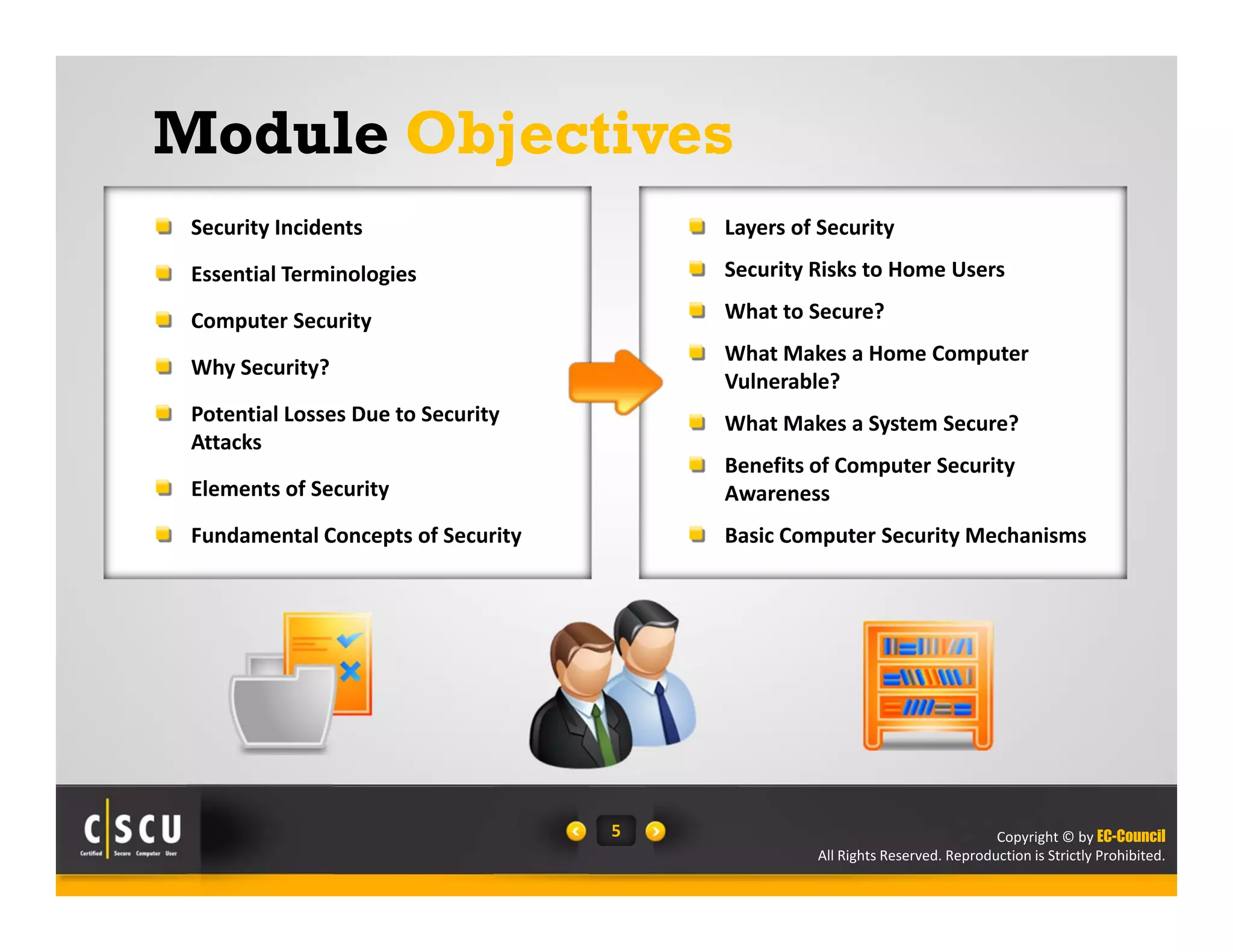
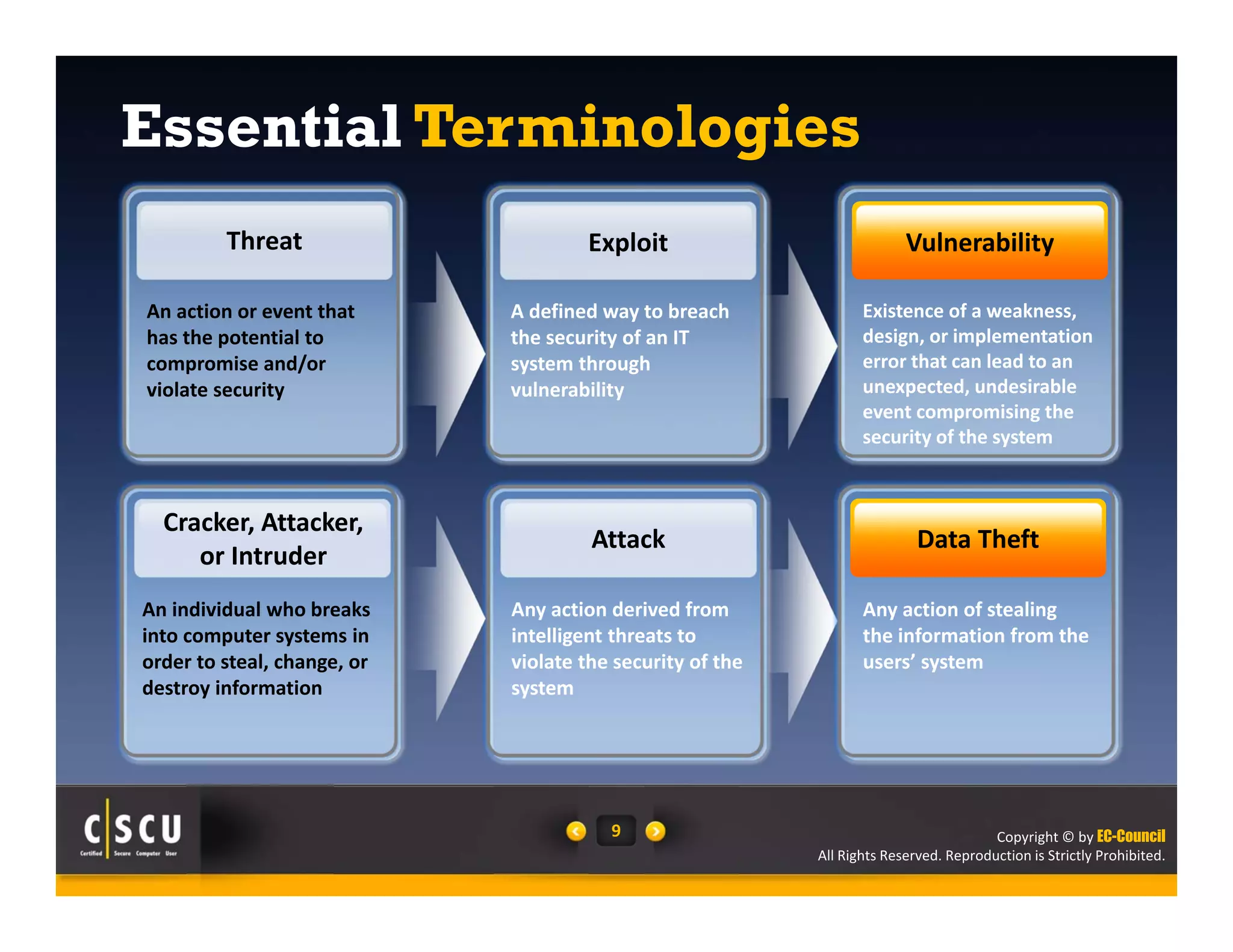
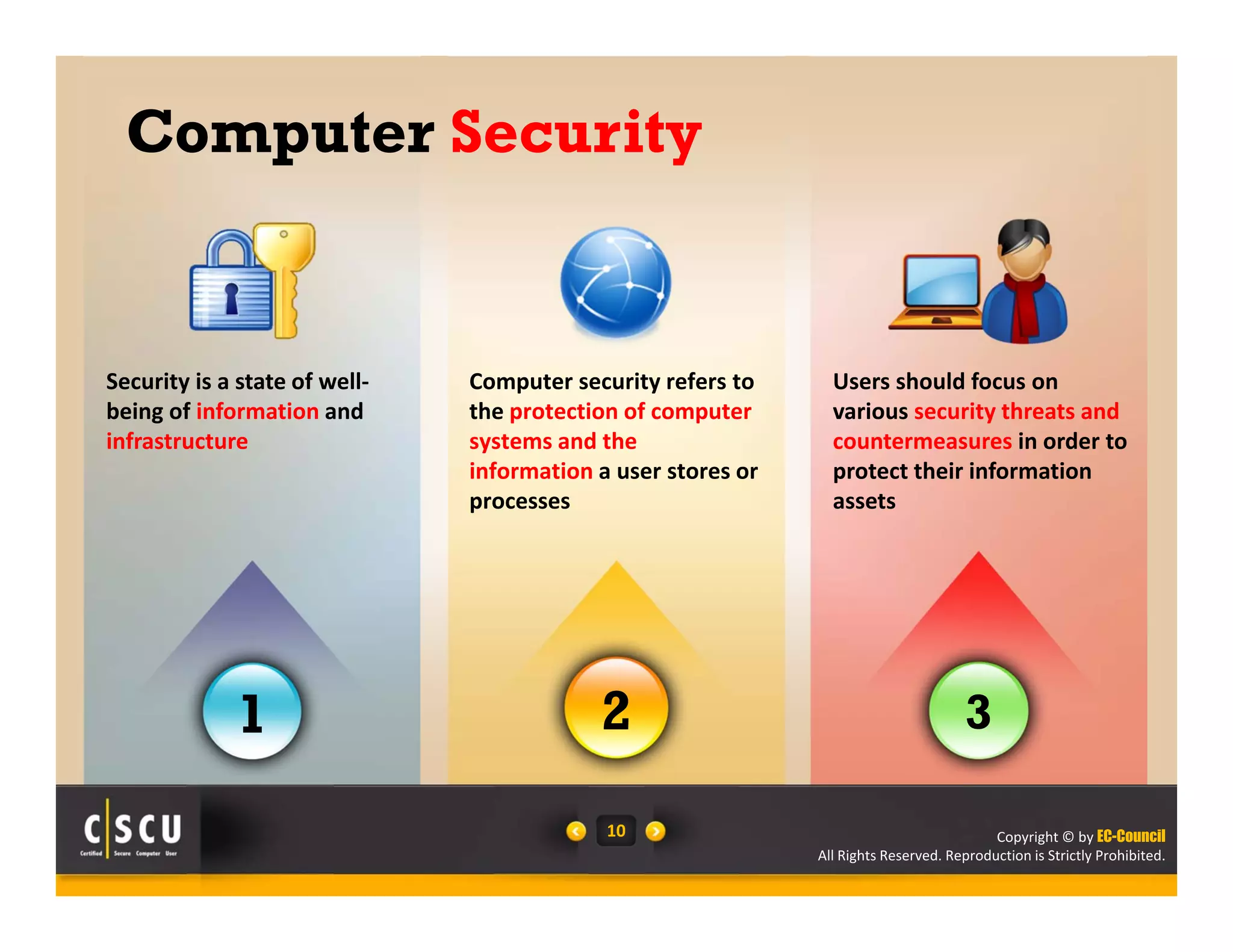
