This document describes configuring PVST+ spanning tree protocol on a network topology. It involves:
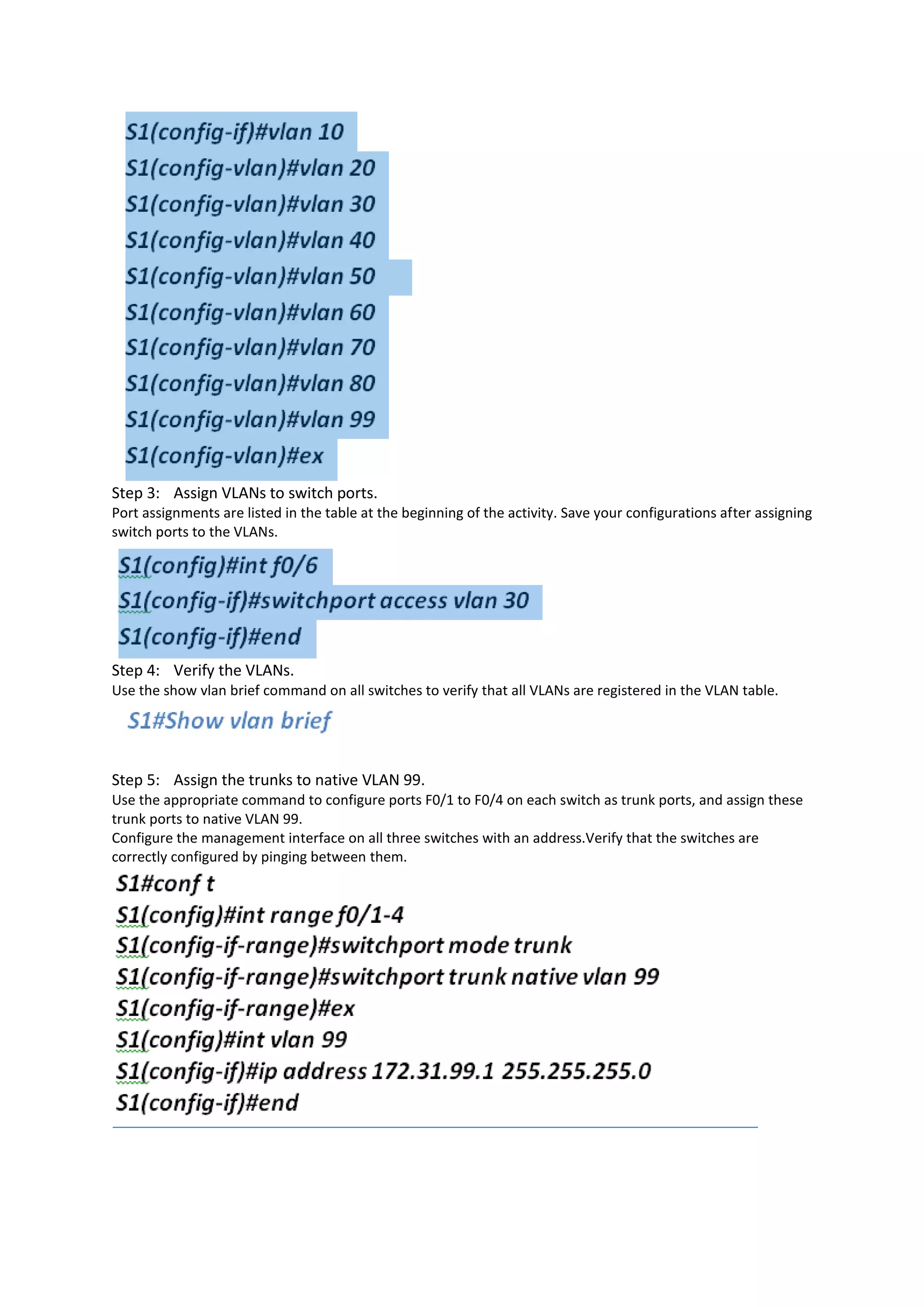
