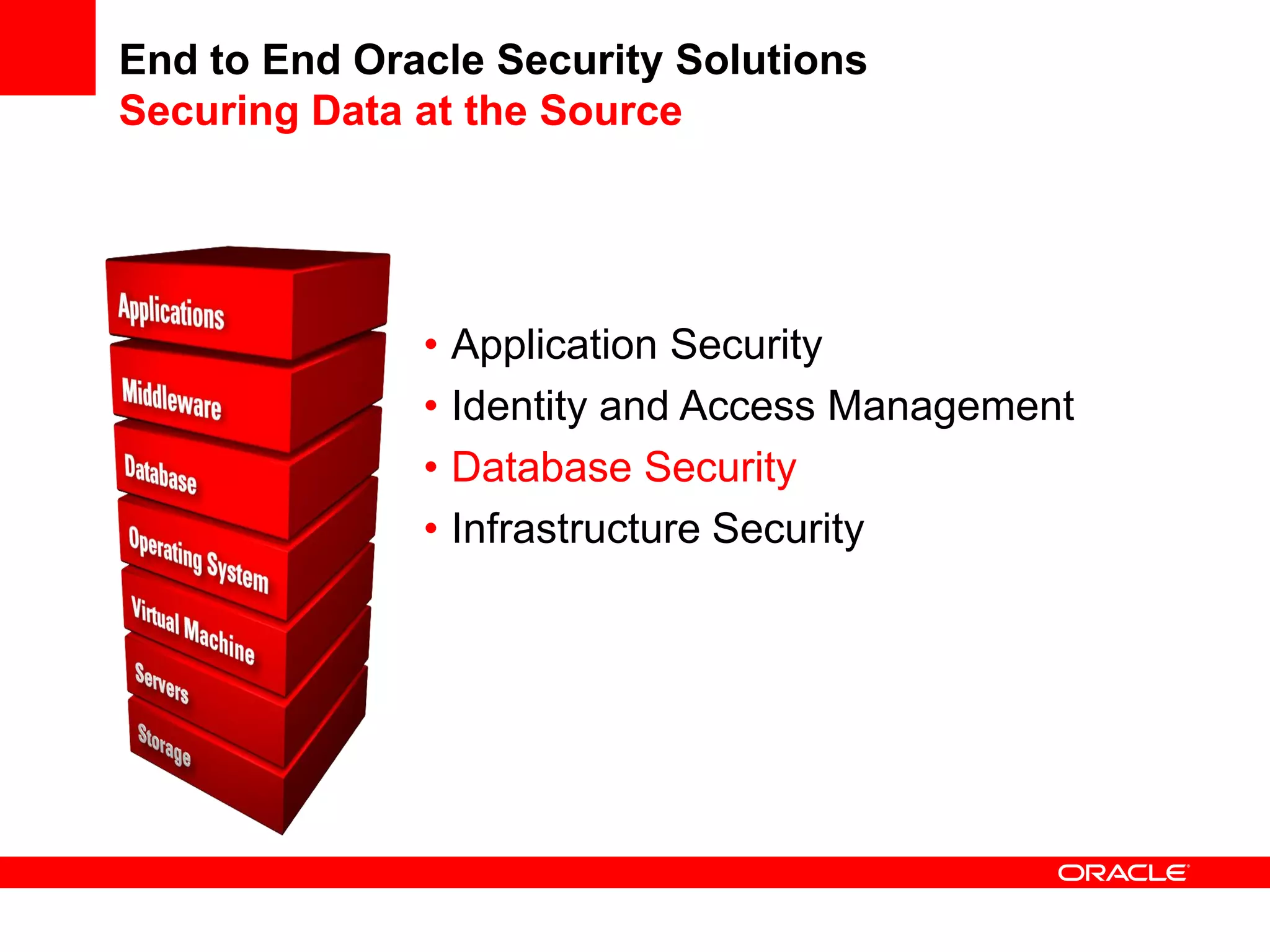
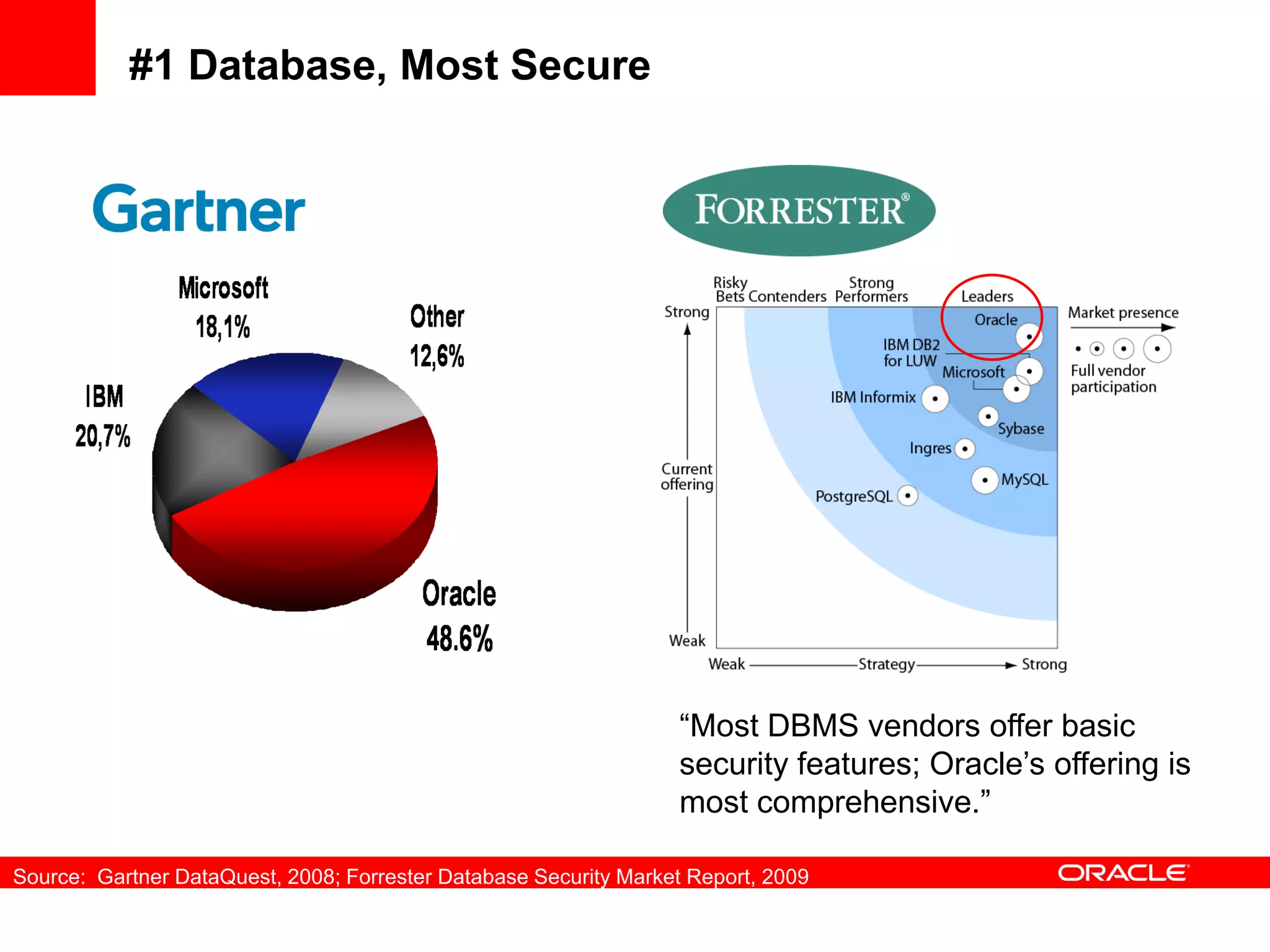
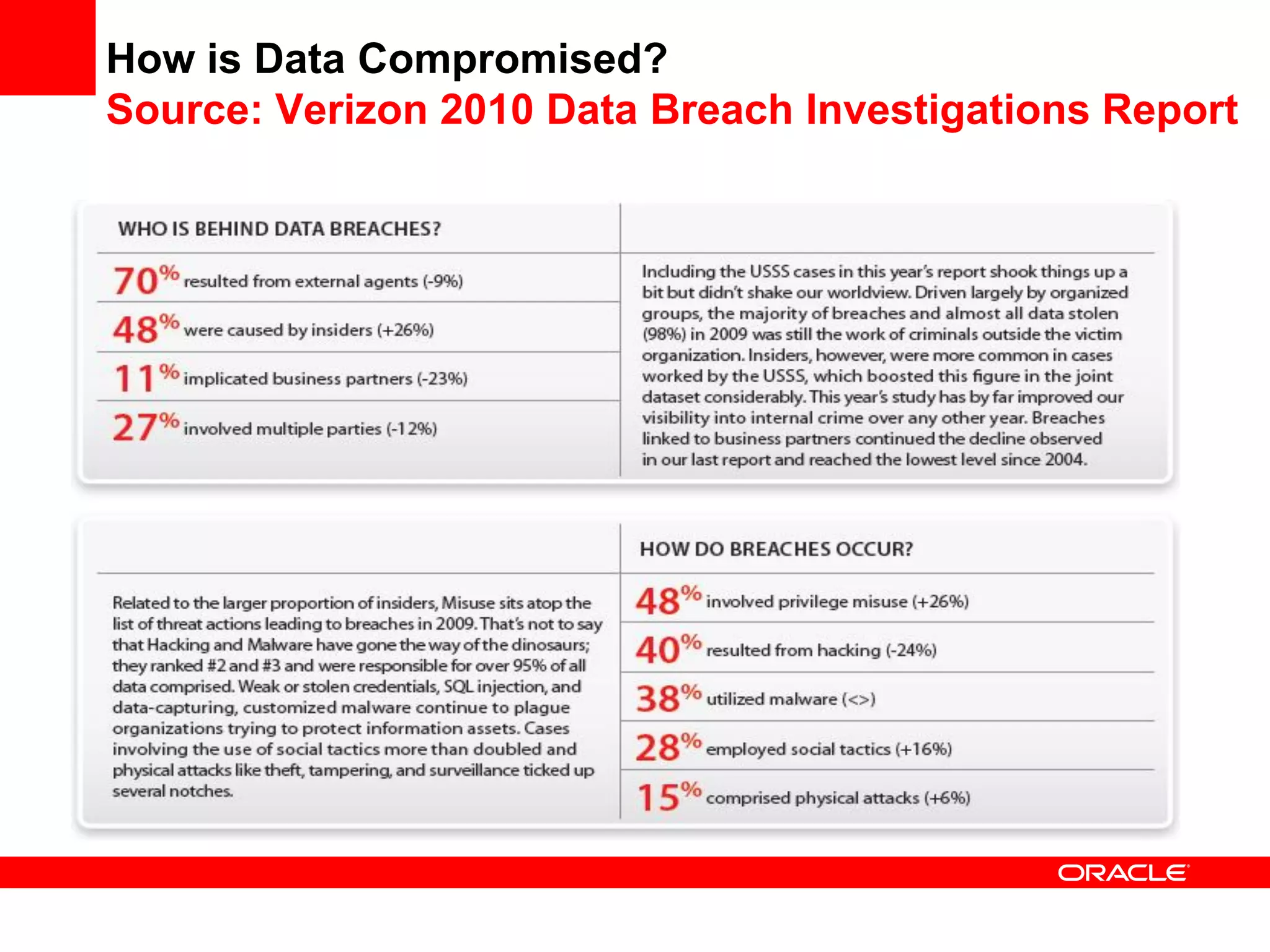
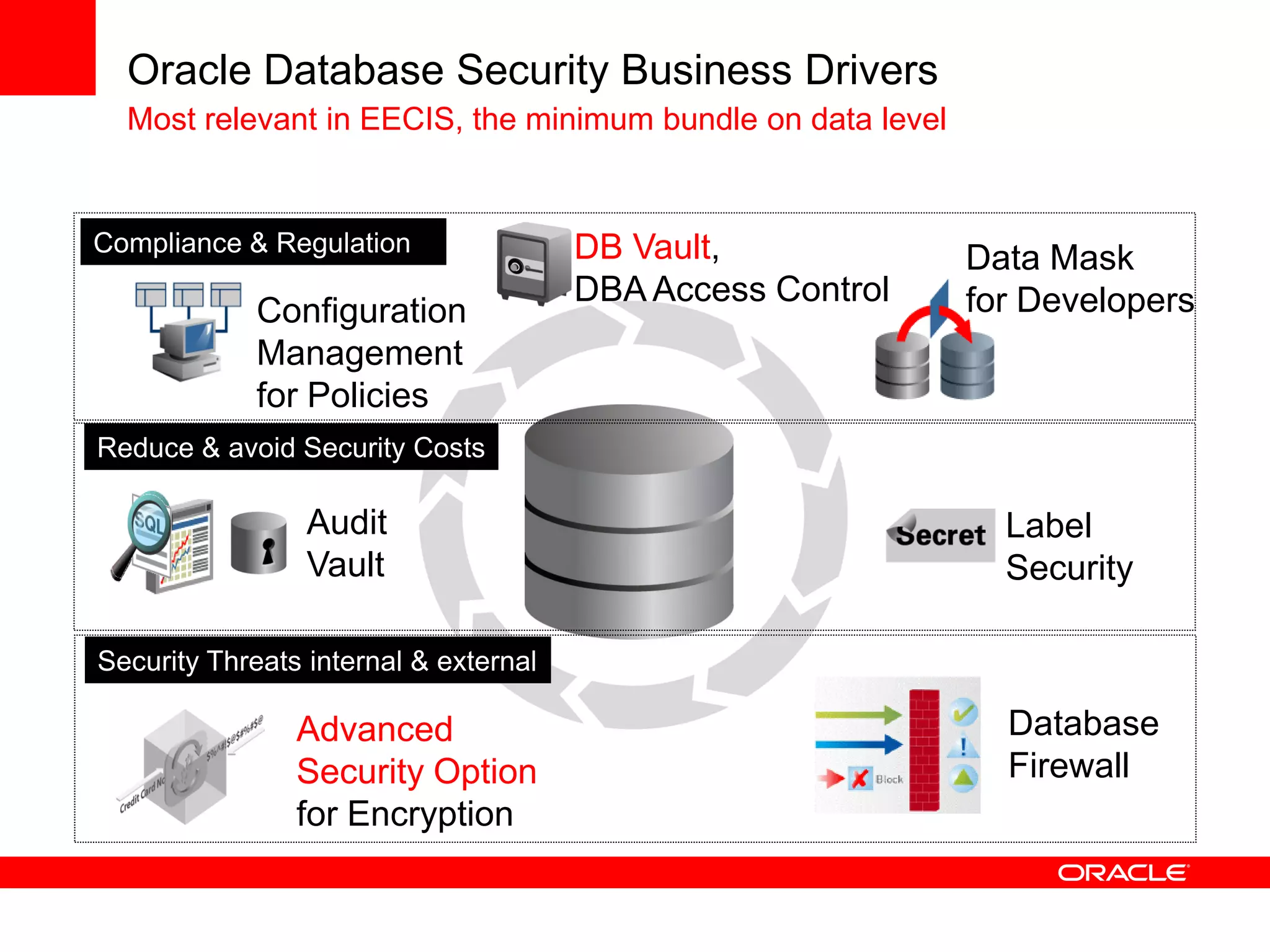
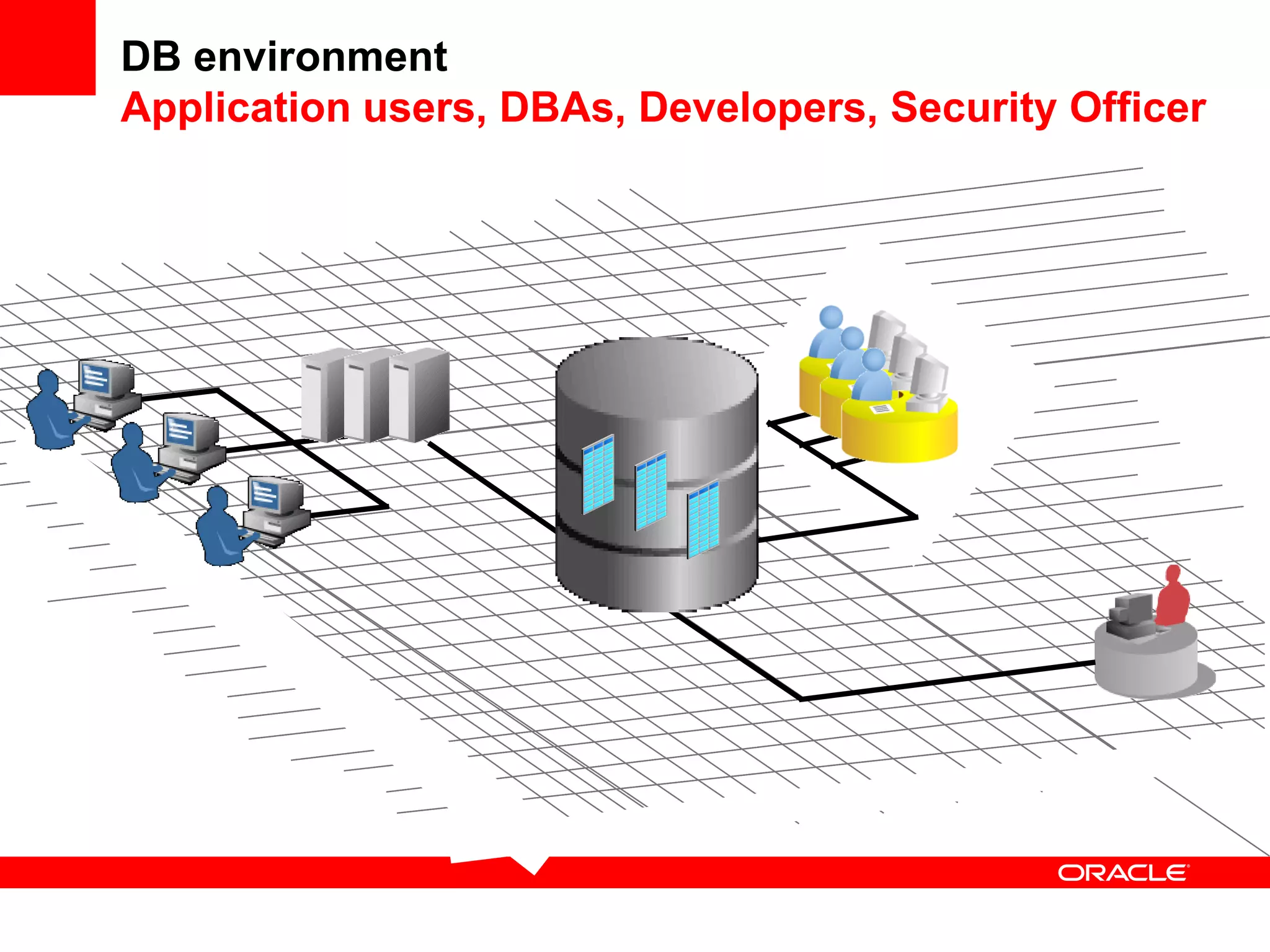
