This document reviews wireless spy device (WSD) technologies and methods for detecting WSDs. It discusses:
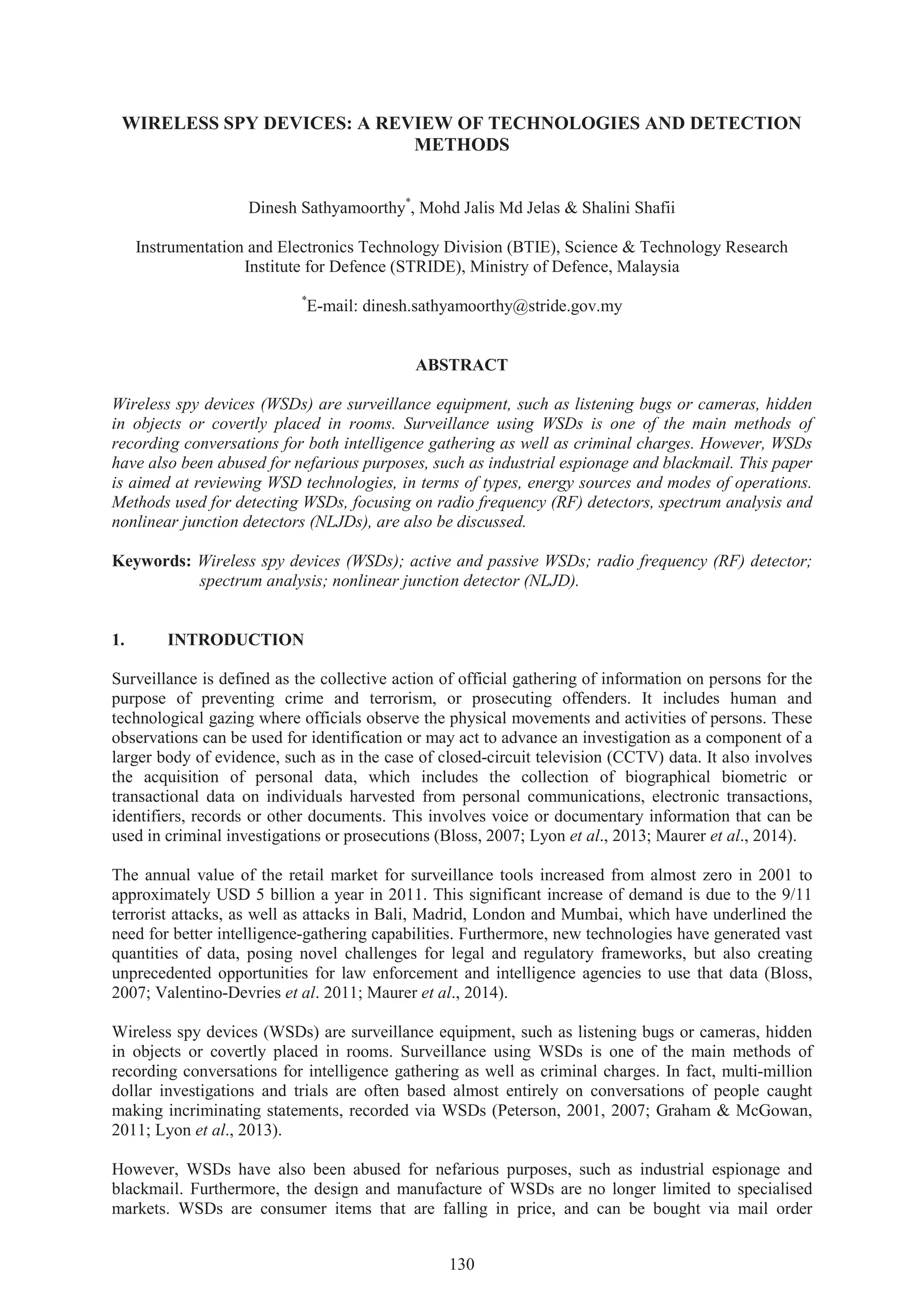
1) Types of WSDs including active devices that transmit signals and passive devices that only record data.
2) Detection methods for active WSDs including radio frequency (RF) detectors and spectrum analysis to identify transmitted signals.
3) Use of nonlinear junction detectors to detect passive WSDs by analyzing harmonic signals generated from semiconductor junctions when illuminated with RF signals.