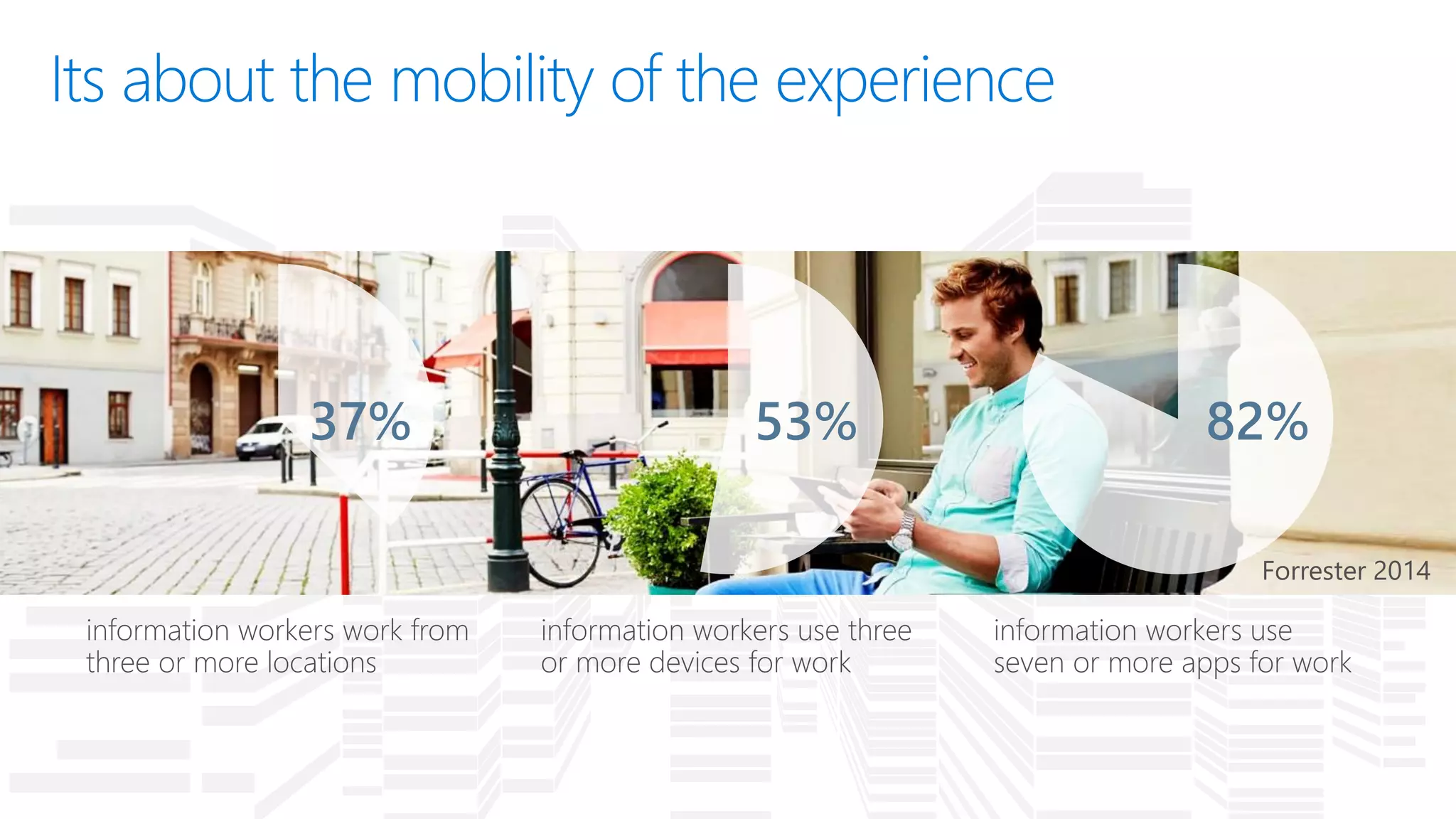
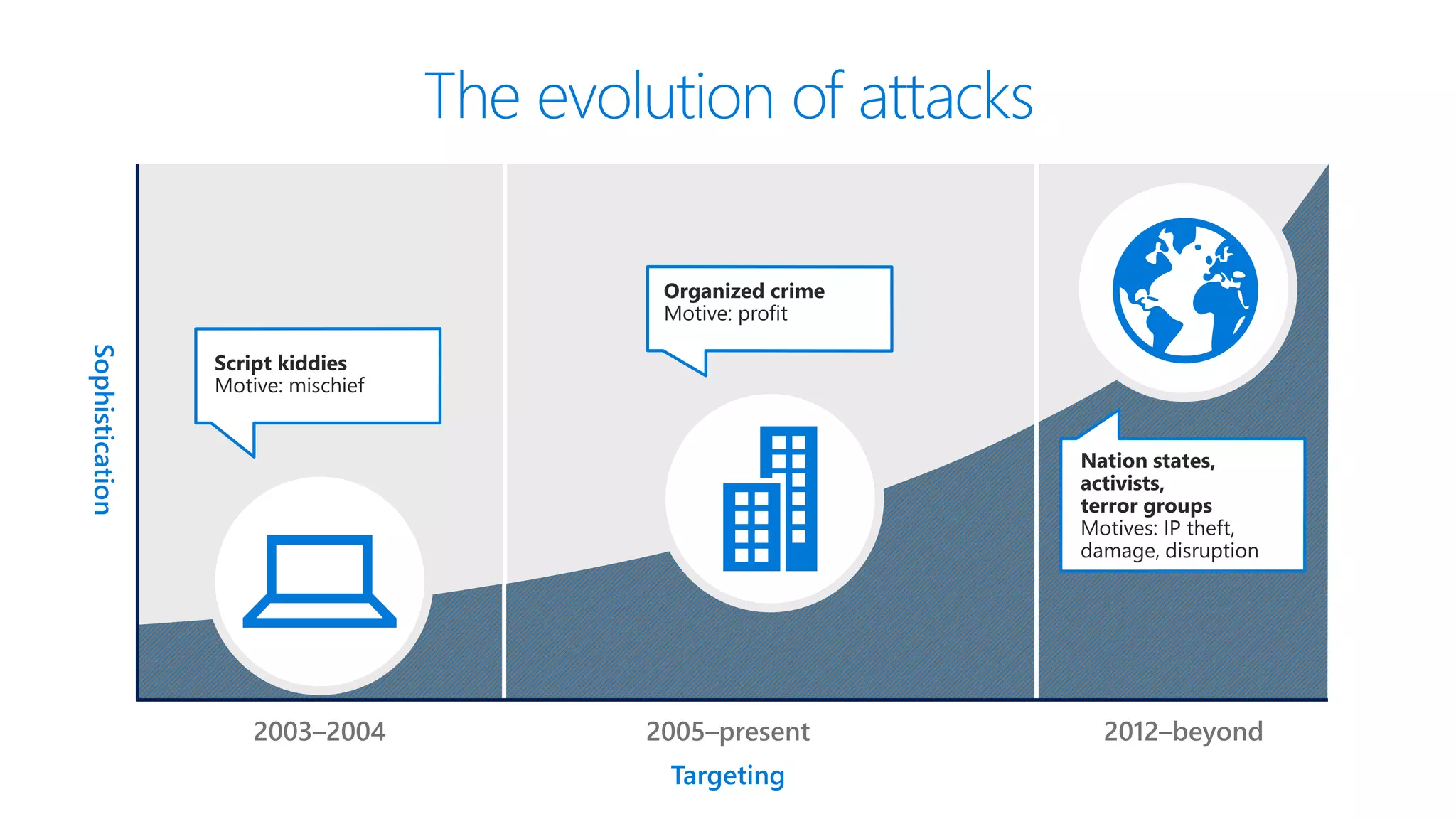
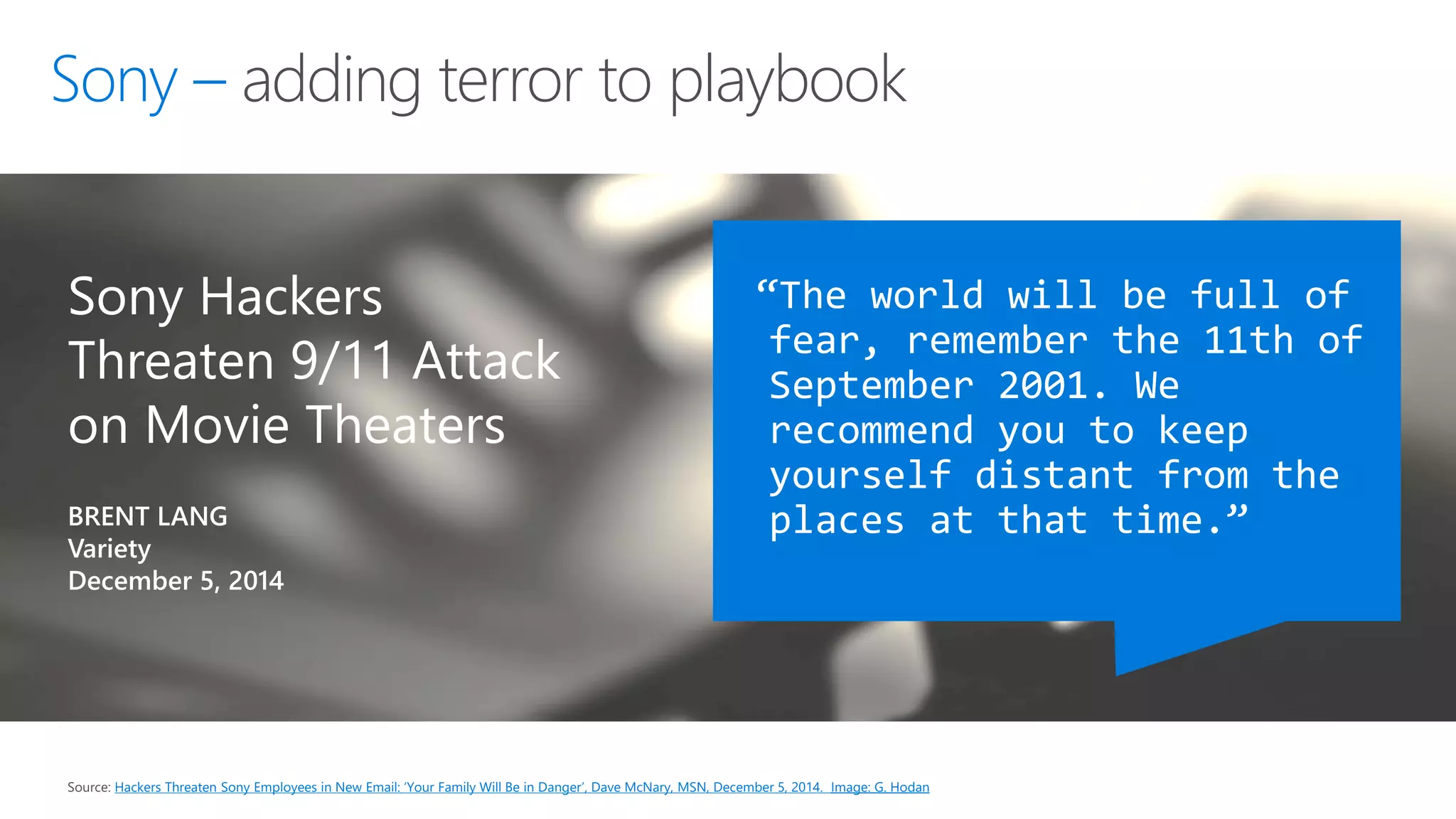
