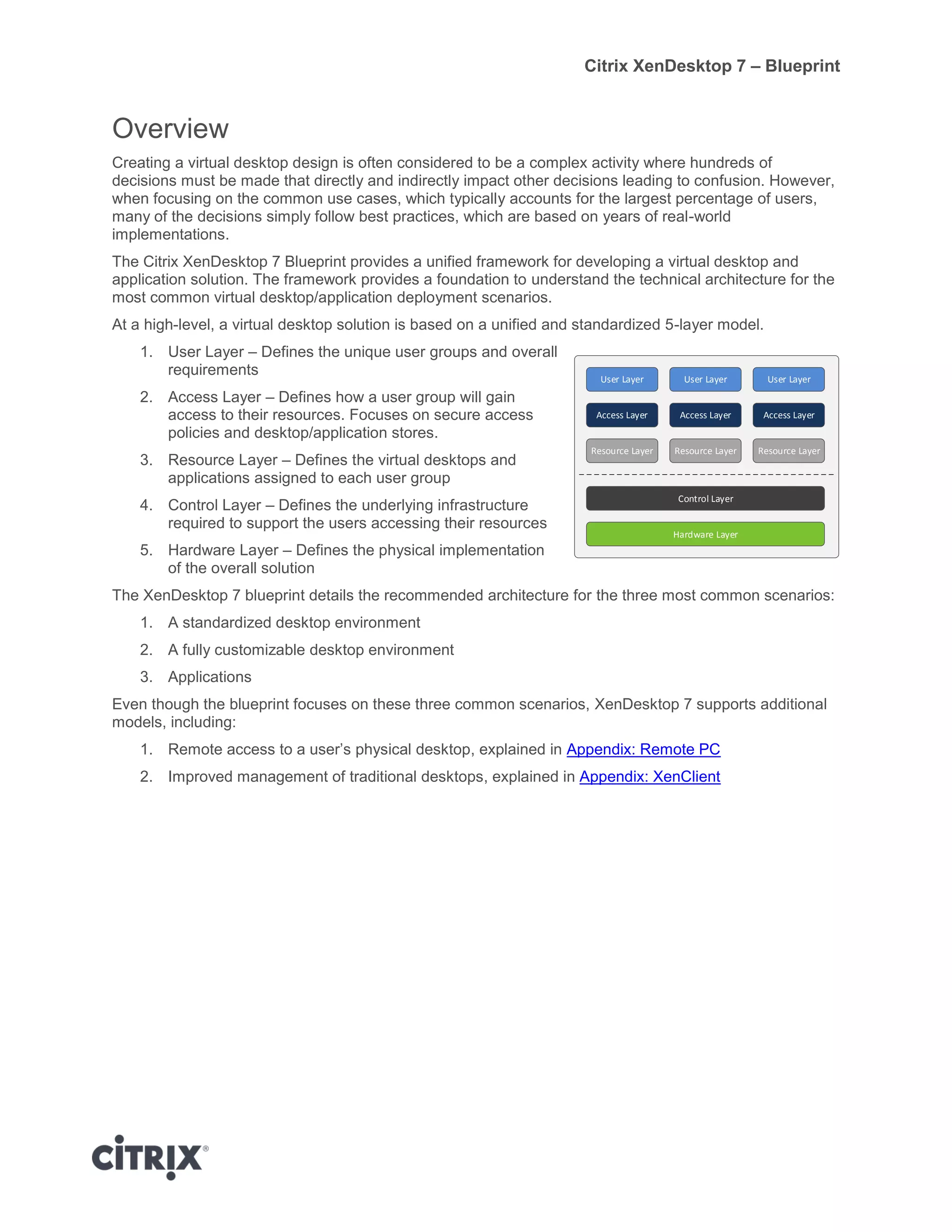
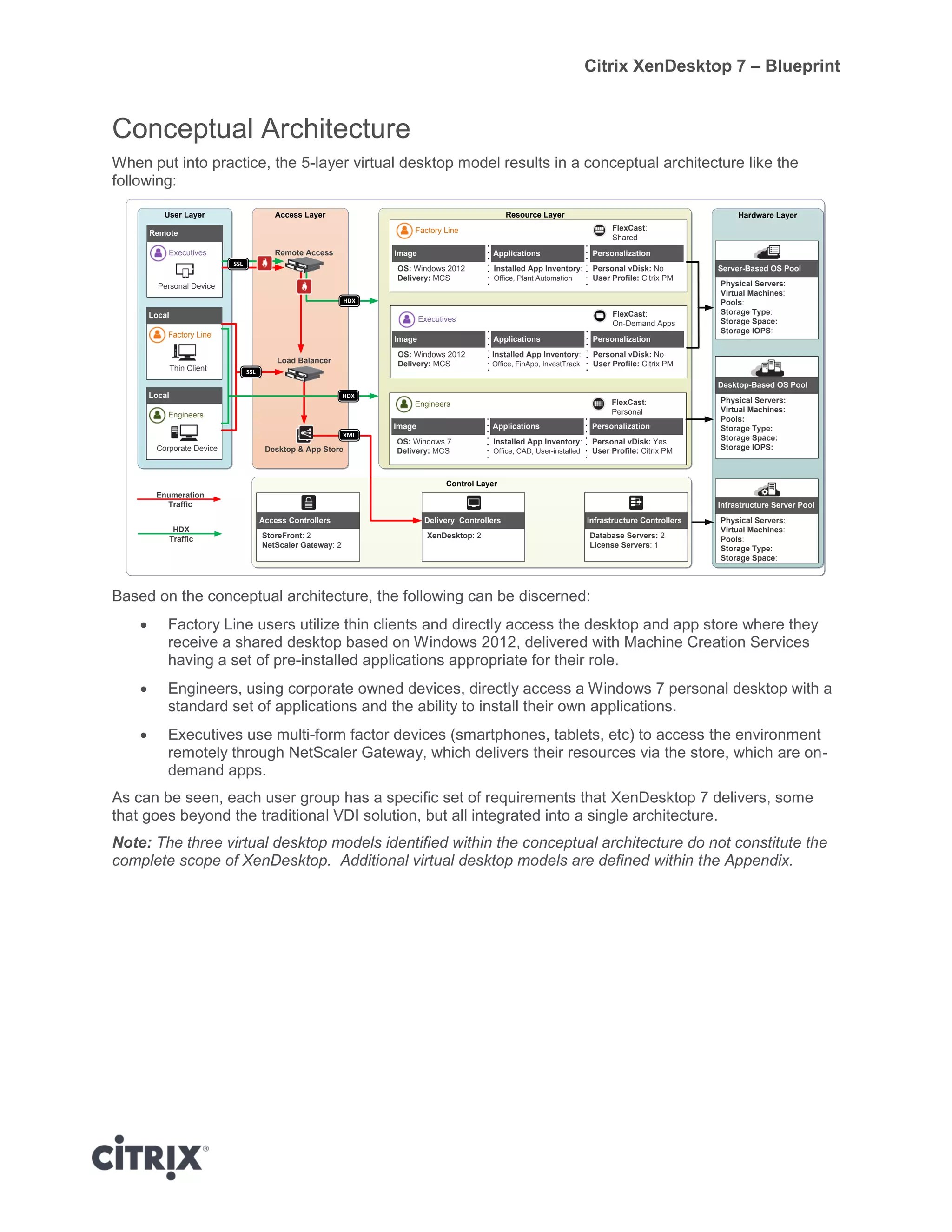
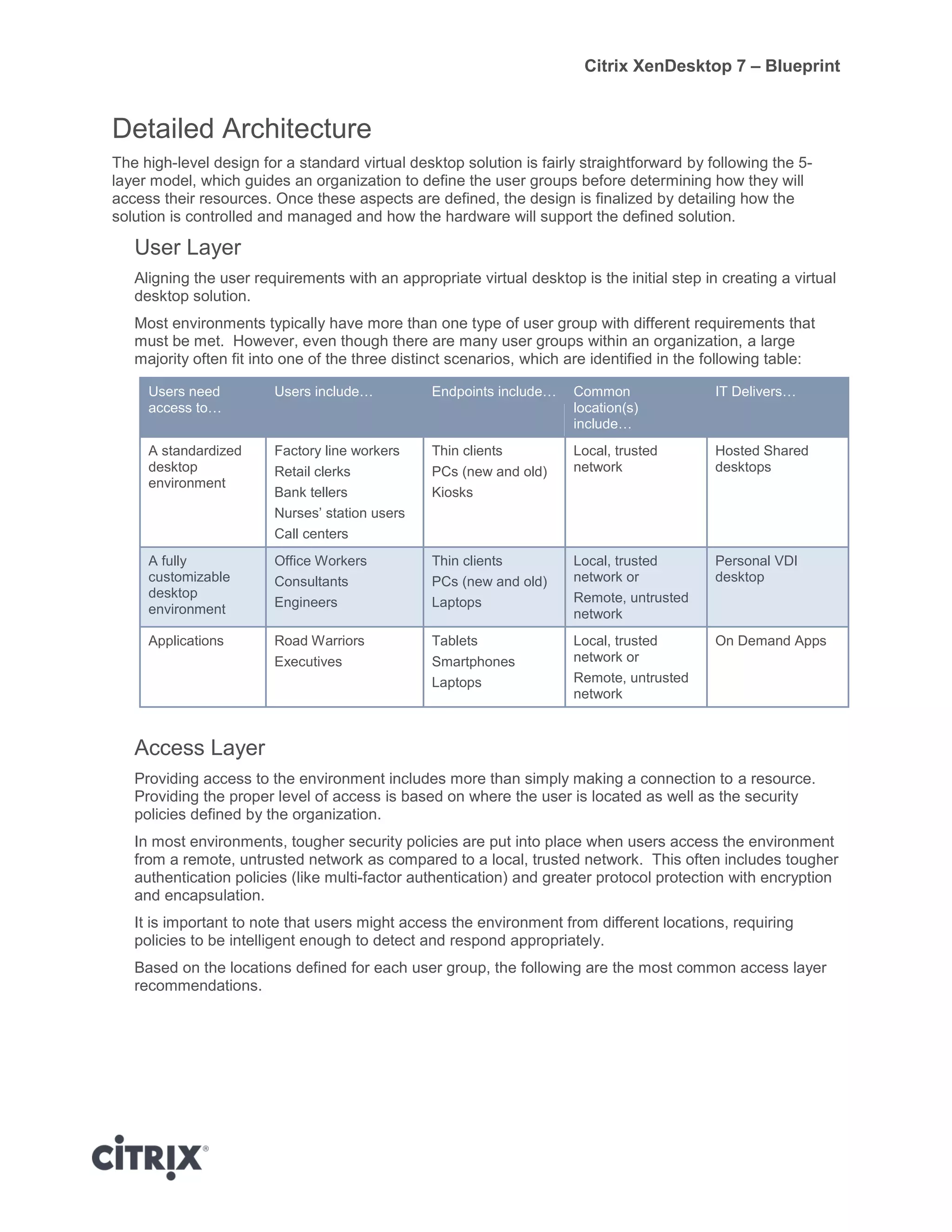
