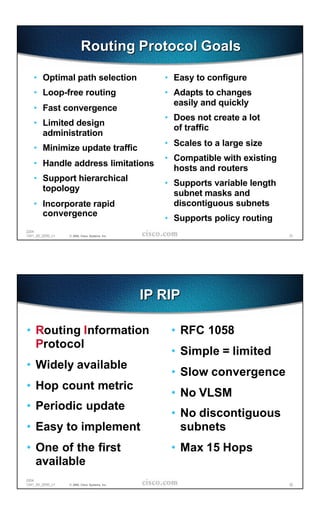
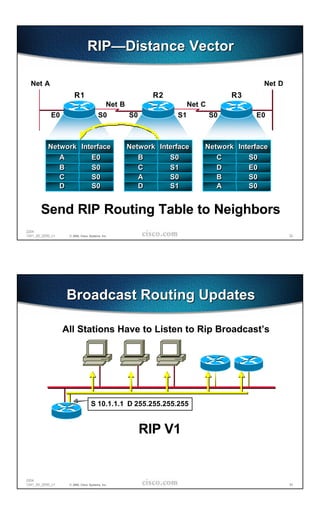
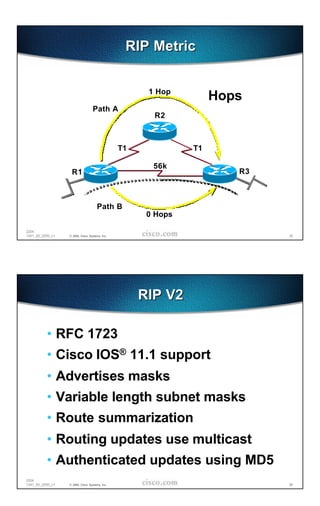
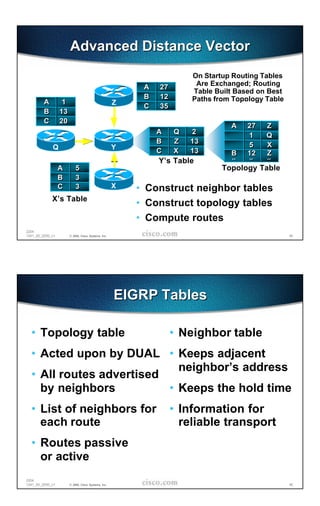
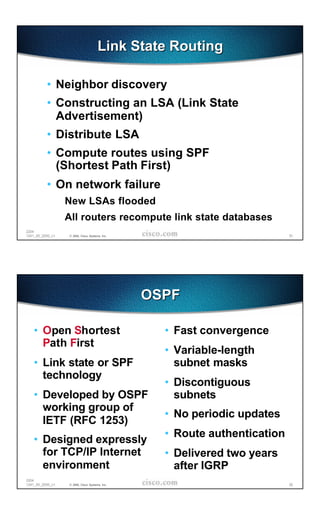
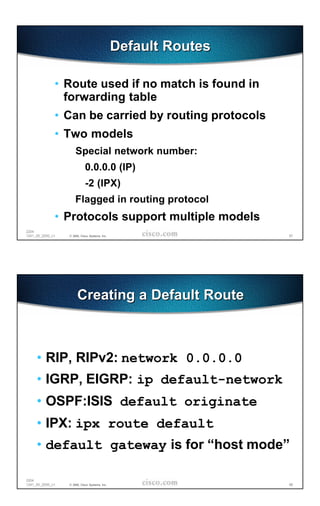
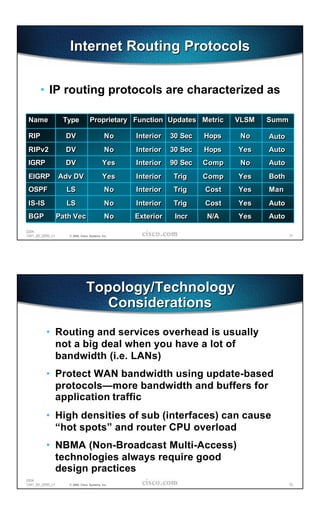
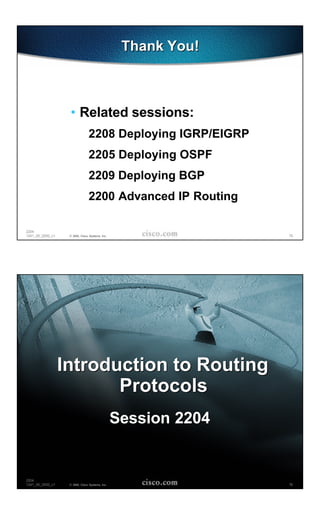
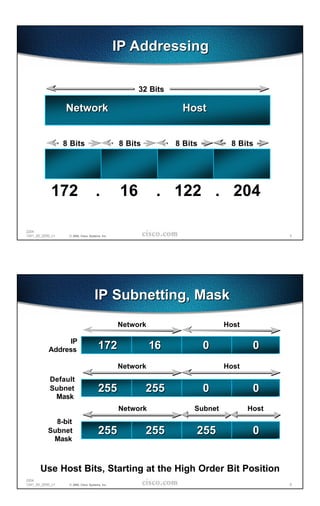
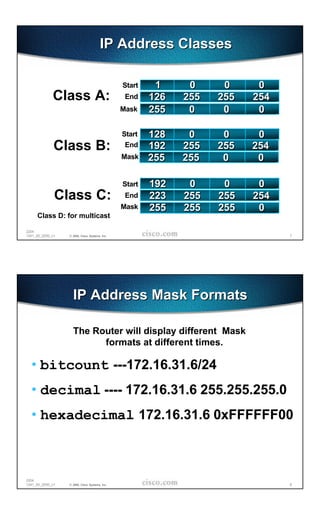
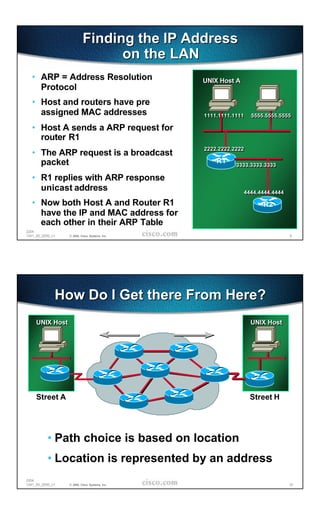
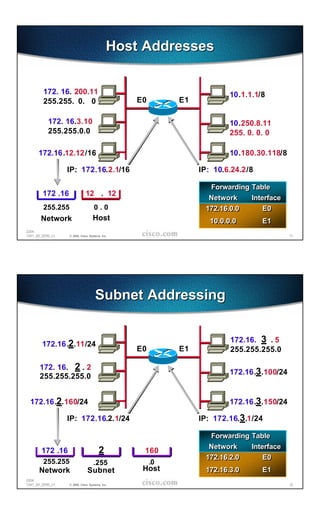
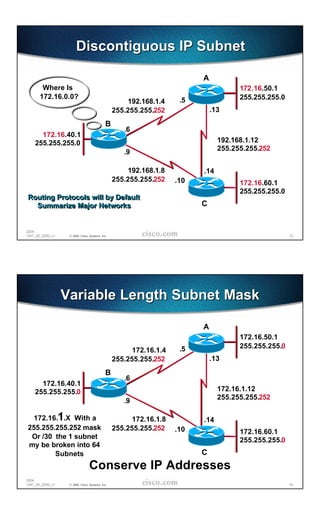
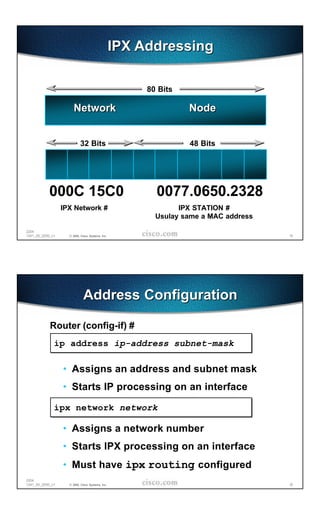
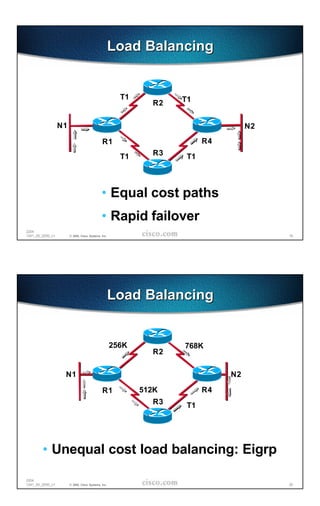
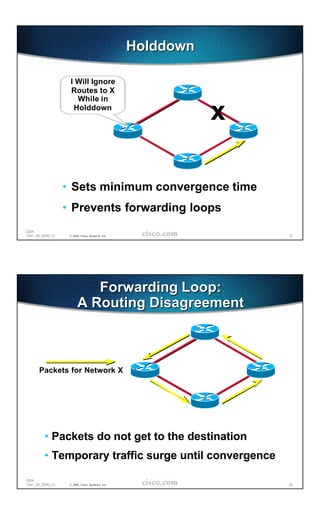
