Embed presentation
Downloaded 33 times
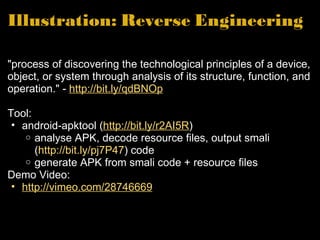

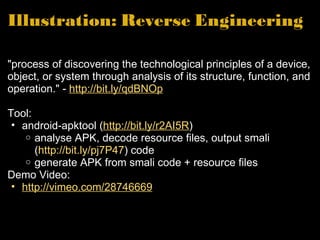
Leong Hean Hong, a project manager at Stream Media Pte. Ltd., discusses the importance of Android security, particularly for mobile commerce and banking applications. The presentation highlights potential security issues, including personal information theft and code modification attacks, and encourages developers to prioritize security throughout the app development process. Tools like android-apktool are introduced for reverse engineering APK files to analyze vulnerabilities.