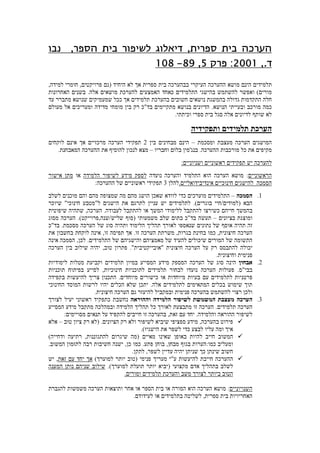
נבו פרק 5 הערכת תלמידים
•Download as DOCX, PDF•
0 likes•1,552 views
The document outlines steps for conducting a risk assessment of a company's IT infrastructure, including identifying key assets, threats, and vulnerabilities. It recommends interviewing stakeholders to understand potential risks, then analyzing impact and likelihood to prioritize risks. Finally, it suggests documenting the assessment and creating a risk treatment plan to address high priority risks.
Report
Share
Report
Share
More Related Content
What's hot
What's hot (20)
Mobile Marketing: 5 Reasons to Care & 7 Steps to Integrate

Mobile Marketing: 5 Reasons to Care & 7 Steps to Integrate
Social recruitment-strategy-case-study-ellis-jones-final

Social recruitment-strategy-case-study-ellis-jones-final
Viewers also liked
Viewers also liked (6)
More from Shaby Haim
More from Shaby Haim (20)
Recently uploaded
Mattingly "AI & Prompt Design: Limitations and Solutions with LLMs"

Mattingly "AI & Prompt Design: Limitations and Solutions with LLMs"National Information Standards Organization (NISO)
Recently uploaded (20)
Keeping Your Information Safe with Centralized Security Services

Keeping Your Information Safe with Centralized Security Services
MARUTI SUZUKI- A Successful Joint Venture in India.pptx

MARUTI SUZUKI- A Successful Joint Venture in India.pptx
Sectors of the Indian Economy - Class 10 Study Notes pdf

Sectors of the Indian Economy - Class 10 Study Notes pdf
Telling Your Story_ Simple Steps to Build Your Nonprofit's Brand Webinar.pdf

Telling Your Story_ Simple Steps to Build Your Nonprofit's Brand Webinar.pdf
Jose-Rizal-and-Philippine-Nationalism-National-Symbol-2.pptx

Jose-Rizal-and-Philippine-Nationalism-National-Symbol-2.pptx
Basic Civil Engg Notes_Chapter-6_Environment Pollution & Engineering

Basic Civil Engg Notes_Chapter-6_Environment Pollution & Engineering
Basic phrases for greeting and assisting costumers

Basic phrases for greeting and assisting costumers
Mattingly "AI & Prompt Design: Limitations and Solutions with LLMs"

Mattingly "AI & Prompt Design: Limitations and Solutions with LLMs"
slides CapTechTalks Webinar May 2024 Alexander Perry.pptx

slides CapTechTalks Webinar May 2024 Alexander Perry.pptx
