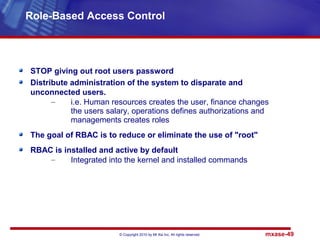
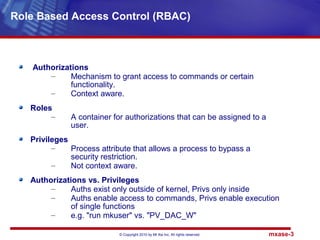
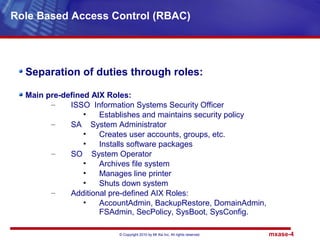
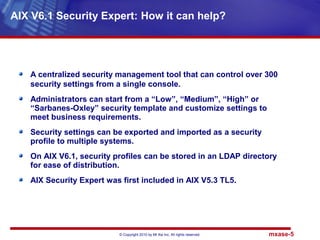
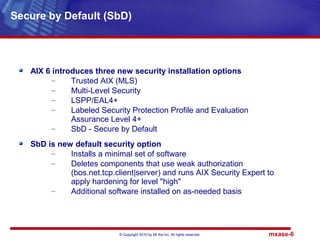
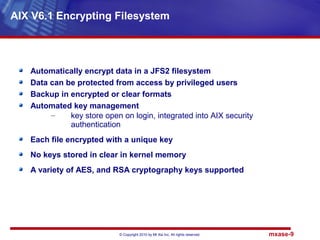
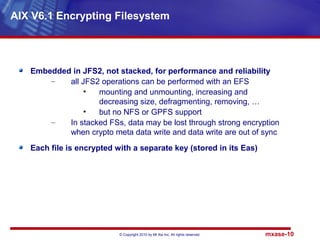
AIX 6.1 introduces several new security features including role-based access control (RBAC) which allows privileged tasks to be delegated to non-privileged users. It also includes an encrypted filesystem that encrypts data for protection and an updated security tool called AIX Security Expert for centralized security management. The document discusses these features and others such as the new secure by default installation option and systems director console.
![© Copyright 2010 by Mt Xia Inc, All rights reserved. mxase-12
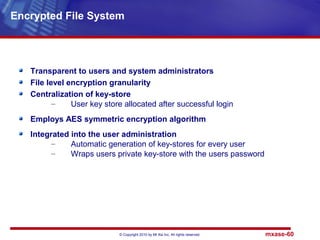
Prereqs
– CryptoLite in C (CLiC) library and kernel extension must be
installed and loaded
– Enhanced RBAC must be enabled (default in AIX6)
– EFS must be explicity enabled (can be done at any time
using 'efsenable')
New and existing FShttp://www.tecmint.com/linux-server-hardening-
security-tips/s can be encrypted
– smitty crfs -> "Enable EFS? [yes]"
– 'crfs' or 'chfs' along with "-a efs=yes"
– not to be applied on "/", /usr, /var and /opt since keystore
can't be opened during boot
– but that's OK, since EFS' main focus is on
protectinguser/application data
– encrypted files can be identified by 'ls -U'
Encrypted File System (EFS)](https://image.slidesharecdn.com/mtxiaaixpert-131007151555-phpapp02/85/AIXpert-AIX-Security-expert-12-320.jpg)