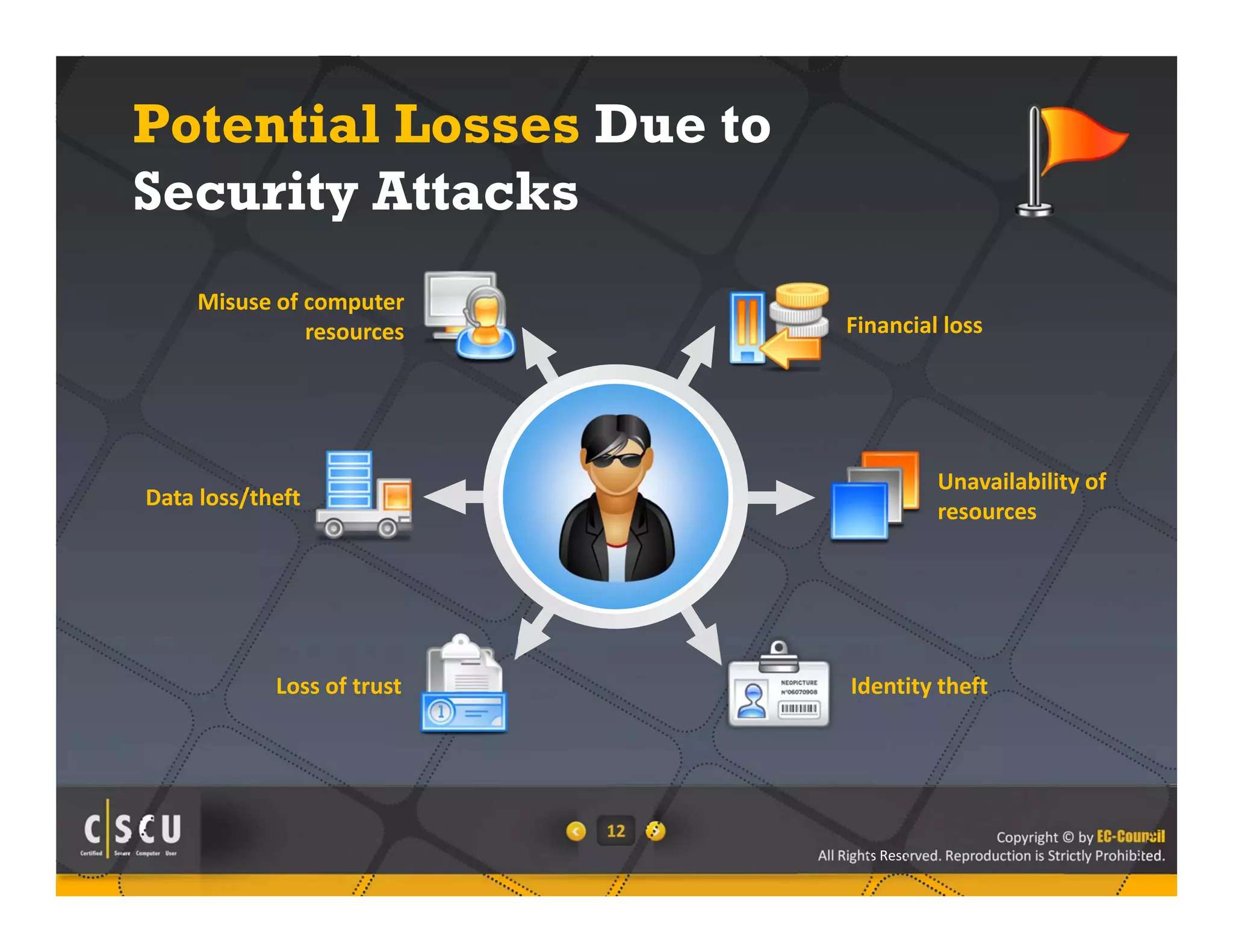
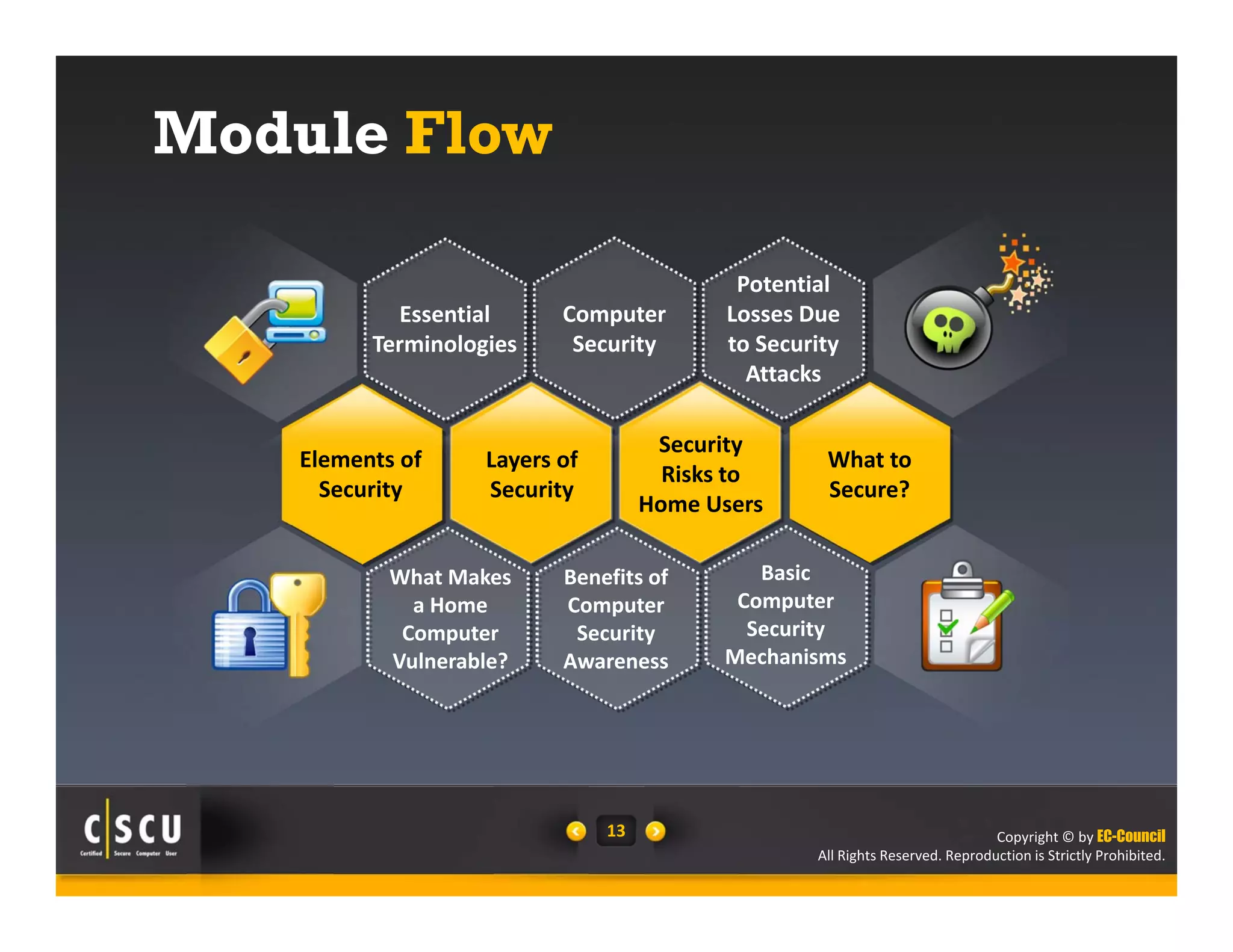
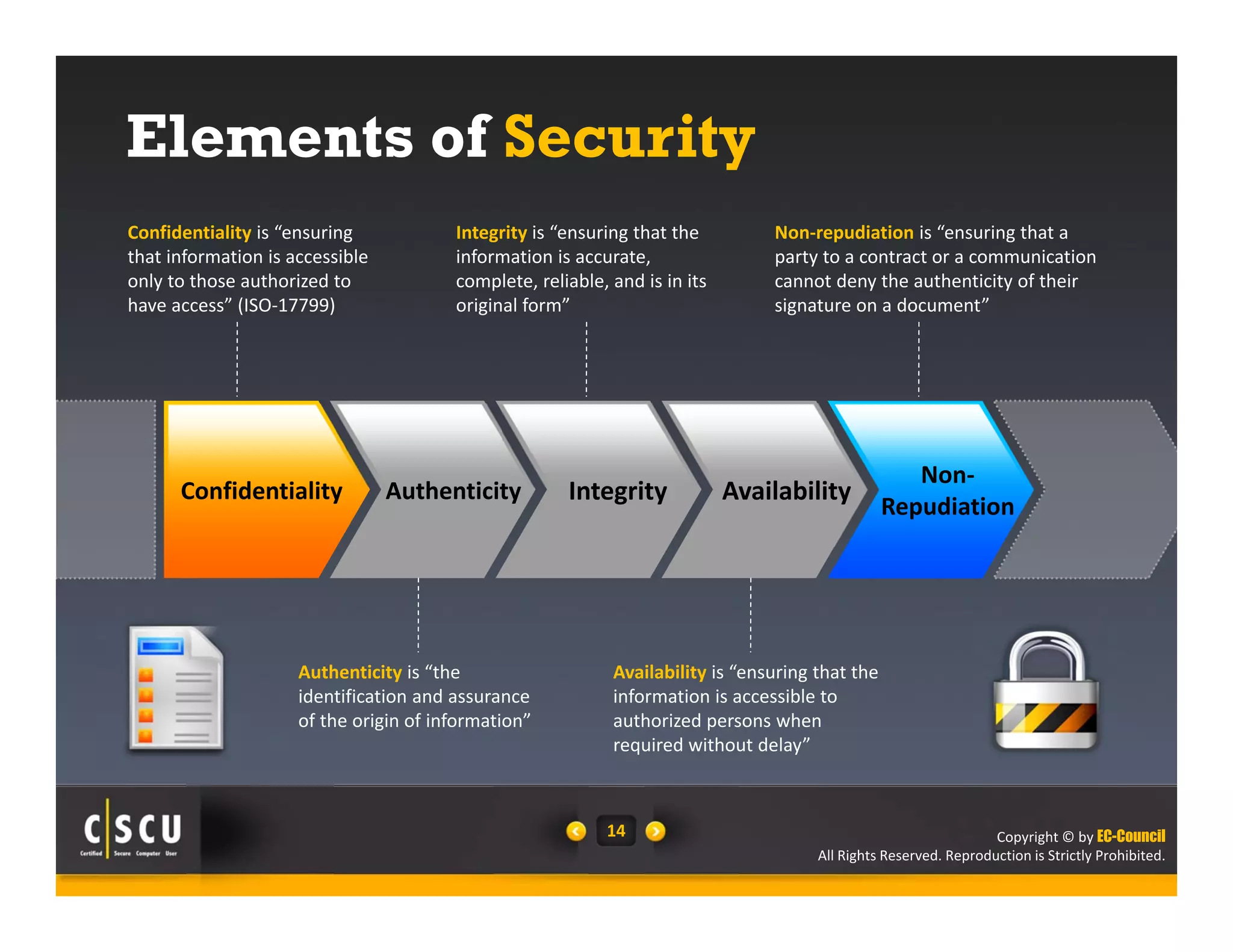
