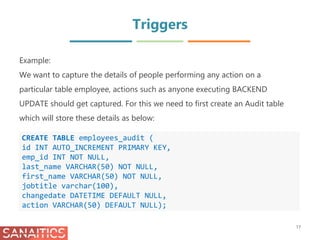
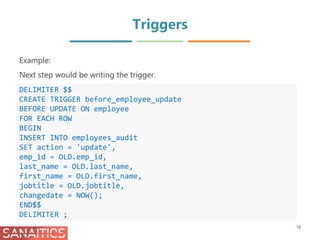
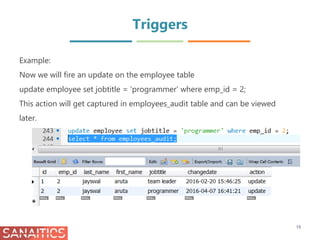
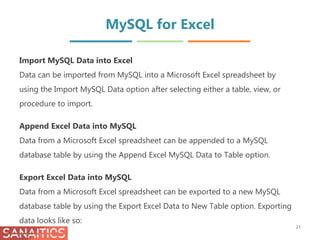
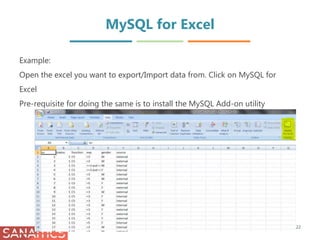
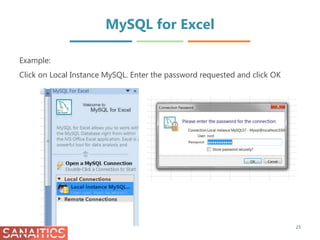
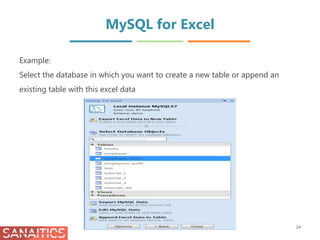
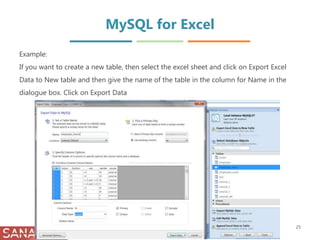
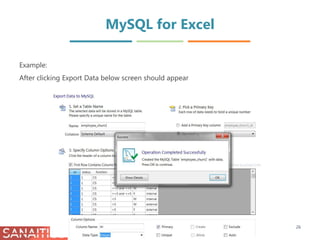
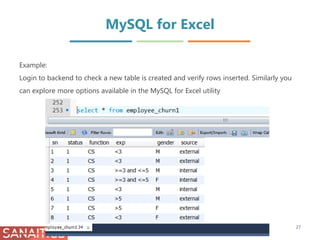
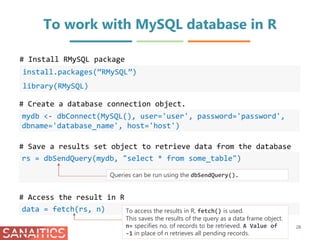
The document discusses database views in MySQL. It provides information on creating views using the CREATE VIEW and CREATE OR REPLACE VIEW statements. Views allow simplifying complex queries, limiting data access, and providing extra security. Performance can be impacted when querying views defined on other views. Views also introduce dependency on the underlying tables. Stored procedures in MySQL are also discussed, including their advantages like increased performance and security, and disadvantages like increased memory usage. Triggers are described as stored programs that execute automatically in response to data changes and can be used for auditing and validation. Examples are provided on creating a trigger for auditing table updates and accessing MySQL from Excel.

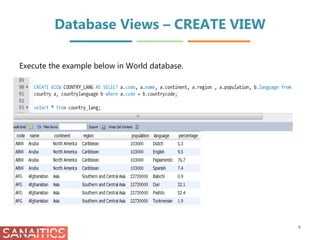
![Database Views – CREATE VIEW
4
Syntax:
CREATE
VIEW [database_name].[view_name]
AS
[SELECT statement]
There are some rules that the SELECT statement must follow:
• The SELECT statement can contain a subquery in WHERE clause but not in
the FROM clause.
• The SELECT statement cannot refer to any variables including local
variables, user variables, and session variables.](https://image.slidesharecdn.com/gettingstartedwithmysqlii-170925105849/85/Getting-Started-with-MySQL-II-4-320.jpg)
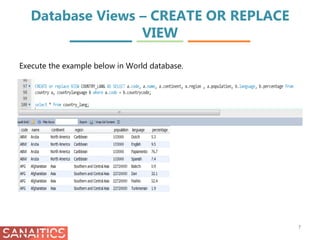
![Database Views – CREATE OR REPLACE
VIEW
5
You can use CREATE OR REPLACE VIEW statement to either create or replace
an existing view. If a view already exists, MySQL simply modifies the view. In
case the view does not exist, MySQL creates a new view.
Syntax:
CREATE OR REPLACE
VIEW [database_name].[view_name]
AS
[SELECT statement]](https://image.slidesharecdn.com/gettingstartedwithmysqlii-170925105849/85/Getting-Started-with-MySQL-II-5-320.jpg)