This document provides an overview of querying and managing data using SQL Server 2005. It discusses managed code, creating managed database objects like stored procedures and functions, and implementing web services. The key points are:
- Managed code allows writing code in .NET languages and running it within a database. It is useful for complex logic, external resource access, and CPU-intensive tasks.
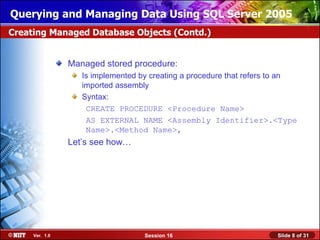
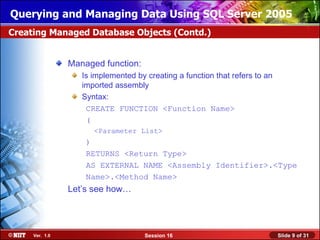
- Assemblies containing managed code are imported using CREATE ASSEMBLY. Managed database objects like procedures and functions are then created referring to the imported assemblies.
- Web services in SQL Server 2005 use HTTP, SOAP, and WSDL standards to provide programmable logic over the internet.
![Querying and Managing Data Using SQL Server 2005
Importing and Configuring Assemblies
Assemblies:
Are created to attach the managed code
Are created using the CREATE ASSEMBLY command
Syntax:
CREATE ASSEMBLY assembly_name
FROM { <client_assembly_specifier> |
<assembly_bits>
[ ,...n ] }
[ WITH PERMISSION_SET =
{ SAFE | EXTERNAL_ACCESS | UNSAFE } ]
Let’s see how…
Ver. 1.0 Session 16 Slide 5 of 31](https://image.slidesharecdn.com/11qmds2005session16-120420160224-phpapp01/85/11-qmds2005-session16-5-320.jpg)
![Querying and Managing Data Using SQL Server 2005
Creating Managed Database Objects (Contd.)
Managed user-defined type:
Is created by using the CREATE TYPE command
Syntax:
CREATE TYPE [ schema_name. ] type_name
{
FROM base_type [ (precision [ , scale ] ) ]
[ NULL | NOT NULL ]
| EXTERNAL NAME assembly_name[.class_name]
}
Let’s see how…
Ver. 1.0 Session 16 Slide 11 of 31](https://image.slidesharecdn.com/11qmds2005session16-120420160224-phpapp01/85/11-qmds2005-session16-11-320.jpg)
![Querying and Managing Data Using SQL Server 2005
Creating HTTP Endpoints (Contd.)
Syntax:
CREATE ENDPOINT endpoint_name
STATE = { STARTED | STOPPED | DISABLED }
AS HTTP (
AUTHENTICATION =( { BASIC | DIGEST |
INTEGRATED | NTLM | KERBEROS },
PATH = 'url', PORTS = (CLEAR) )
FOR SOAP(
[ { WEBMETHOD [ 'namespace' .] 'method_alias'
( NAME = 'database.owner.name'
[ , SCHEMA = { NONE | STANDARD | DEFAULT } ]
[ , FORMAT = { ALL_RESULTS | ROWSETS_ONLY } ])
} [ ,...n ] ]
[ BATCHES = { ENABLED | DISABLED } ]
[ , WSDL = { NONE | DEFAULT | 'sp_name' } ]
Let’s see how…
Ver. 1.0 Session 16 Slide 23 of 31](https://image.slidesharecdn.com/11qmds2005session16-120420160224-phpapp01/85/11-qmds2005-session16-23-320.jpg)