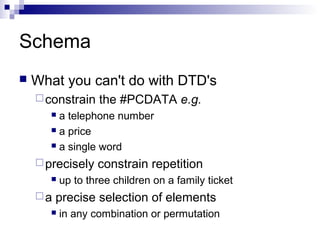
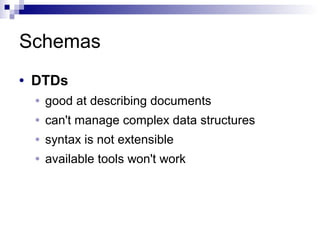
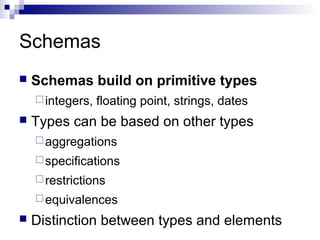
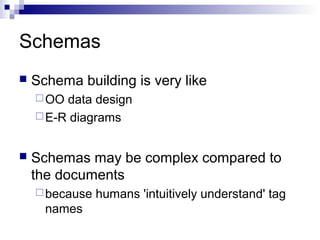
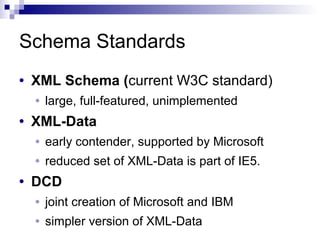
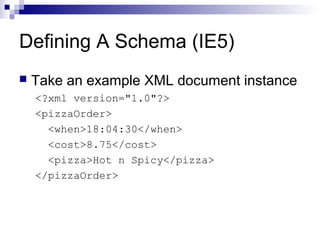
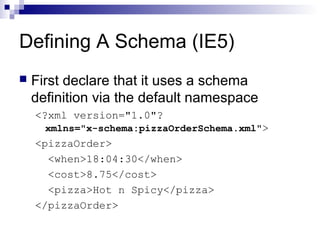
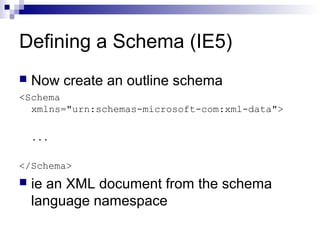
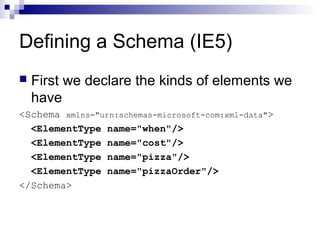
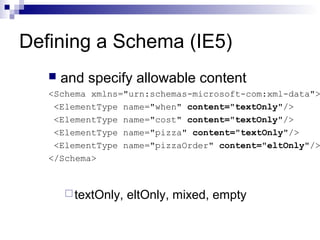
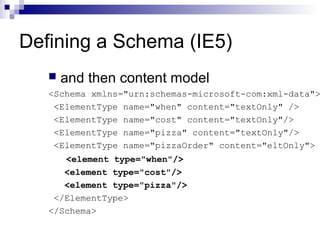
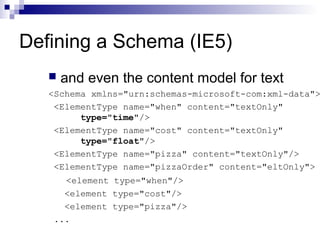
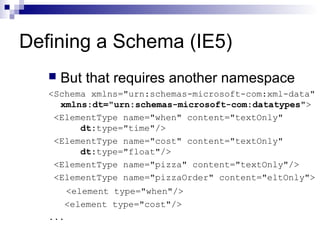
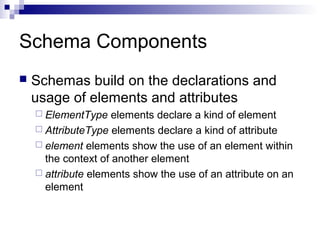
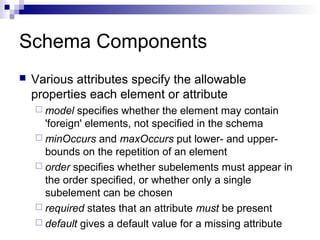
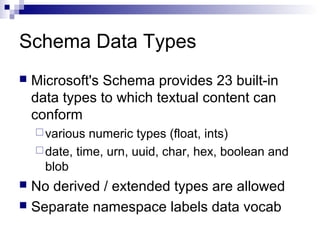
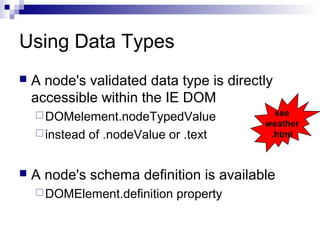
The document discusses schemas and their purpose in specifying the structure and constraints of an XML document. It provides examples of things that cannot be done with DTDs but can be done with schemas, such as constraining text values. The document outlines the components of a schema, including elements, attributes, and data types. It provides an example of defining a schema in IE5 and the steps involved, including declaring element types, specifying content models, and using data types.