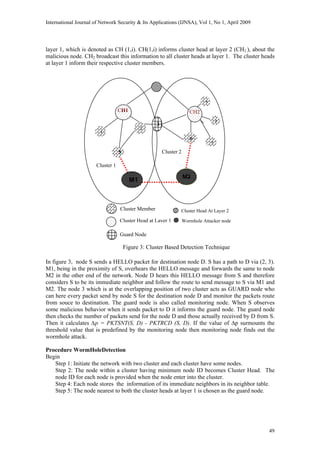
The document presents a new cluster-based algorithm aimed at detecting wormhole attacks within mobile ad-hoc networks (MANETs). It highlights the vulnerabilities of multi-hop wireless systems to these types of attacks, which exploit the lack of centralized control in ad-hoc networks. The proposed solution involves a layered structure with cluster heads and guard nodes to enhance detection and mitigation of malicious activities associated with wormhole attacks.
![International Journal of Network Security & Its Applications (IJNSA), Vol 1, No 1, April 2009
A NEW CLUSTER-BASED WORMHOLE INTRUSION
DETECTION ALGORITHM FOR MOBILE AD-HOC
NETWORKS
1
Debdutta Barman Roy, 2
Rituparna Chaki, 3
Nabendu Chaki
1
Calcutta Institute of Engineering and Management, Kolkata, India,
barmanroy.debdutta@gmail.com
2
West Bengal University of Technology, Kolkata 700064, India,
rchaki@ieee.org
3
University of Calcutta, 92 A.P.C. Road, Kolkata 700009, India
nabendu@ieee.org
ABSTRACT
In multi-hop wireless systems, the need for cooperation among nodes to relay each other's packets
exposes them to a wide range of security attacks. A particularly devastating attack is the wormhole
attack, where a malicious node records control traffic at one location and tunnels it to another
compromised node, possibly far away, which replays it locally. Routing security in ad hoc networks is
often equated with strong and feasible node authentication and lightweight cryptography. Unfortunately,
the wormhole attack can hardly be defeated by crypto graphical measures, as wormhole attackers do not
create separate packets. They simply replay packets already existing on the network, which pass the
cryptographic checks. Existing works on wormhole detection have often focused on detection using
specialized hardware, such as directional antennas, etc. In this paper, we present a cluster based
counter-measure for the wormhole attack, that alleviates these drawbacks and efficiently mitigates the
wormhole attack in MANET. Simulation results on MATLab exhibit the effectiveness of the proposed
algorithm in detecting wormhole attacks.
KEY WORDS
MANET, Wormhole, Cluster, Guard Node, routing
1. INTRODUCTION
Mobile wireless ad hoc networks are fundamentally different from wired networks, as they use
wireless medium to communicate, do not rely on fixed infrastructure, and can arrange them into
a network quickly and efficiently. In a Mobile Ad Hoc Network (MANET), each node serves as
a router for other nodes, which allows data to travel, utilizing multi-hop network paths, beyond
the line of sight without relying on wired infrastructure. Security in such networks, however, is
a great concern [1, 2, 7, 8]. The open nature of the wireless medium makes it easy for outsiders
to listen to network traffic or interfere with it. Lack of centralized control authority makes
deployment of traditional centralized security mechanisms difficult, if not impossible. Lack of
clear network entry points also makes it difficult to implement perimeter-based defense
mechanisms such as firewalls. Finally, in a MANET nodes might be battery-powered and might
have very limited resources, which may make the use of heavy-weight security solutions
undesirable [2, 3, 7, 8, 13].
A wormhole attack is a particularly severe attack on MANET routing where two attackers,
connected by a high-speed off-channel link, are strategically placed at different ends of a
network, as shown in figure 1. These attackers then record the wireless data they overhear,
forward it to each other, and replay the packets at the other end of the network. Replaying valid
44](https://image.slidesharecdn.com/0409s5-180419074619/75/A-NEW-CLUSTER-BASED-WORMHOLE-INTRUSION-DETECTION-ALGORITHM-FOR-MOBILE-AD-HOC-NETWORKS-1-2048.jpg)
![International Journal of Network Security & Its Applications (IJNSA), Vol 1, No 1, April 2009
45
network messages at improper places, wormhole attackers can make far apart nodes believe they
are immediate neighbors, and force all communications between affected nodes to go through
them.
