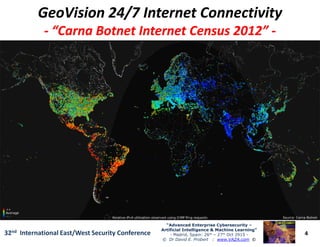
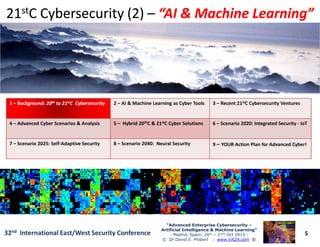
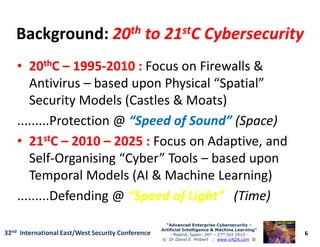
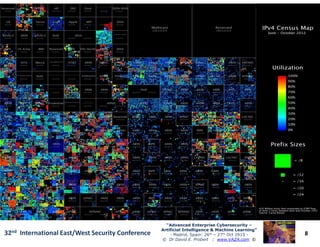
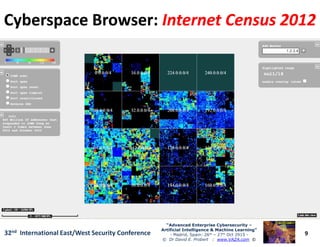
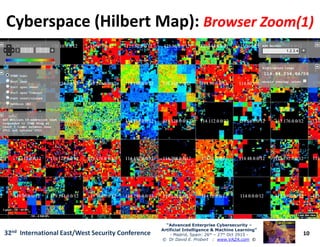
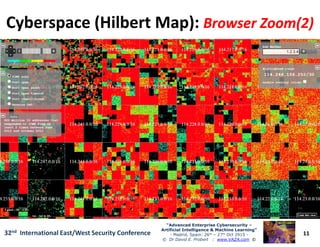
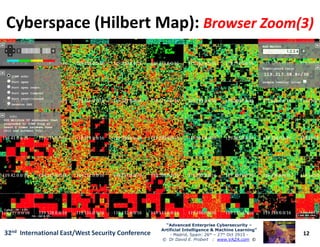
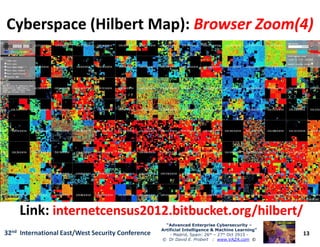
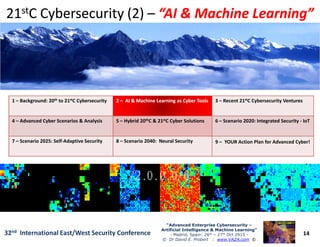
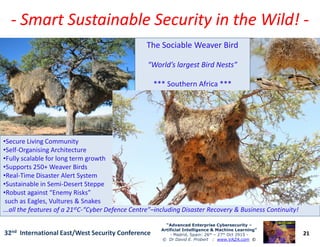
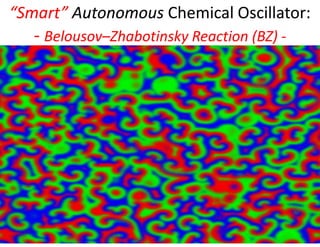
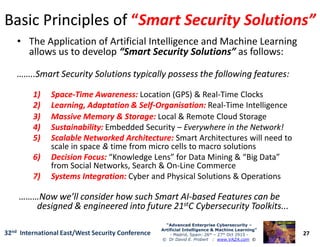
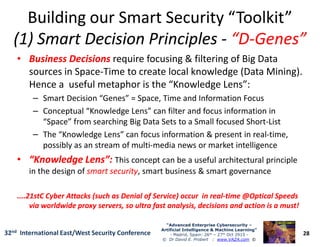
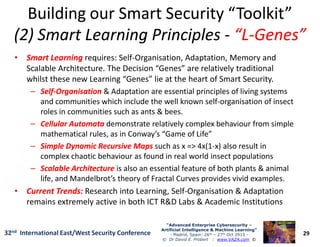
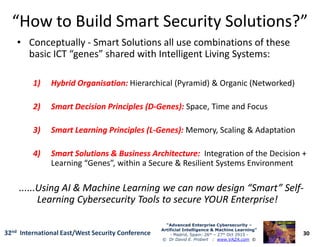
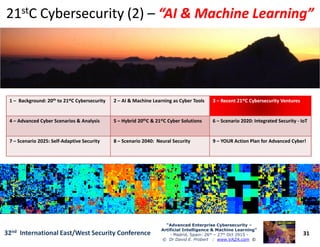
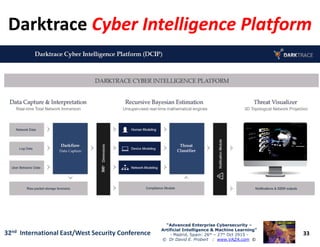
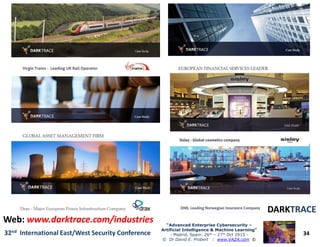
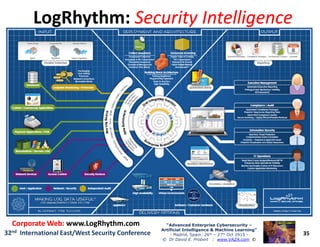
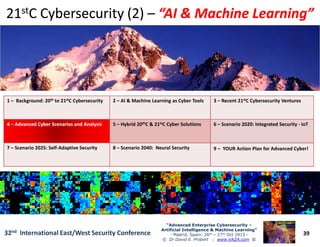
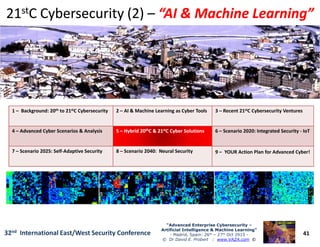
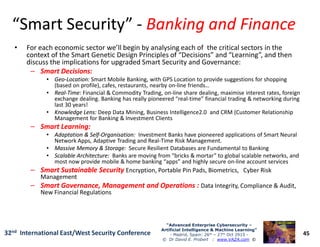
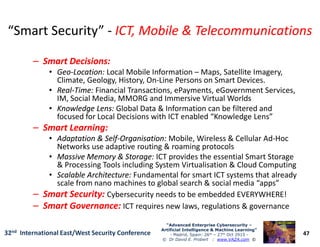
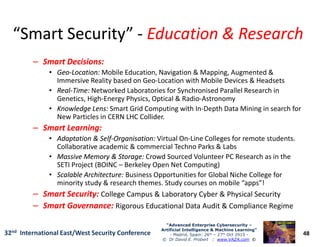
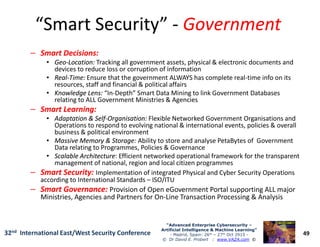
