Embed presentation

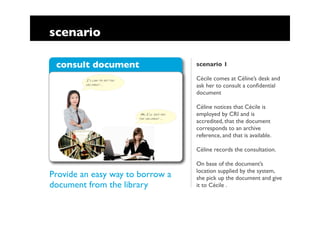
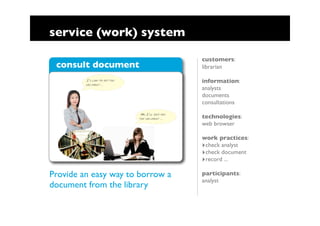




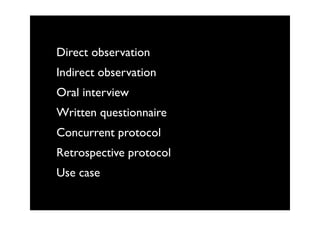






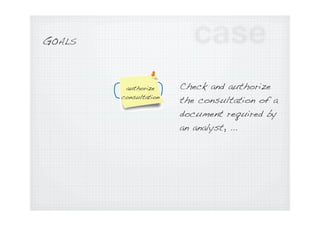
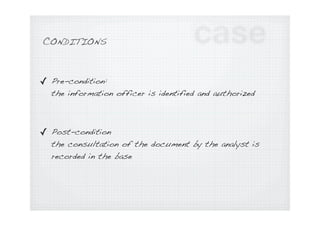


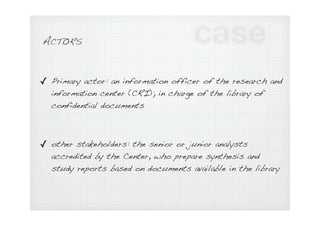

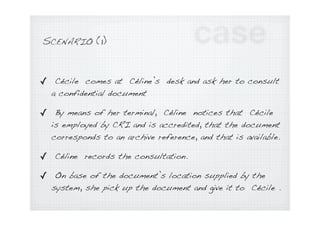
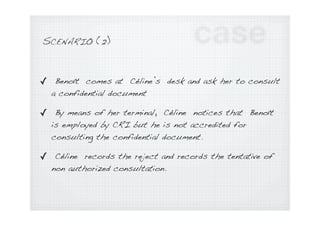
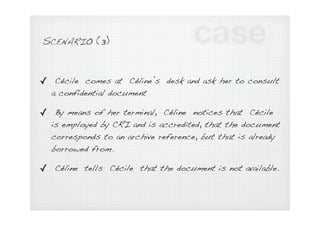


