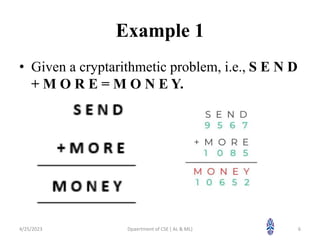
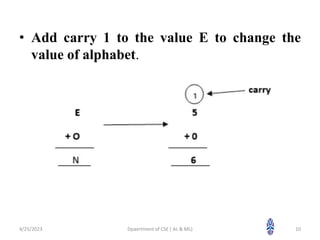
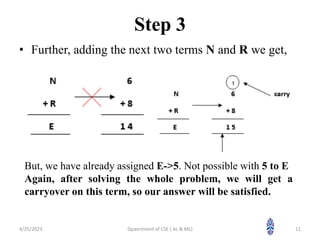
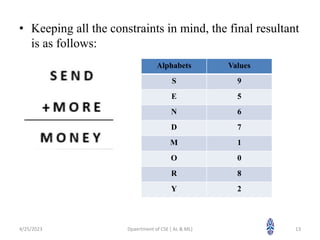
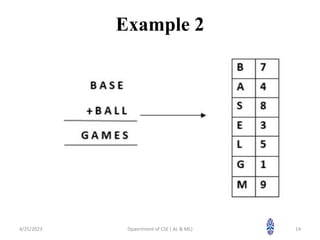
This document summarizes a session on artificial intelligence topics taught by Assistant Professor M. Gokilavani. The session covered adversarial search, constraint satisfaction problems, and propositional logic. Constraint satisfaction problems included cryptarithmetic puzzles where digits are substituted with letters while maintaining arithmetic rules. Two examples of solving cryptarithmetic puzzles were shown step-by-step by assigning digits to letters to satisfy constraints. The next session will cover backtracking for constraint satisfaction problems.