This document provides a comprehensive introduction to Apache Cassandra, a distributed NoSQL database known for its scalability and fault tolerance. It covers key topics such as its architecture, data model, features, replication capabilities, security, and tools for managing Cassandra. Additionally, it lists notable organizations that utilize Cassandra and provides resources for further learning.

![Data Model
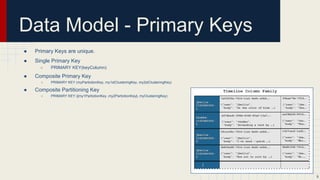
● [Keyspace][ColumnFamily][Key][Column]
● A keyspace is akin to a database in RDBMS
● The keyspace is a row-oriented, column structure
● A column family is similar to an RDBMS table
○ More flexible/dynamic
● A row in a column family is indexed by its key (Primary Key).
○ Cassandra supports up to 2 billion columns per (physical) row.
● Sample code to create keyspace and column family:
○ CREATE KEYSPACE logs WITH replication = {'class': 'SimpleStrategy',
'replication_factor': 1} ;
○ CREATE TABLE logs.samples (
node_id text,
metric text,
collection_ts timestamp,
value bigint,
PRIMARY KEY ((node_id, metric), collection_ts)
) WITH CLUSTERING ORDER BY (collection_ts DESC);
8](https://image.slidesharecdn.com/wo7vvppprls31wpirbww-signature-7a6e840e850305205c4ce6b026fff178cbba0f46c15bc2a04dec02fcccac02a7-poli-150203095516-conversion-gate02/85/An-Introduction-to-Apache-Cassandra-8-320.jpg)




![Nodetool
● A command line interface for managing a cluster.
○ CASSANDRA_PATH/bin/nodetool
● Useful commands:
○ nodetool info - Display node info (uptime, load and etc.).
○ nodetool status [keyspace] - Display cluster info (state, load and etc.).
○ nodetool cfstats [keyspace] - Display statistics of column families.
○ nodetool tpstats - Display usage statistics of thread pool.
○ nodetool netstats - Display network information.
○ nodetool repair - Repair one or more column families.
○ nodetool rebuild - Rebuild data by streaming from other nodes (similarly to bootstrap).
○ nodetool drain - Flush Memtables to SSTables on disk and stop accepting writes. Useful before a restart to make startup
quick.
○ nodetool flush [keyspace [columnfamily]] - Flushes one or more column families from the memtable.
○ nodetool cfhistograms keyspace columnfamily - Display statistic histograms for a given column family.
○ nodetool proxyhistograms - Display statistic histograms for network operations.
○ nodetool help - Display help information!
29](https://image.slidesharecdn.com/wo7vvppprls31wpirbww-signature-7a6e840e850305205c4ce6b026fff178cbba0f46c15bc2a04dec02fcccac02a7-poli-150203095516-conversion-gate02/85/An-Introduction-to-Apache-Cassandra-29-320.jpg)