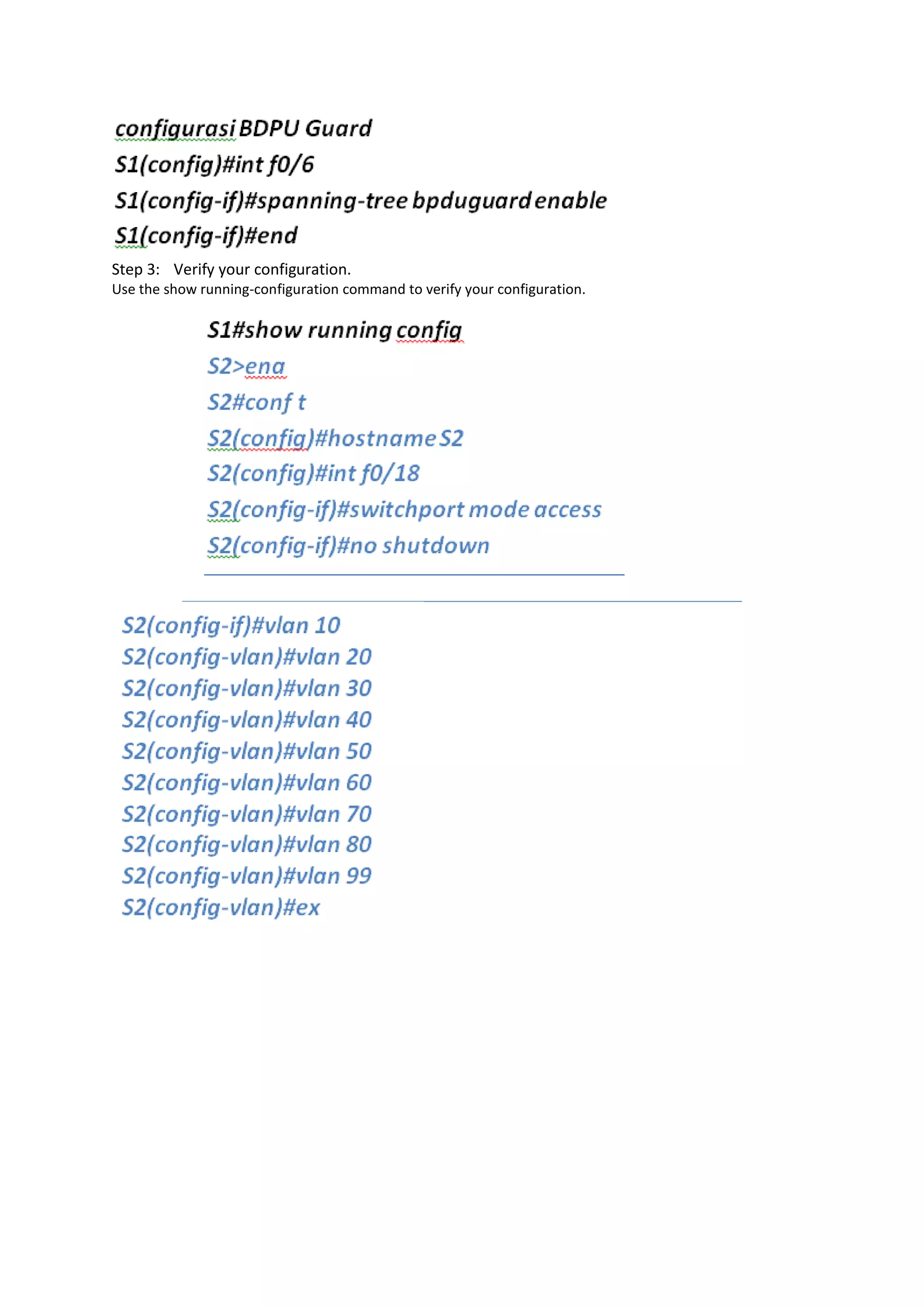
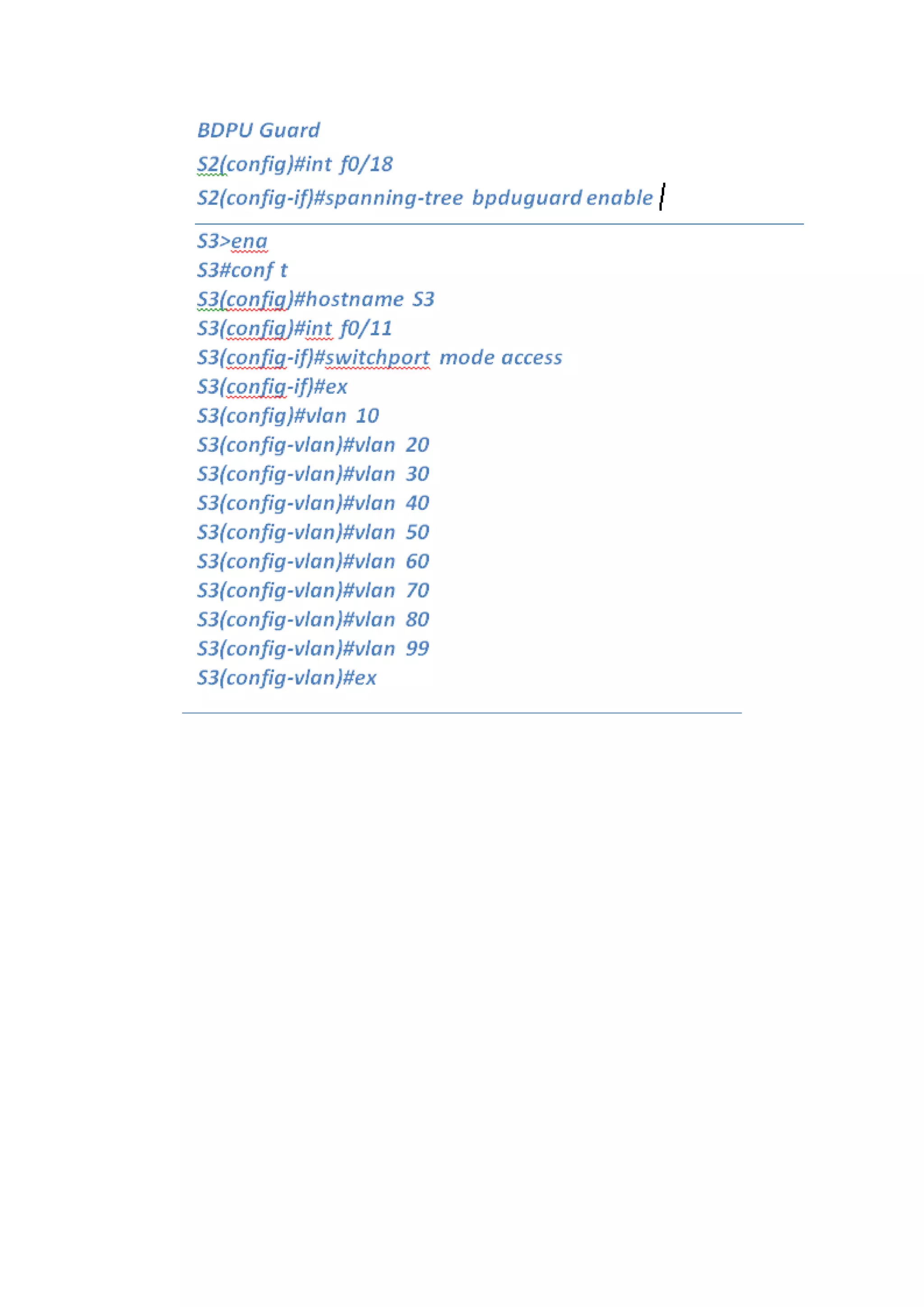
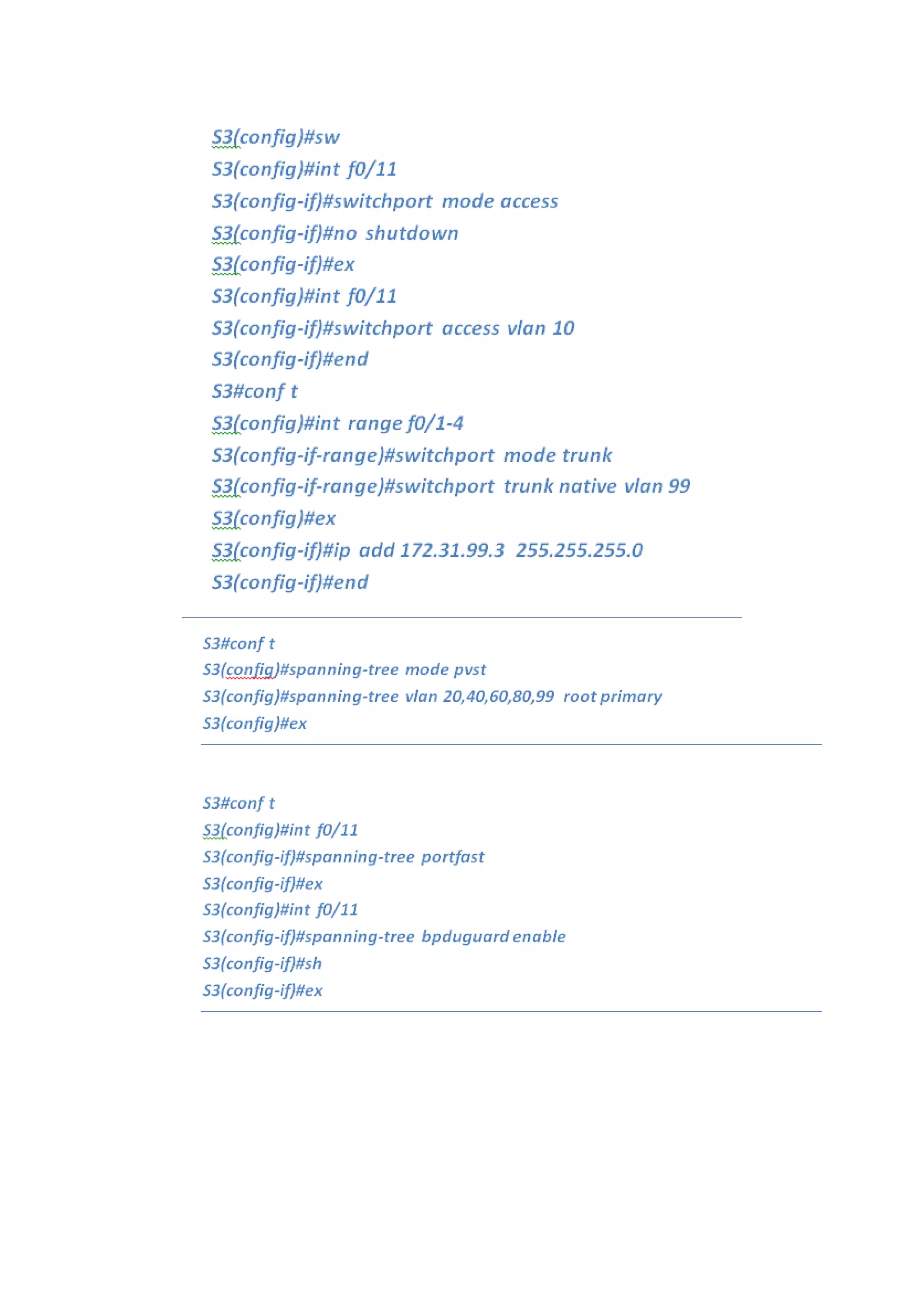
1. Configuring VLANs, trunk