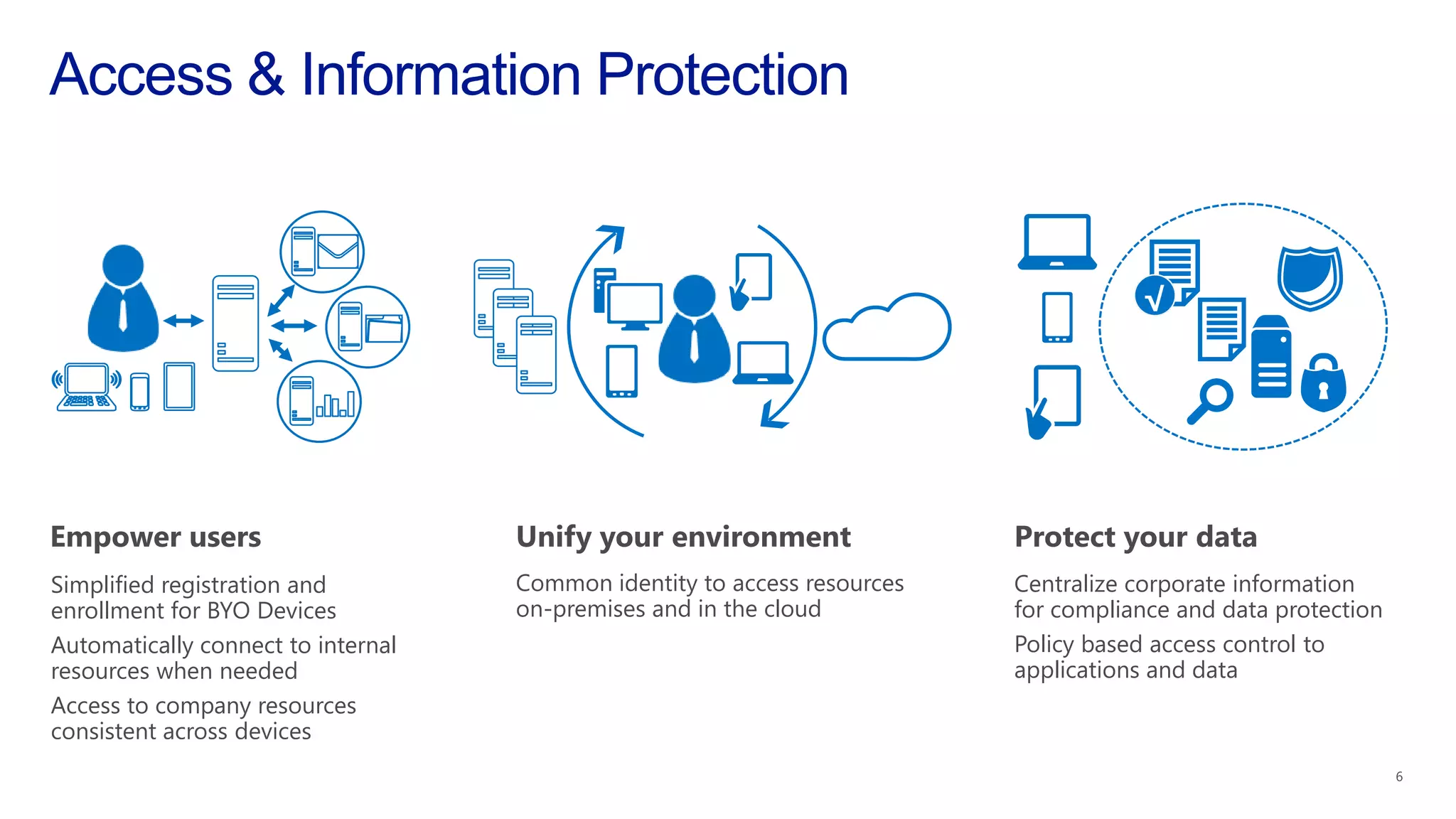
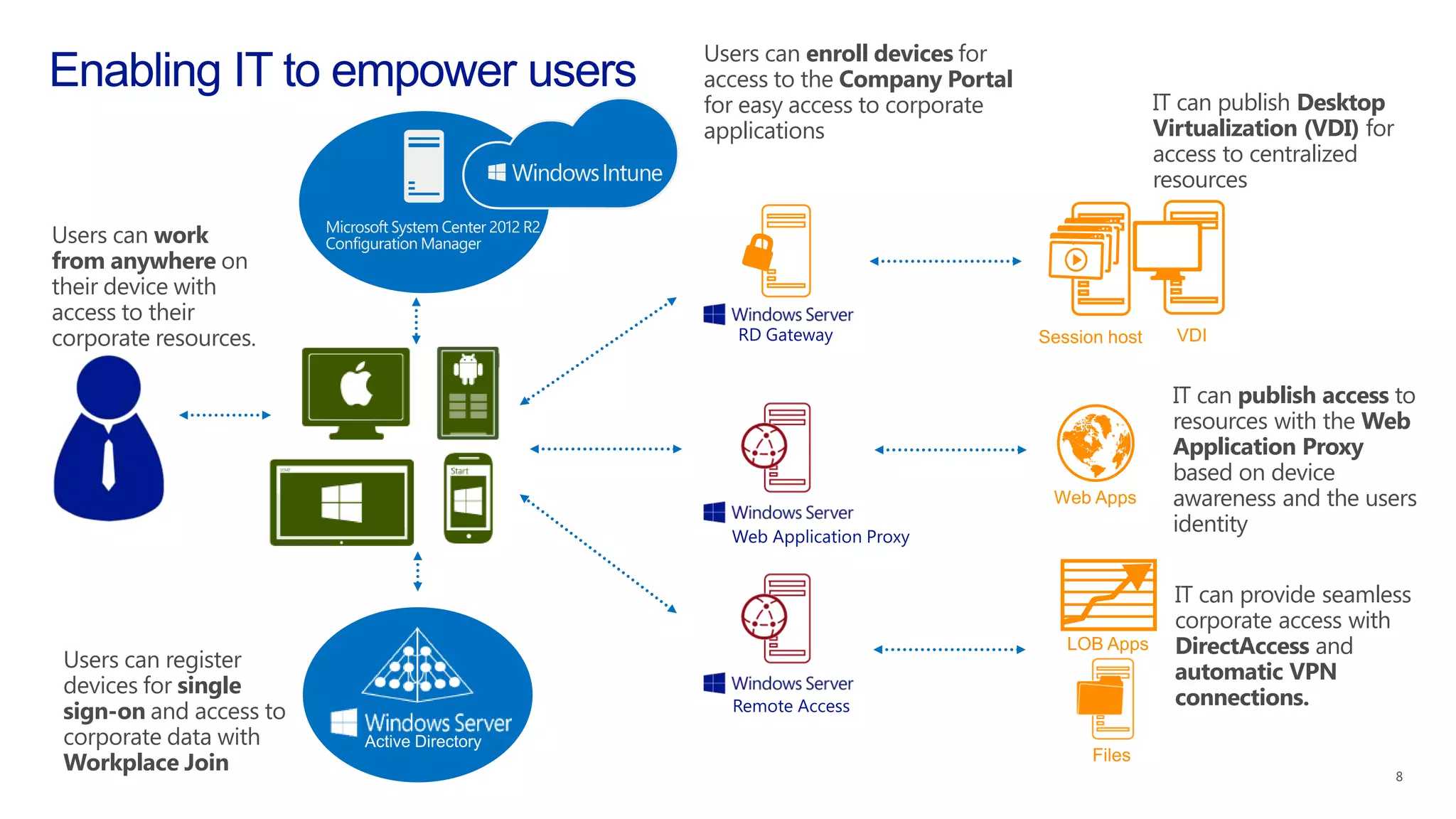
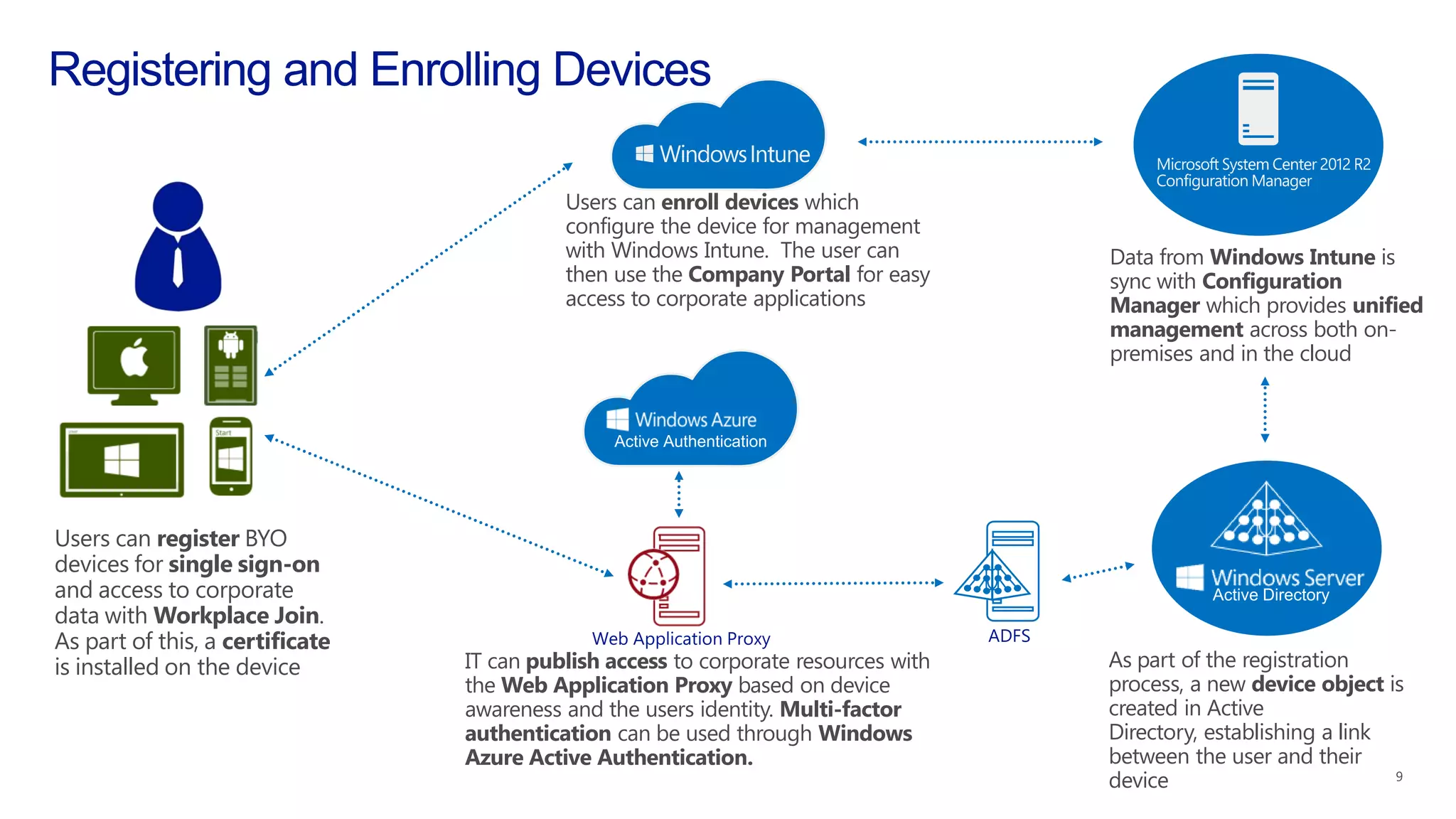
