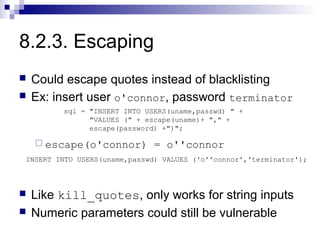
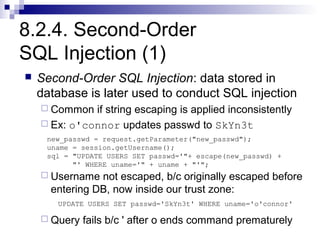
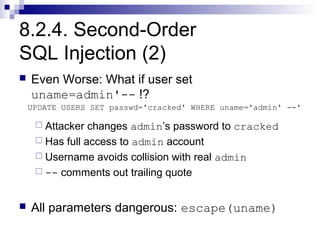
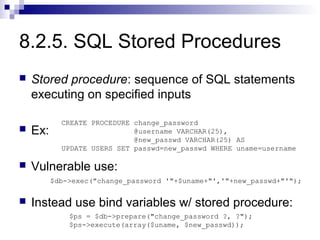
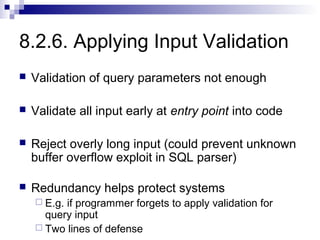
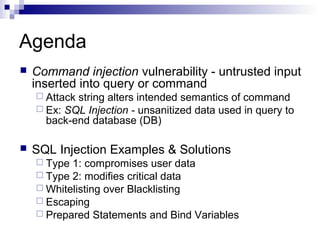
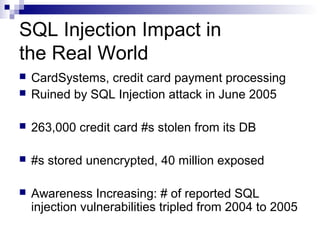
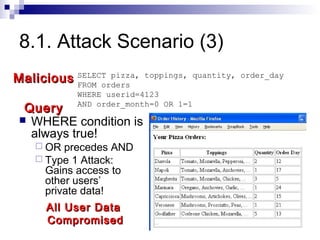
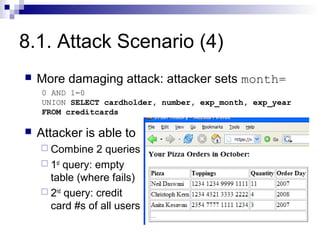
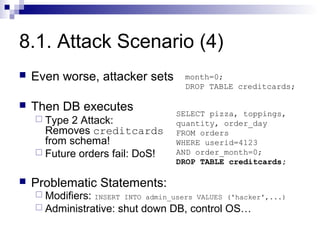
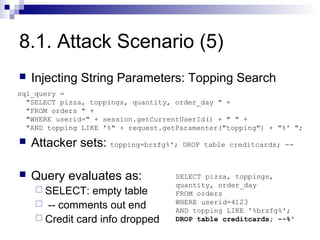
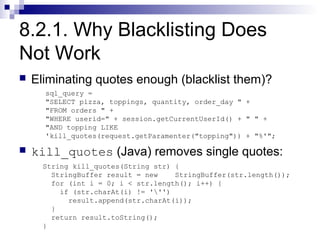
SQL injection attacks pose a major security threat by allowing attackers to alter intended database queries or commands through injection of malicious SQL code. Effective defenses include whitelisting input, escaping special characters, and using prepared statements with bind variables to separate data from SQL commands. These techniques help prevent attacks that could compromise user data, modify critical database information, or grant unauthorized access to attackers.

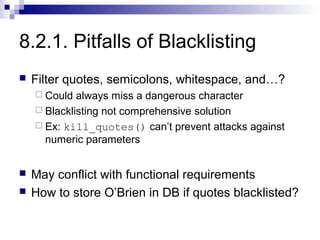
![8.2.2. Whitelisting-Based Input
Validation
Whitelisting – only allow input within well-defined
set of safe values
setimplicitly defined through regular expressions
RegExp – pattern to match strings against
Ex: month parameter: non-negative integer
RegExp: ^[0-9]*$ - 0 or more digits, safe subset
The ^, $ match beginning and end of string
[0-9] matches a digit, * specifies 0 or more](https://image.slidesharecdn.com/8-sqlinjection-121017024705-phpapp02/85/8-sql-injection-14-320.jpg)