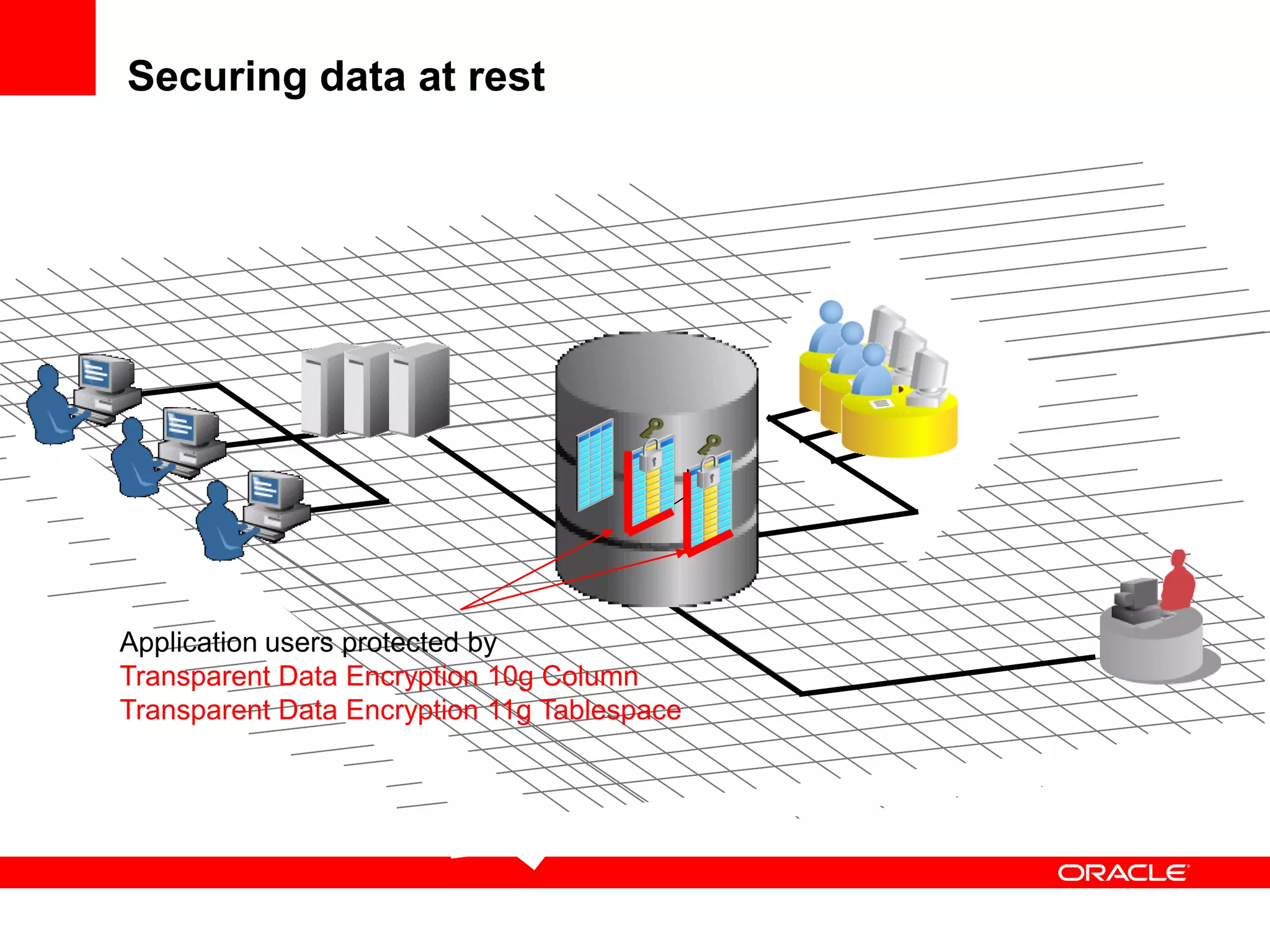
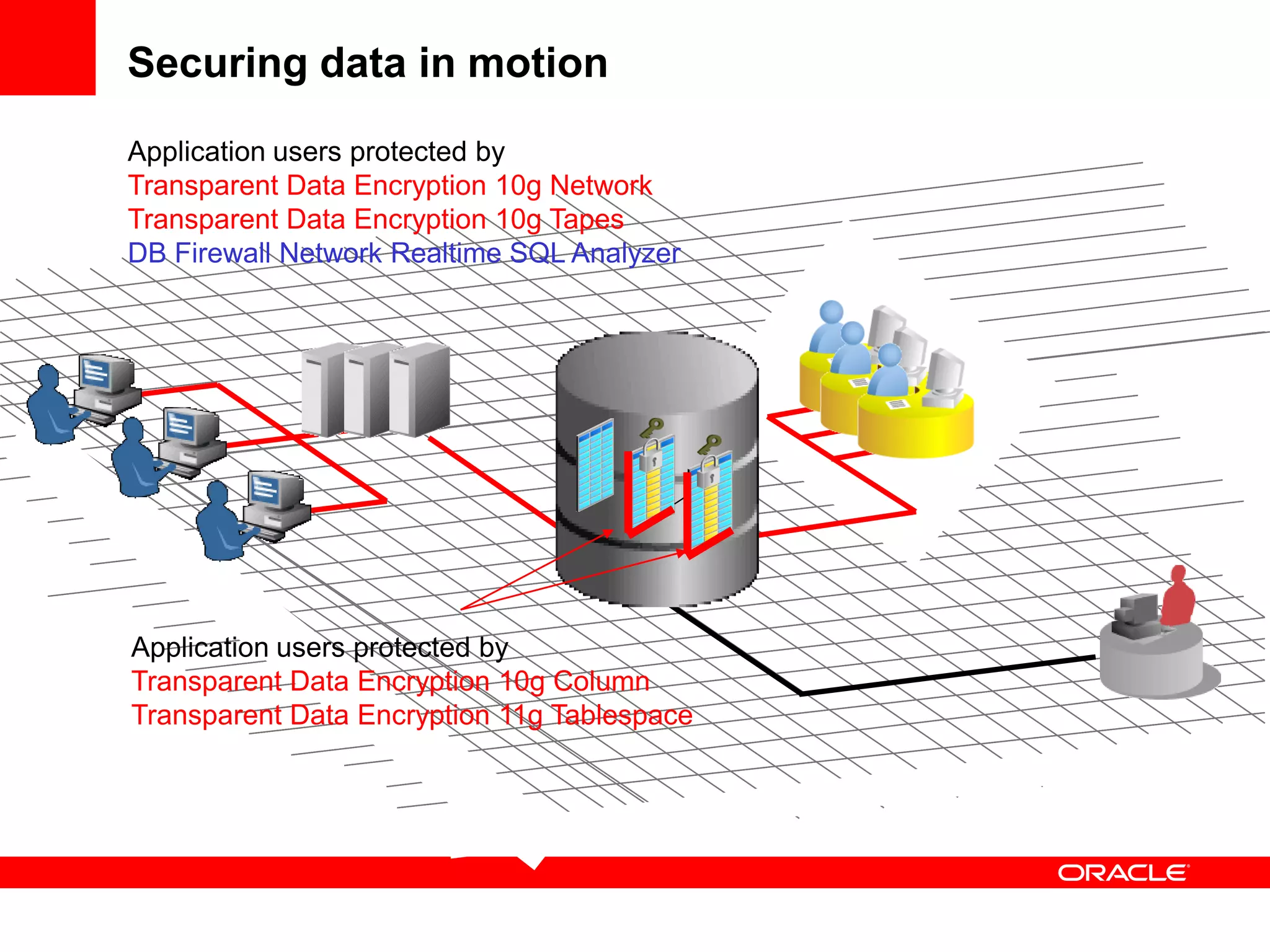
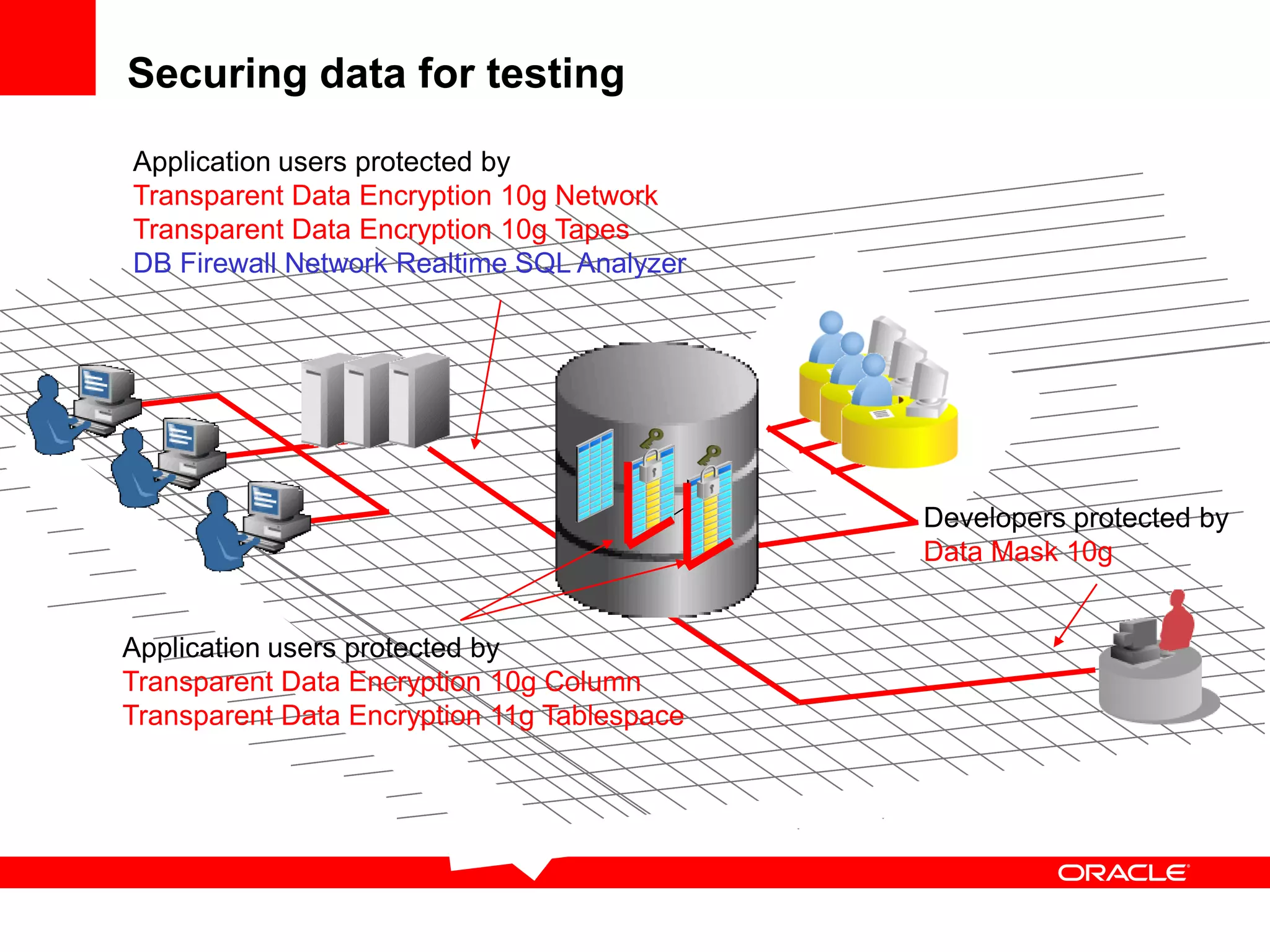
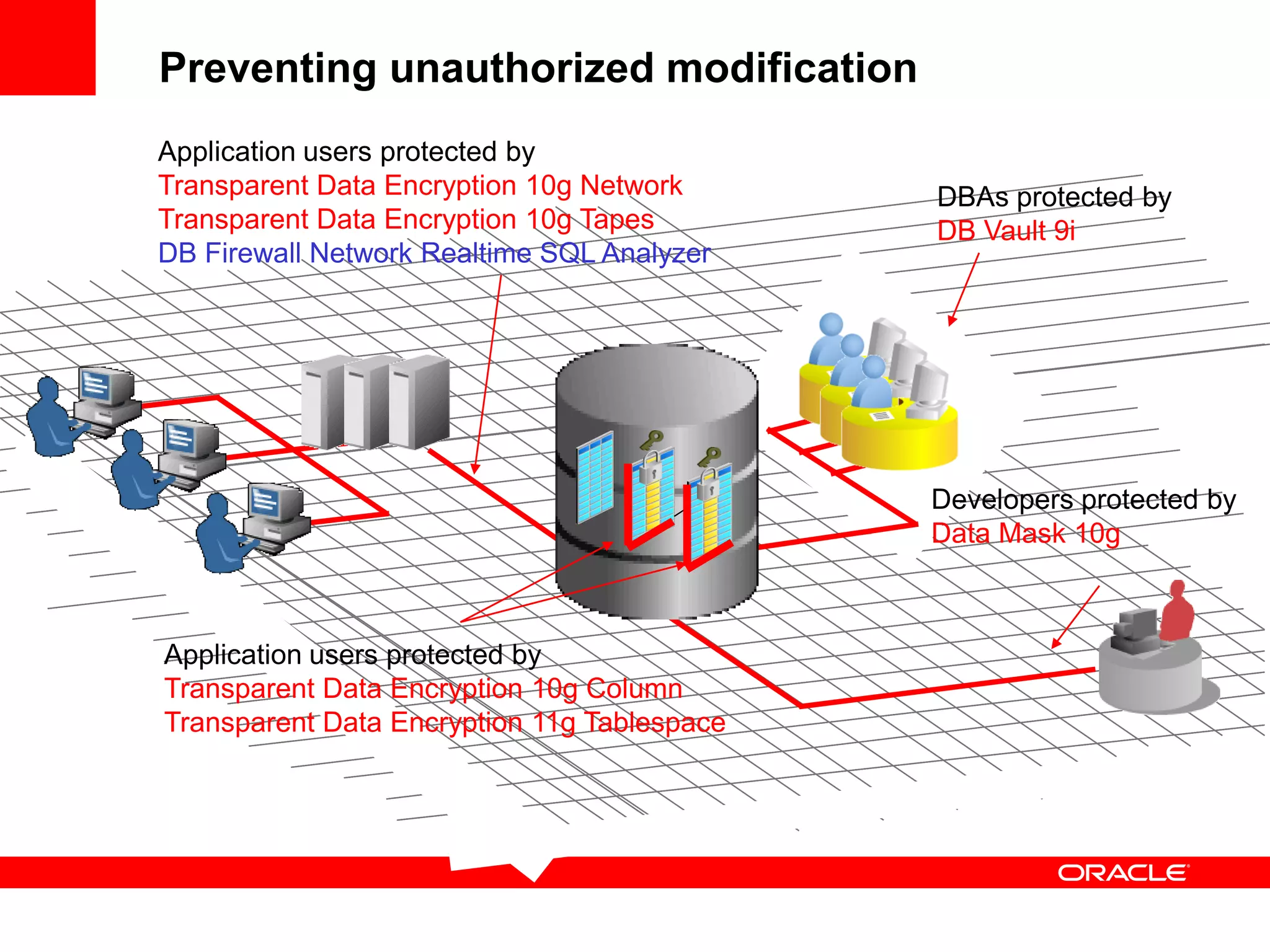
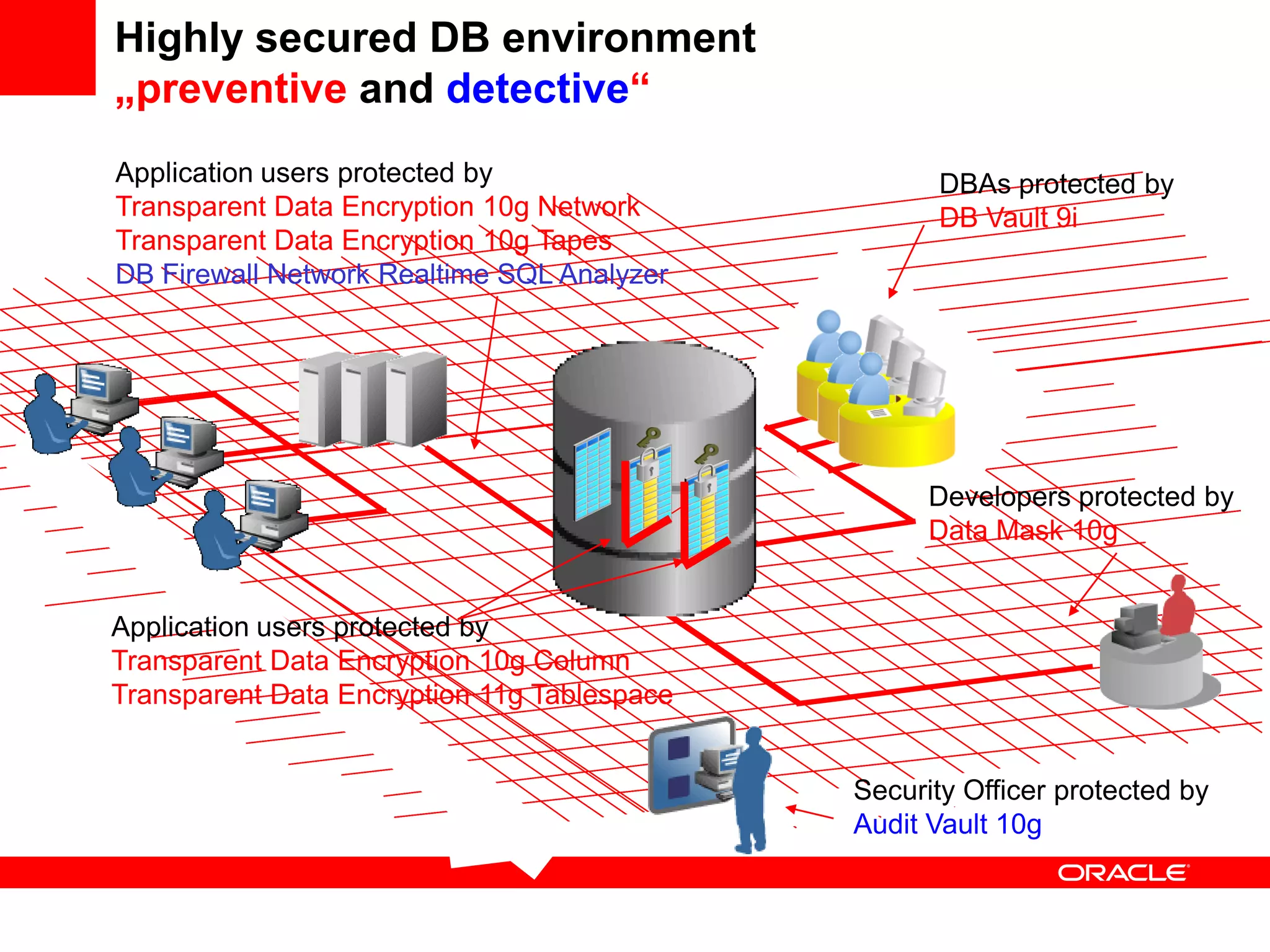
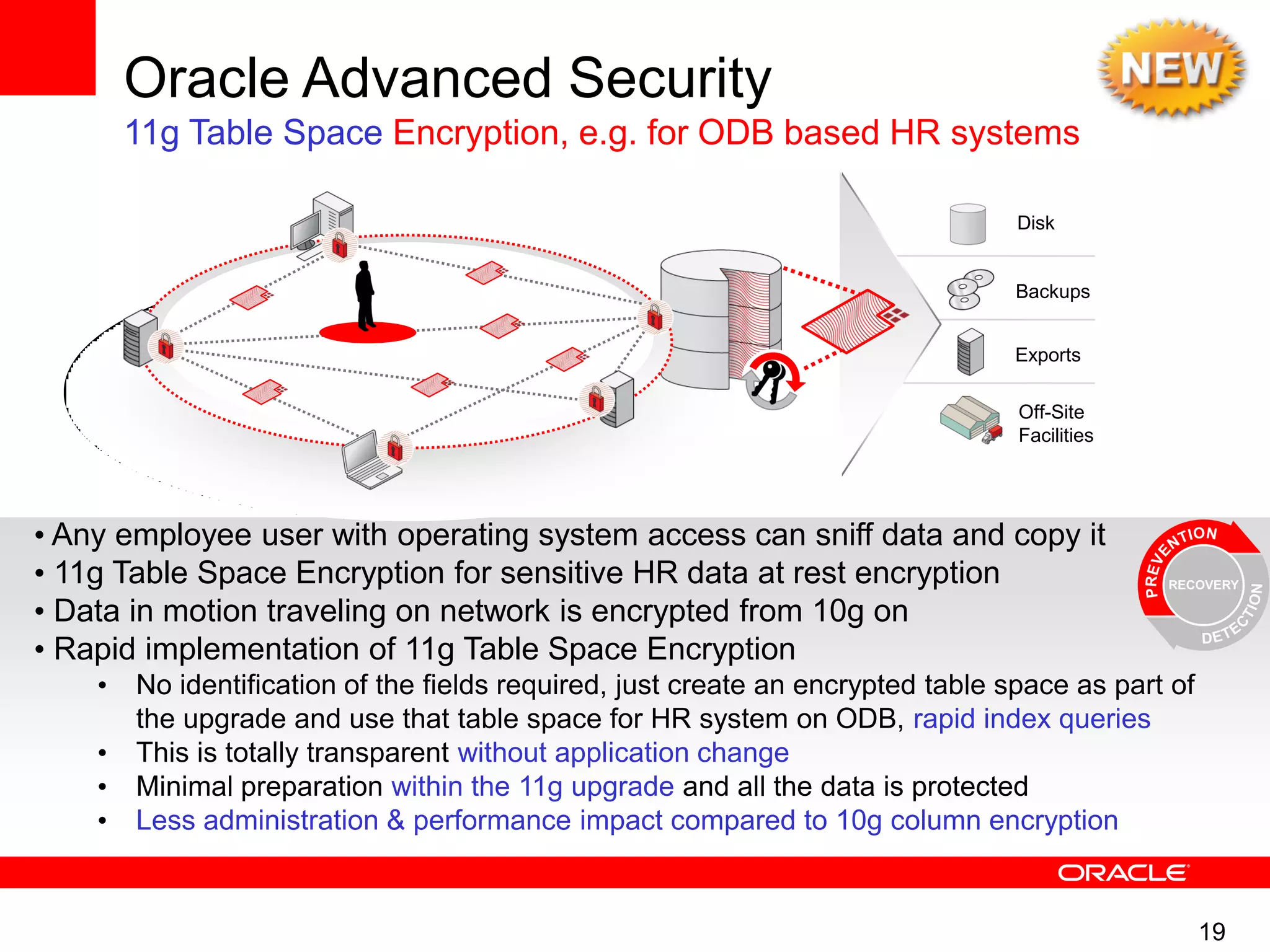
