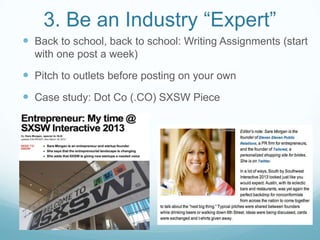
This document provides 8 tips for gaining brand credibility and distribution. The tips include finding your brand voice, leveraging partnerships, becoming an industry expert through writing, using flattery to get coverage, never saying no to coverage opportunities, putting founders and personalities forward, building a loyal community, and performing random acts of kindness for others in your industry. Case studies are provided for each tip.