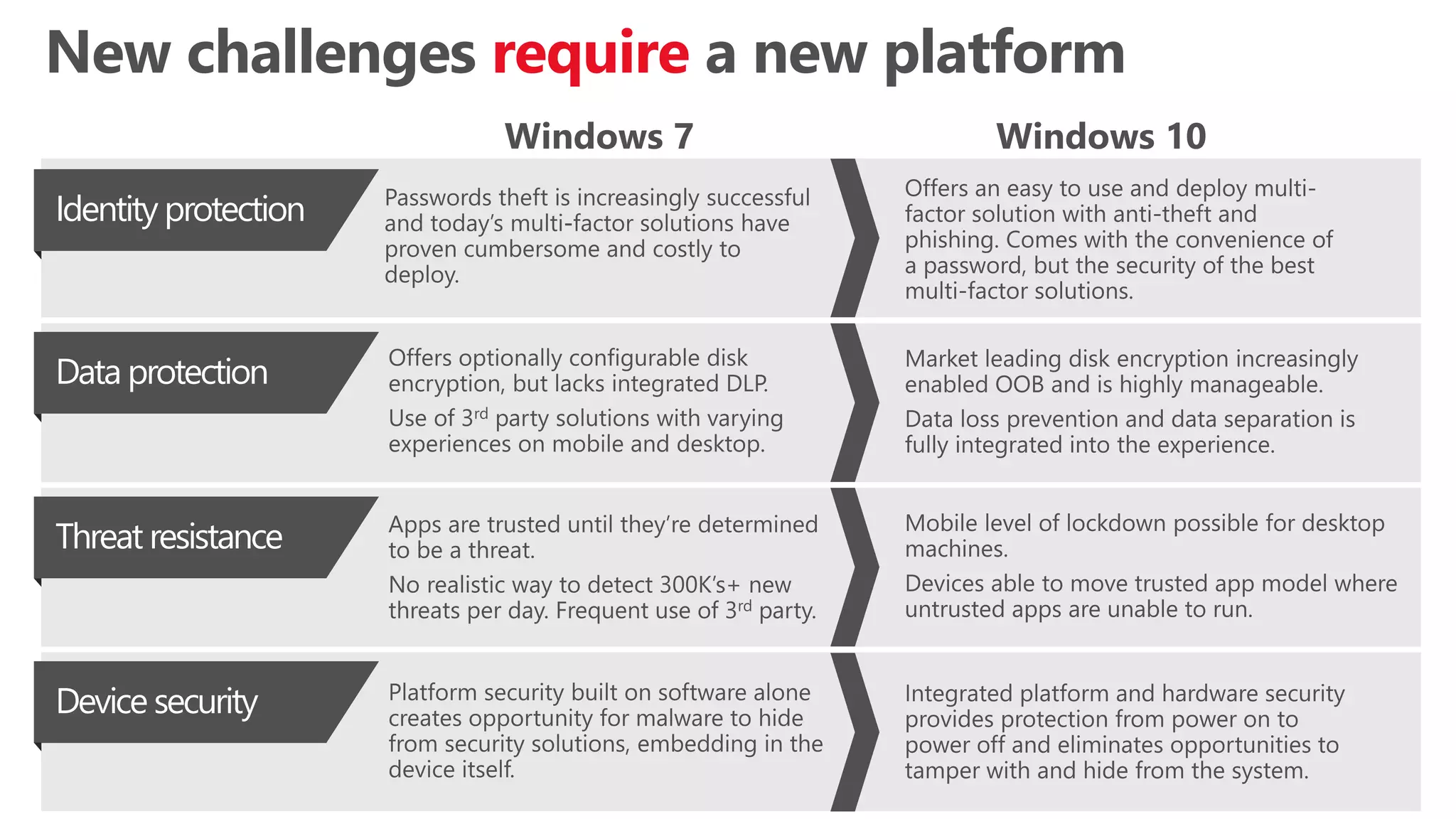
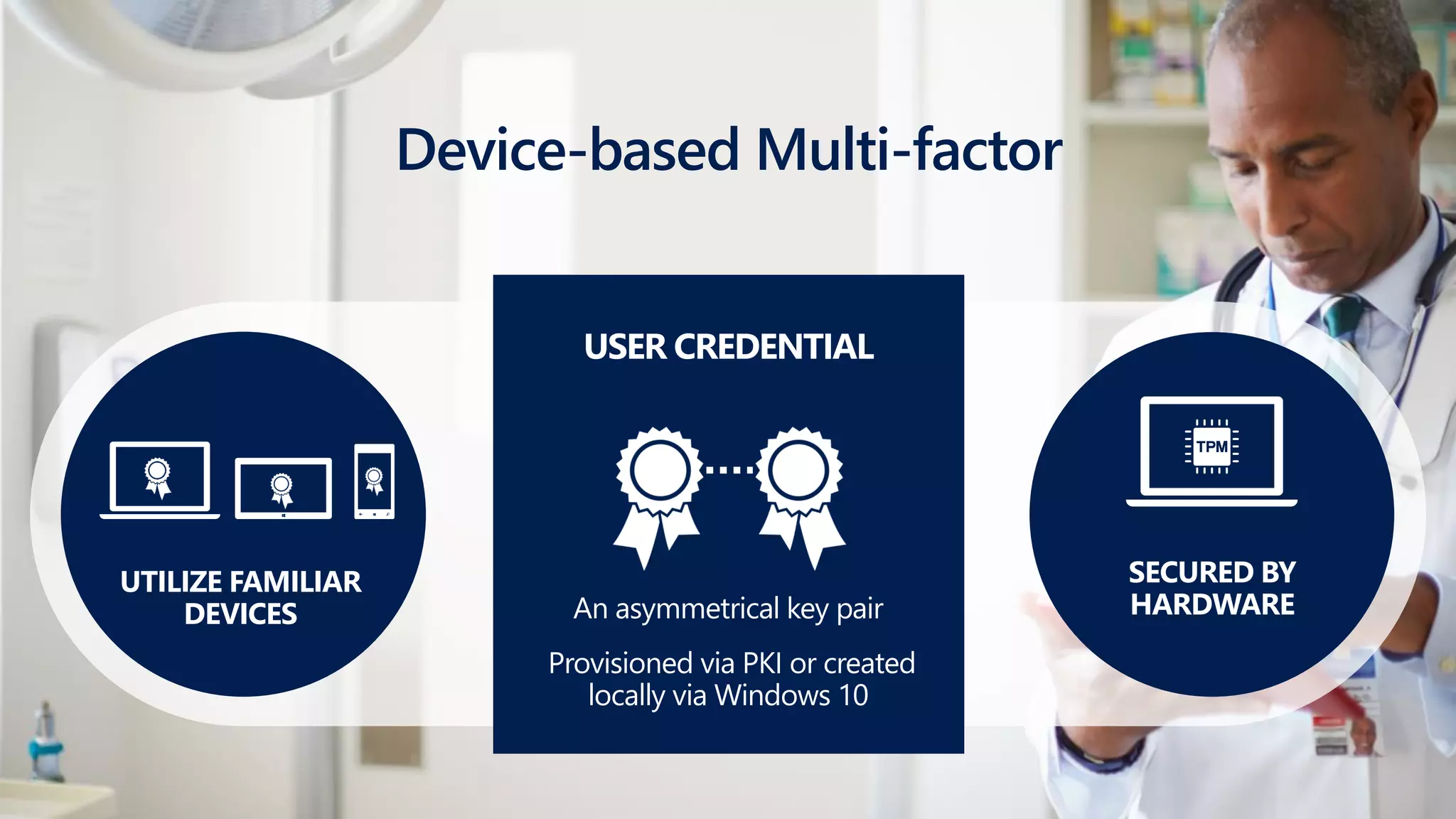
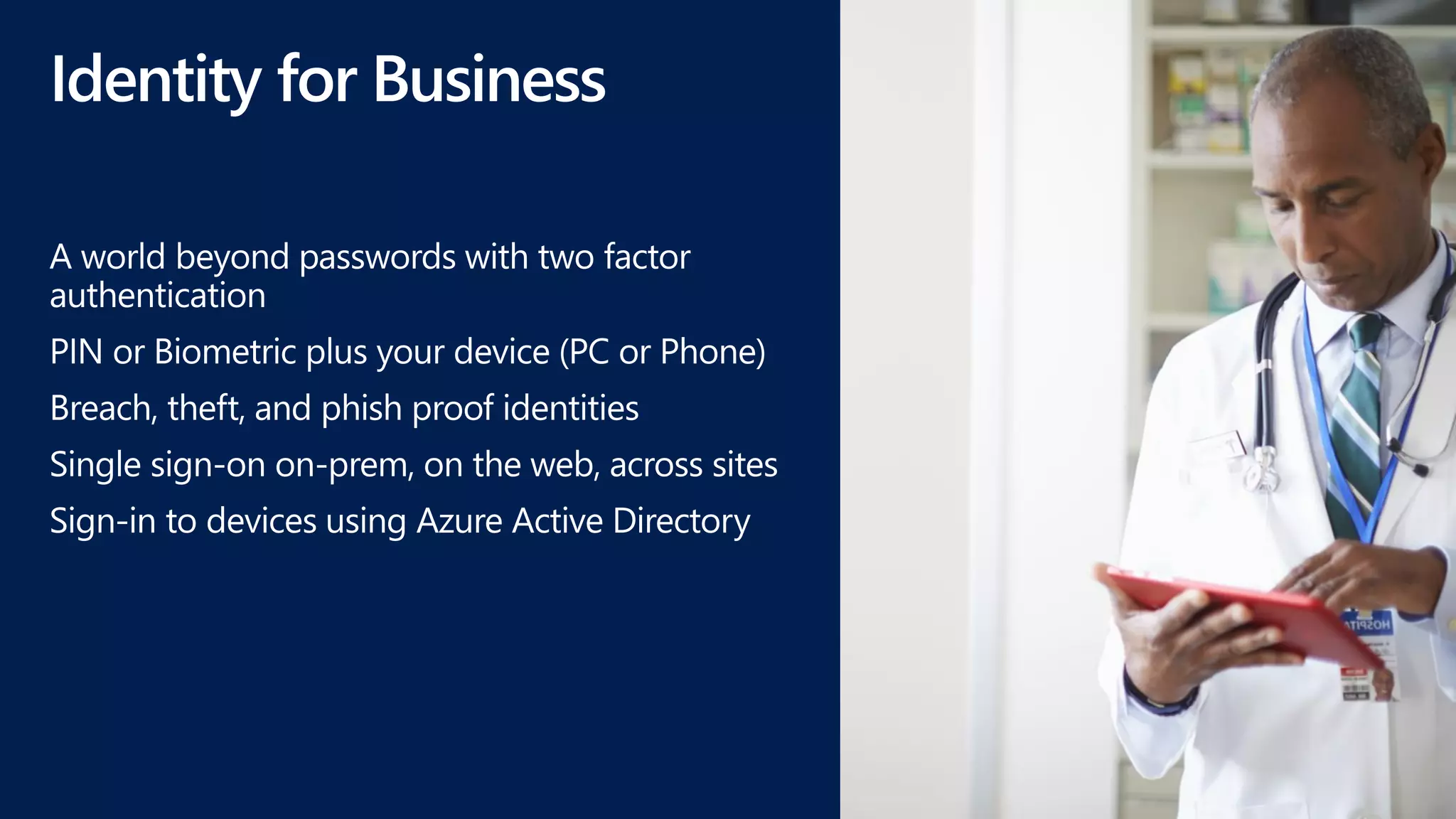