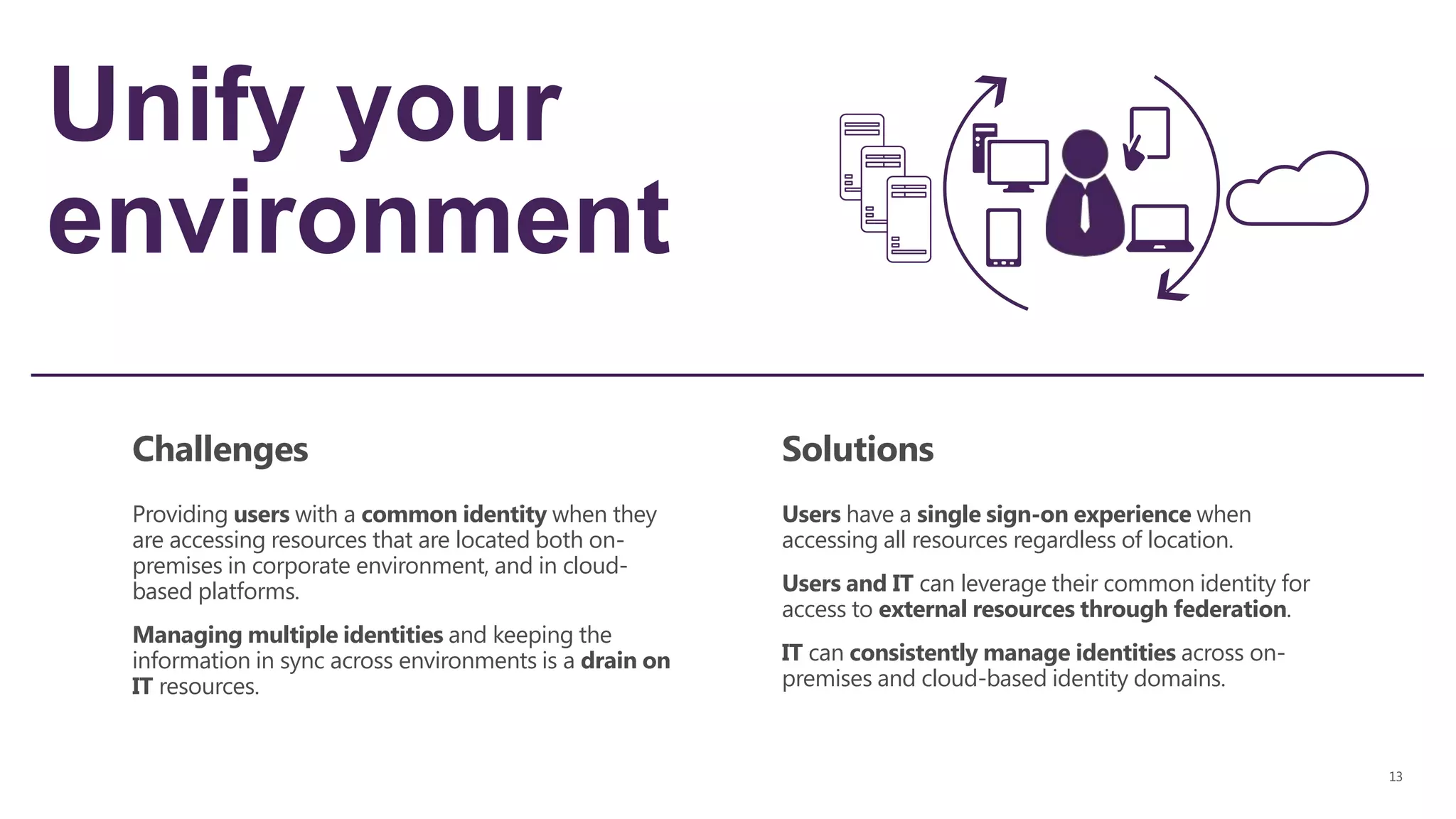
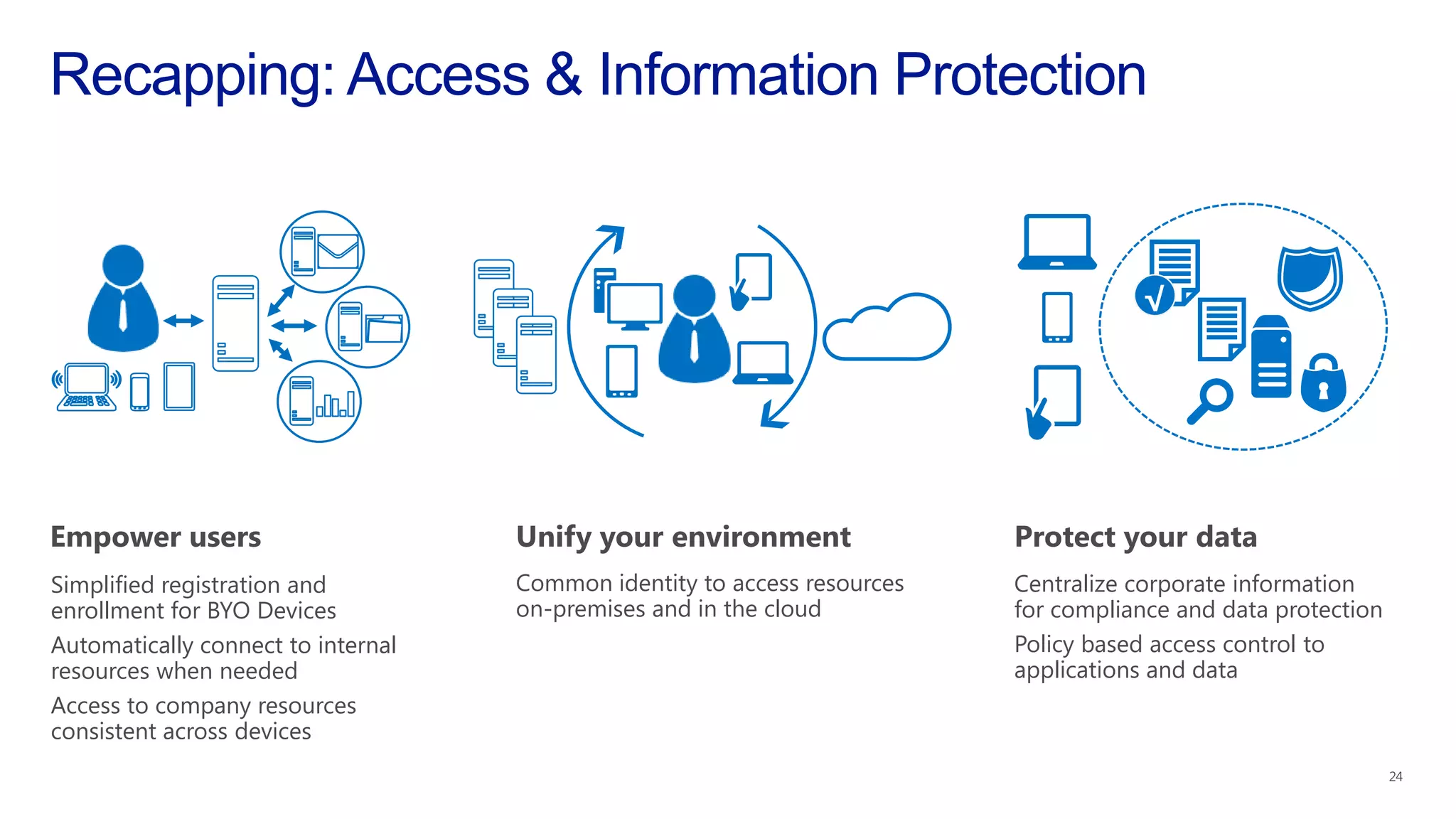
The document outlines a two day training on Windows Server 2012 R2 and System Center 2012 R2. Day 1 covers new features of Windows Server 2012 R2 including server virtualization, cloud optimized networking, and storage. Day 2 focuses on server management, VDI, access and information protection, and web applications. The document also provides information on downloading the Windows Server 2012 R2 and System Center 2012 R2 previews and an upcoming System Center 2012 R2 Jumpstart event.