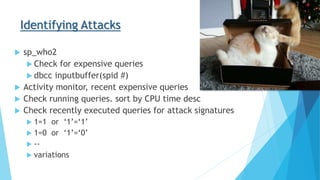
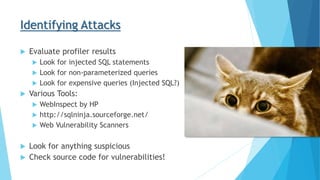
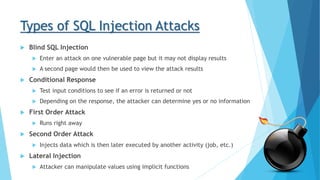
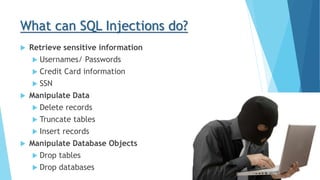
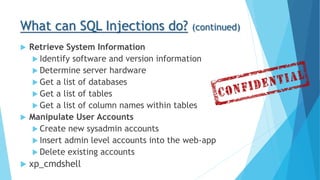
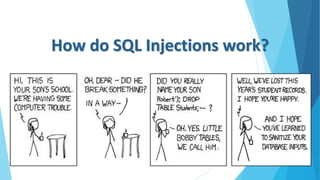
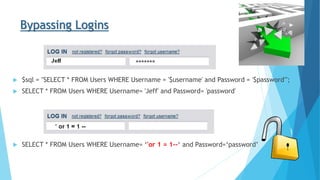
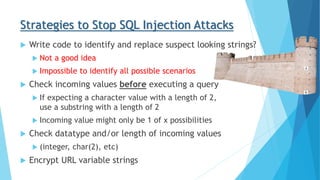
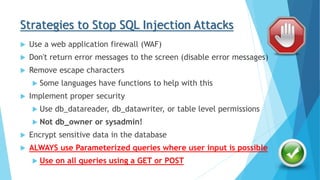
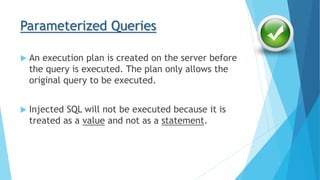
This document discusses SQL injections and how to prevent them. It begins by defining SQL injections as a code injection technique used to attack data-driven applications by inserting malicious SQL statements. It then covers what SQL injections can do, like retrieve sensitive data, manipulate data, or retrieve system information. The document discusses how SQL injections work through different attack techniques. It provides strategies for preventing SQL injections like using parameterized queries and input validation. It also offers tips for identifying SQL injection attacks.







![Parameterized Queries – Code Example
Not Safe (Non-Parameterized)
$tsql_States = sprintf("SELECT * FROM vw_DimState WHERE stateCode='%s' AND
countryCode='%s'", $_GET[‘State’], $_GET[‘Country’]);
$stmt_States = sqlsrv_query($conn, $tsql_States);
$row_States = sqlsrv_fetch_array($stmt_States, SQLSRV_FETCH_ASSOC);
Safe (Parameterized)
$tsql_States = "SELECT * FROM vw_DimState WHERE stateCode=? AND countryCode=?";
$params_States = array($_GET[‘State’], $_GET[‘Country’]);
$stmt_States = sqlsrv_query($conn, $tsql_States, $params_States);
$row_States = sqlsrv_fetch_array( $stmt_States, SQLSRV_FETCH_ASSOC);](https://image.slidesharecdn.com/fa81d333-3675-45d4-9eaa-8ad0a091f8d4-160404161732/85/SQL-Injections-2016-Huntington-Beach-24-320.jpg)