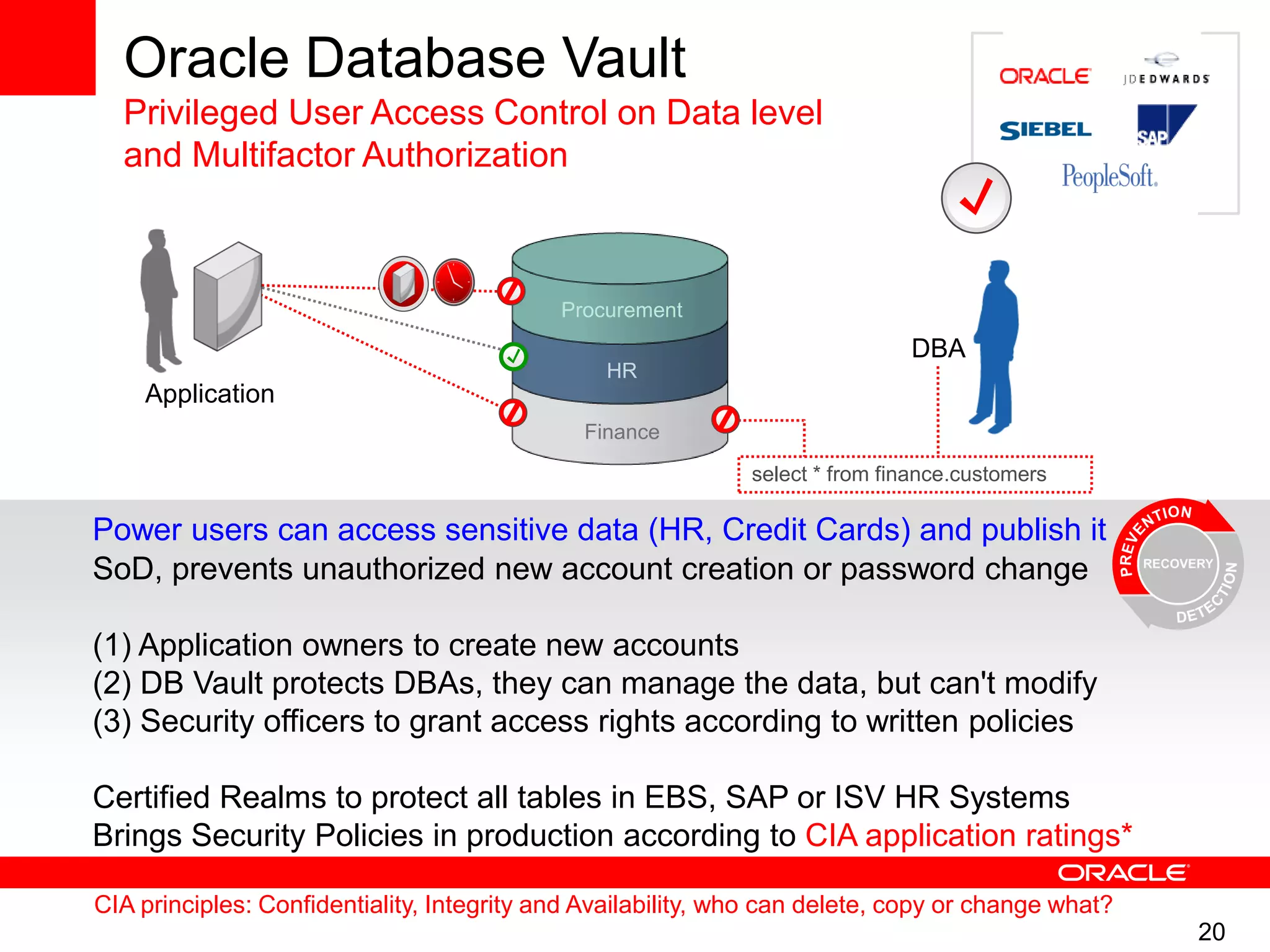
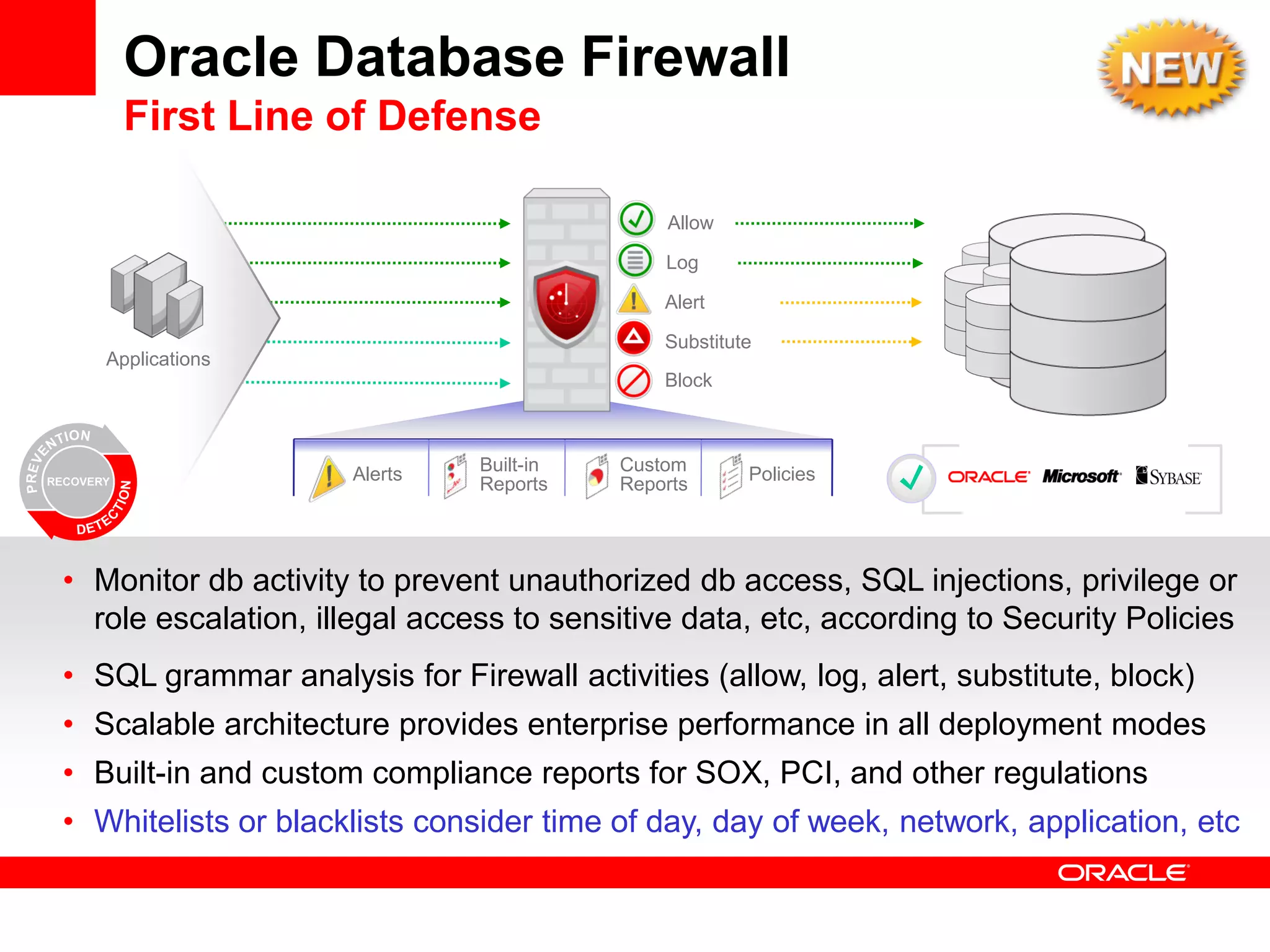
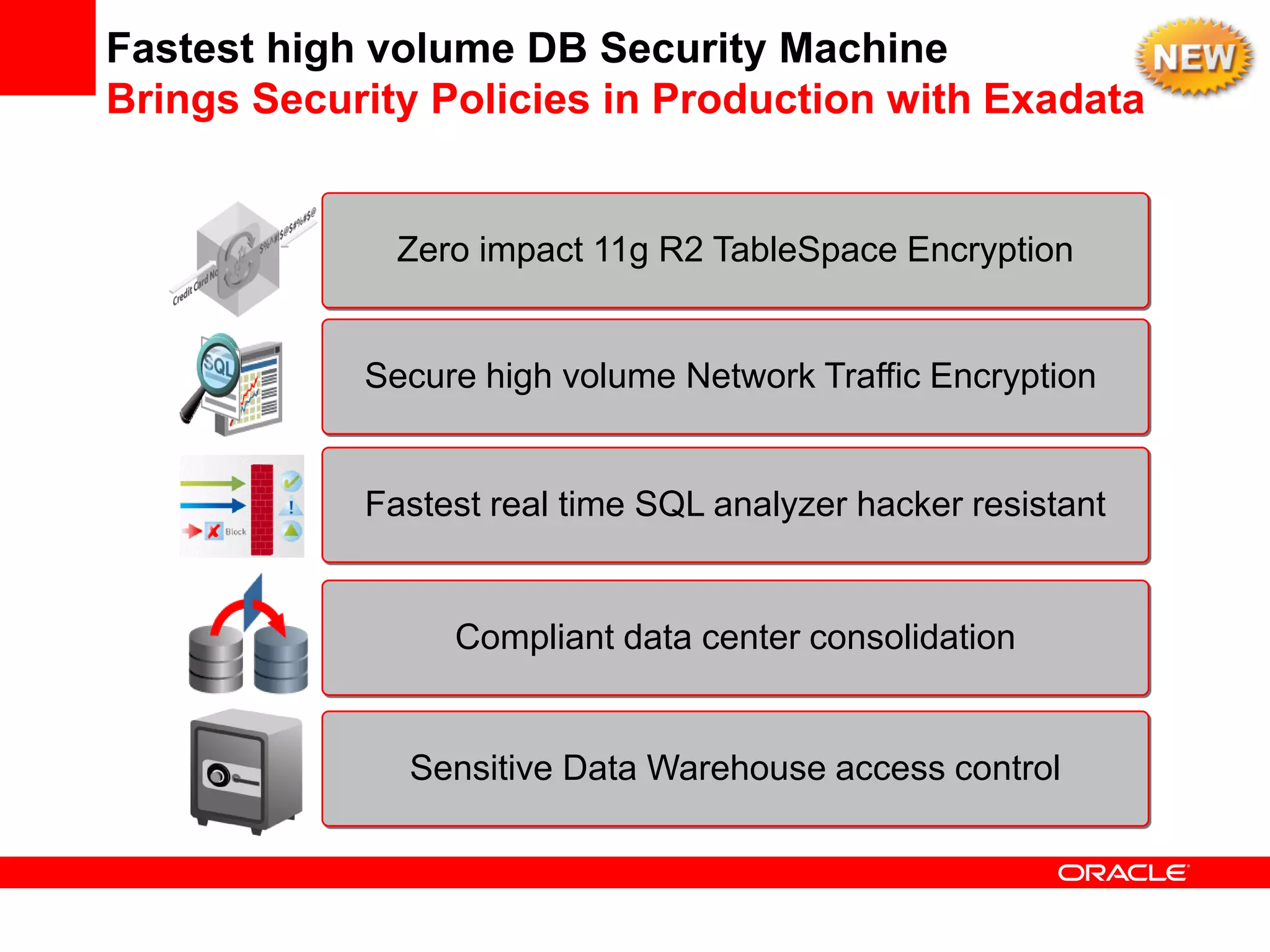
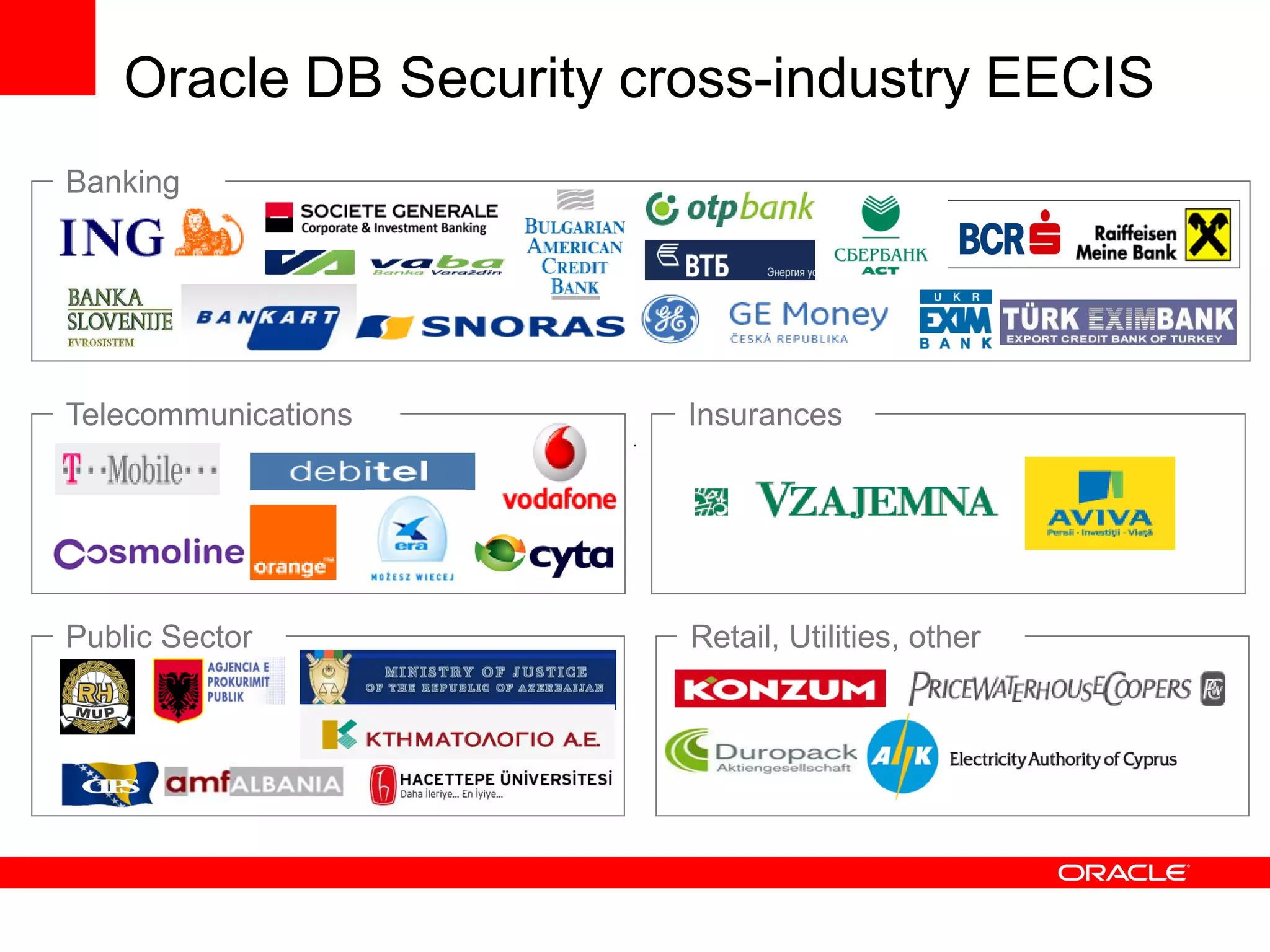
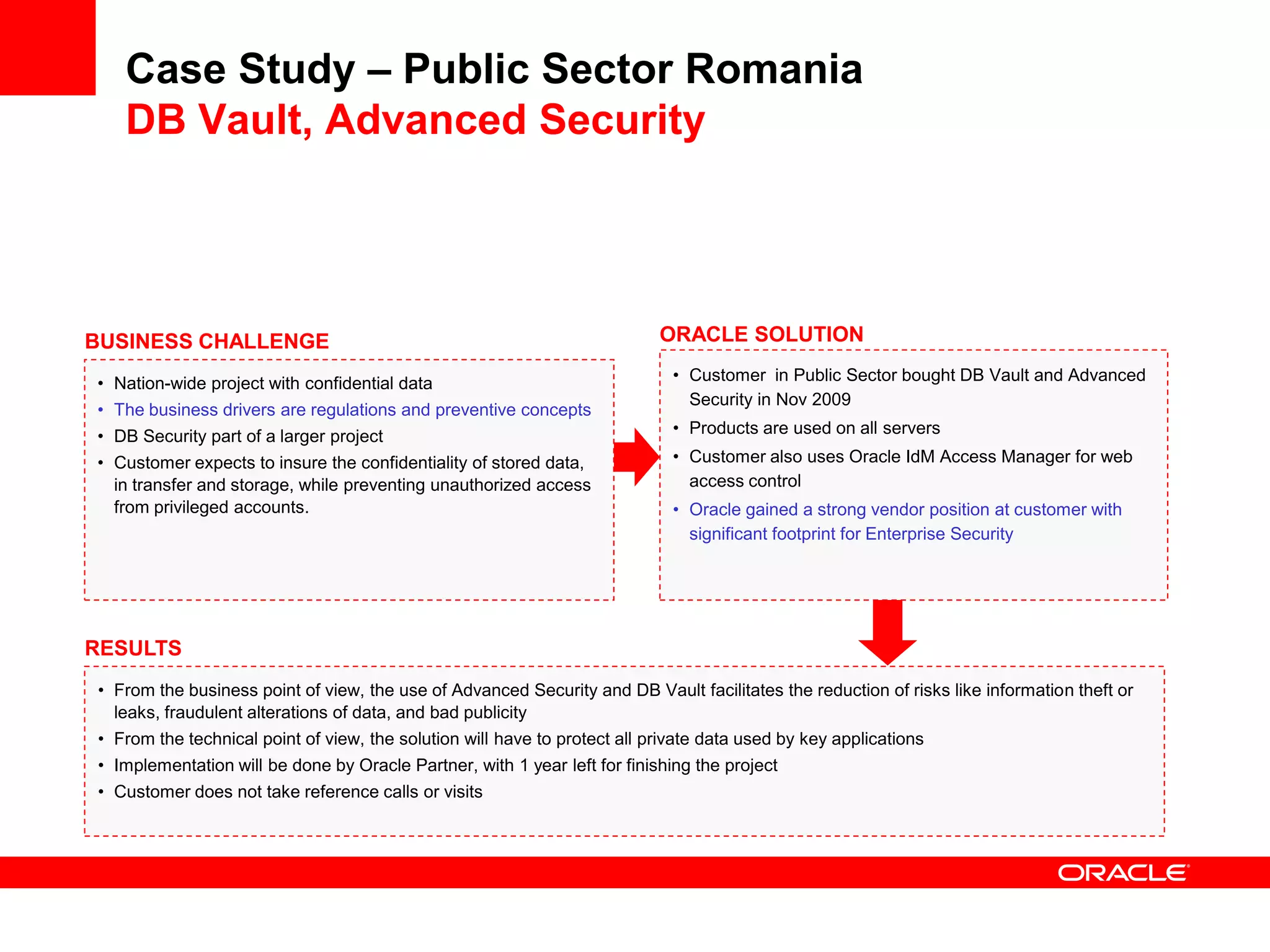