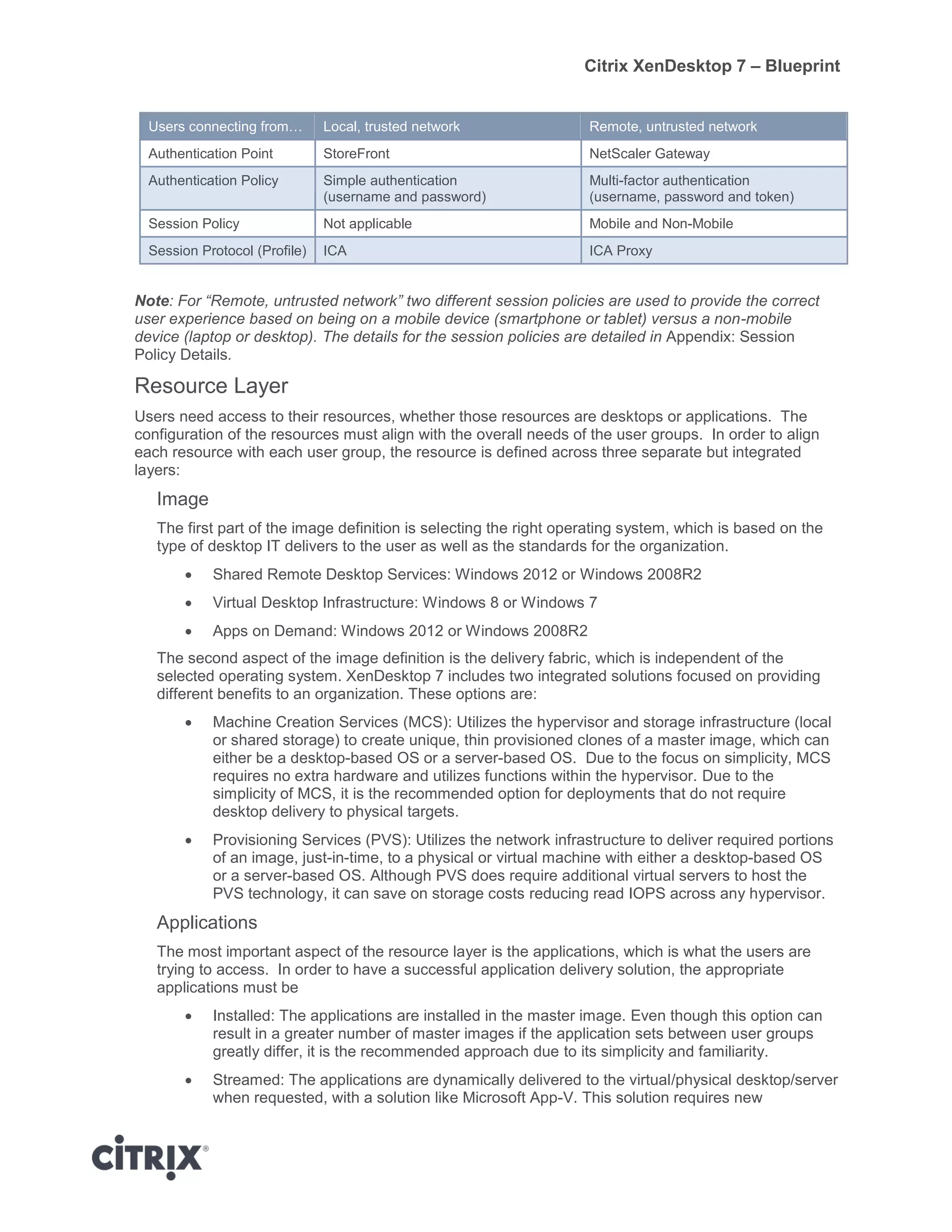
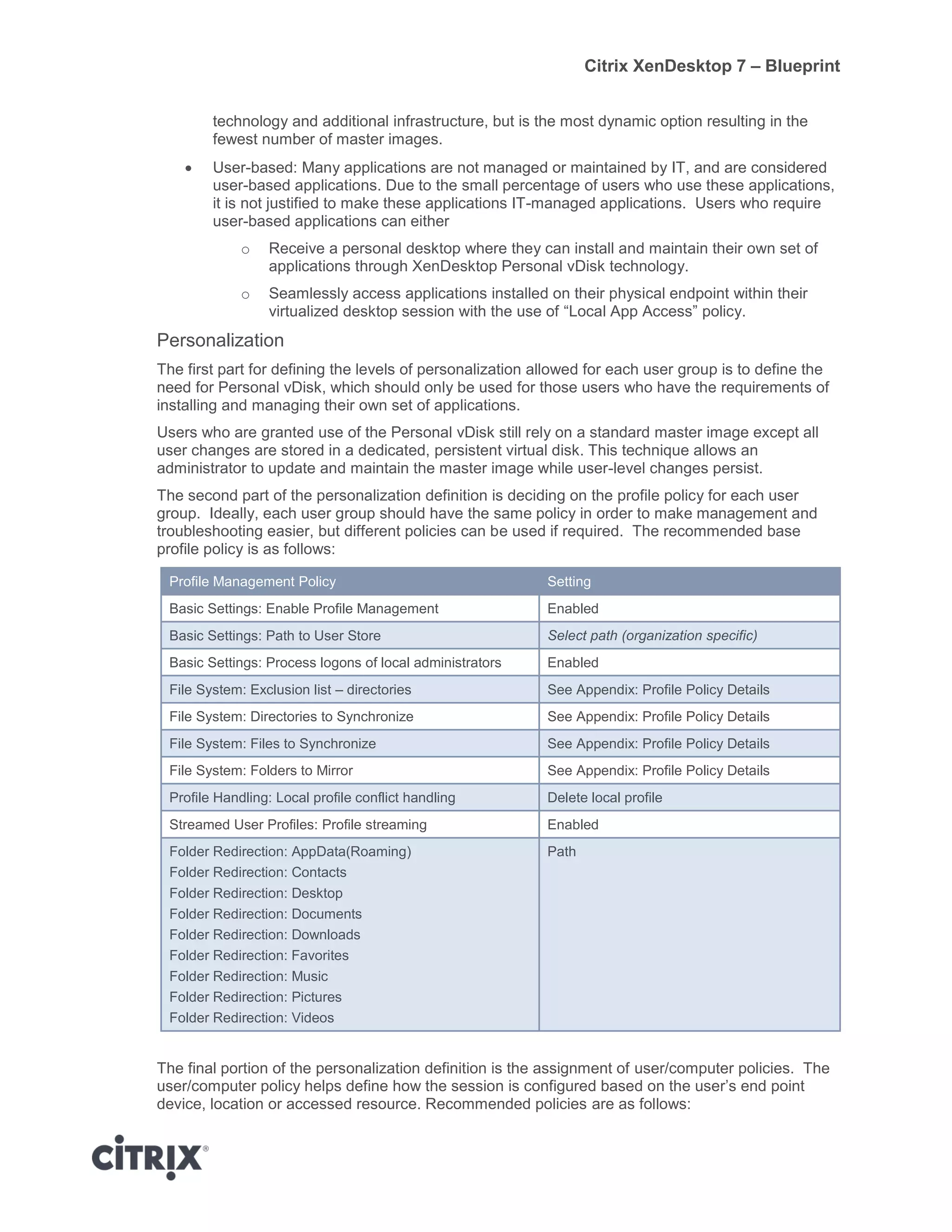
