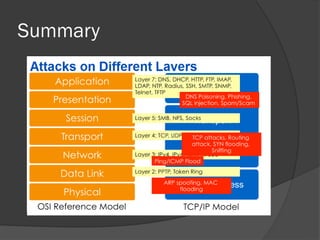
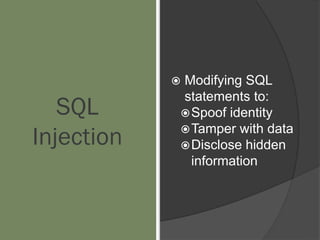
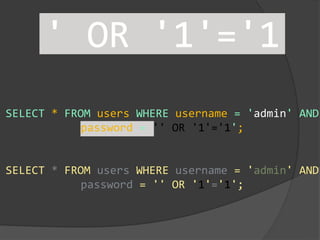
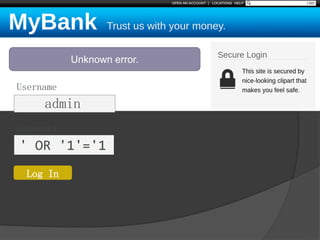
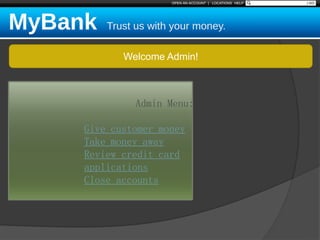
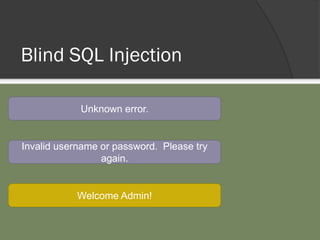
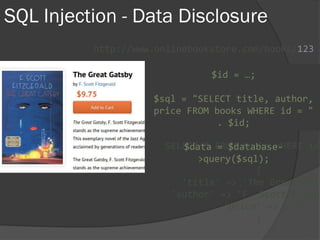
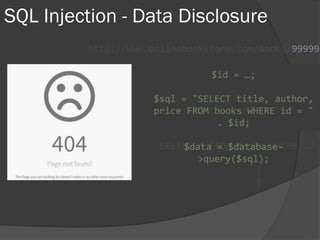
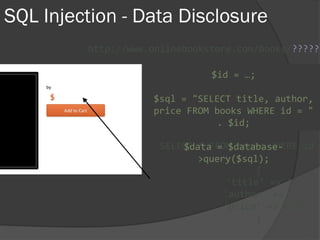
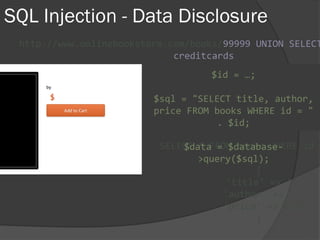
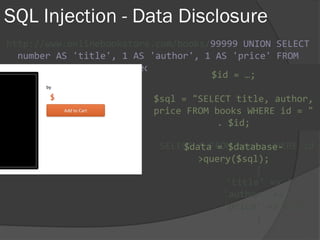
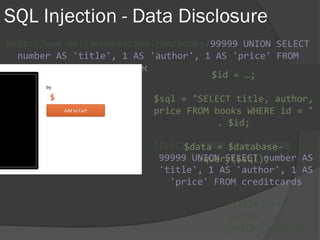
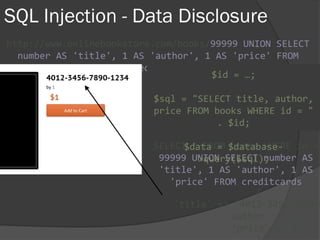
This document discusses various cybersecurity topics related to PHP, including hacking, attacks, and recovering from attacks. It provides an overview of general security aspects and the OSI model layers. It then covers specific types of attacks like denial-of-service, spoofing, and man-in-the-middle attacks. It also discusses vulnerabilities, exploits, and the OWASP top 10 security risks. A large portion of the document focuses on SQL injection attacks, how they work, and ways to protect against them. It also briefly discusses other injection attacks and cross-site scripting attacks.