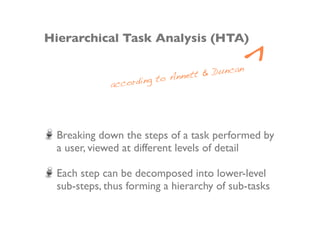
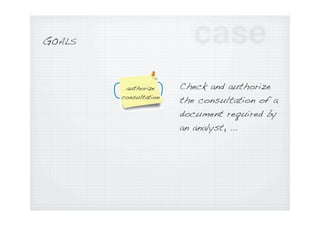
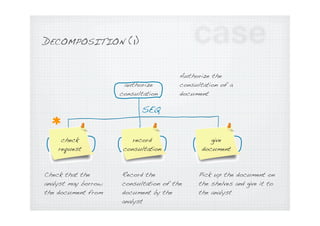
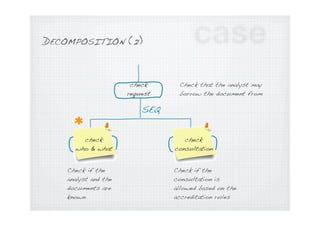
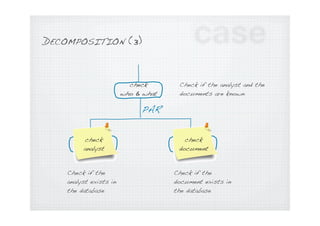
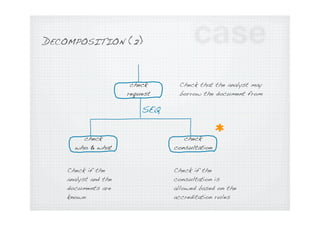
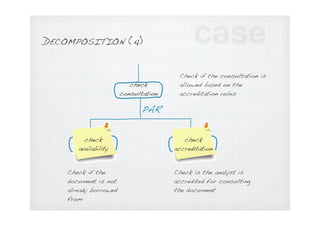
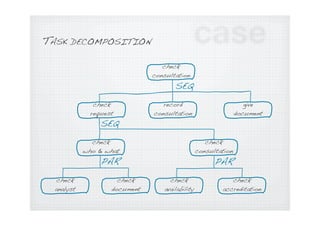
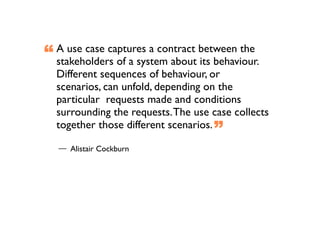
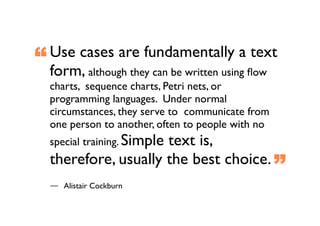
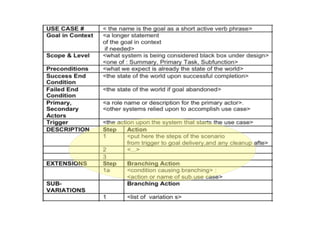
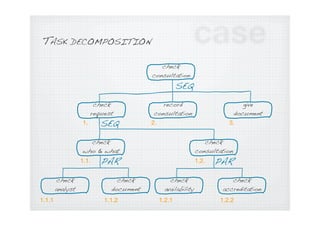
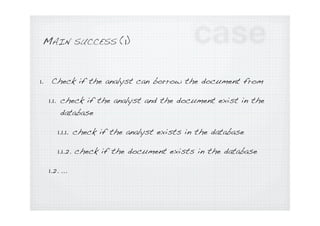
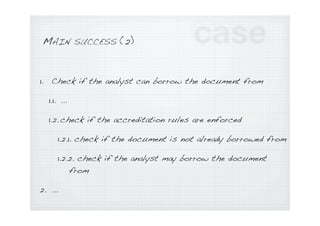
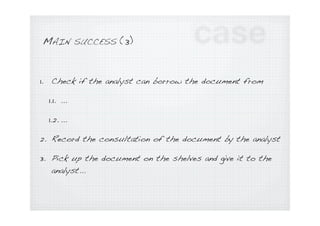
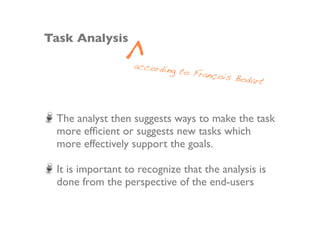
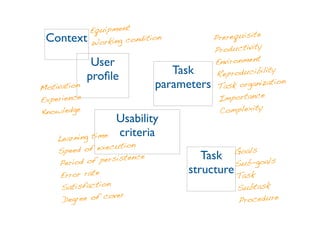