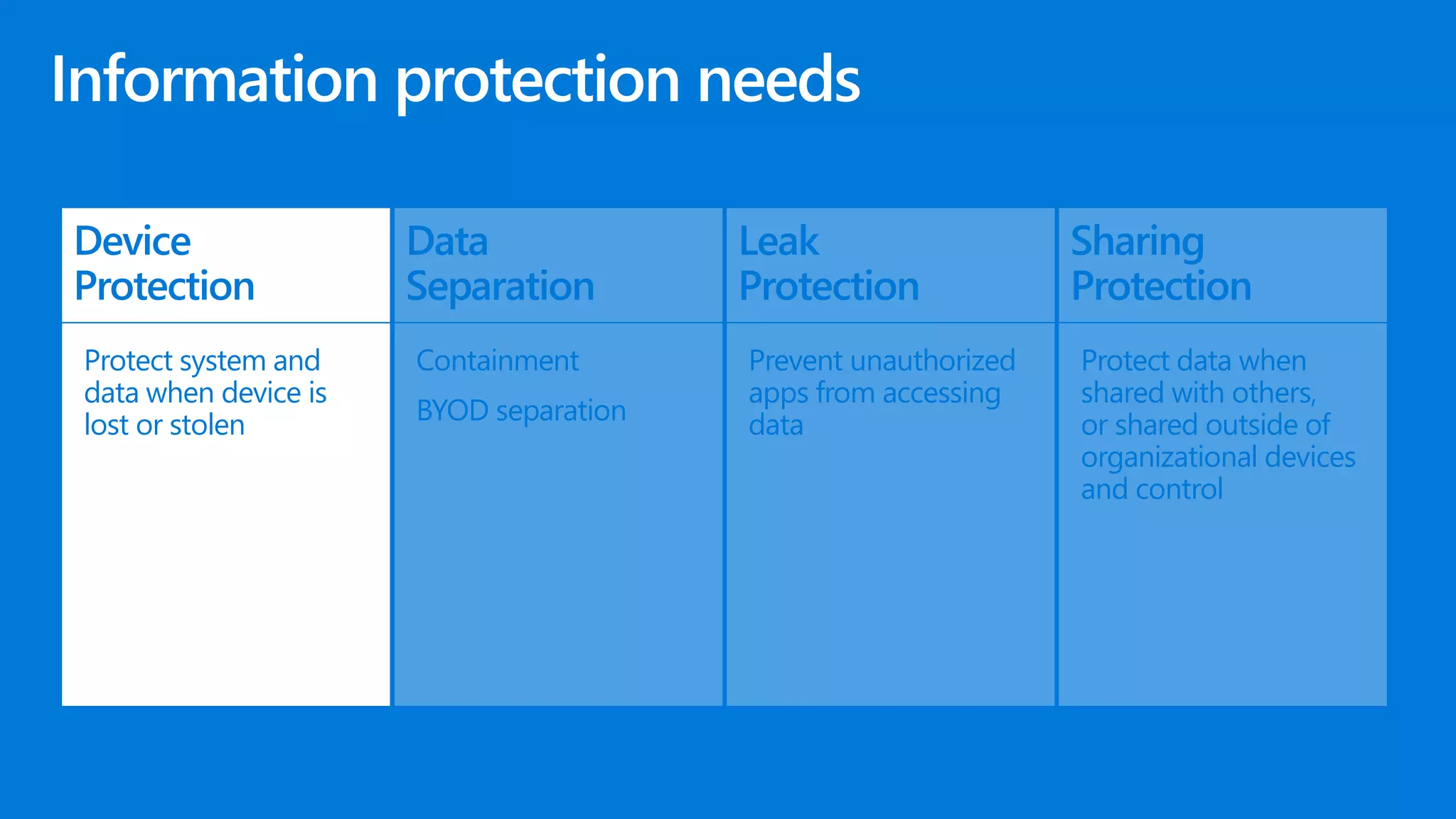
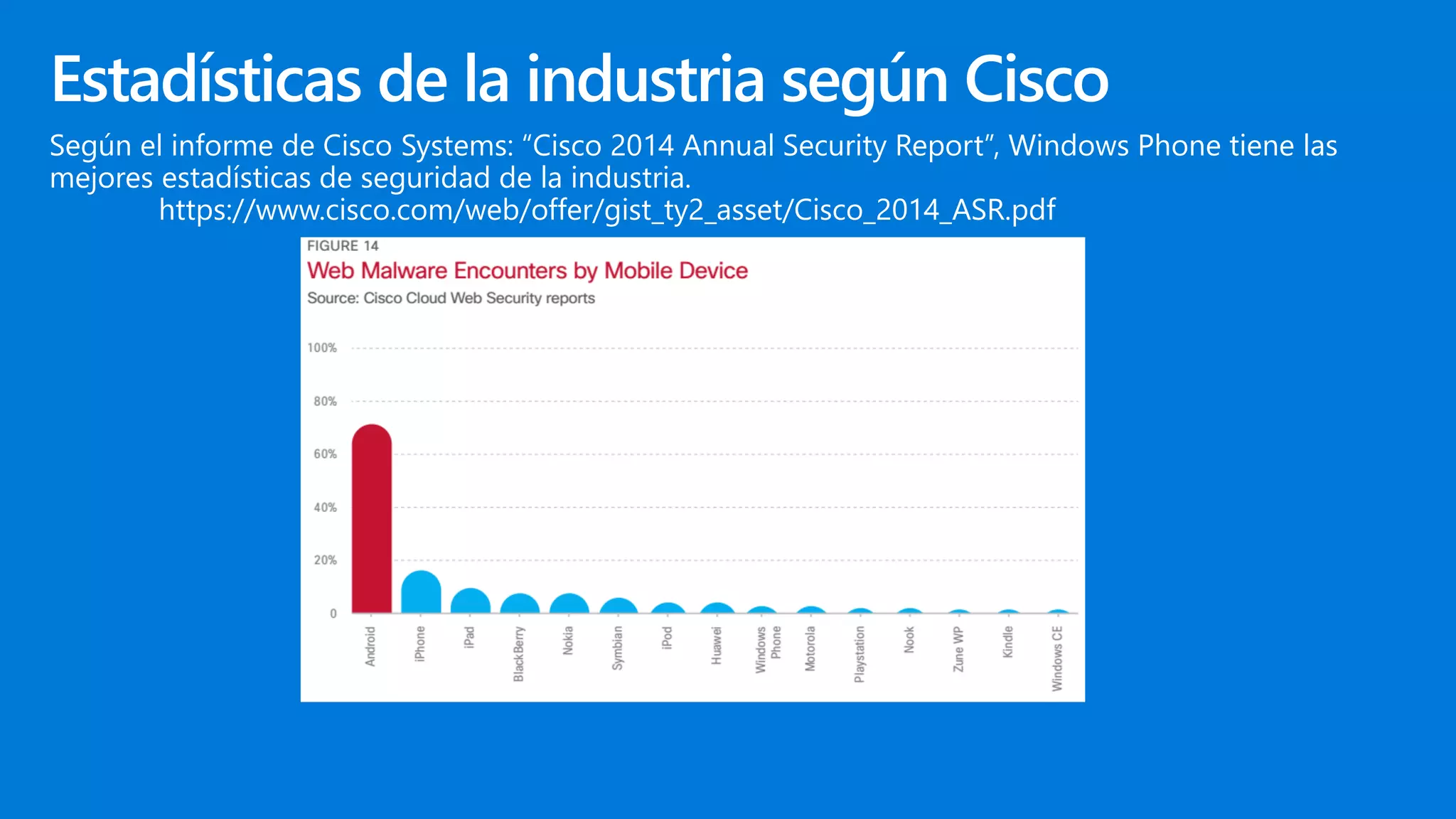
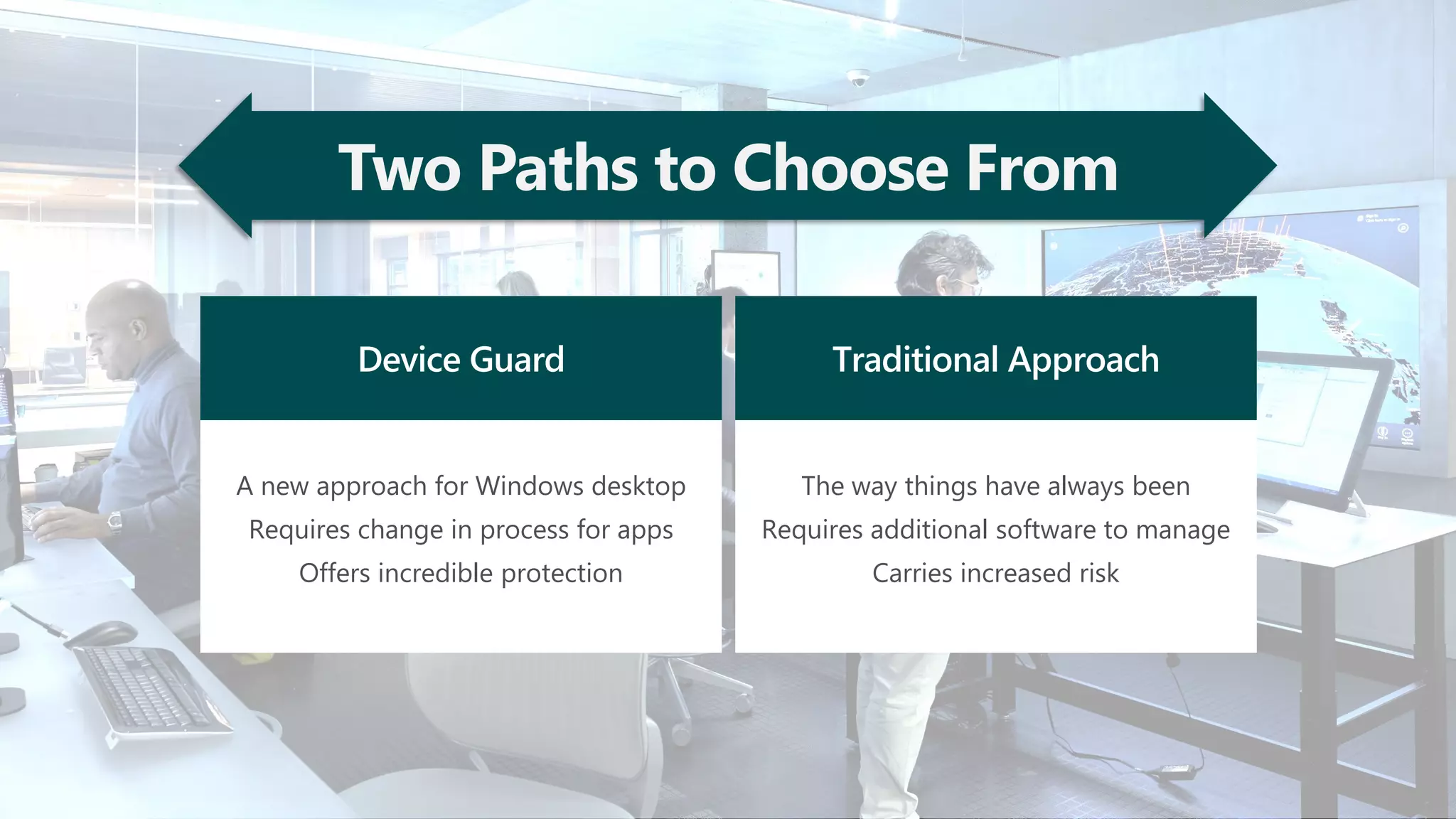