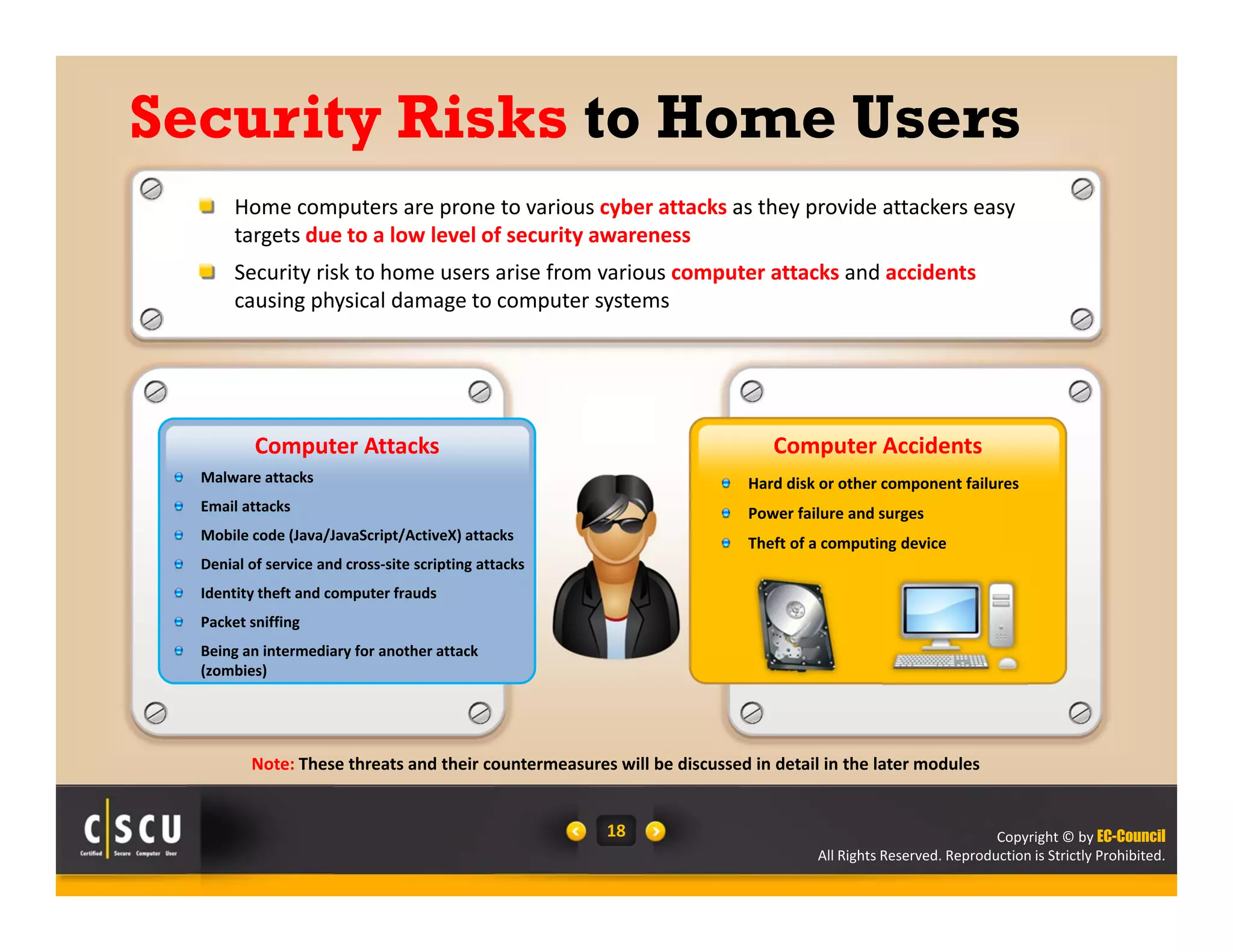
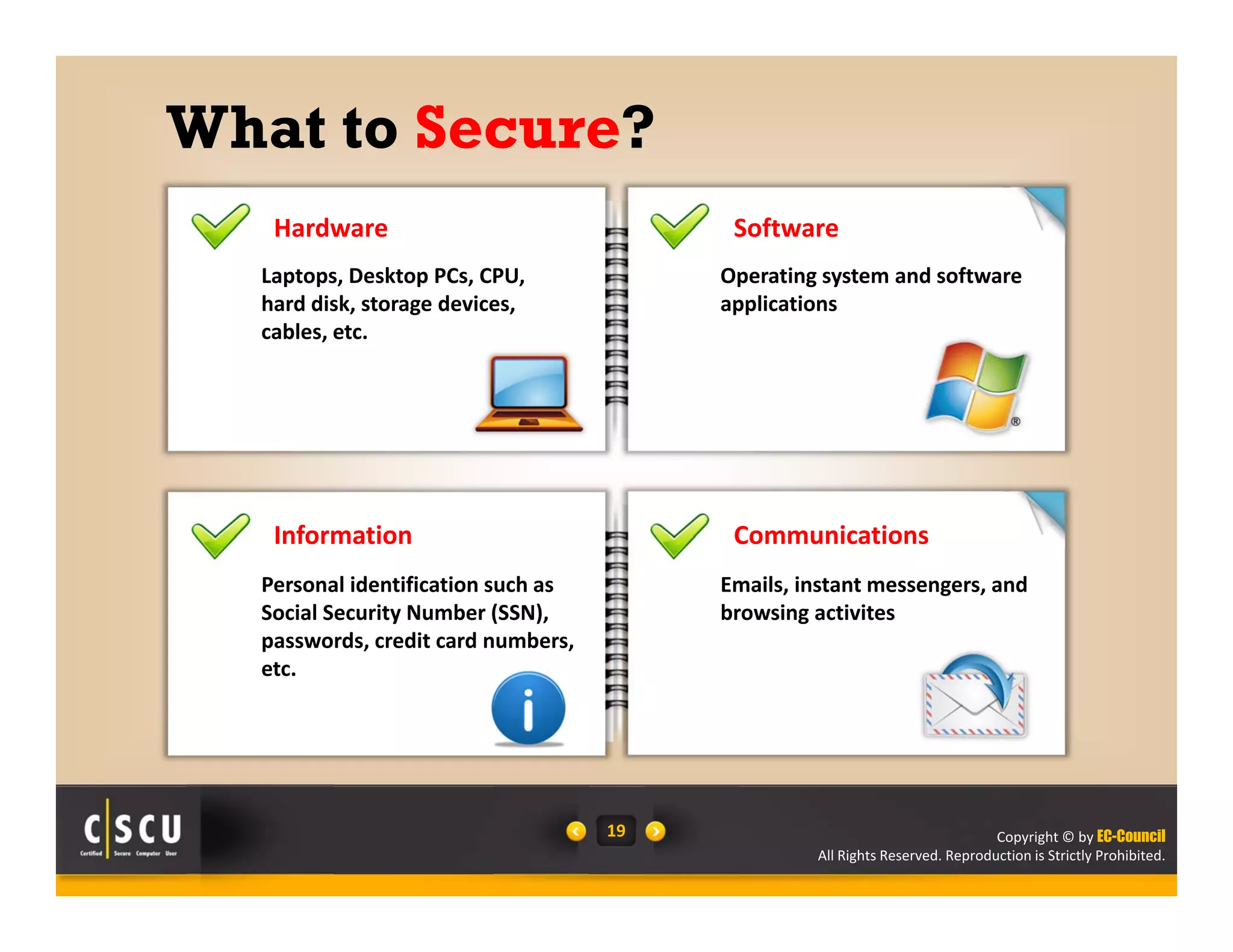
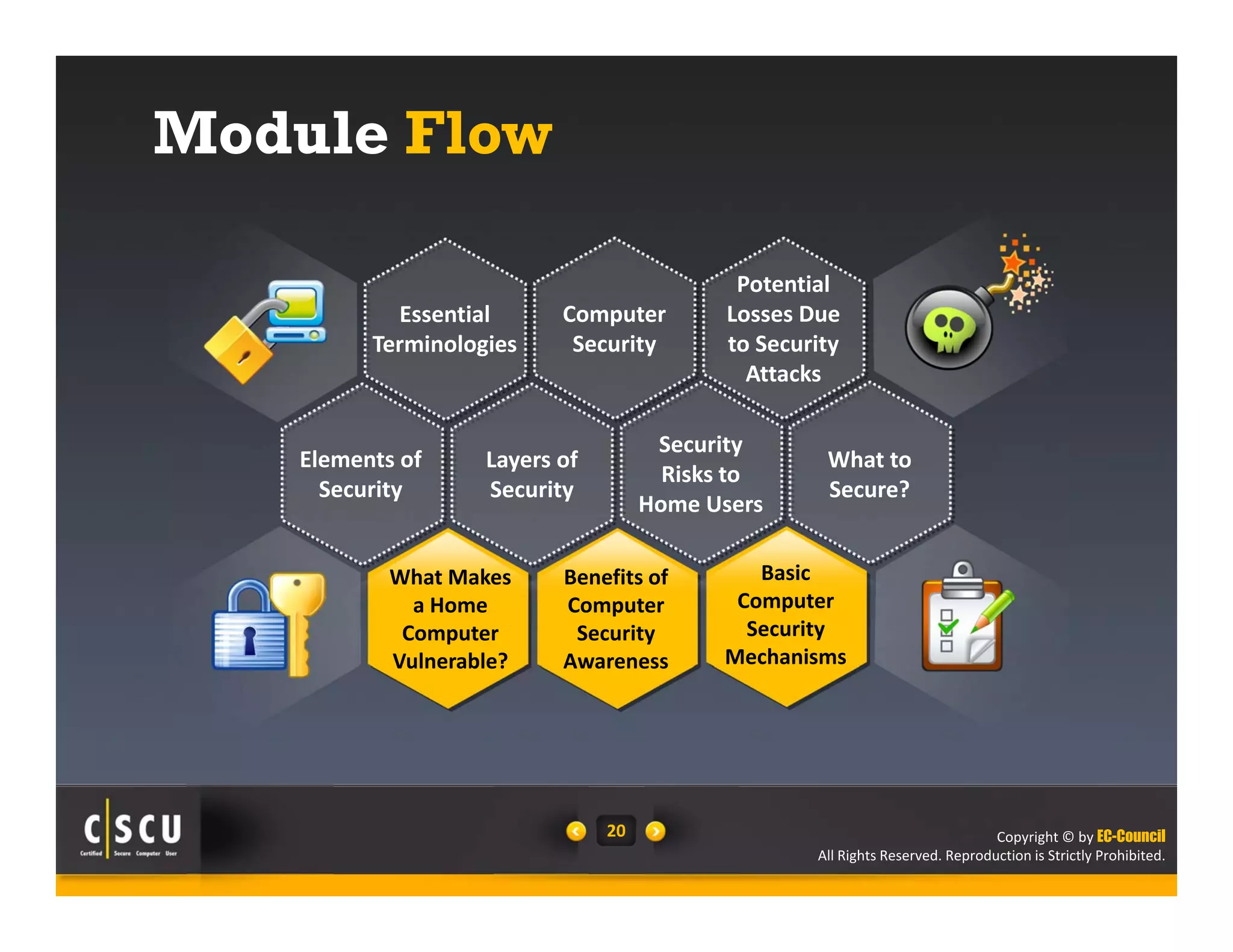