ports between switches, and IP addresses for switch management.
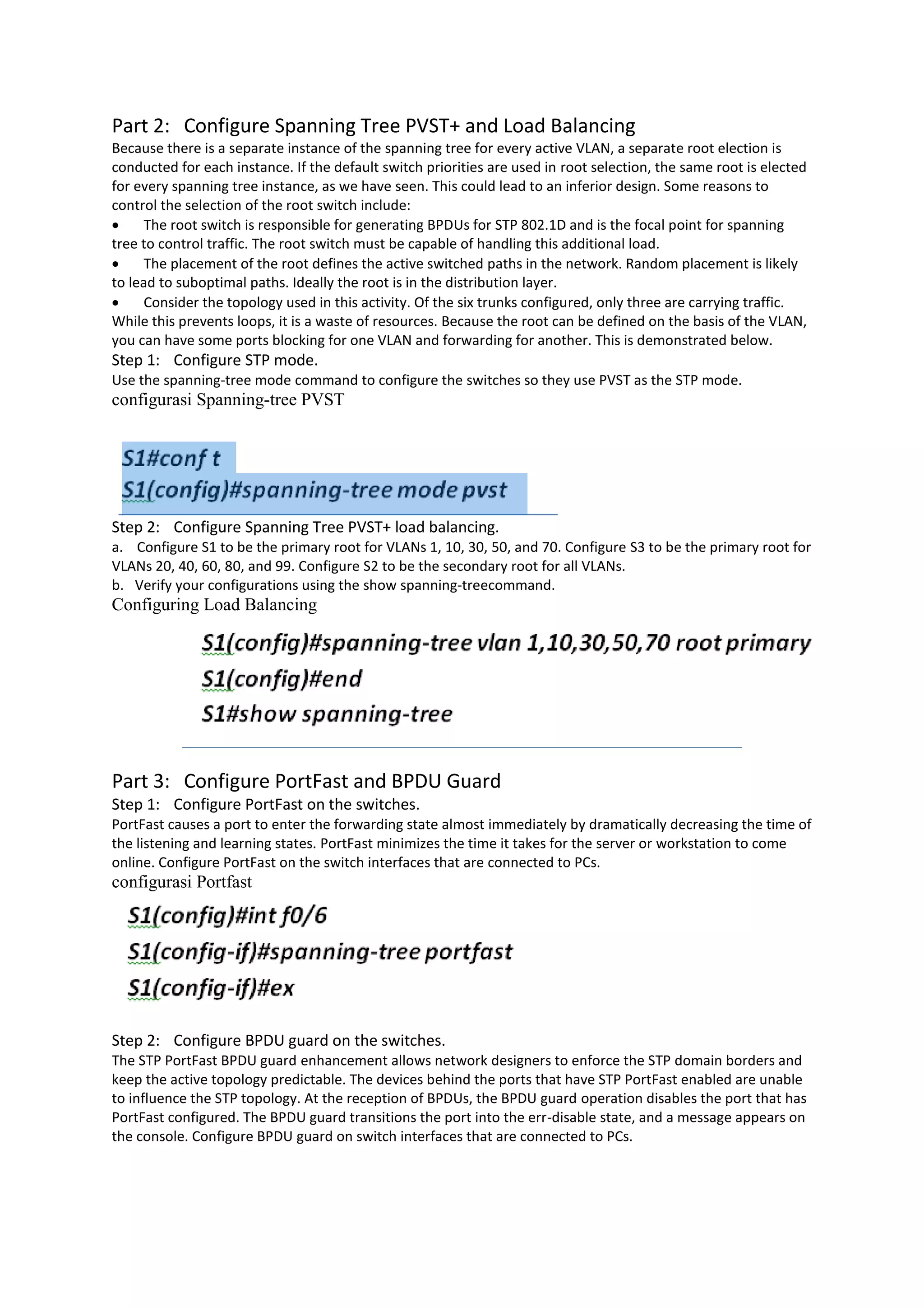
2. Optimizing the spanning tree configuration by making one switch the primary root for certain VLANs and another the secondary root to load balance traffic across trunks.
3. Enabling PortFast on end-user ports to quickly forward traffic and BPDU guard to protect against devices connected to those ports influencing the spanning tree.