This document summarizes a presentation on new SQL injection obfuscation techniques. It provides details on the speaker, Nick Galbreath, and the event: DEFCON 20 in Las Vegas on July 27, 2012. It then discusses libinjection, a tool for detecting SQLi, and analyses it on 32,000 SQLi attacks to find syntax not previously seen. The rest of the document explores unusual and underexploited SQL syntax related to numbers, comments, strings, and data types that could be useful for fuzzing, validation, and obfuscation.
![Regexp Based WAF
(?:)s*whens*d+s*then)|(?:"s*(?:#|--|{))|(?:/*!s?d+)|(?:ch(?:a)?rs*(s*d)|(?:(?:(n?and|x?or|not)s+||||&&)s*w+()
(?:[s()]cases*()|(?:)s*likes*()|(?:havings*[^s]+s*[^ws])|(?:ifs?([dw]s*[=<>~])
(?:"s*ors*"?d)|(?:x(?:23|27|3d))|(?:^.?"$)|(?:(?:^["]*(?:[d"]+|[^"]+"))+s*(?:n?and|x?or|not||||&&)s*[w"[+&!@(),.-])|(?:[^ws]w+s*[|-]
s*"s*w)|(?:@w+s+(and|or)s*["d]+)|(?:@[w-]+s(and|or)s*[^ws])|(?:[^ws:]s*dW+[^ws]s*".)|(?:Winformation_schema|table_nameW)
(?:"s**.+(?:or|id)W*"d)|(?:^")|(?:^[ws"-]+(?<=ands)(?<=ors)(?<=xors)(?<=nands)(?<=nots)(?<=||)(?<=&&)w+()|(?:"[sd]*[^ws]+W*d
W*.*["d])|(?:"s*[^ws?]+s*[^ws]+s*")|(?:"s*[^ws]+s*[Wd].*(?:#|--))|(?:".**s*d)|(?:"s*ors[^d]+[w-]+.*d)|(?:[()*<>%+-][w-]+[^ws]
+"[^,])
(?:d"s+"s+d)|(?:^admins*"|(/*)+"+s?(?:--|#|/*|{)?)|(?:"s*or[ws-]+s*[+<>=(),-]s*[d"])|(?:"s*[^ws]?=s*")|(?:"W*[+=]+W*")|(?:"s*[!=|]
[ds!=+-]+.*["(].*$)|(?:"s*[!=|][ds!=]+.*d+$)|(?:"s*likeW+[w"(])|(?:siss*0W)|(?:wheres[sw.,-]+s=)|(?:"[<>~]+")
(?:unions*(?:all|distinct|[(!@]*)?s*[([]*s*select)|(?:w+s+likes+")|(?:likes*"%)|(?:"s*likeW*["d])|(?:"s*(?:n?and|x?or|not ||||&&)s+[s
w]+=s*w+s*having)|(?:"s**s*w+W+")|(?:"s*[^?ws=.,;)(]+s*[(@"]*s*w+W+w)|(?:selects*[[]()sw.,"-]+from)|(?:find_in_sets*()
(?:ins*(+s*select)|(?:(?:n?and|x?or|not ||||&&)s+[sw+]+(?:regexps*(|soundss+likes*"|[=d]+x))|("s*ds*(?:--|#))|(?:"[%&<>^=]+ds*(=|
or))|(?:"W+[w+-]+s*=s*dW+")|(?:"s*iss*d.+"?w)|(?:"|?[w-]{3,}[^ws.,]+")|(?:"s*iss*[d.]+s*W.*")
(?:[dW]s+ass*["w]+s*from)|(?:^[Wd]+s*(?:union|select|create|rename|truncate|load|alter|delete|update|insert|desc))|(?:(?:select|create|rename|
truncate|load|alter|delete|update|insert|desc)s+(?:(?:group_)concat|char|load_file)s?(?)|(?:ends*);)|("s+regexpW)|(?:[s(]load_files*()
(?:@.+=s*(s*select)|(?:d+s*ors*d+s*[-+])|(?:/w+;?s+(?:having|and|or|select)W)|(?:ds+groups+by.+()|(?:(?:;|#|--)s*(?:drop|alter))|(?:
(?:;|#|--)s*(?:update|insert)s*w{2,})|(?:[^w]SETs*@w+)|(?:(?:n?and|x?or|not ||||&&)[s(]+w+[s)]*[!=+]+[sd]*["=()])
(?:"s+ands*=W)|(?:(s*selects*w+s*()|(?:*/from)|(?:+s*d+s*+s*@)|(?:w"s*(?:[-+=|@]+s*)+[d(])|(?:coalesces*(|@@w+s*[^ws])|(?:W!
