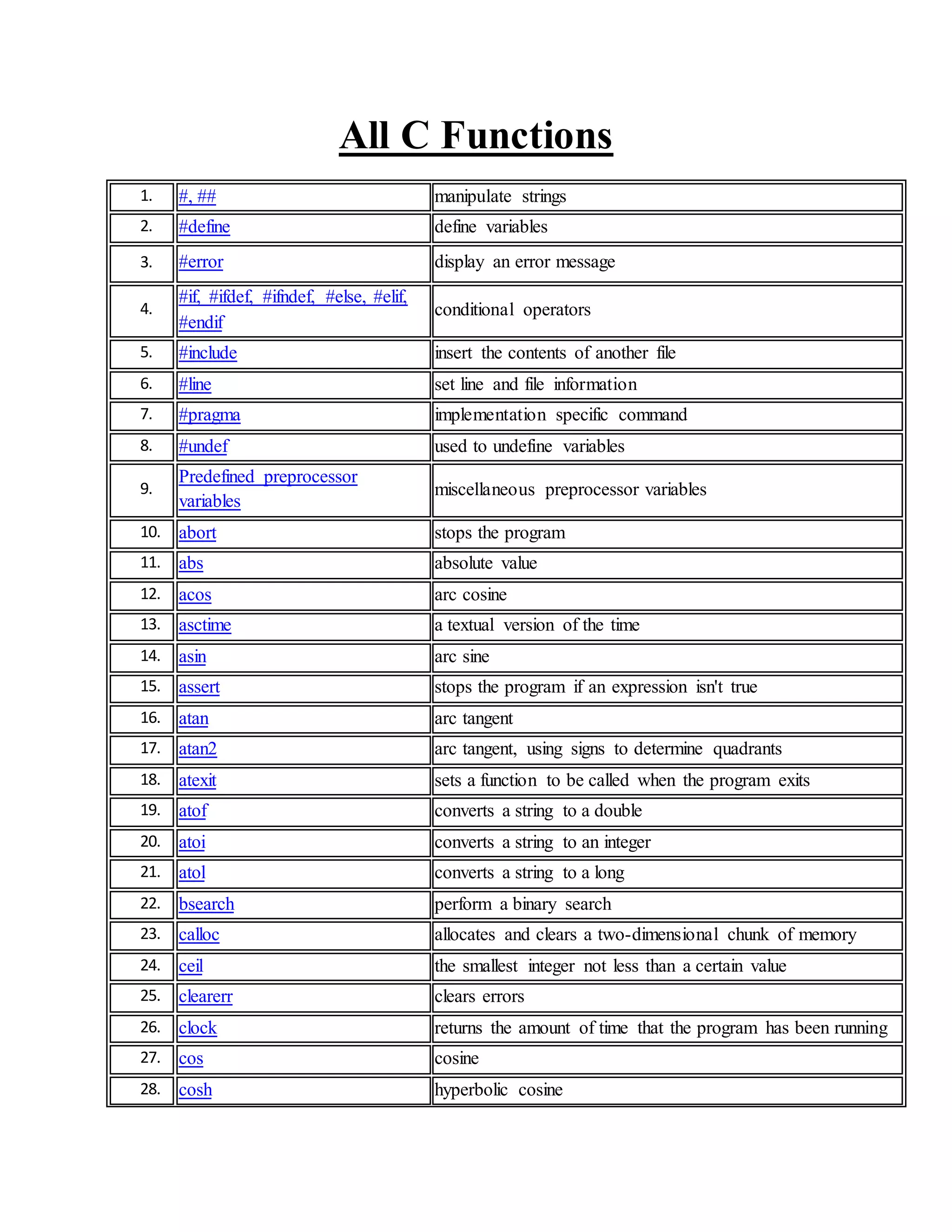
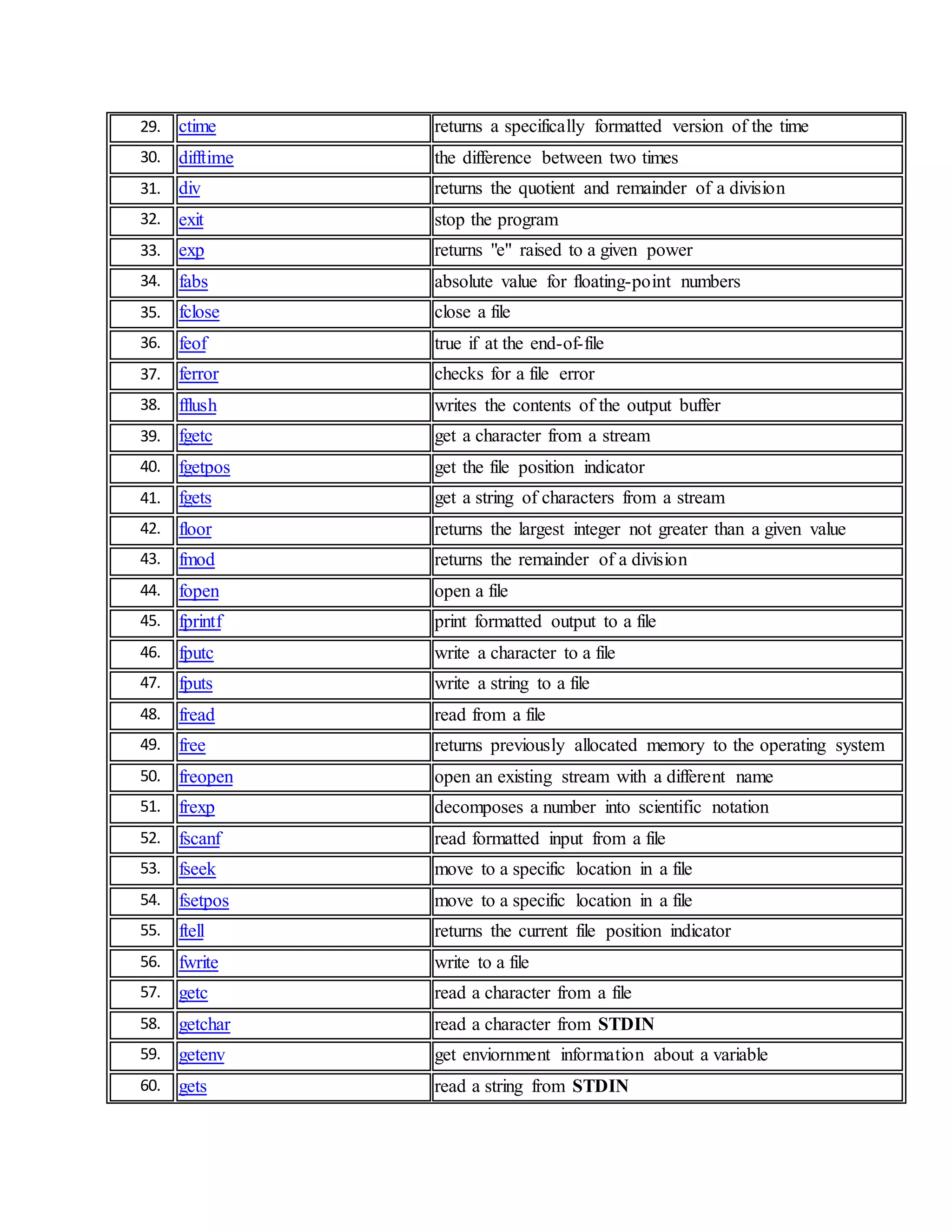
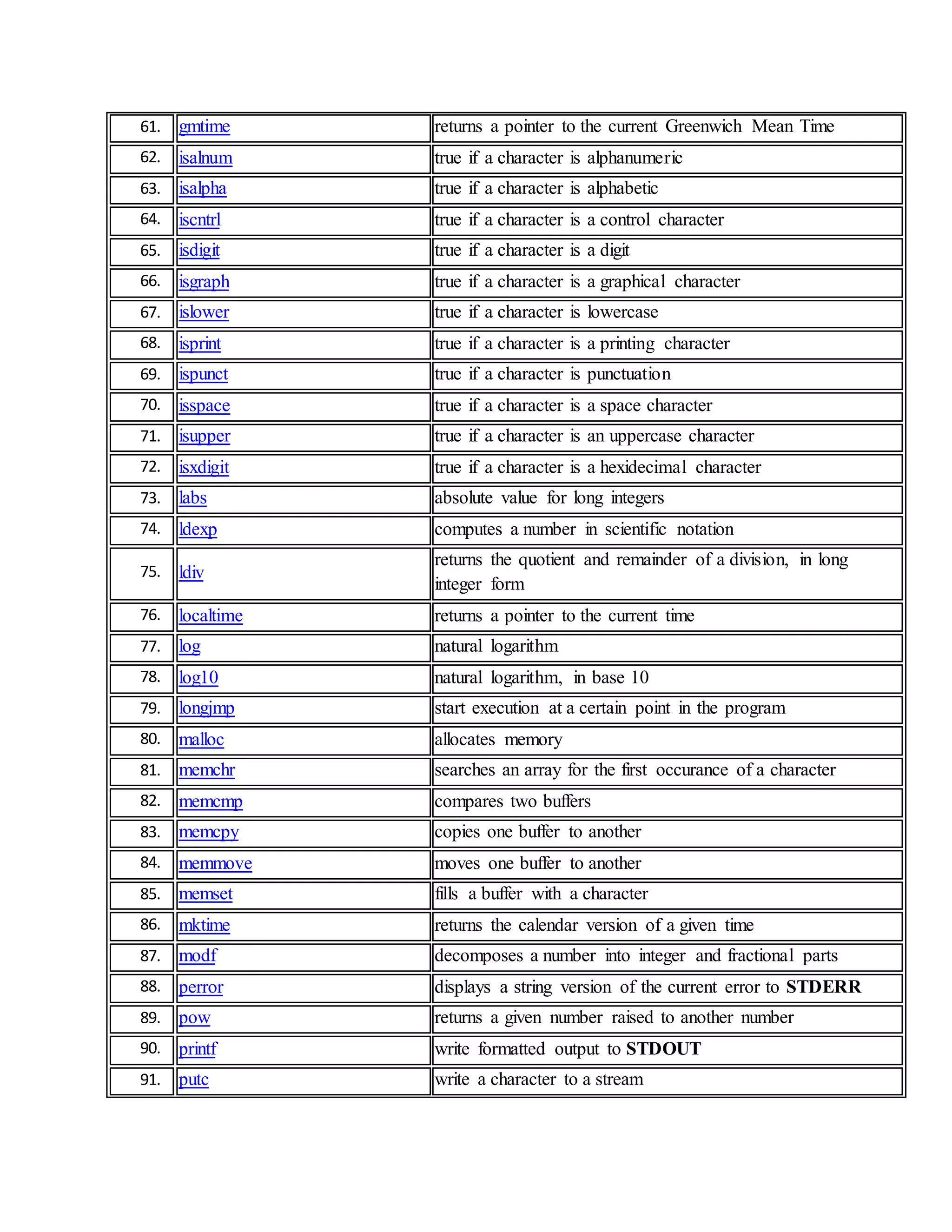
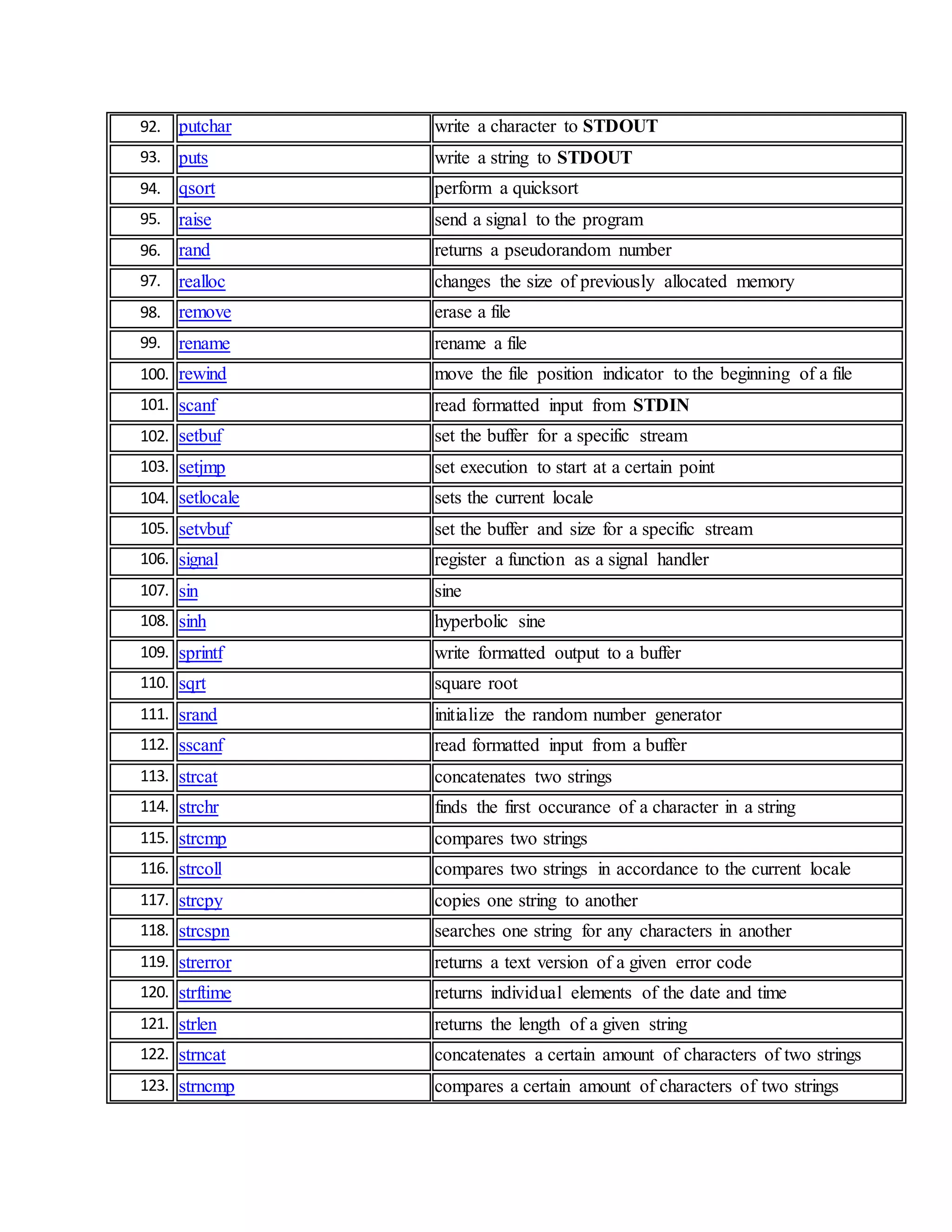
