1) The document discusses modeling techniques for active components in digital systems to accurately capture their dynamic behavior at high speeds.
2) Traditional SPICE models and transmission line equivalents are not suitable for simulating circuits with hundreds of elements due to slow simulation times and convergence problems.
3) The modeling approach presented uses primitives from the DWN simulator to create behavioral models of active components based on time domain reflectometer (TDR) measurements, allowing for much faster simulations while maintaining accuracy.
![PB 1990-2009 AN 02
DWN & DWV
MODELING OF ACTIVE COMPONENTS
The fast growth of signal integrity equivalents, as those utilized in the
and EMC problems of digital transmission line simulators, are The modeling approach shown in
systems requires very accurate not sufficient to describe the this application note is based on the
modeling techniques of active unpredictable dynamic effects of primitives offered by the DWN
components, especially regarding real devices. simulator and allows the designer to
their dynamic behavior at high
speed. On the other hand, the
growing complexity of systems
imposes severe goals regarding the Ctdr
coax
simulation speed. As known the
two requirements of speed and Z0 DUT
accuracy are opposite, so that the
R
traditional approach to these Vbias vcc
problems leads to unsatisfying TDR gnd
ground plane
results. SPICE models, for
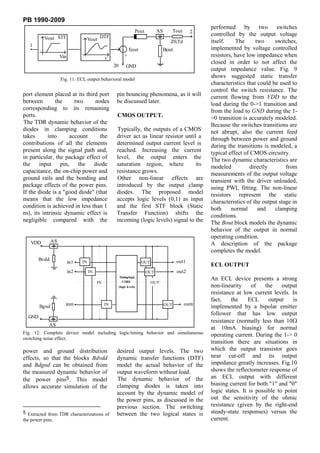
example, are not suitable for the Fig. 1: Measurement set-up for TDR characterization.
simulation of circuits with more
than few hundred elements, A behavioral or mixed electrical- perform very accurate electrical
because the simulation time rises behavioral approach is much more simulations with a speed at least
prohibitively with circuit effective to face real-world two orders of magnitude greater
complexity and convergence situations, where the effects of than other commercial products1.
problems could occur. active parts, lossless or lossy This modeling procedure is simple
Furthermore, the results often don't interconnections, EMC constraints, and the data can be collected from
reflect the real situations. In fact, and electrical, logical and timing several sources. In particular, it is
the parasitic effects introduced by issues must be taken possible to extract model
the discontinuities of the package simultaneously into account. parameters from datasheet, from
and the pin bouncing (caused by analog simulations (SPICE, ELDO,
simultaneous output switching) DWN MODELING etc.) or, better, directly from
can often invalidate the results. On APPROACH TDR (Time Domain
the other hand, simple circuital Reflectometer) measurements.
1.00 # Thanks to this fast experimental
#RHO
D approach, the model can take all the
0.80 #
non-linearities of the I/O cells of
0.60 # the device into account,
C
0.40 #
B
0.20 #
A
-0.00 #
-0.20 #
-0.40 #
-0.60 #
-0.80 #
-1.00 #
1DWN uses a very fast DSP engine that
0.40 0.60 0.80 1.00 1.20 1.40 1.60 1.80 2.00 2.20 2.40 2.60 assures high speed without convergence
TIME[nS] problems.
Fig. 2: TDR response for a CMOS input
HDT Copyright 1990](https://image.slidesharecdn.com/an02dws-120331083228-phpapp02/85/An02-dws-1-320.jpg)
![PB 1990-2009
0.60 #
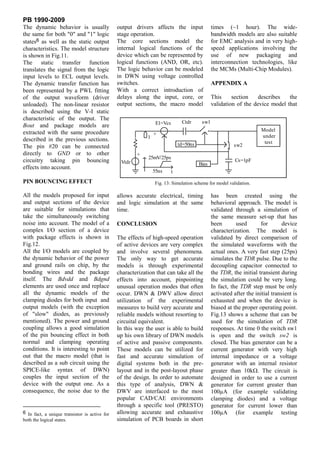
clamping diodes for protection
0.40 # against electrical discharge, so an
Iclamp=0.2MA accurate model must take both their
0.20 #
non-linear and dynamic effects into
-0.00 # account, as shown in Fig.5. In this
situation it is necessary to introduce
Iclamp=1MA
-0.20 #
the effect of power and ground pins
-0.40 #
because during the clamping action
the diode current flows through
Iclamp=5MA
-0.60 #
them.
-0.80 # Iclamp=20MA
-1.00 #
0.00 2.00 4.00 6.00 8.00 10.00 12.00 14.00 16.00 18.00 20.00 V (V) I(mA)
TIME[nS]
0.00 0.0
a) 0.50 0.1
0.60 #
0.55 0.3
0.40 #
0.60 0.9
0.20 #
0.65 1.8
Iclamp=0.5MA
0.68 3.8
-0.00 #
0.70 10.7
-0.20 #
Iclamp=1MA 0.72 25.4
Tab.1: Example of static charac-
-0.40 # teristic of clamping diode.
-0.60 #
Iclamp=5MA Often each diode has a specific
static and dynamic behavior.