S E
High Speed off Channel Link
D
C
F
B
HG
M1 M2
Tunnel
Figure 1: MANET with a wormhole attack
In general, ad hoc routing protocols fall into two categories: proactive routing protocol that
relies on periodic transmission of routing packets updates, and on-demand routing protocols that
search for routes only when necessary. A wormhole attack is equally worse a threat for both
proactive and on-demand routing protocols [3, 7, 8, 9].
When a proactive routing protocol [10] is used, ad hoc network nodes send periodic HELLO
messages to each other indicating their participation in the network. In Figure 2, when node S
sends a HELLO message, intruder M1 forwards it to the other end of the network, and node H
hears this HELLO message. Since H can hear a HELLO message from S, it assumes itself and
node S to be direct neighbors. Thus, if H wants to forward anything to S, it may do so
unknowingly through the wormhole link. This effectively allows the wormhole attackers full
control of the communication link.
In case of on-demand routing protocols, such as AODV [11], when a node wants to
communicate with another node, it floods its neighbors with requests, trying to determine a path
to the destination. In figure 2, if S wants to communicate with H, it sends out a request. A
wormhole, once again, forwards such request without change to the other end of the network,
may be directly to node H. A request also travels along the network in a proper way, so H is
lead to believe it has a possible route to node S thru the wormhole attacker nodes. If this route is
selected by the route discovery protocol, once again wormhole attackers get full control of the
traffic between S and H. Once the wormhole attackers have control of a link, attackers can drop
the packets to be forwarded by their link. They can drop all packets, a random portion of
packets, or specifically targeted packets1. Attackers can also forward packets out of order or
‘switch’ their link on and off [3].
In this paper, we have proposed an algorithm where intrusion detection has been done in a
cluster based approach to detect the wormhole attacks. The AODV routing protocol is used as
the underlying network topology. A two layer approach is used for detecting whether a node is
acting as a wormhole.
2. RELATED WORKS
Routing security in ad hoc networks is often equated with strong and feasible node
authentication and lightweight cryptography. A wide variety of secure extensions to existing
routing protocols have been proposed over the years. However, the majority of these protocols
are focused on using crypto graphical solutions to prevent unauthorized nodes from creating
seemingly valid packets [8]. Unfortunately, the wormhole attack can not be defeated by crypto](https://image.slidesharecdn.com/0409s5-180419074619/85/A-NEW-CLUSTER-BASED-WORMHOLE-INTRUSION-DETECTION-ALGORITHM-FOR-MOBILE-AD-HOC-NETWORKS-2-320.jpg)
![International Journal of Network Security & Its Applications (IJNSA), Vol 1, No 1, April 2009
graphical measures, as wormhole attackers do not create separate packets - they simply replay
packets already existing on the network, which pass all cryptographic checks. Perhaps the most
commonly cited wormhole prevention mechanism is ‘packet leashes’ by Hu et al [13]. Hu
proposed to add secure ‘leash’ containing timing and/or Global Positioning System (GPS)
information to each packet on a hop-by-hop basis. Based on the information contained in a
packet leash, a node receiving the packet would be able to determine whether the packet has
traveled a distance larger than physically possible.
Hu proposed two different kinds of leashes: geographical leashes and temporal leashes.
Geographic leashes require each node to have access to up-to-date GPS information, and rely on
loose (in the order of ms) clock synchronization. When geographical leashes are used, a node
sending a packet appends to it the time the packet is sent ts and its location ps. A receiving node
uses its own location pr and the time it receives a packet tr to determine the distance the packet
could have traveled. Keeping in mind maximum possible node velocity v, clock synchronization
error ∆, and possible GPS distance error ∆, the distance between the sender and the receiver dsr
is upper-bounded by:
dsr <||ps - pr||+2v(tr - ts+∆)+∆
Geographical leashes should work fine when GPS coordinates are practical and available.
However, modern GPS technology has significant limitations that should not be overlooked.