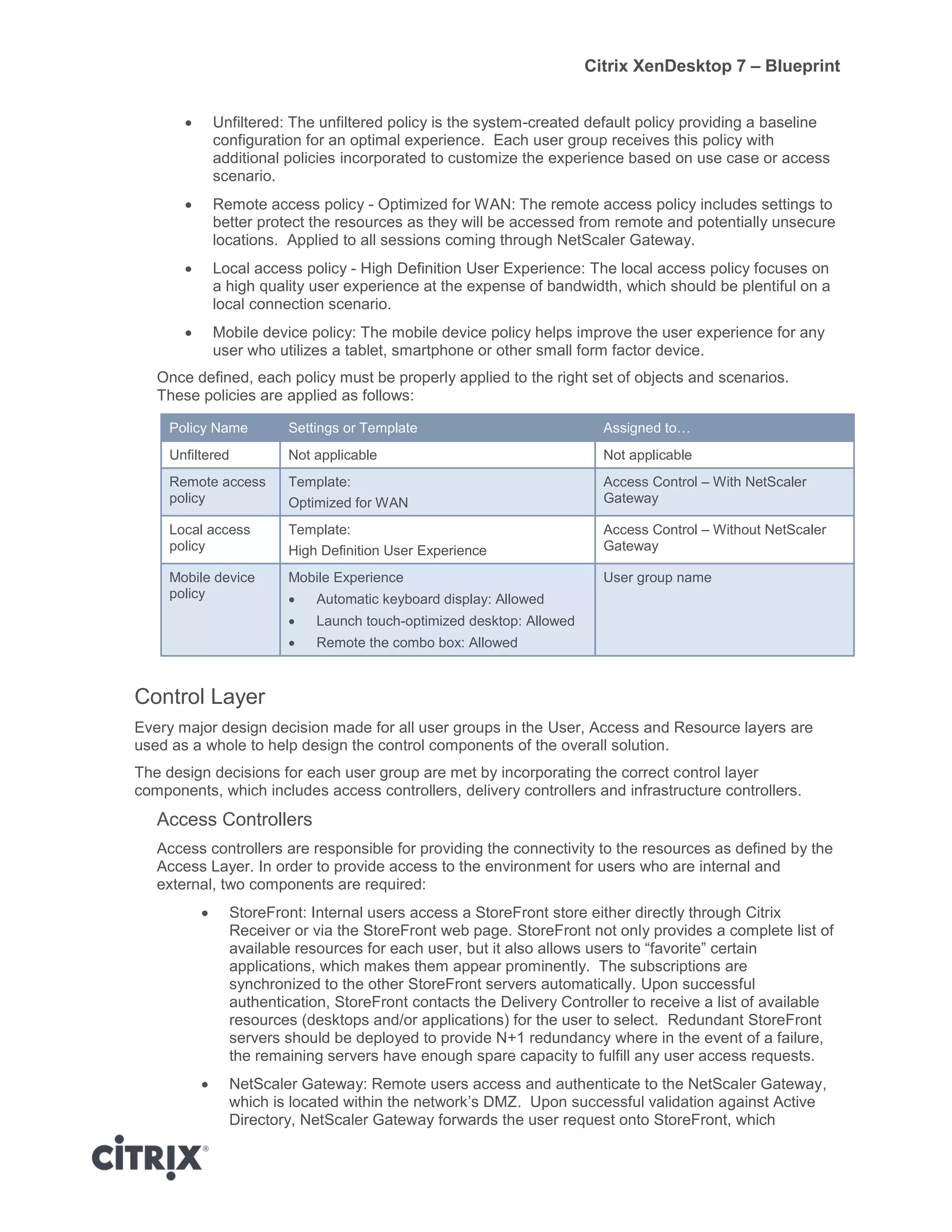
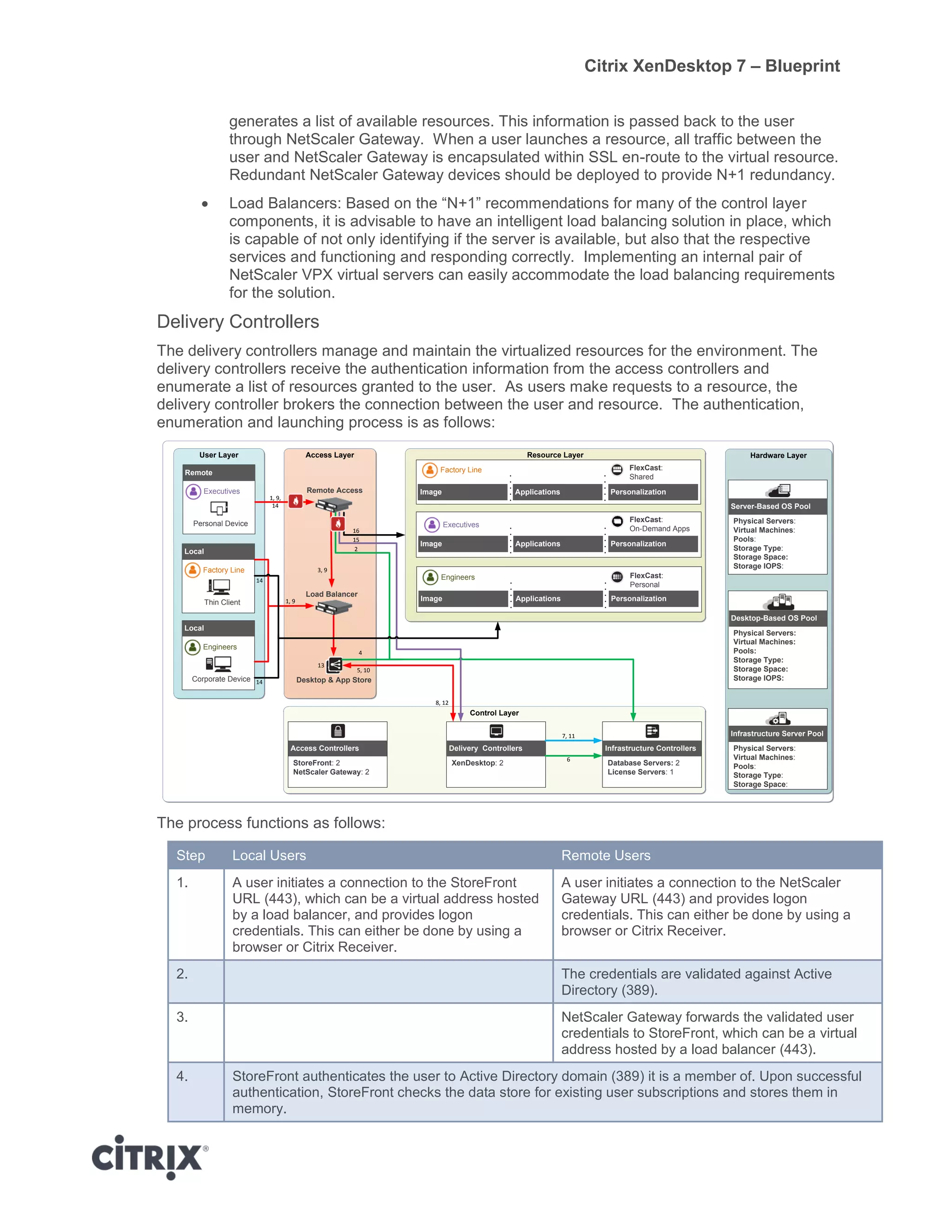
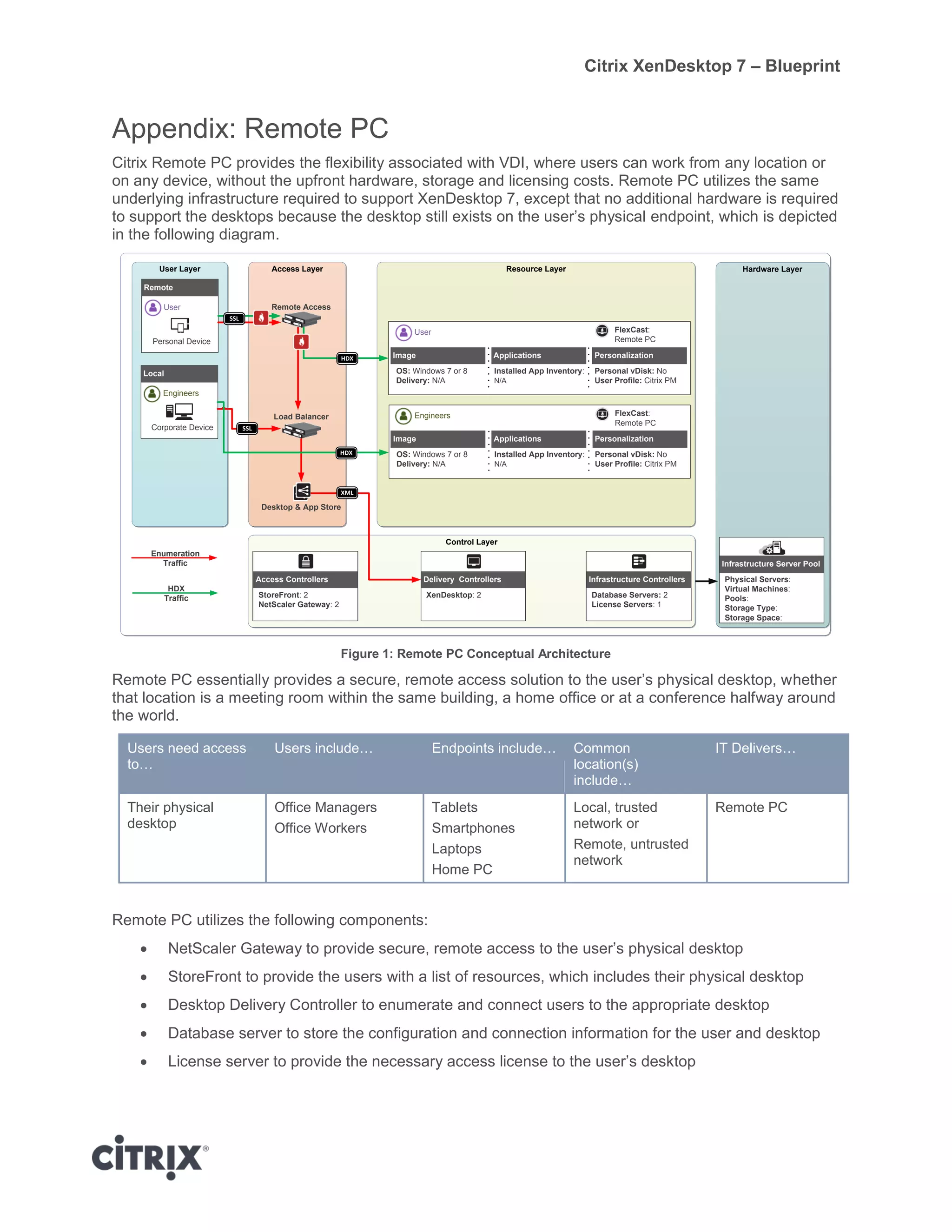