+"w)|(?:";s*(?:if|while|begin))|(?:"[sd]+=s*d)|(?:orders+bys+ifw*s*()|(?:[s(]+cased*W.+[tw]hen[s(])
(?:(select|;)s+(?:benchmark|if|sleep)s*?(s*(?s*w+)
(?:creates+functions+w+s+returns)|(?:;s*(?:select|create|rename|truncate|load|alter|delete|update|insert|desc)s*[[(]?w{2,})
(?:alters*w+.*characters+sets+w+)|(";s*waitfors+times+")|(?:";.*:s*goto)
(?:procedures+analyses*()|(?:;s*(declare|open)s+[w-]+)|(?:creates+(procedure|function)s*w+s*(s*)s*-)|(?:declare[^w]+[@#]s*w+)|(execs*
(s*@)
(?:selects*pg_sleep)|(?:waitfors*delays?"+s?d)|(?:;s*shutdowns*(?:;|--|#|/*|{))
(?:sexecs+xp_cmdshell)|(?:"s*!s*["w])|(?:fromW+information_schemaW)|(?:(?:(?:current_)?user|database|schema|connection_id)s*([^)]*)|(?:";?
s*(?:select|union|having)s*[^s])|(?:wiifs*()|(?:execs+master.)|(?:union select @)|(?:union[w(s]*select)|(?:select.*w?user()|(?:into[s+]+
(?:dump|out)files*")
(?:merge.*usings*()|(executes*immediates*")|(?:W+d*s*havings*[^s-])|(?:matchs*[w(),+-]+s*againsts*()
(?:,.*[)da-f"]"(?:".*"|Z|[^"]+))|(?:Wselect.+W*from)|((?:select|create|rename|truncate|load|alter|delete|update|insert|desc)s*(s*spaces*()
(?:[$(?:ne|eq|lte?|gte?|n?in|mod|all|size|exists|type|slice|or)])
(?:(sleep((s*)(d*)(s*))|benchmark((.*),(.*))))
(?:(union(.*)select(.*)from))
(?:^(-0000023456|4294967295|4294967296|2147483648|2147483647|0000012345|-2147483648|-2147483649|0000023456|2.2250738585072007e-308|1e309)$)
Some of the regular expressions used by PHPIDS 0.7
Nick Galbreath DEFCON20 @ngalbreath](https://image.slidesharecdn.com/newtechniquesinsqlobfuscation-120710095604-phpapp02/85/New-techniques-in-sql-obfuscation-from-DEFCON-20-5-320.jpg)
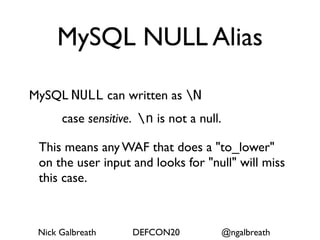
![NULL PGSQL
• ISNULL, NOTNULL (same as IS NULL),
this is a function in MSSQL
• "IS [NOT] UNKNOWN"
• "IS [NOT] DISTINCT"
Nick Galbreath DEFCON20 @ngalbreath](https://image.slidesharecdn.com/newtechniquesinsqlobfuscation-120710095604-phpapp02/85/New-techniques-in-sql-obfuscation-from-DEFCON-20-12-320.jpg)
![Floating Point
• digits • digits[.]digits[eE]digits
• digits[.] • digits[.]digits[eE][+-]digits
• digits[.]digits • [.]digits
• digits[eE]digits • [.]digits[eE]digits
• digits[eE][+-]digits • [.]digits[eE][+-]digits
• digits[.][eE]digits
Optional starts with [+-]
Optional ending with [dDfF] (Oracle)](https://image.slidesharecdn.com/newtechniquesinsqlobfuscation-120710095604-phpapp02/85/New-techniques-in-sql-obfuscation-from-DEFCON-20-14-320.jpg)

![Oracle Q String
http://docs.oracle.com/cd/B28359_01/appdev.111/b28370/
fundamentals.htm#autoId6
q'!...!' notation allows use of single quotes inside literal
string_var := q'!I'm a string!';
You can use delimiters [, {, <, and (, pair them with ], }, >, and ),
pass a string literal representing a SQL statement to a
subprogram, without doubling the quotation marks around
'INVALID' as follows:
func_call(q'[SELECT index_name FROM user_indexes
WHERE status ='INVALID']');
Nick Galbreath DEFCON20 @ngalbreath](https://image.slidesharecdn.com/newtechniquesinsqlobfuscation-120710095604-phpapp02/85/New-techniques-in-sql-obfuscation-from-DEFCON-20-29-320.jpg)