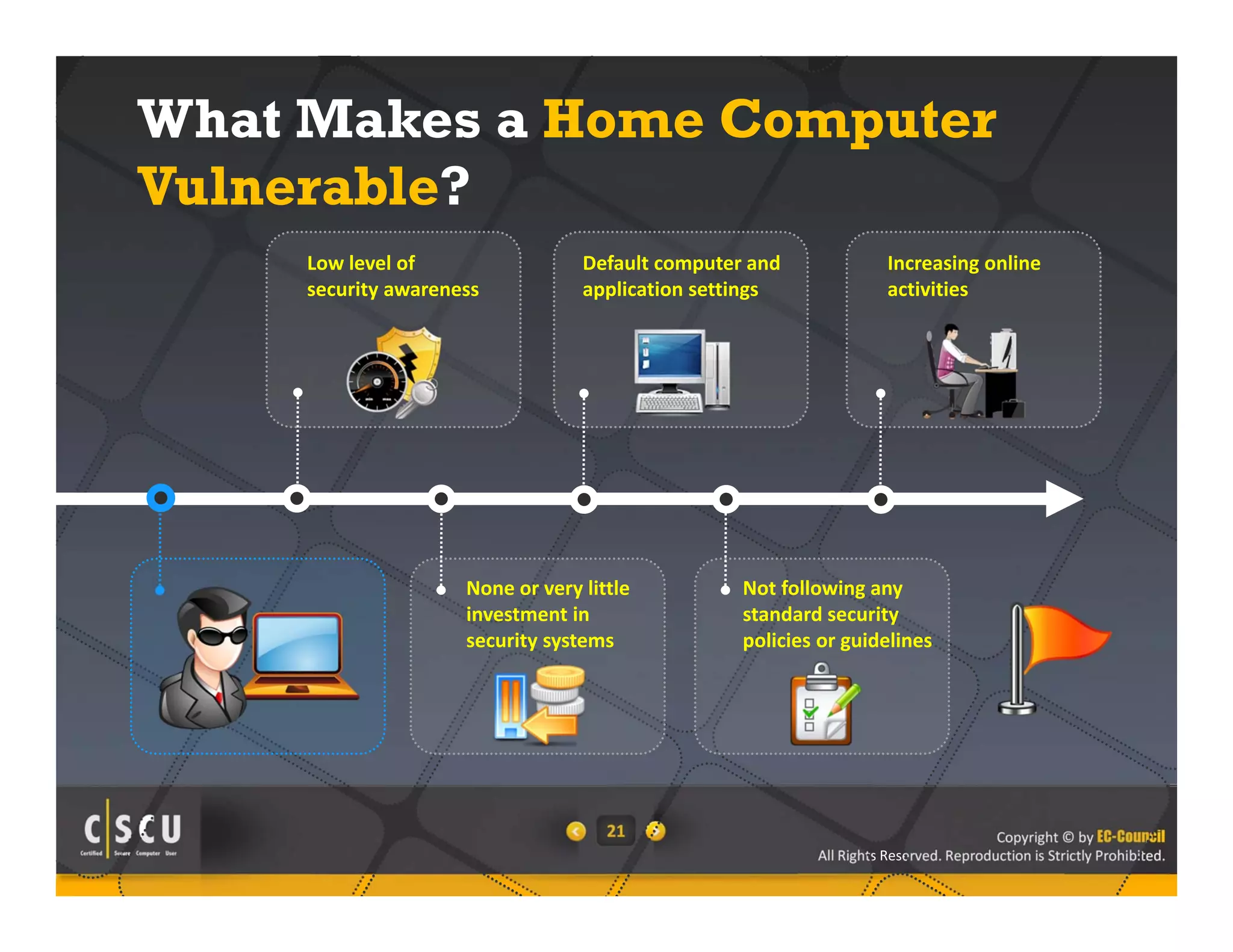
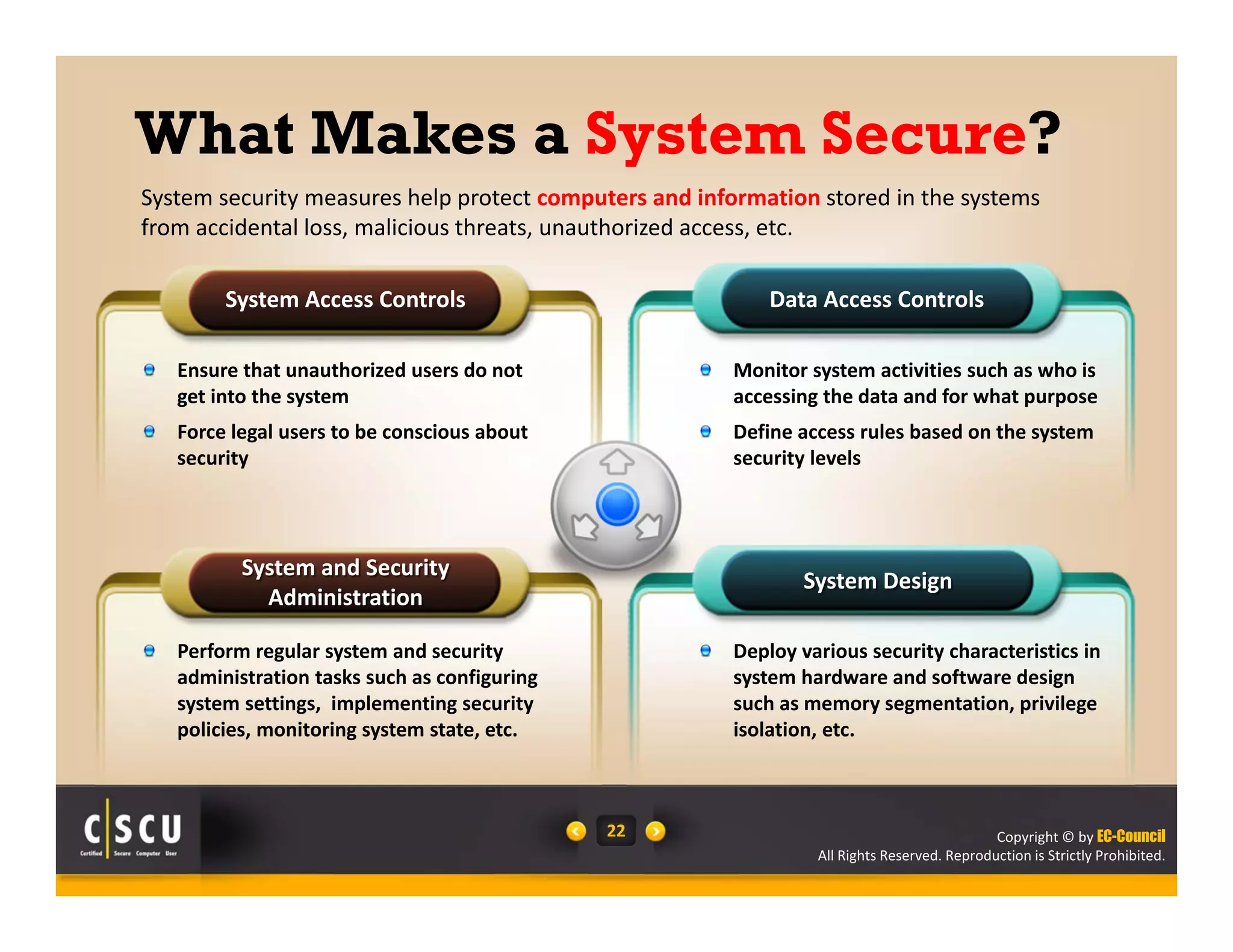
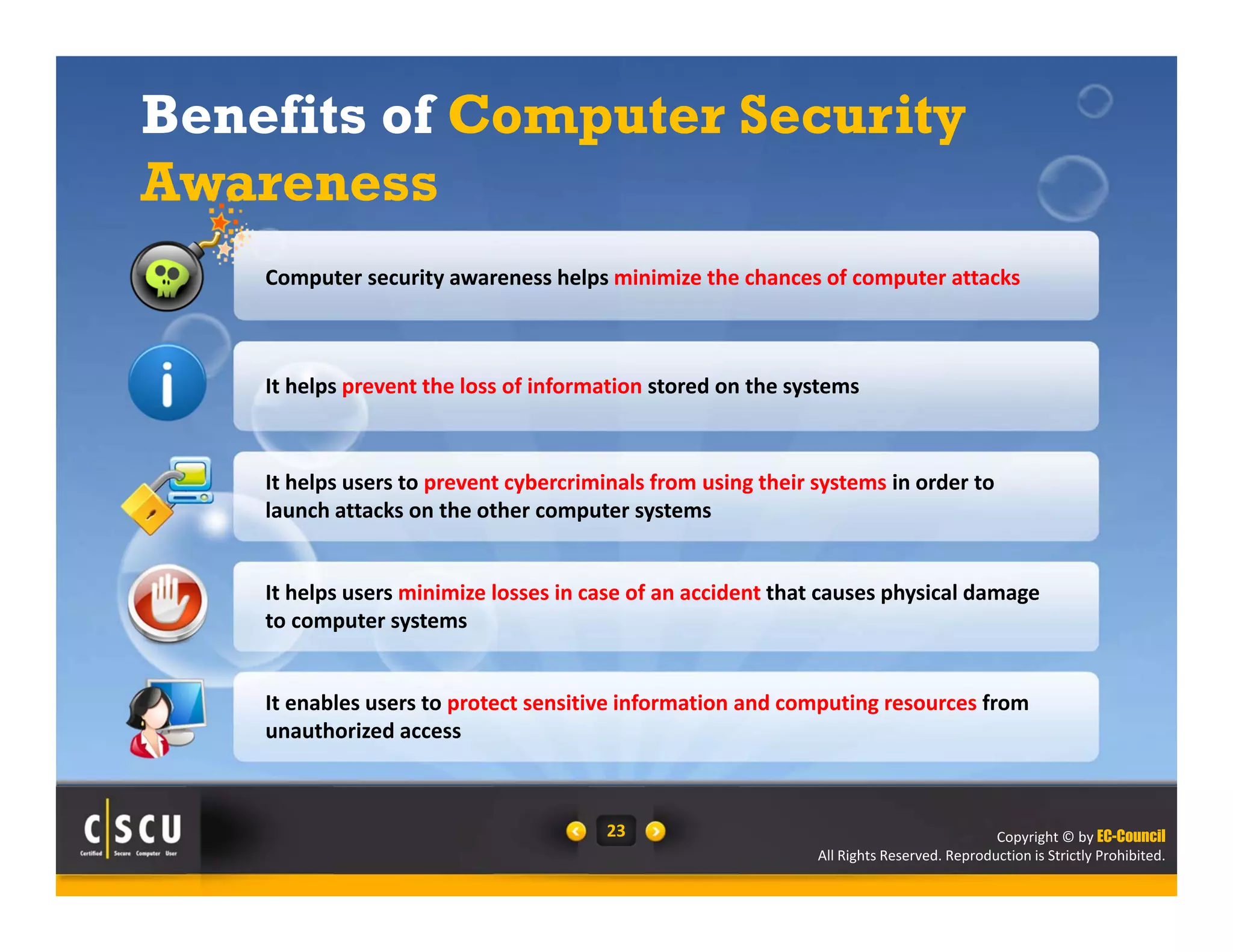
