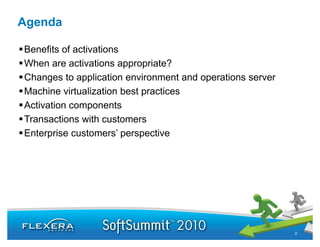
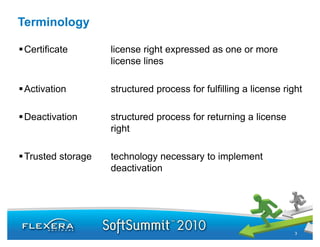
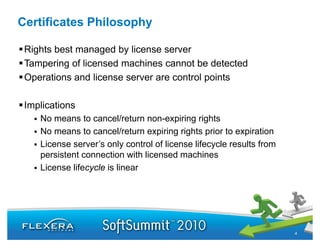
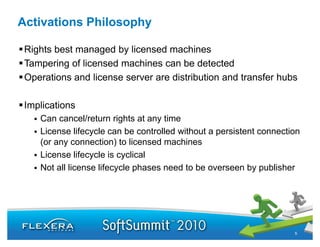
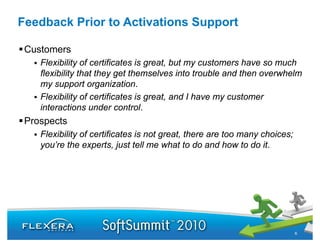
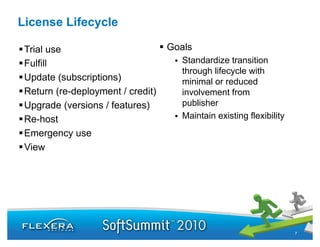
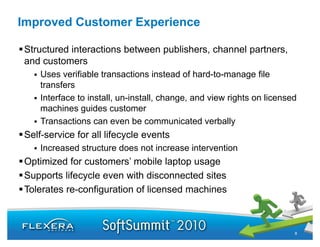
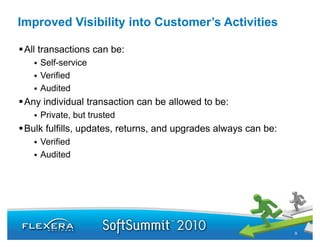
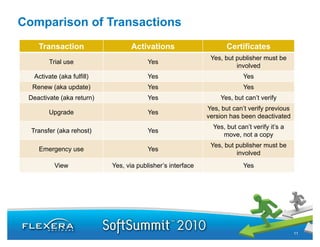
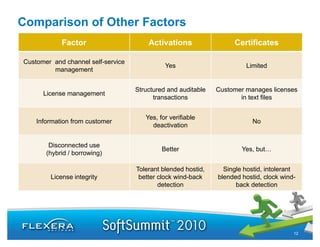
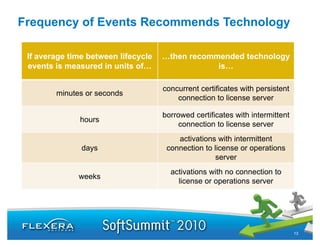
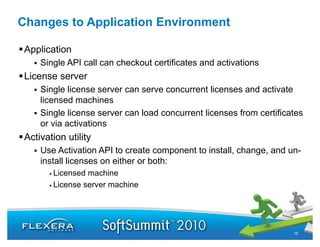
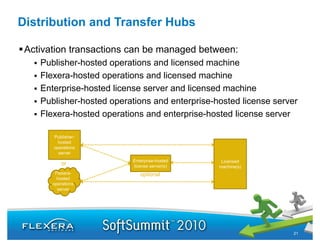
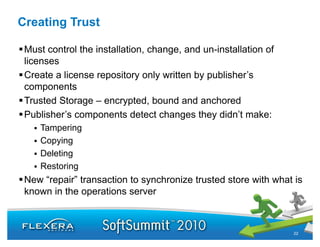
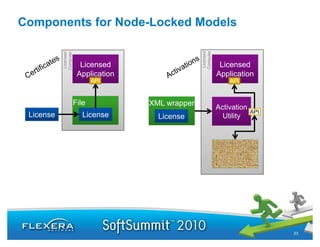
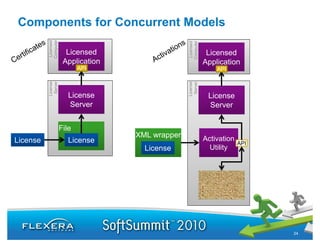
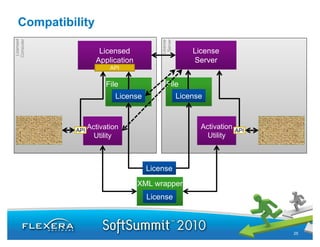
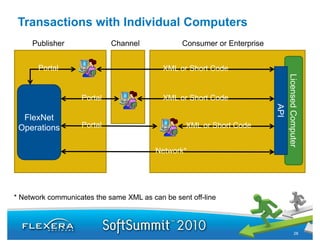
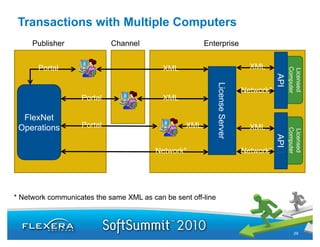
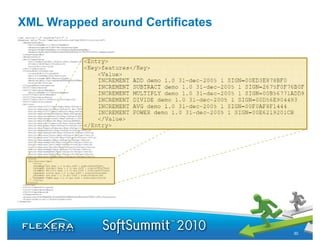
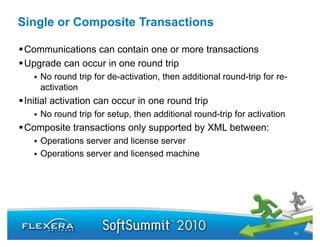
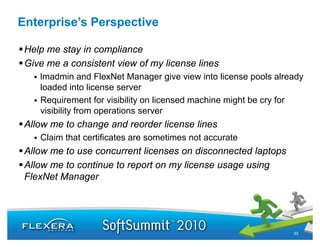
This document discusses the benefits of migrating from software license certificates to activations. It outlines that activations provide more flexibility in managing the license lifecycle by allowing licenses to be canceled, returned, or upgraded at any time without needing a persistent connection to a license server. Activations also allow for more visibility into customer license usage through structured, auditable transactions. The document provides guidelines on when activations are most appropriate based on the frequency of license lifecycle events and compares activations to certificates. It also describes changes needed to applications, license servers, and operations servers to support activations.