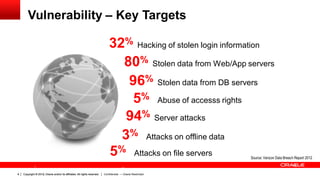
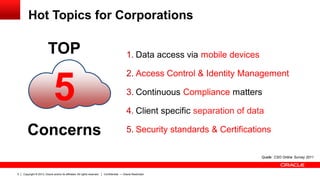
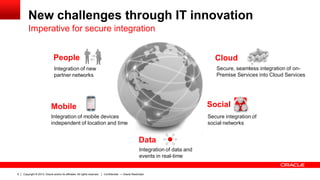
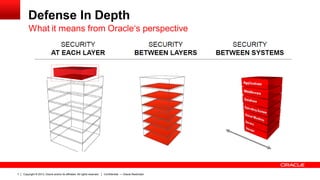
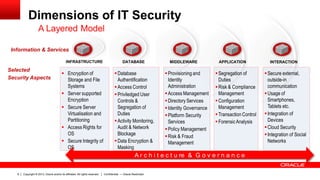
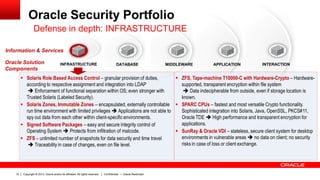
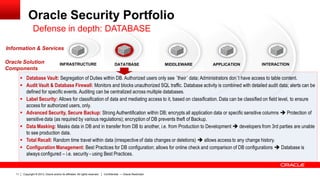
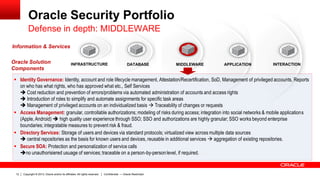
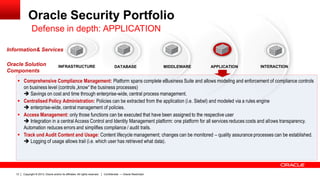
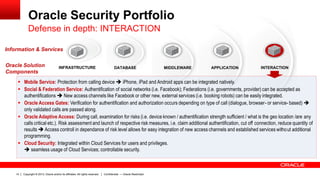
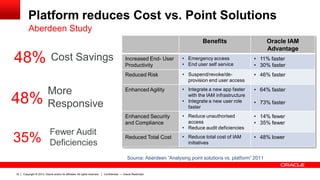
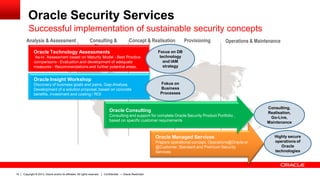
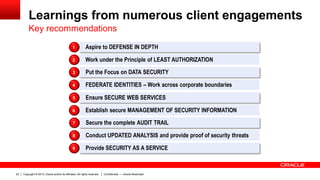
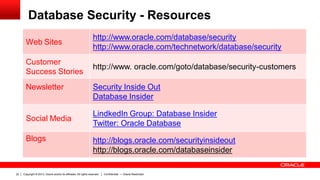
This document discusses Oracle security solutions. It begins with an overview of recent security breaches and their causes and consequences. It then discusses Oracle's defense-in-depth approach to security across infrastructure, database, middleware, applications, and interactions. The document outlines Oracle's security portfolio and components across these areas. It notes benefits to customers such as cost savings, compliance support, and integration capabilities. It concludes with recommendations based on lessons from client engagements and references Oracle security resources.