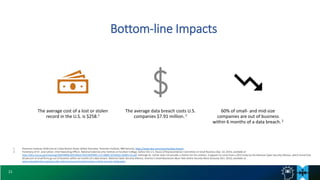
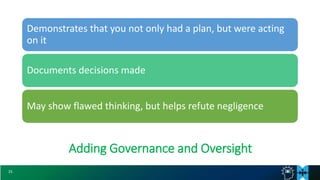
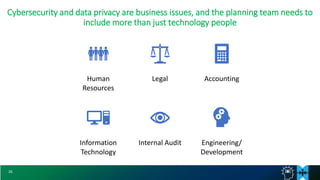
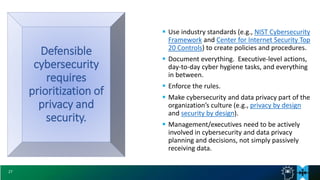
The document discusses defensible cybersecurity strategies and practices. It notes recent large data breaches and increasing regulatory focus on data privacy and cybersecurity. It emphasizes the importance of having a comprehensive cybersecurity plan that uses industry standards and best practices, and of demonstrating executive involvement, in order to defend against potential legal liability from cyber incidents. It provides examples of business risks from cybersecurity issues and costs of data breaches. It recommends prioritizing privacy and security using standards like NIST CSF, documenting policies and procedures, and making cybersecurity part of an organization's culture.