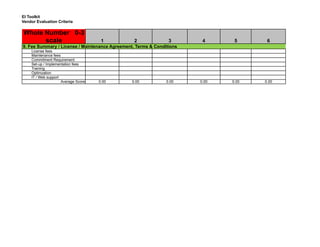
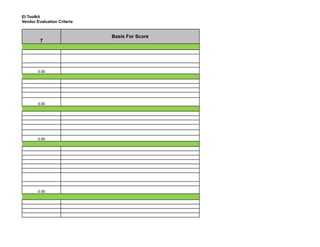
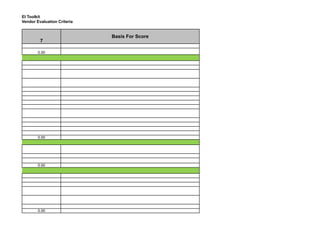
The document outlines vendor evaluation criteria for an EI toolkit using a scoring system ranging from 0 to 3. It covers various metrics, including compliance, global capability, integrations, and customer service. Each category appears to have received an average score of 0.00, indicating no evaluations or assessments have been completed.