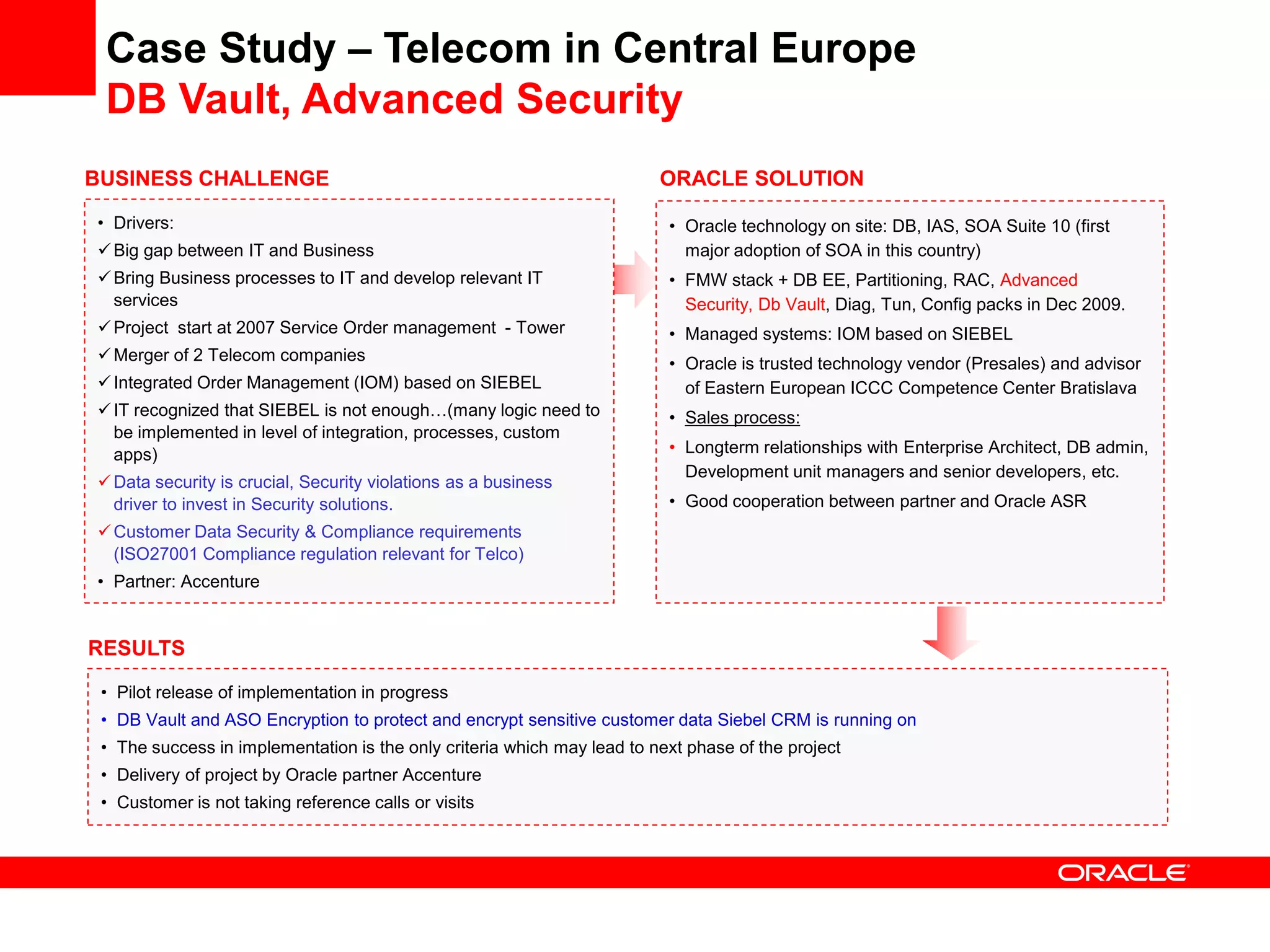
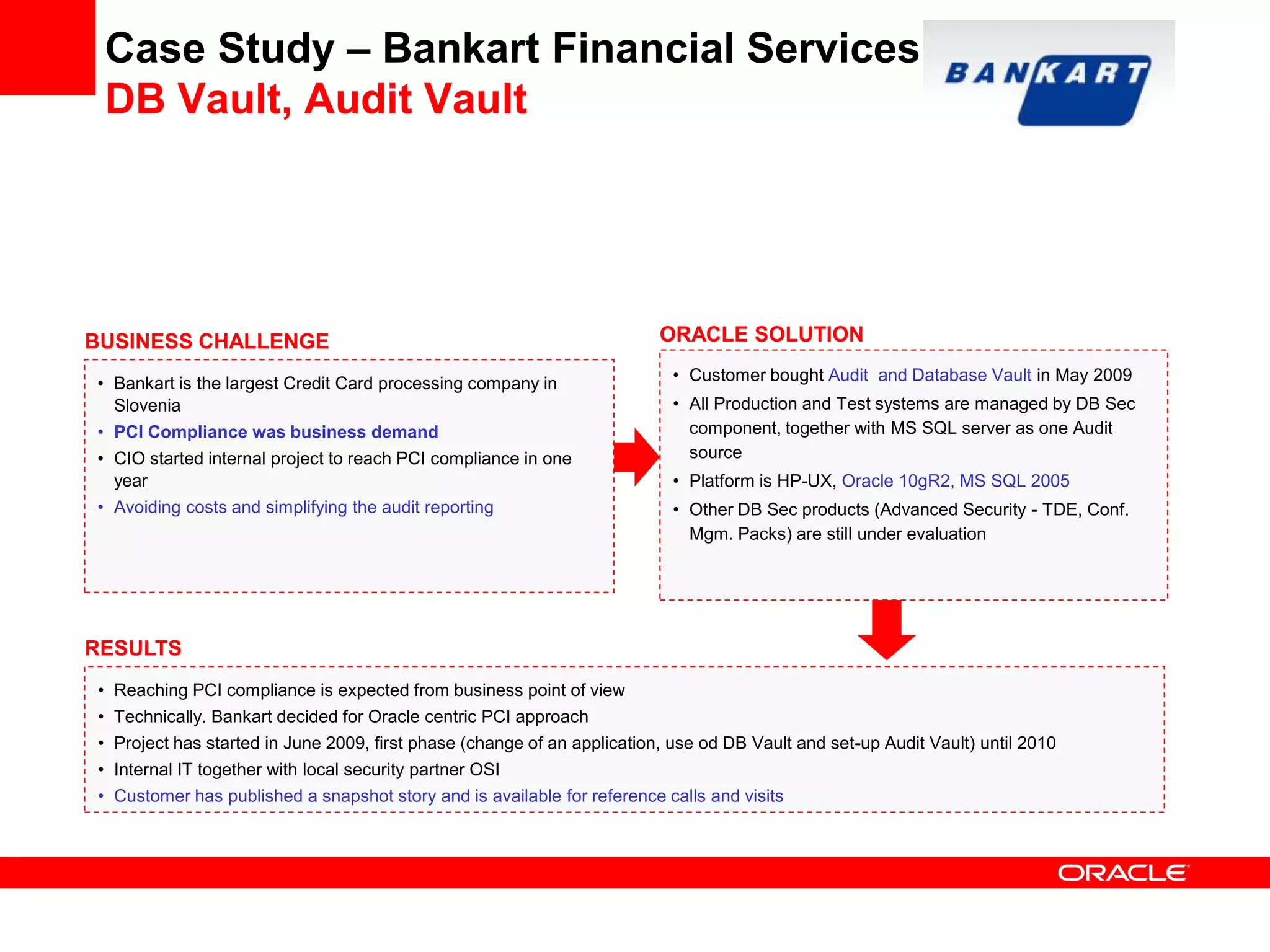
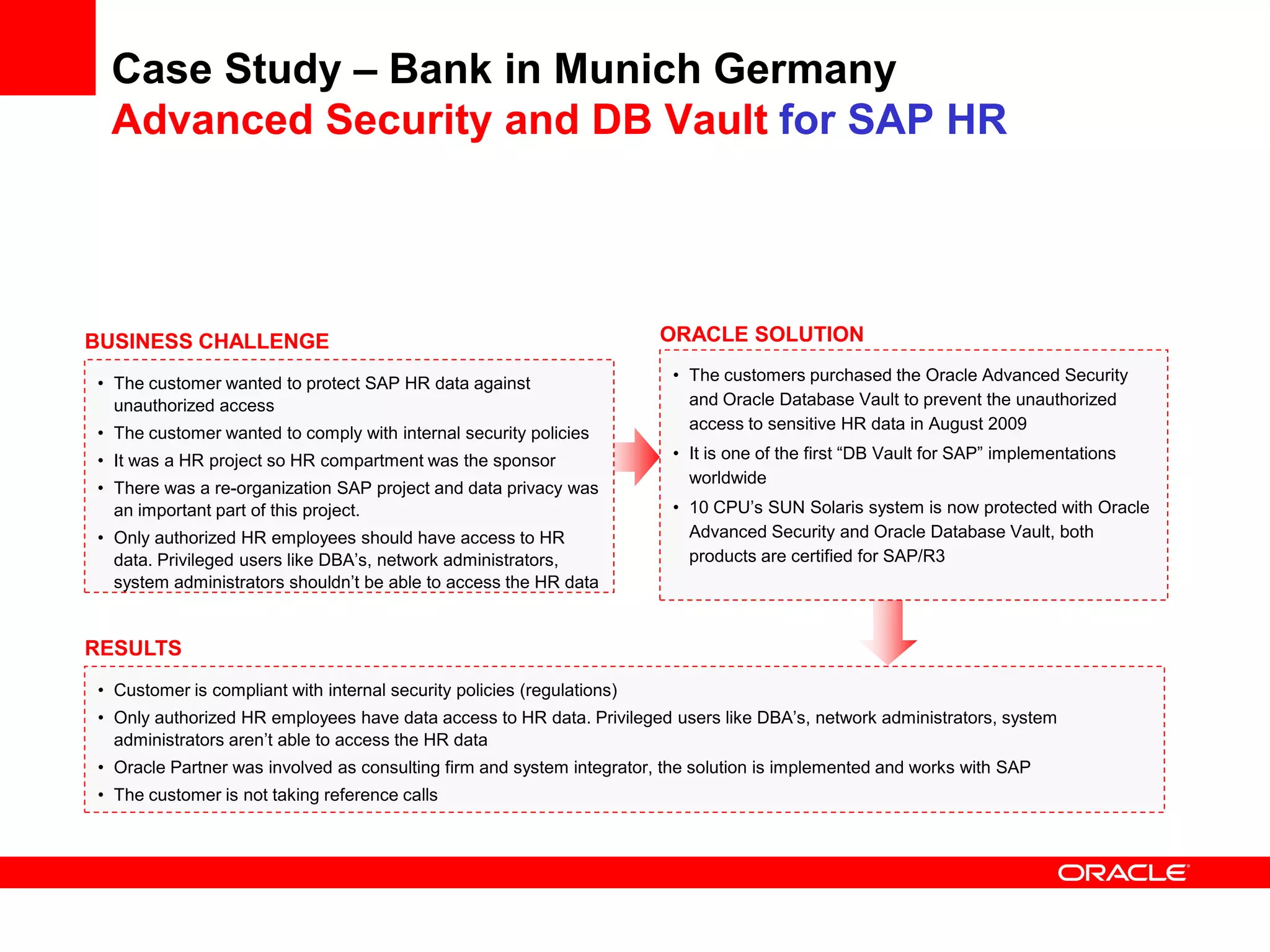
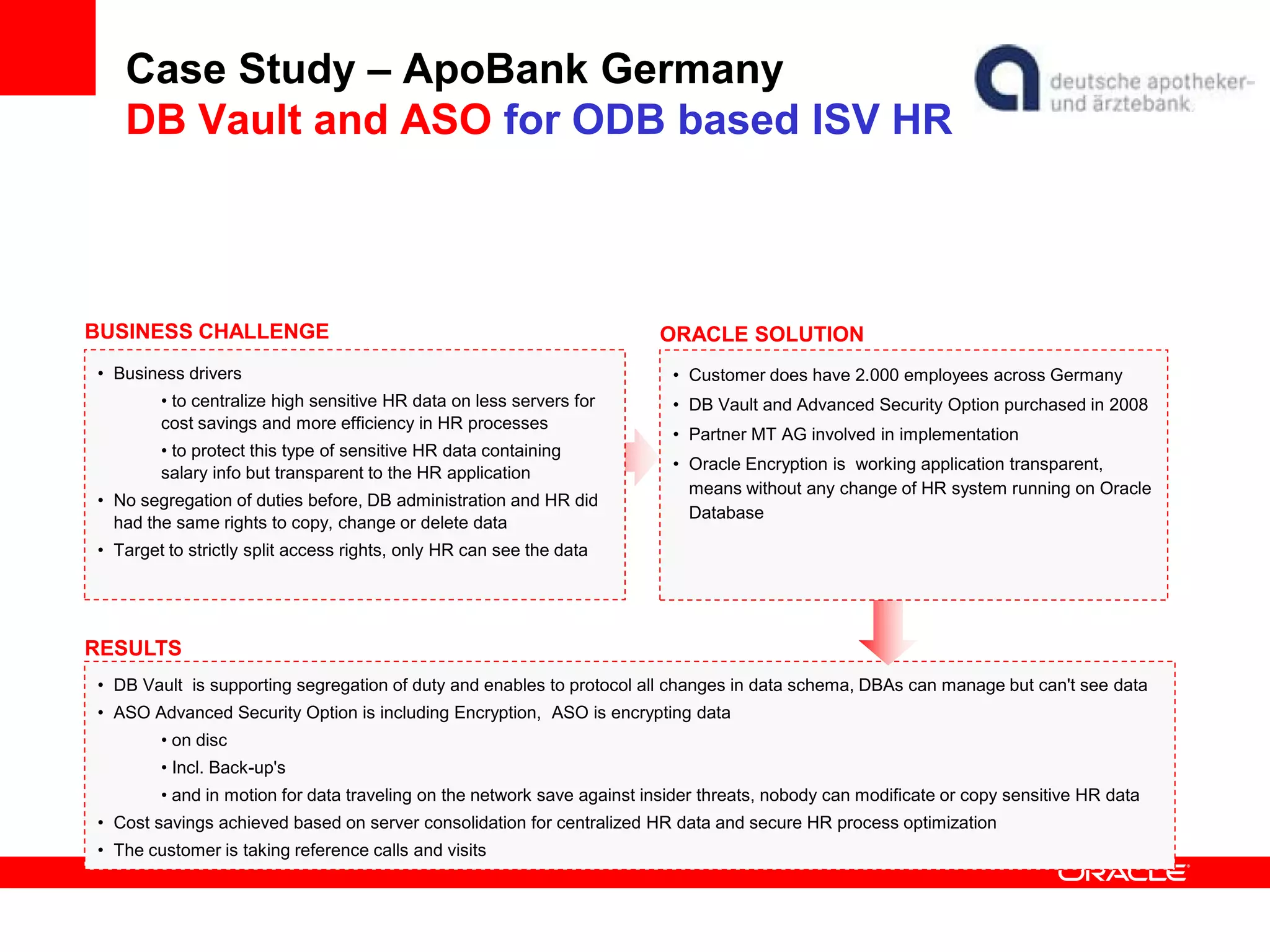
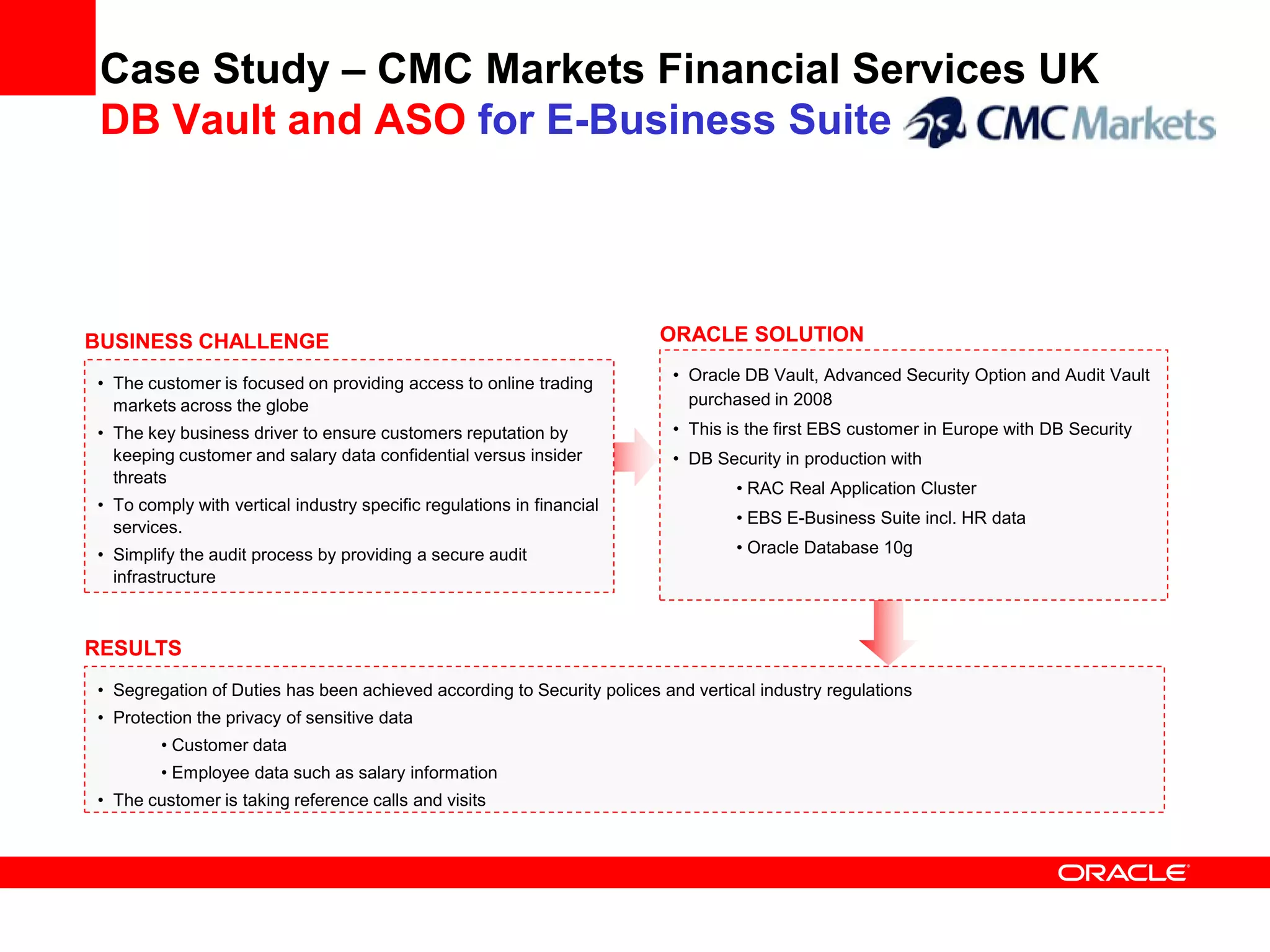