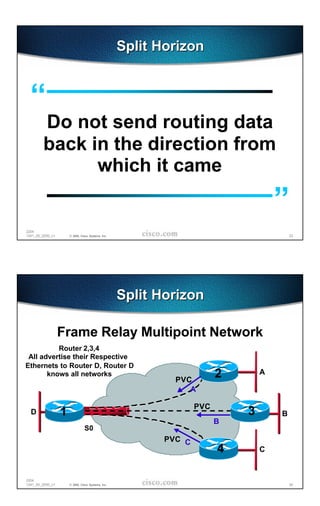
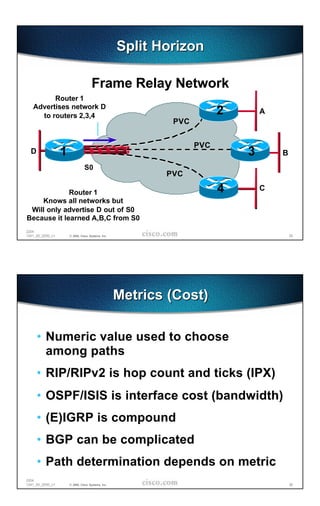
The document provides an overview of routing protocols and IP addressing concepts. It discusses MAC addresses, IP addressing including classes and subnetting, IPX addressing, and routing fundamentals such as forwarding tables, convergence, metrics, and routing protocols. Specific protocols covered include RIP, with details on distance vector routing. The overall agenda is to introduce IP and IPX addressing, generic routing concepts, specific routing protocols, and static and default routes.
![Agenda
• IP, IPX Addressing Concepts