![SQL Injection Basics
$value = $_REQUEST['value'];
SELECT * FROM x WHERE y = '[MALICIOUS CODE
HERE]' ";
$sql = "SELECT * FROM x WHERE y = '$value'
";
$database->query($sql);](https://image.slidesharecdn.com/php-security-170908201811/85/Php-Security-OWASP-30-320.jpg)





![$val = $_REQUEST['value'];
$sql = "SELECT * FROM x WHERE y = '$val'
";
$database->query($sql);
Protecting Against
SQL Injection
Block input with
special characters](https://image.slidesharecdn.com/php-security-170908201811/85/Php-Security-OWASP-68-320.jpg)
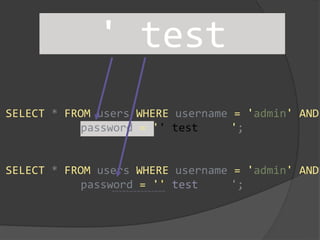
![Protecting
Against SQL
Injection
Block input with
special characters
Escape user input
$value = $_REQUEST['value'];
$escaped = mysqli_real_escape_string($value);
$sql = "SELECT * FROM x WHERE y = '$escaped' ";
$database->query($sql);
' OR '1'
= '1
' OR '1'
= '1
mysqli_real_escape_string()
SELECT * FROM x
WHERE y = '' OR '1' = '1'](https://image.slidesharecdn.com/php-security-170908201811/85/Php-Security-OWASP-69-320.jpg)
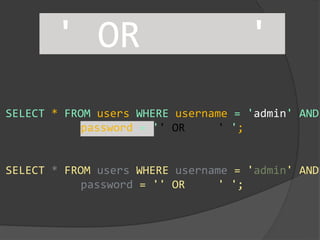
![Protecting
Against SQL
Injection
Block input with
special characters
Escape user input
$value = $_REQUEST['value'];
$escaped = mysqli_real_escape_string($value);
$sql = "SELECT * FROM x WHERE y = '$escaped' ";
$database->query($sql);
' OR '1'
= '1
' OR '1'
= '1
mysqli_real_escape_string()
SELECT * FROM x
WHERE y = '' OR '1' = '1'](https://image.slidesharecdn.com/php-security-170908201811/85/Php-Security-OWASP-70-320.jpg)
![Protecting
Against SQL
Injection
Block input with
special characters
Escape user input
Use prepared
statements
$mysqli = new mysqli("localhost", "user", "pass", "db");
$q = $mysqli->prepare("SELECT * FROM x WHERE y = '?' ");
$q->bind_param(1, $_REQUEST['value']);
$q->execute();
Native PHP:
● mysqli
● pdo_mysql
Frameworks / Libraries:
● Doctrine
● Eloquent
● Zend_Db](https://image.slidesharecdn.com/php-security-170908201811/85/Php-Security-OWASP-71-320.jpg)
![XSS Attack
Basics
Raw code/script
is injected onto a
page
$value = $_POST['value'];
$value = $rssFeed->first->title;
$value = db_fetch('SELECT x FROM table');
<?php echo $value ?>](https://image.slidesharecdn.com/php-security-170908201811/85/Php-Security-OWASP-74-320.jpg)

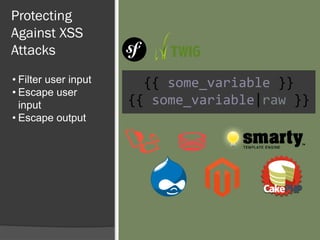
![Protecting
Against XSS
Attacks $value = $_POST['value'];
$value = db_fetch('SELECT value FROM table');
$value = $rssFeed->first->title;
<?php echo $value ?>](https://image.slidesharecdn.com/php-security-170908201811/85/Php-Security-OWASP-88-320.jpg)
![Protecting
Against XSS
Attacks
• Filter user input
$value = strip_tags($_POST['value']);
$value = strip_tags(
db_fetch('SELECT value FROM table')
);
$value = strip_tags($rssFeed->first->title);
<?php echo $value ?>](https://image.slidesharecdn.com/php-security-170908201811/85/Php-Security-OWASP-89-320.jpg)
![Protecting
Against XSS
Attacks
• Filter user input
• Escape user
input
$value = htmlspecialchars($_POST['value']);
$value = htmlspecialchars(
db_fetch('SELECT value FROM table')
);
$value = htmlspecialchars($rssFeed->first->title);
<?php echo $value ?>
<script> <script>
htmlspecialchars()](https://image.slidesharecdn.com/php-security-170908201811/85/Php-Security-OWASP-90-320.jpg)
![Protecting
Against XSS
Attacks
• Filter user input
• Escape user
input
• Escape output
$value = $_POST['value'];
$value = db_fetch('SELECT value FROM table');
$value = $rssFeed->first->title;
<?php echo htmlspecialchars($value) ?>](https://image.slidesharecdn.com/php-security-170908201811/85/Php-Security-OWASP-91-320.jpg)