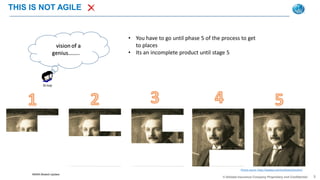
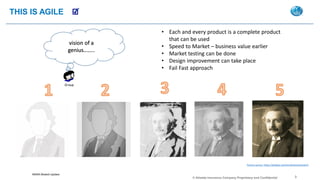
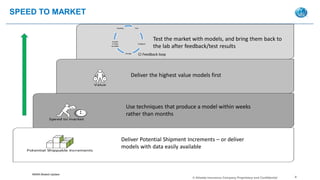
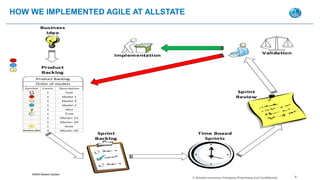
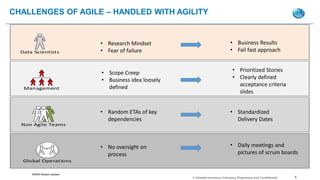
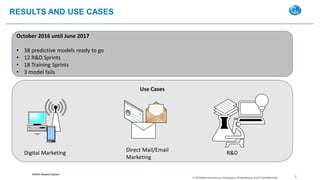
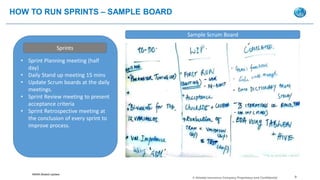
The document discusses implementing an agile approach to developing predictive models at Allstate Insurance. It outlines how agile allows for more incremental and iterative development, with the ability to test and improve models more quickly. An agile process was adopted with sprints, backlogs, and daily standup meetings. This resulted in 38 predictive models being developed over 12 research and development sprints within 10 months, with only 3 model failures, allowing for faster delivery of business value.