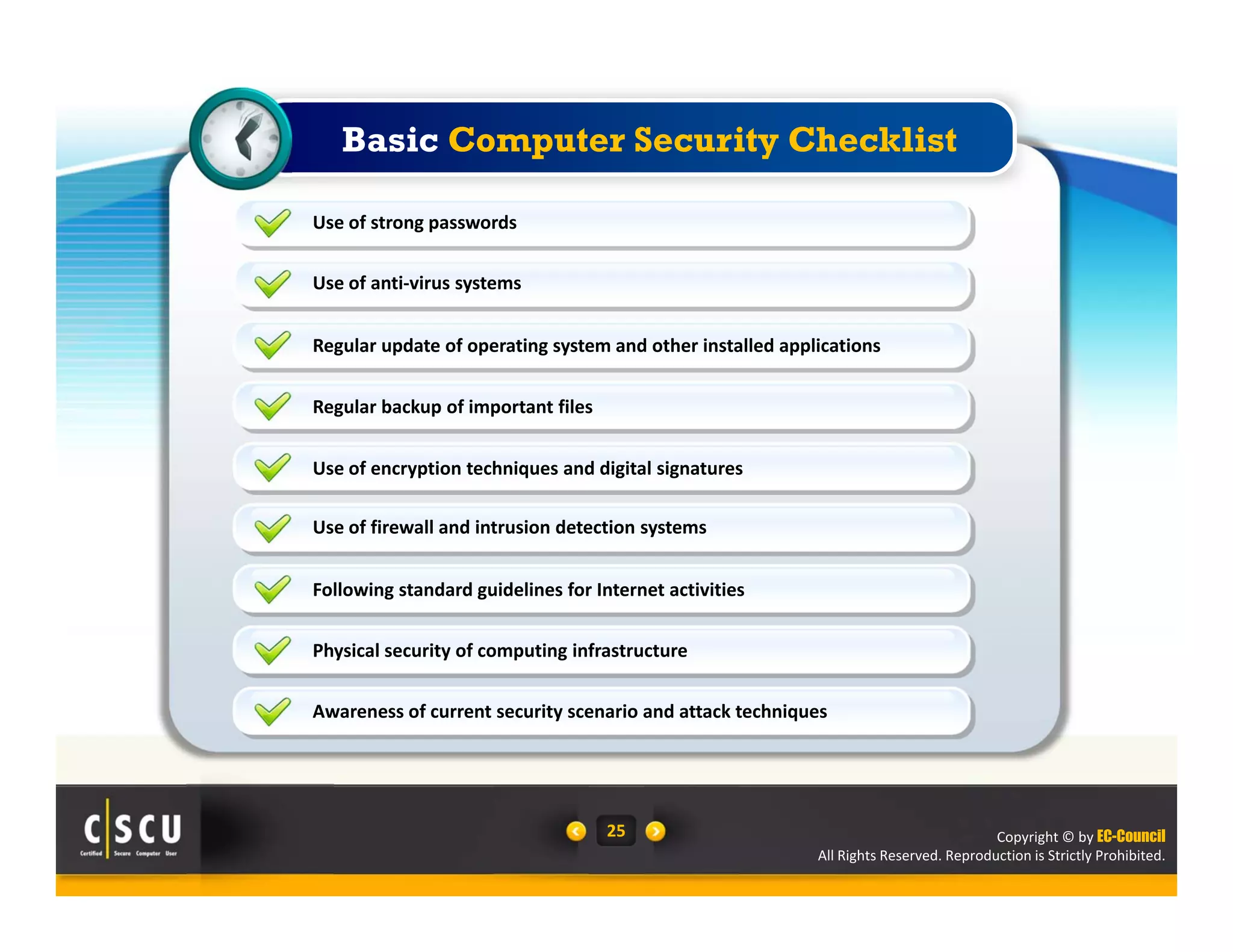
Franklin downloaded free software that infected his system with malware. After installing the software, Franklin's system rebooted and started malfunctioning. The document discusses computer security risks for home users, including risks from computer attacks like malware infections and accidents that can cause physical damage. It also covers essential computer security topics like threats, vulnerabilities, security elements, and defenses that can help secure systems and information.