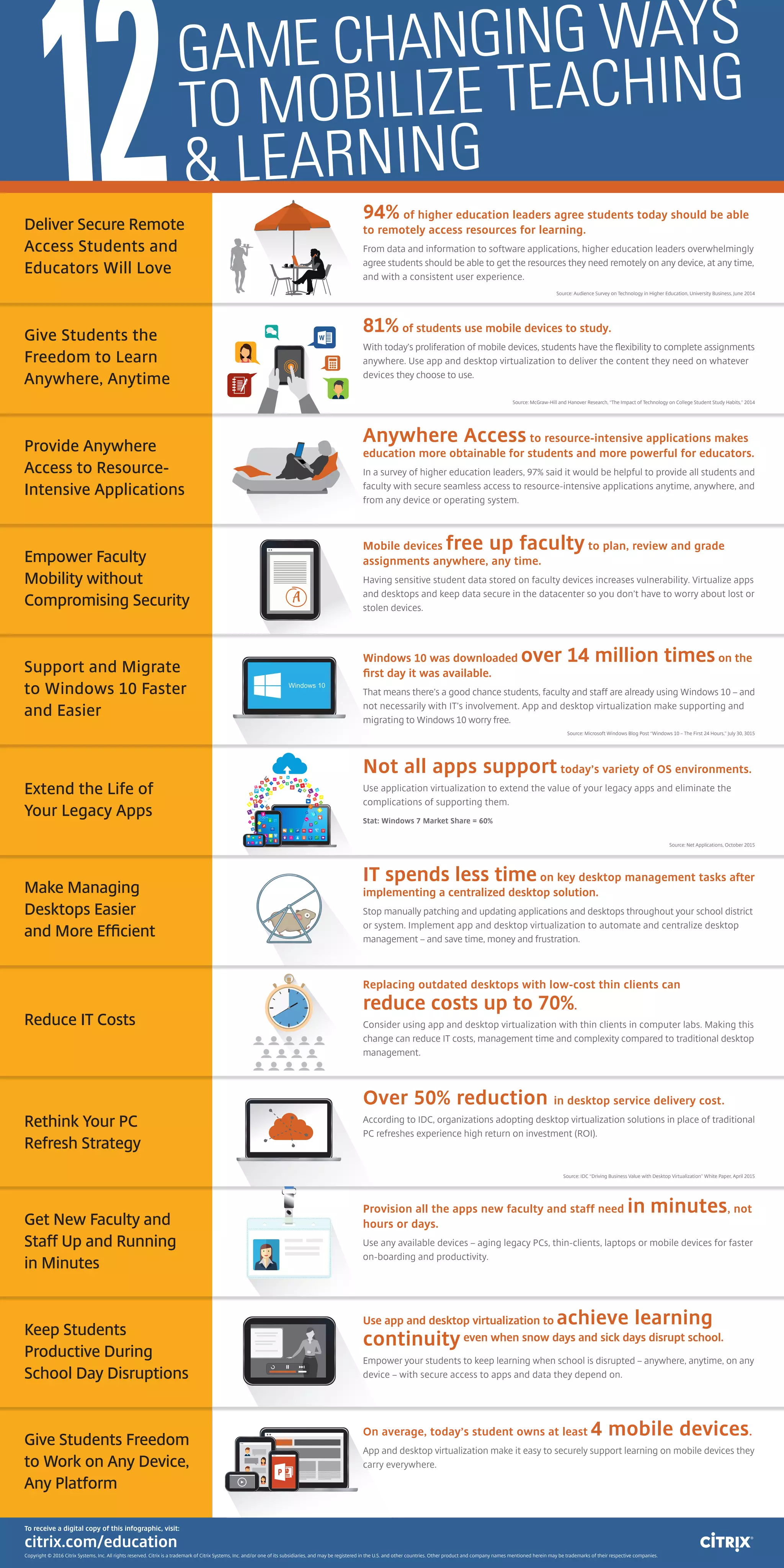
The document discusses how application virtualization can extend the life of legacy applications and avoid complications of supporting different operating systems. It notes that Windows 7 currently has a 60% market share, and promotes the benefits of application and desktop virtualization for education institutions, such as increased mobility and security, lower costs, and easier management and support across devices and platforms.