• Generic Routing Categories
• Specific Routing Protocols
• Static and Defaults Routes
2204
1241_05_2000_c1 © 2000, Cisco Systems, Inc. 27
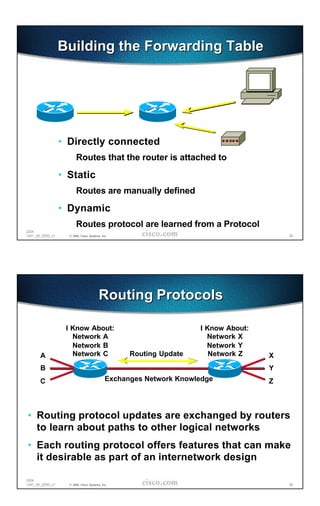
Forwarding Table
One Forwarding Table per Router
One Forwarding Table per Network Protocol
Network # Interface Next Hop Metric Age Source
198.113.181.0 Ethernet0 192.150.42.177 [170/304793] 02:03:50 D
198.113.178.0 Ethernet0 192.150.42.177 [110/9936] 02:03:50 O
192.168.96.0 Ethernet0 192.150.42.177 [120/3] 00:00:20 R
192.168.97.0 Ethernet0 C
2204
1241_05_2000_c1 © 2000, Cisco Systems, Inc. 28](https://image.slidesharecdn.com/2204-100408021037-phpapp02/85/2204-14-320.jpg)