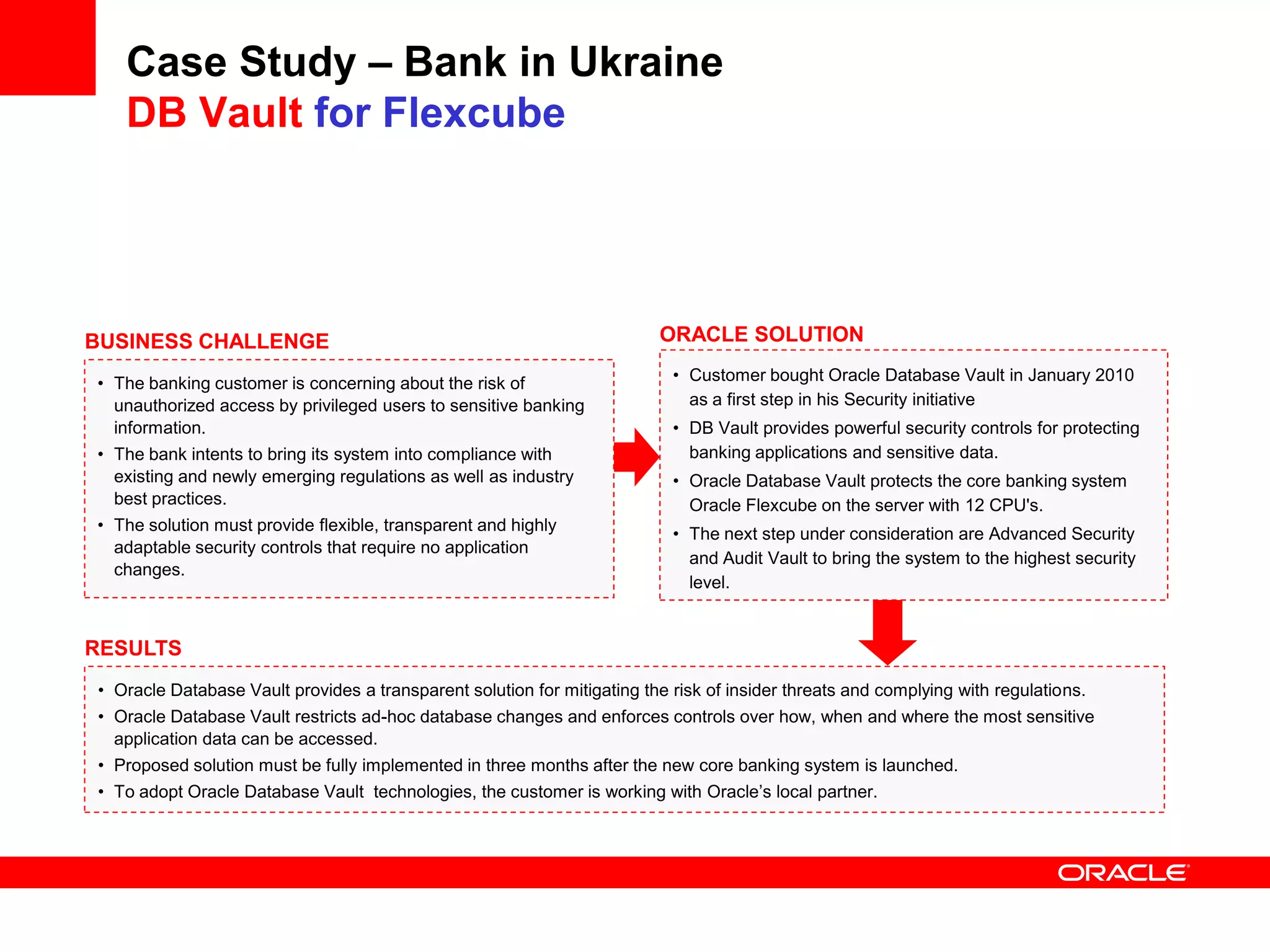
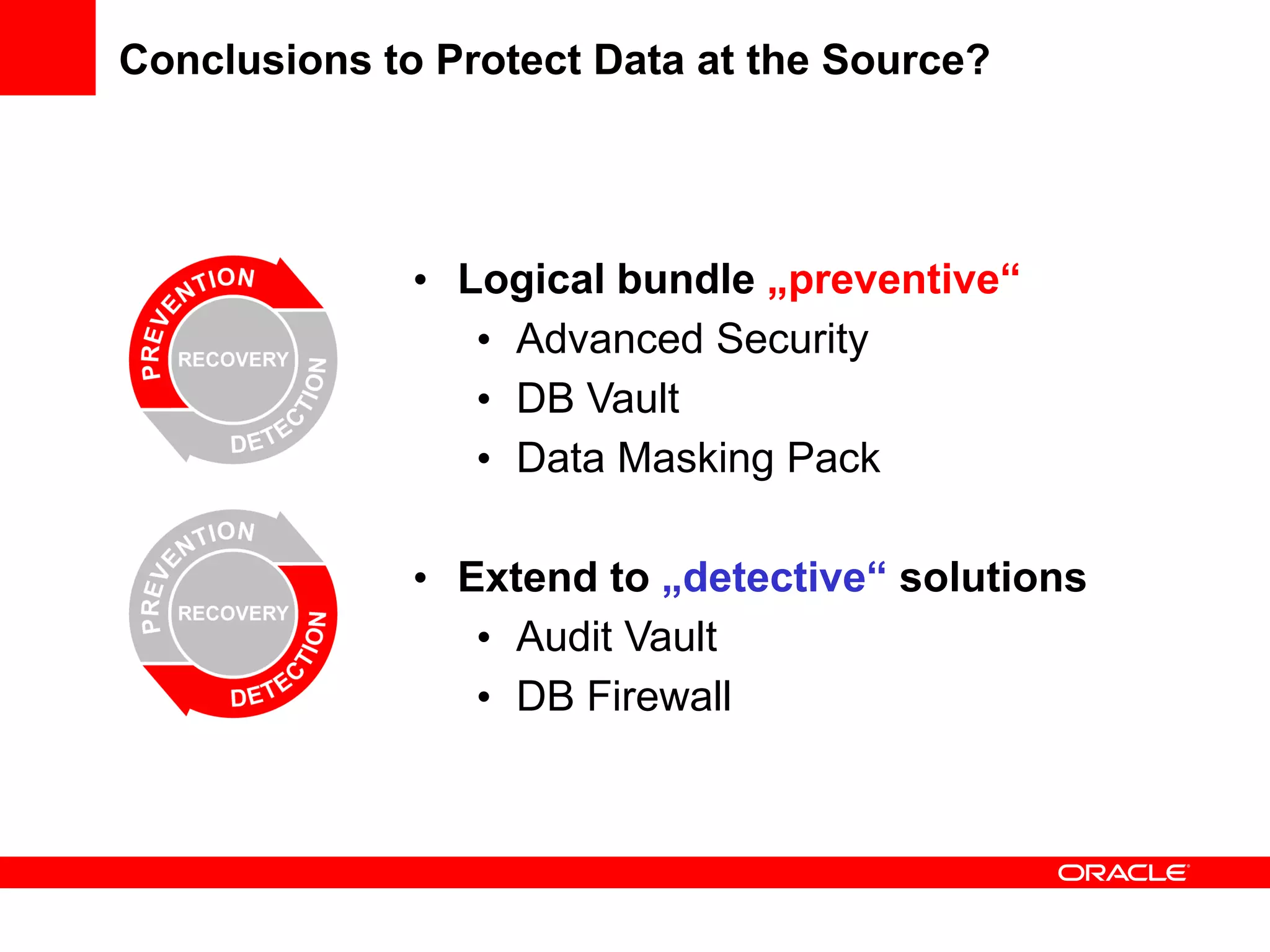
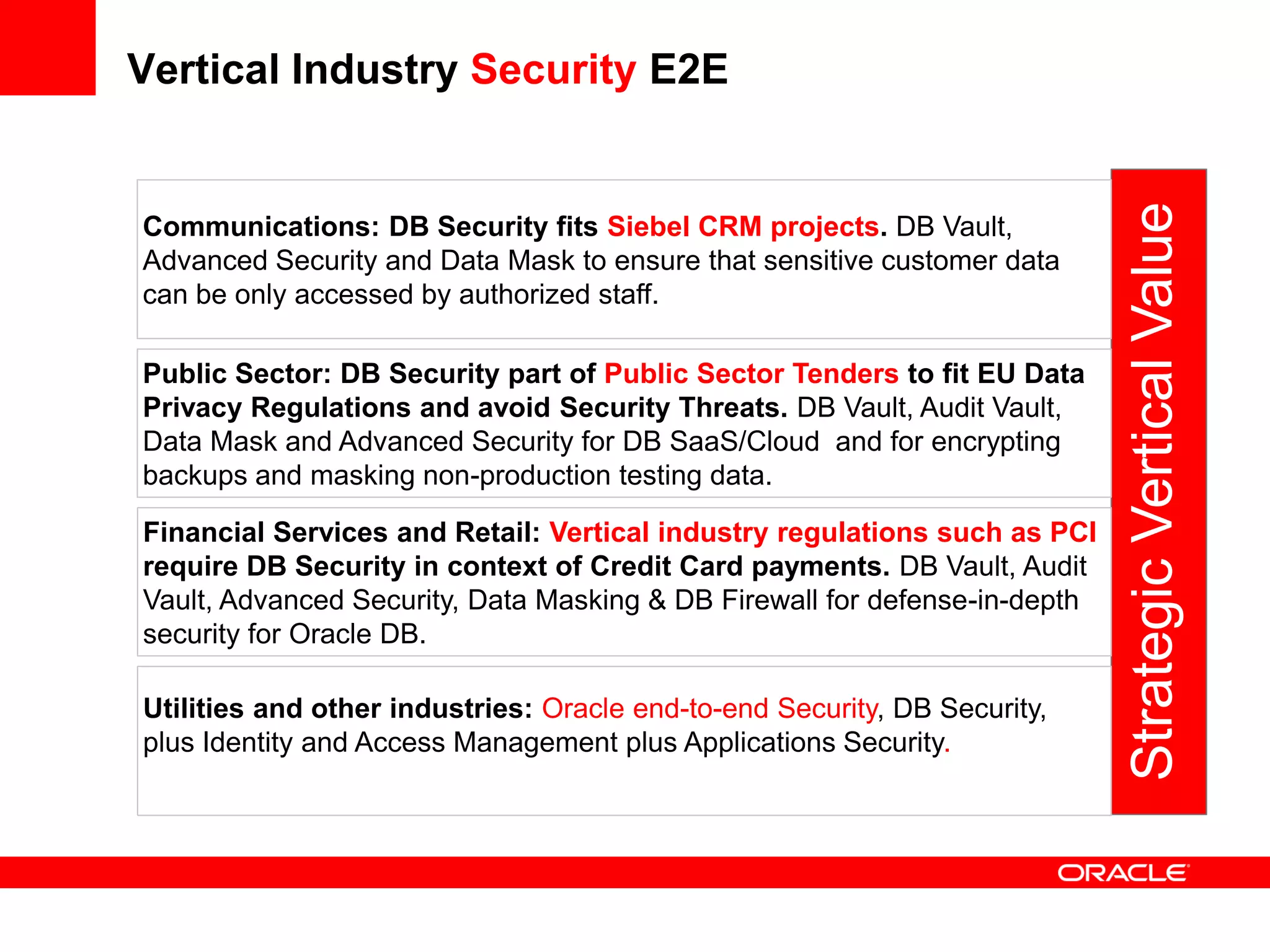
This document outlines Oracle's product direction for data security at the source in public and private sectors. It discusses business drivers for security such as governance, risk management and compliance needs as well as security threats. It then describes Oracle's database security solutions like Transparent Data Encryption, Database Vault, and Audit Vault that secure data at rest, in motion and for testing. Case studies show how customers in various industries like banking, telecom, and public sectors have implemented Oracle's database security to protect sensitive data and comply with regulations. The document concludes that Oracle's database security solutions provide a preventive and detective approach to protect data at the source.