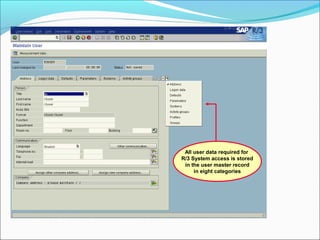
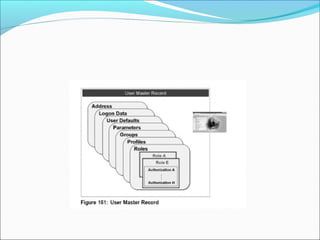
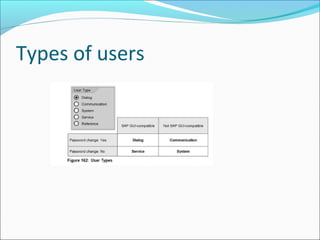
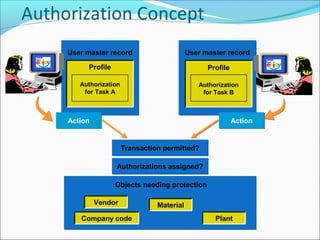
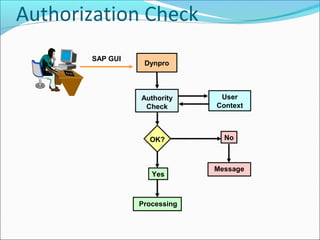
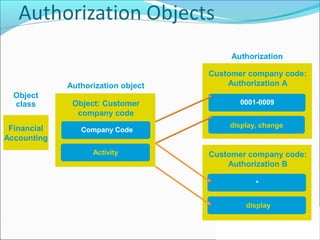
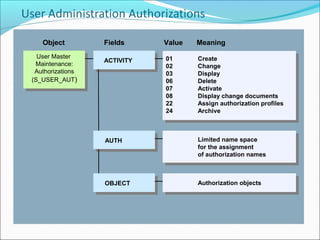
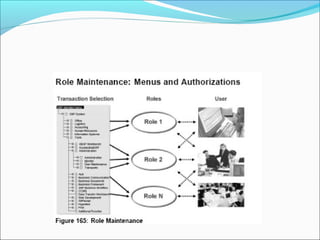
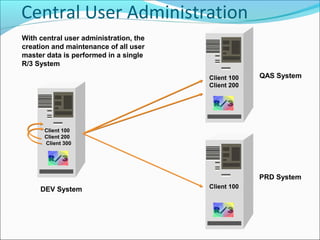
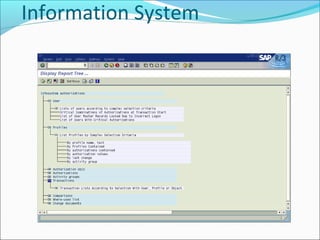
The document discusses user authorization in SAP systems, explaining that user master records must be set up and assigned roles before users can access the system. A user's menu and authorizations are linked to their user master record via roles, and the user master record stores all user data required for system access across eight categories. Central user administration allows creation and maintenance of all user master data to be performed in a single SAP system.