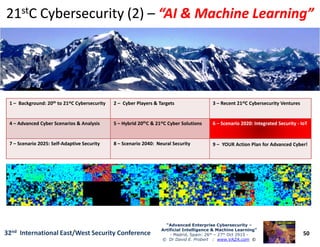
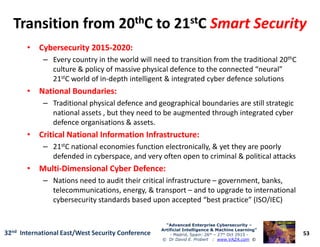
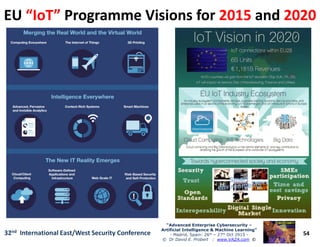
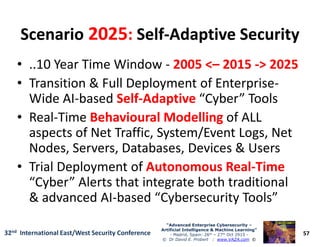
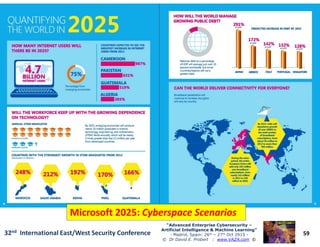
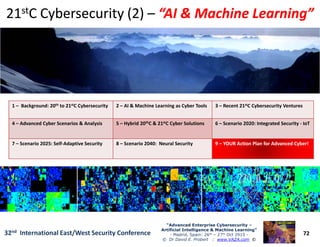
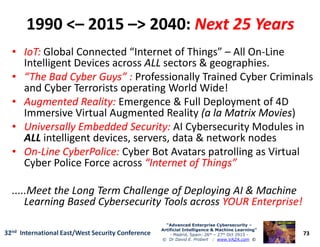
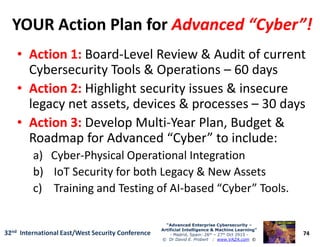
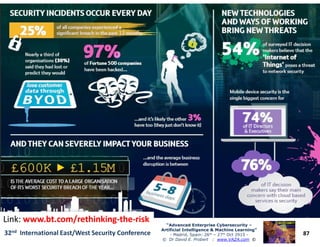
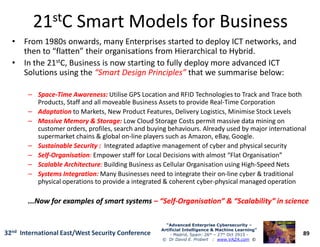
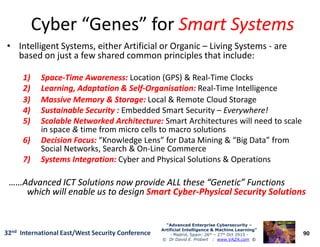
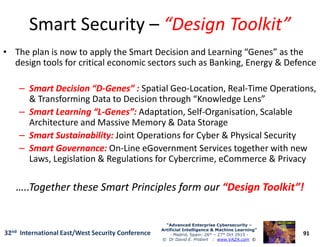
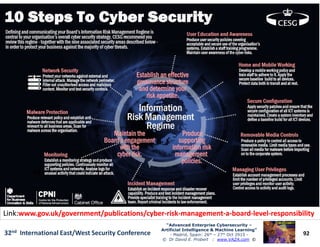
The document discusses advanced cybersecurity trends, focusing on the integration of artificial intelligence and machine learning for enhanced security measures. It highlights the transition from traditional security models to more adaptive, self-organizing systems that can mitigate risks in an increasingly interconnected world, particularly with the rise of the Internet of Things. The conference, held in Madrid in October 2015, emphasizes the need for enterprises to develop comprehensive action plans to address future cyber threats.