While the price of GPS devices is going down, it remains substantial. Besides, GPS is somewhat
of a nuisance for personal laptops. Also, while, as Hu [13, 3] specifies, it is possible to achieve
GPS precision of about 3m with state-of-the-art GPS devices, consumer-level devices do not get
(and do not require) this level of resolution. Finally, GPS systems are not versatile, as GPS
devices do not function well inside buildings, under water, in the presence of strong magnetic
radiation, etc. As opposed to geographical leashes, temporal leashes require much tighter clock
synchronization (in the order of nanoseconds), but do not rely on GPS information. When
temporal leashes are used, the sending node specifies the time it sends a packet ts in a packet
leash, and the receiving node uses its own packet reception time tr for verification. In a slightly
different version of temporal packet leashes, the sending node calculates an expiration time te
after which a packet should not be accepted, and puts that information in the leash. This is to
prevent a packet from traveling farther than distance L
te = ts+L/C-∆, where, C is the speed of light and ∆ is the maximum clock
synchronization error.
Another set of wormhole prevention techniques, somewhat similar to temporal packet leashes
[10], is based on the time of flight of individual packets. Wormhole attacks are possible because
an attacker can make two far-apart nodes see themselves as neighbors. One possible way to
prevent wormholes, as used by Capkun et al [14], Hu et al [15], Hong et al [4], and Korkmaz
[5], is to measure round-trip travel time of a message and its acknowledgement, estimate the
distance between the nodes based on this travel time, and determine whether the calculated
distance is within the maximum possible communication range. The basis of all these
approaches is the following. The Round Trip Travel Time (RTT) δ of a message in a wireless
medium can, theoretically, be related to the distance d between nodes, assuming that the
wireless signal travels with a speed of light c:
d =(δc)/2 and δ=2d/c
The neighbor status of nodes is verified if d is within the radio transmission range R for R > d
(d within transmission range): R >δc/2 and δ<2R/c. In essence, the use of RTT eliminates the
need for tight clock synchronization required in temporal leashes: a node only uses its own
clock to measure time. However, this approach, while accounting for message propagation,
46](https://image.slidesharecdn.com/0409s5-180419074619/85/A-NEW-CLUSTER-BASED-WORMHOLE-INTRUSION-DETECTION-ALGORITHM-FOR-MOBILE-AD-HOC-NETWORKS-3-320.jpg)
![International Journal of Network Security & Its Applications (IJNSA), Vol 1, No 1, April 2009
completely ignores message processing time. When a message is sent by one node and is
acknowledged by another, the time it takes for a node to process a message and to reply to it is
generally non-negligible, particularly in the context of bounding short distances using signals
whose speed is similar to that of light in vacuum. After all, it takes the light less than 0.2
seconds to circle the entire Earth around the equator. Outstanding clock precision and
practically nonexistent errors are required to bind distances on the order of hundreds of meters.
Several researchers worked on the wormhole attack problem by treating a wormhole as a
misbehaving link. In such approaches, a wormhole attack is not specifically identified. Rather,
the wormhole’s destructive behavior is mitigated. Baruch [6] and Chigan [12] use link rating
schemes to prevent blackhole and wormhole attacks. They both rely on authenticated
acknowledgements of data packets to rate links: if a link is dropping packets, the
acknowledgements do not get through; link is rated low and avoided in the future. These
approaches are geared towards discovery and prevention of only one kind of wormhole
behavior: packet loss. Wormholes can do much more than that: they can send packets out of
order, confuse location-based schemes, or simply aggregate packets for traffic analysis. Even
the distortion of topology information that a wormhole introduce can be a significant problem in
particular networks. The real problem with the wormholes is that unauthorized nodes (wormhole
attackers) are able to transmit valid network messages. Techniques based on links’ performance
may be suitable in certain cases, but they do not fully address the wormhole problem.
In one of our earlier works, [1] a new collaborative algorithm called IDSX had been proposed.
The proposed IDSX offers an extended architecture and is compatible with heterogeneous IDS
already deployed in the participating nodes. In the high level of the architecture of the IDSX
mechanism, the cluster heads act as the links across different clusters. The cluster heads are
IDSX enabled and hence, can utilize alerts to generate the alarms. Alerts represent the potential
security breaches as identified by local IDS active nodes. The IDSX nodes are authorized to
take the final decision of discarding a node after aggregating and correlating the alerts that has
been generated over a period of time.
3. PROPOSED METHODOLOGY
Our objective is to find out the malicious node that performs the wormhole attack in network.
We have assumed that the MANET consists of clusters of nodes. The assumptions regarding the
organization of the MANET are listed in section 3.1.