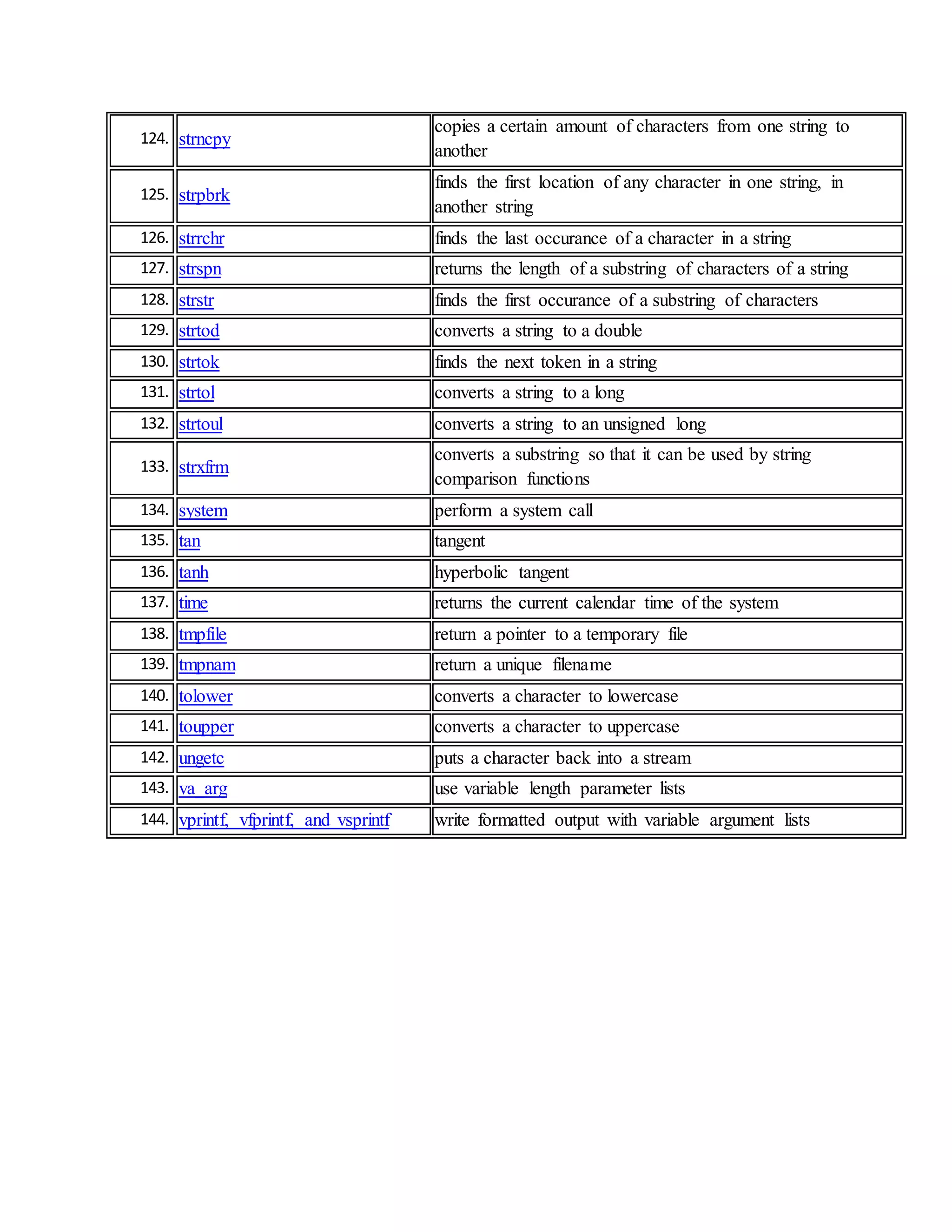
This document lists and describes 143 C functions. It groups the functions into categories such as string manipulation, preprocessor directives, mathematical functions, file handling, and more. Some key functions include printf() for formatted output, scanf() for formatted input, strcpy() to copy strings, atoi() to convert strings to integers, and exit() to terminate a program.