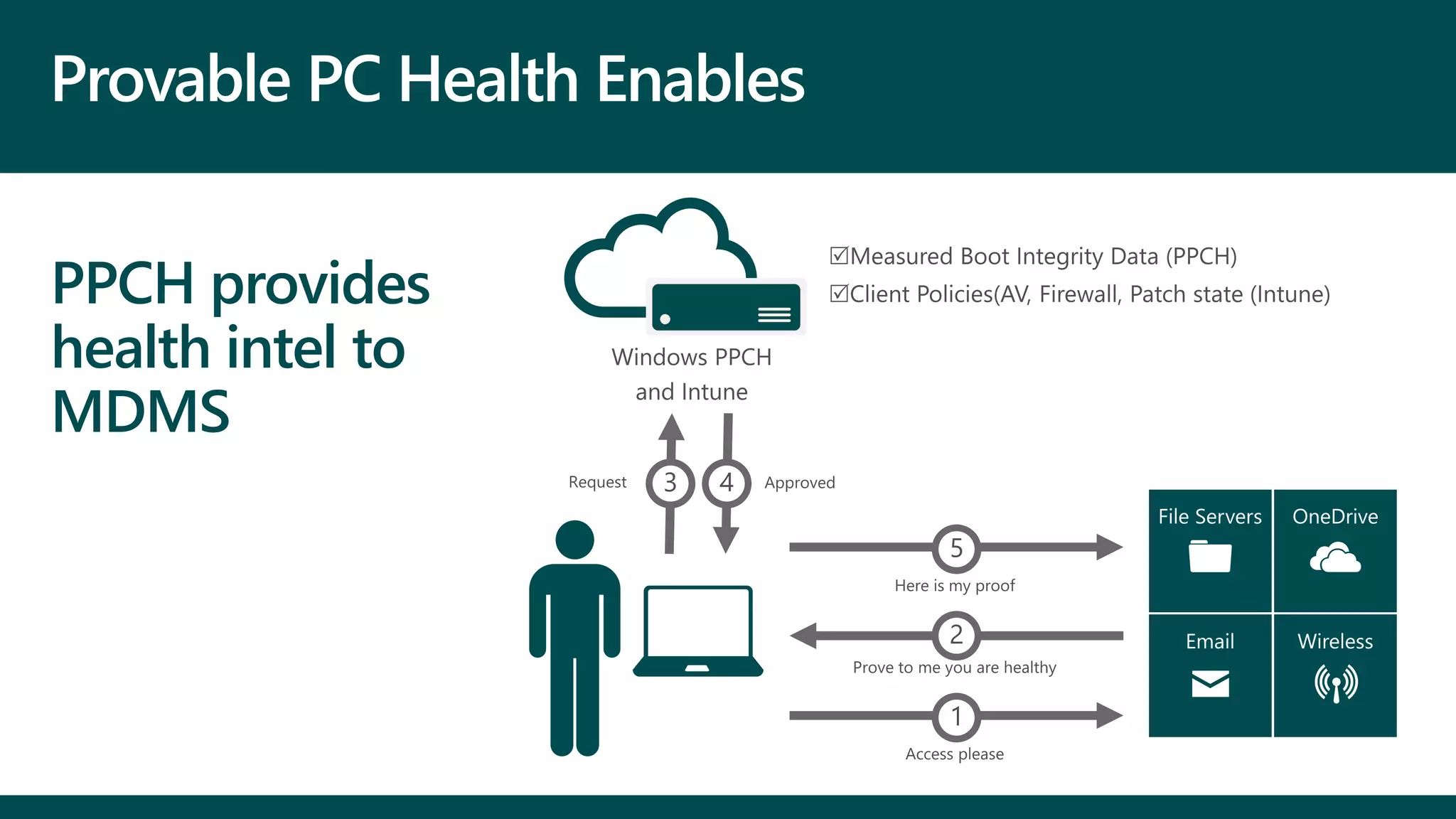
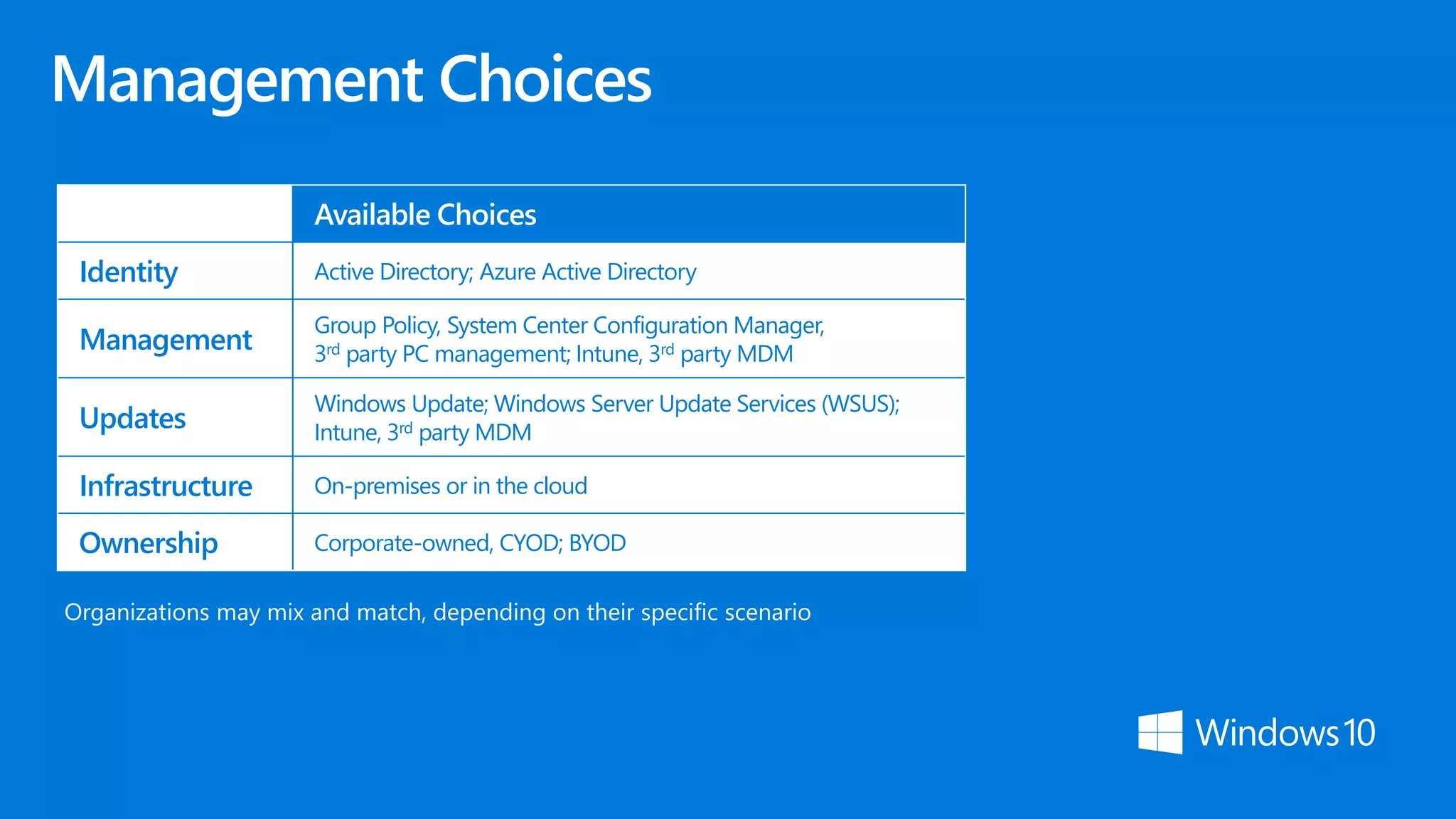
The document discusses the need for adopting advanced security technologies as passwords become insufficient for protecting corporate data, with a focus on enhancing device and identity protection. It highlights various modern security approaches, including multi-factor authentication, device guard, and data loss prevention strategies aimed at managing security threats and improving user mobility. Additionally, it emphasizes the importance of a unified management platform for streamlined deployment and continuous innovation in security measures.