3.1 Assumptions
The following assumptions are taken in order to design the proposed algorithm.
1. A node interacts with its 1-hop neighbors directly and with other nodes via intermediate
nodes using multi-hop packet forwarding.
2. Every node has a unique id in the network, which is assigned to a new node collaboratively
by existing nodes.
3. The entire network is geographically divided into a few disjoint or overlapping clusters
4. The network is considered to be layered.
5. A cluster head at the inner layer is represented as CH (1,i), where 1 signifies inner Layer, and
i stands for the cluster number
6. Each cluster is monitored by only one cluster head (monitoring node).
7. The cluster membership is restricted up to 2 hops.
3.2 Cluster formation
In this paper, we have proposed an algorithm where intrusion detection has been done in a
cluster based manner to take care of the wormhole attacks. The AODV routing protocol is used
47](https://image.slidesharecdn.com/0409s5-180419074619/85/A-NEW-CLUSTER-BASED-WORMHOLE-INTRUSION-DETECTION-ALGORITHM-FOR-MOBILE-AD-HOC-NETWORKS-4-320.jpg)


![International Journal of Network Security & Its Applications (IJNSA), Vol 1, No 1, April 2009
In figure 4, we observe that in presence of a single guard node, the number of packet drop and
the number of packet send are nearly the same. So, there is a 50 % improvement in
performance, with the presence of a single guard node.
In figure 5, the number of packet send and the number of packet drops vary due to the presence
of 2 guard nodes. The performance of the network improves further. As evident from figures 6
and 7, it is observed that as the number of guard node increases to 3 and 4 respectively, the
number of packets dropped minimizes. The performance of the network increases accordingly.
Thus, the increase in the number of guard nodes steadily increases the probability of detection
of wormhole attack.
5. CONCLUSION
In this work, a new cluster based wormhole detection method has been proposed. In multi-hop
wireless systems, the need for cooperation among nodes to relay each other's packets exposes
them to a wide range of security threats including the wormhole attack. A number of recent
works have been studied before proposing this new methodology. The proposed solution unlike
some of its predecessors does not require any specialized hardware like directional antennas, etc
for detecting the attackers. or extremely accurate clocks, etc. The simulation using 30 nodes
and variable number of guard nodes prove the effectiveness of the proposed algorithm.
Currently more studies are being done to analyze the performance of the proposed algorithm in
presence of multiple attacker nodes.
6. REFERENCE
[1] Chaki, Rituparna; Chaki, Nabendu; "IDSX: A Cluster Based Collaborative Intrusion Detection
Algorithm for Mobile Ad-Hoc Network"; Proc. of the 6th Int’l Conf. on Computer Information
Systems and Industrial Management Applications (CISIM '07); pp. 179 - 184, June 2007; ISBN:
0-7695-2894-5
[2] Marko Jahnke, Jens Toelle, Alexander Finkenbrink,. Alexander Wenzel, et.al; “Methodologies
and Frameworks for Testing IDS in Adhoc Networks”; Proceedings of the 3rd ACM workshop
on QoS and security for wireless and mobile networks; Chania, Crete Island, Greece, Pages: 113
- 122, 2007
[3] Y.-C. Hu, A. Perrig, D. B. Johnson; “Wormhole Attacks in Wireless Networks”; IEEE Journal
on Selected Areas of Communications, vol. 24, numb. 2, pp. 370-380, 2006
[4] F. Hong, L. Hong, C. Fu; “Secure OLSR”; 19th International Conference on Advanced
Information Networking and Applications, AINA 2005, Vol. 1, 25-30, pp. 713-718, March 2005
[5] Korkmaz T.; “Verifying Physical Presence of Neighbours against Replay-based Attacks in
Wireless Ad Hoc Networks”; Proc. International Conference on Information Technology:
Coding and Computing 2005, ITCC 2005, pp. 704-709, 2005
[6] A. Baruch, R. Curmola, C. Nita-Rotaru, D. Holmer, H. Rubens; “On the Survivability of Routing
Protocols in Ad Hoc Wireless Networks”; Converence on Security and Privacy for Emerging
Areas in Communications, SecureComm 2005
[7] Yang, H. and Luo, H. and Ye, F. and Lu, S. and Zhang, U.; “Security in Mobile Ad Hoc
Networks: Challenges and Solutions”; Wireless Communications, IEEE, vol. 11, num. 1, pp. 38-
47, 2004
[8] Y.-C. Hu, A. Perrig; “A Survey of Secure Wireless Ad Hoc Routing”; Security and Privacy
Magazine, IEEE, vol. 2, issue 3, pp. 28-39, May 2004.