-0.80 #
Iclamp=20MA
Sometimes the static characteristic
is available from the datasheet with
-1.00 #
0.00 0.20 0.40 0.60 0.80 1.00 1.20 1.40 1.60 1.80 2.00
a format similar to tab.1. Biasing
TIME[nS] the device at 5.7V (on the DUT
b) pin) it is possible to test the
Fig. 6: Reflectometer response of protection diodes versus clamping current: a) VDD diode, clamping effect toward the supply,
b) GND diode. while a bias voltage of -0.7V
tests of the ground clamping diode.
In order to simulate the I/O timing By changing the current in
properties of the device it is CMOS INPUT WITH clamping conditions, it is possible
possible to include in the model the PROTECTION DIODES. to collect a family of reflectometer
input static transfer characteristics responses for each protection diode.
of the device with output values Usually, a CMOS input has two Fig.6 shows an example of these
shifted to the logical state "0" and
"1". In this way the model is 0.60 #
directly interfaceable to a core 0.40 #
block able to model the timing logic
behavior of the component. Fig.4 0.20 #
shows DWN net list of the model
-0.00 #
composed by the Bin block and the
transmission line that models the -0.20 #
package contribution. The level
-0.40 #
shifter completes the model. DWN
uses a SPICE-like syntax and this -0.60 #
model can become a DWN sub
-0.80 #
circuit.
Upon the model is completed, it is -1.00 #
possible to validate it through a 0.00 0.20 0.40 0.60 0.80 1.00 1.20 1.40 1.60 1.80 2.00
TIME[nS]
simulation of the measure set-up Fig. 7: PWL fitting of a clamping diode reflectometer response: the last sample is
that has been used during the extrapolated to -1000m .
characterization (see App.A).](https://image.slidesharecdn.com/an02dws-120331083228-phpapp02/85/An02-dws-3-320.jpg)
![PB 1990-2009
10 VDD internal available) or directly from V-I
DT F measurements and used for Pvdd
Vout E1 and Pgnd (non-linear resistors)
descriptions;
t Pvdd - plot the TDR dynamic behavior
of both protection diodes in
ST F
sw1 clamping condition (with a suitable
Vout 2
1 value of clamping current4). The
sw2
Z0,T d bottom value of the response,
Bout
Vin always higher than -1000m (for
DT F Pgnd typical CMOS protection diodes
Vout the value ranges from -700m to
E2
-900m ), is the reflection
t
coefficient related to the ohmic
20 GND internal
resistance of the diode. Because
this resistance has been already
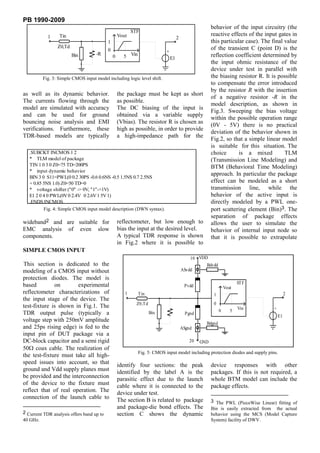
Fig. 8: CMOS output behavioral (BTM) model.
taken into account by the non-
linear resistor Pvdd and Pgnd, it is
graphs for a CMOS EPROM in DIL - extract the package and Bin
necessary to compensate this effect
package. It is interesting to observe descriptions as already explained
during the PWL extraction with the
the different behavior of the two
related utility MCS of DWV, as
diodes. R( ) shown in Fig.7.
The ground diode shows a very fast
1M The dynamic behavior of the VDD
response so that low impedance sw2 sw1 and GND path through the supply
levels are reached in about a 1K pins is easily modeled in a
nanosecond. On the contrary, the
behavioral way. This can be
Vdd diode shows a slow transient 1
accomplished by means of the two
(several nanoseconds long) before
2.5 5 S-parameter blocks Bdvdd and
it reaches low impedance levels. Vcontrol Bdgnd obtained as PWL fittings of
This slow behavior obviously has Fig. 9: Static characteristics of the two actual TDR behaviors. The two
significant impact in the clamp switches.
series adaptors ASvdd and ASgnd
action, so that, if a voltage
are used to connect the blocks in
overshoot due to reflections occurs, for the model of Fig.3;
series to the supply paths. In fact
it will be effectively clamped only
after the delay observed in the TDR 0.60 #
characterization. This kind of
situation is very common and 0.40 #
difficult to forecast. This modeling 0.20 #
1MA
approach, based on TDR
measurement, is the best way to -0.00 #
pinpoint these effects. Furthermore, 2MA
during the modeling, the user gets -0.20 #
also a lot of information, not 5MA
-0.40 #
supplied by the manufacturer,
concerning the "quality" of the -0.60 #
10MA
component he is going to use.
20MA
To complete the model shown in -0.80 #
Fig.5 the following procedure is
suggested: -1.00 #
0.00 0.20 0.40 0.60 0.80 1.00 1.20 1.40 1.60 1.80 2.00
TIME[nS]
Fig. 10: TDR responses for an ECL output versus biasing current.
- determine the static input the series adaptor connects the one-
characteristic of the DUT in normal
and clamping conditions. The data
can be extracted from datasheet (if 4 It is suggested to increase the clamping
current up to its maximum limits.](https://image.slidesharecdn.com/an02dws-120331083228-phpapp02/85/An02-dws-4-320.jpg)