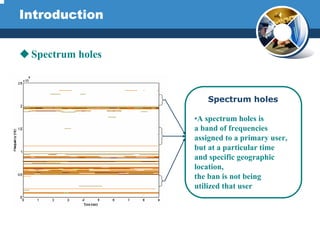
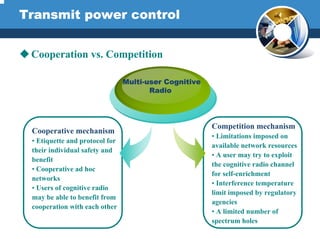
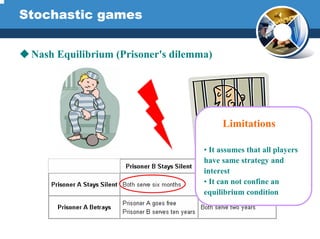
Cognitive radio is an intelligent wireless communication system that is aware of its environment and can learn and adapt to better utilize available spectrum. It aims for highly reliable communication and efficient spectrum usage. Cognitive radios use radio scene analysis to detect spectrum holes by analyzing signals over time and space. They also estimate interference temperature using spectral estimation and adaptive beamforming. Transmit power control and dynamic spectrum management allow cognitive radios to opportunistically access spectrum holes while avoiding interference. Future work may focus on language understanding, MIMO techniques, and nanoscale processing to improve cognitive radio capabilities.