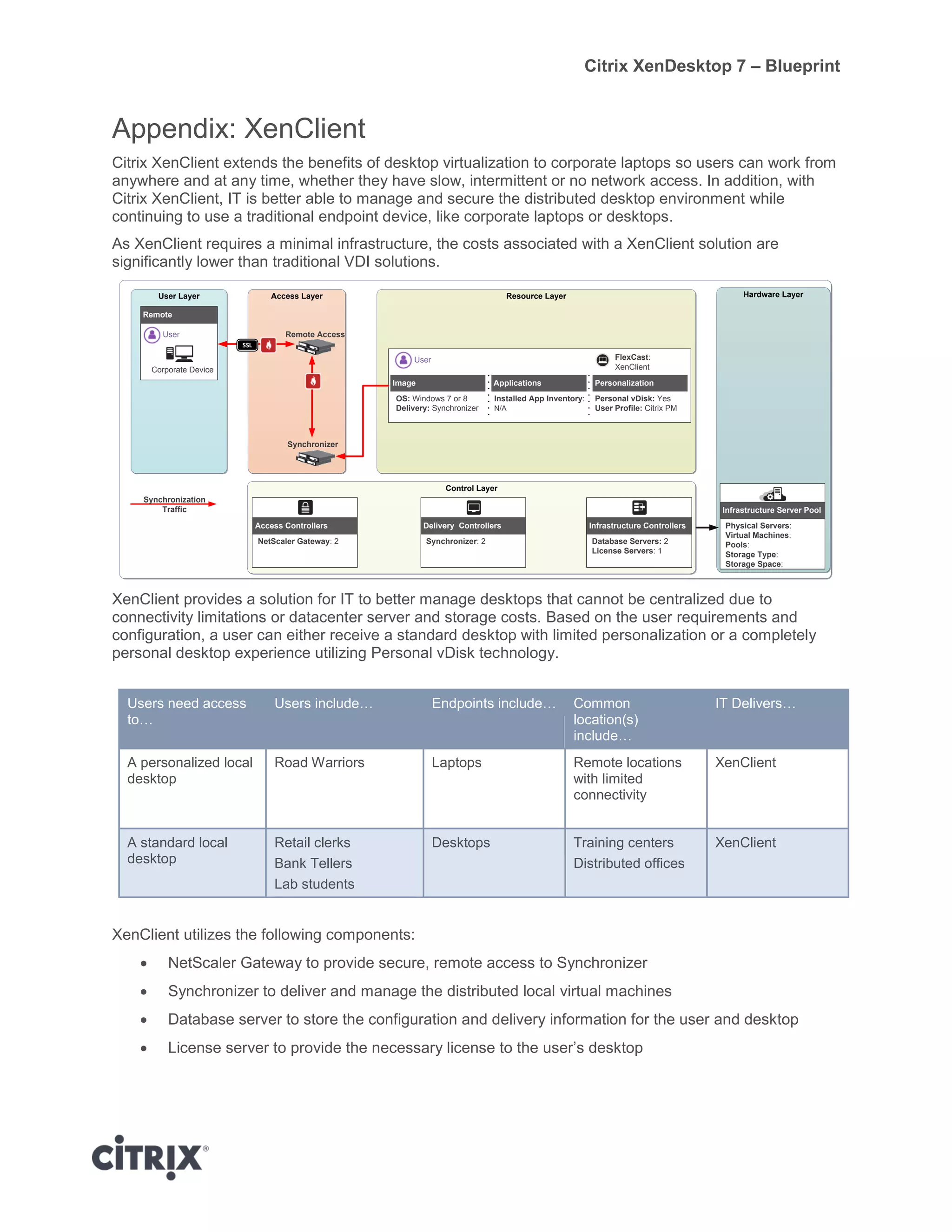
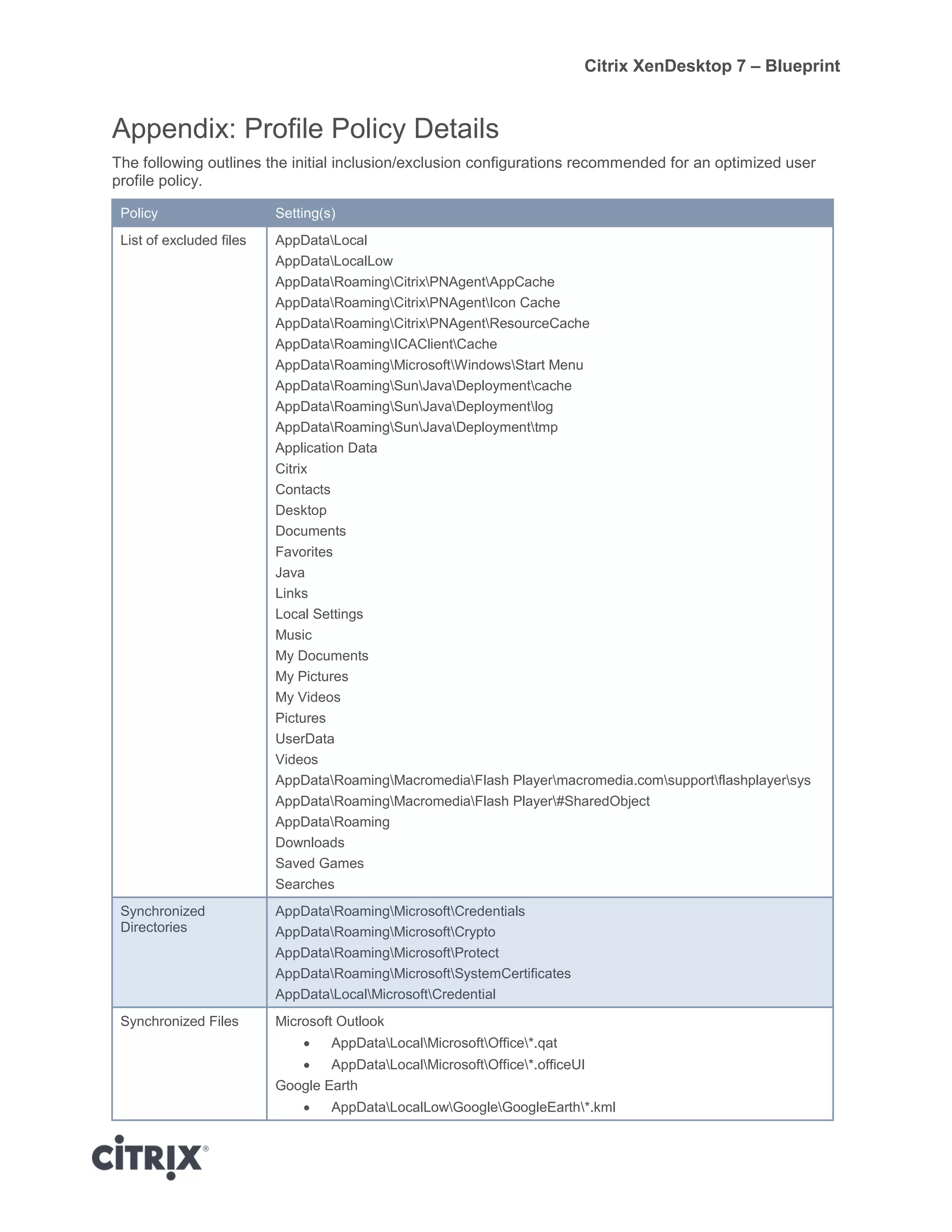
Citrix XenDesktop 7 provides a unified framework for virtual desktop and application solutions based on a 5-layer model. The blueprint details architectures for standardized desktops, customizable desktops, and applications. It recommends Machine Creation Services for image delivery and defines policies, personalization settings, and control components to meet requirements for different user groups accessing resources from various locations.