Embed presentation
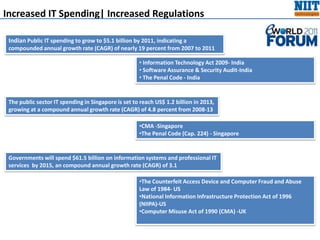
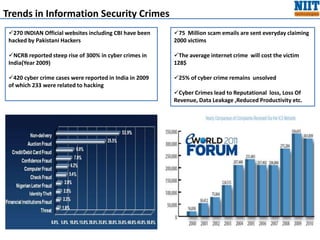
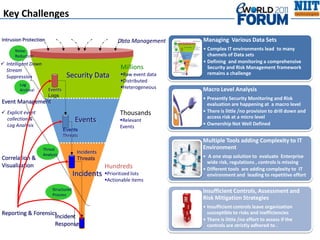
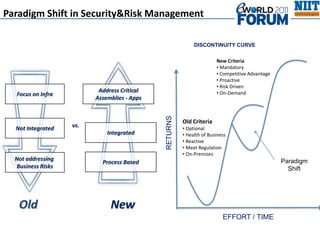

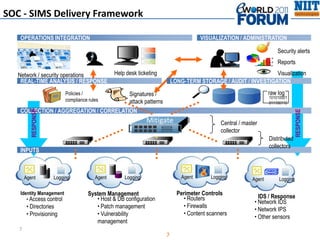
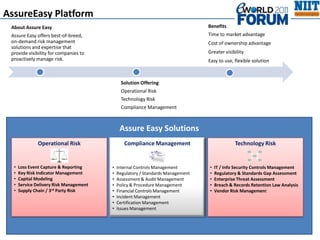
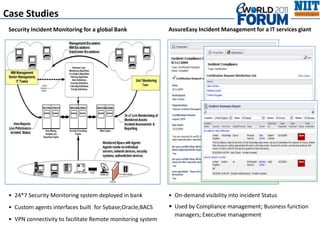


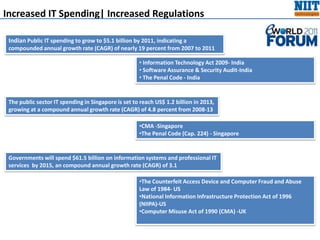
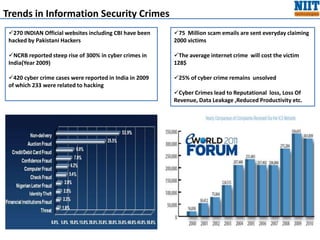
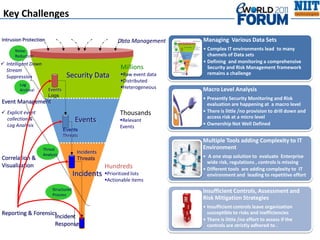
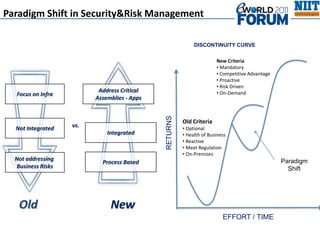
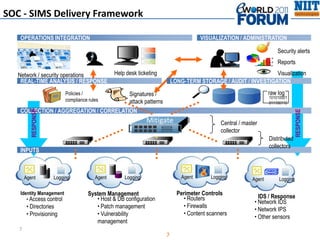
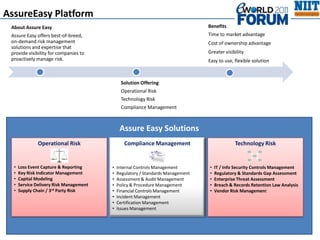
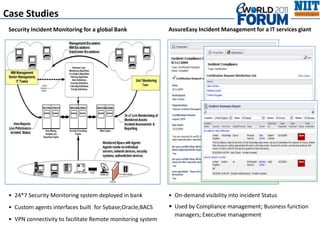
The document discusses trends and forecasts in IT spending and security regulations in India, Singapore, and the US, highlighting significant growth in public sector IT investments. It notes a sharp increase in cyber crimes in India, characterized by hacking incidents and rising scam activities, emphasizing the need for robust information security measures. The proposed solutions include integrated security monitoring frameworks and risk management platforms designed to enhance compliance and incident response capabilities.