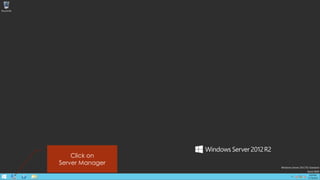
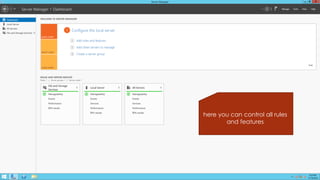
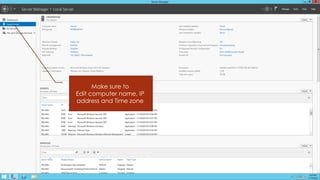
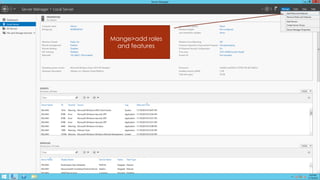
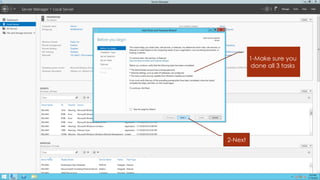
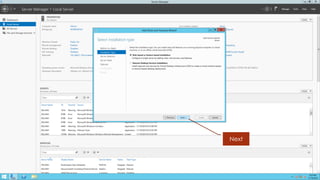
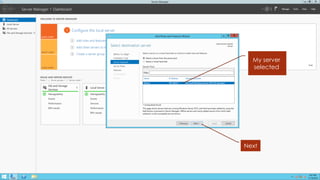
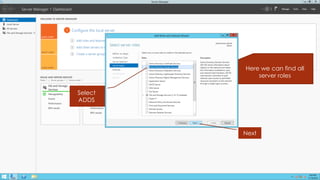
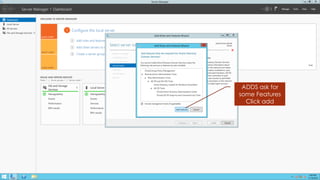
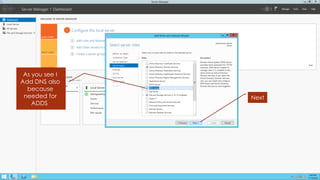
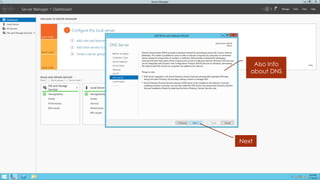
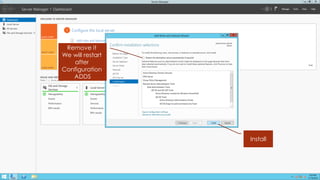
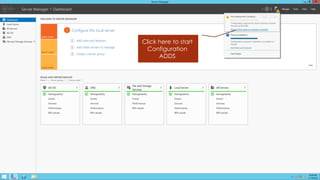
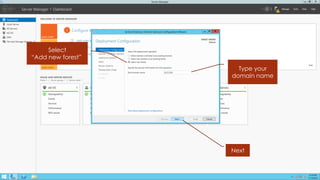
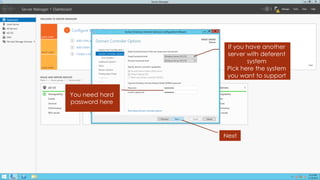
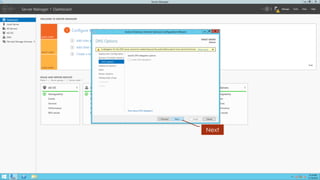
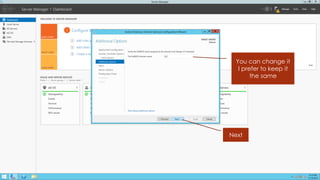
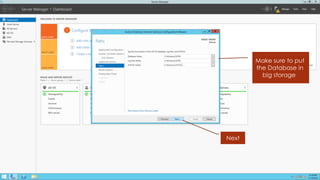
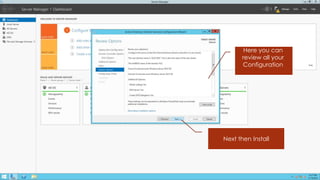
The document provides a step-by-step guide for installing and configuring Active Directory Domain Services on Windows Server 2012 R2, emphasizing secure data storage for network objects. It includes instructions on server role selection, adding DNS, and setting up the domain name and configuration settings. The author expresses hope that the guide will be helpful, despite potential omissions.