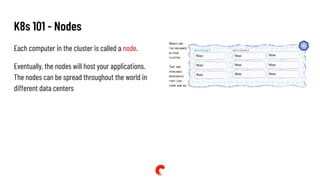
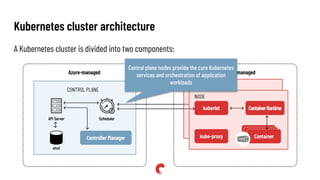
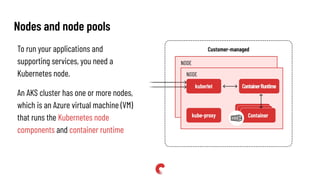
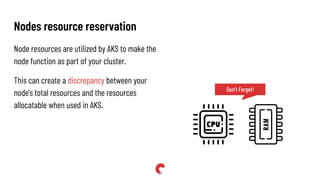
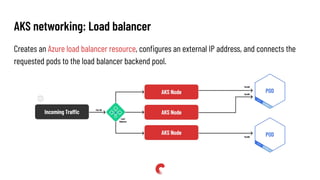
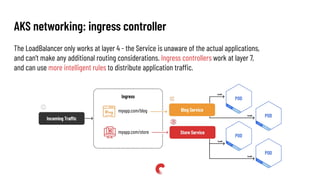
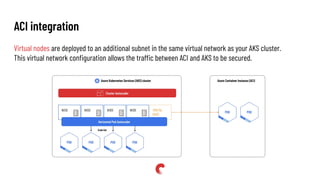
The document provides an introduction to microservices and Kubernetes (K8s), explaining concepts like service-oriented architecture, pods, deployments, and various configuration methods. It details Kubernetes' architecture, including control planes, nodes, networking options, and storage solutions, including Azure's specific implementations. Additionally, it discusses scaling options and the benefits and challenges of a microservices architecture.