[9] A. Mishra, K. Nadkarni, A. Patcha; “Intrusion Detection in Wireless Ad Hoc Networks”; IEEE
Wireless Communications, Vol 11, issue 1, pg. 48-60, February 2004.
51](https://image.slidesharecdn.com/0409s5-180419074619/85/A-NEW-CLUSTER-BASED-WORMHOLE-INTRUSION-DETECTION-ALGORITHM-FOR-MOBILE-AD-HOC-NETWORKS-8-320.jpg)
![International Journal of Network Security & Its Applications (IJNSA), Vol 1, No 1, April 2009
[10] T. Clausen, P. Jacquet, A. Laouiti, P. Muhlethaler, A. Qayyum, L. Viennot; “Optimized Link
State Routing Protocol”; Proceedings of IEEE INMIC, Pakistan 2001.
[11] Charles E. Perkins and Elizabeth M. Royer. "Ad hoc On-Demand Distance Vector Routing."
Proceedings of the 2nd IEEE Workshop on Mobile Computing Systems and Applications, New
Orleans, LA, pp. 90-100, 1999.
[12]. C. Chigan, R. Bandaru; “Secure Node Misbehaviors in Mobile Ad Hoc Networks”; Proc. of
IEEE Conf. on Vehicular Technology Conference, VTC 2004, Vol. 7, pp. 4730-4734, 2004
[13] Y.-C. Hu, A. Perrig, D. B. Johnson; “Packet leashes: a defense against wormhole attacks in
wireless networks”; INFOCOM 2003, Twenty-Second Annual Joint Conference of the IEEE
Computer and Communication Societies, Vol. 3, pp. 1976-1986, 2003
[14] S. Capkun, L. Buttyan, J.-P. Hubaux; “SECTOR: Secure Tracking of Node Encounters in Multi-
Hop Wireless Networks”; Proc. of the 1st ACM Workshop on Security of Ad Hoc and Sensor
Networks; 2003
[15] Y-C Hu, A. Perrig, D. Johnson; “Rushing Attacks and Defense in Wireless Ad Hoc Network
Routing Protocols”; Proc. of WISE 2003, September 19, San Diego, California, USA, 2003
Authors
Debdutta Pal received her M. Tech. Degree in Software Engineering from the West
Bengal University of Technology in 2007. She is at present working as a Lecturer at
Calcutta Institute of Engineering and Management, Kolkata, West Bengal. Her
research interests include the field of Computer Networking, and Wireless Mobile
Ad hoc Network.
Rituparna Chaki is a Reader (Associate Professor) in the Department of Computer
Science & Engineering, West Bengal University of Technology, Kolkata, India
since 2005. She received her Ph.D. in 2002 from Jadavpur University, India. The
primary area of research interest for Dr. Chaki is Wireless Mobile Ad hoc
Networks. She has also served as a Systems Manager for Joint Plant Committee,
Government of India for several years before she switched to Academia. Dr. Chaki
also serves as a visiting faculty member in other leading Universities including
Jadavpur University. Dr. Chaki has about 20 referred international publications to
her credit.
Nabendu Chaki is a faculty member in the Department of Computer Science &
Engineering, University of Calcutta, Kolkata, India. He received his Ph.D. in
2000 from Jadavpur University, India. His areas of research interests include
distributed computing and software engineering. Dr. Chaki has also served as a
Research Faculty member in the Ph.D. program in Software Engineering in U.S.
Naval Postgraduate School, Monterey, CA during 2001-2002. He is a visiting
faculty member for many Universities including the University of Ca’Foscari,
Venice, Italy. Dr. Chaki has published more than 50 referred research papers and a
couple of text books. Besides being in the editorial board for 4 Journals, Dr. Chaki
has also served in the committees of several international conferences.
52](https://image.slidesharecdn.com/0409s5-180419074619/85/A-NEW-CLUSTER-BASED-WORMHOLE-INTRUSION-DETECTION-ALGORITHM-FOR-MOBILE-AD-HOC-NETWORKS-9-320.jpg)