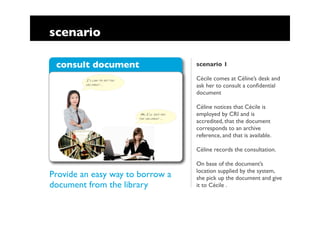
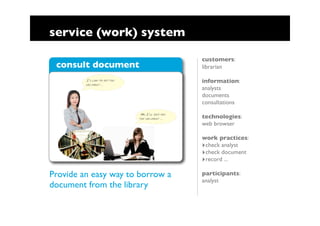
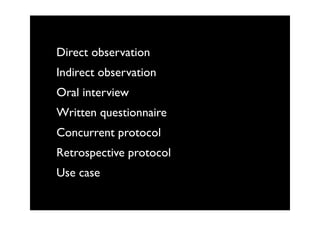
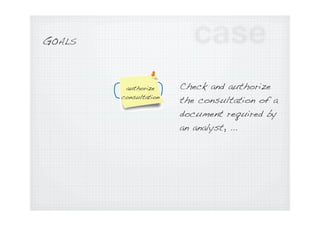
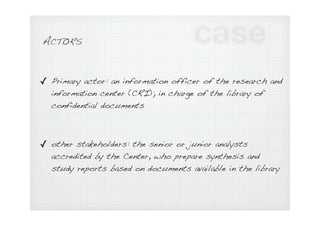
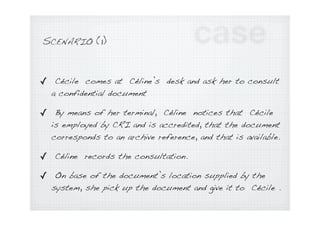
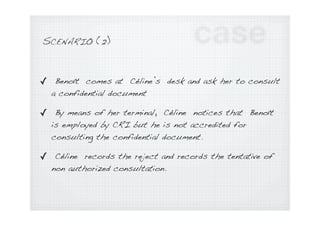
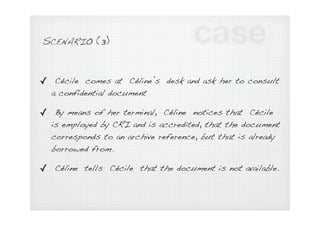
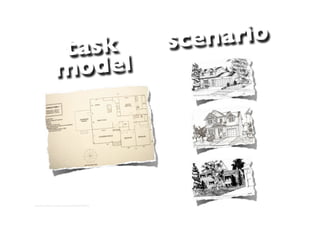
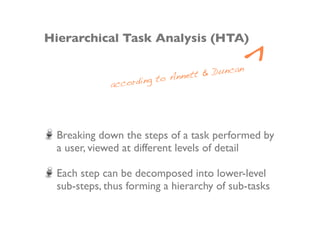
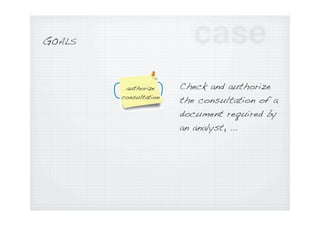
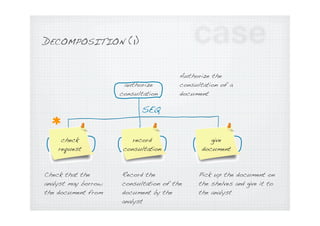
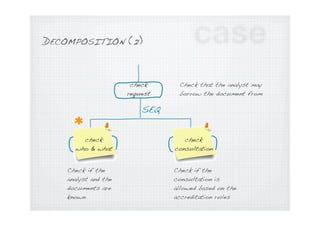
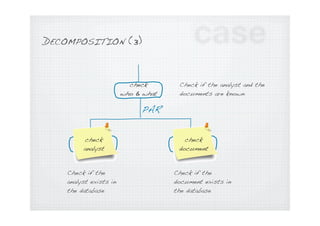
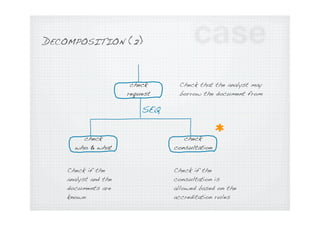
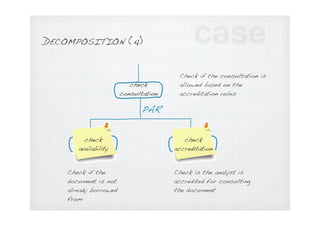
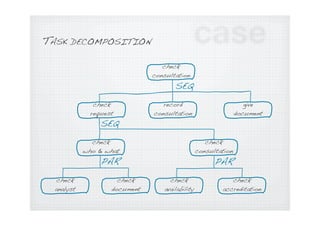
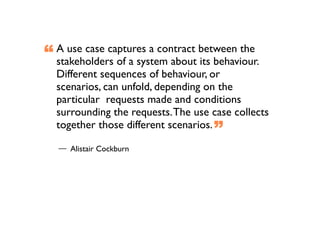
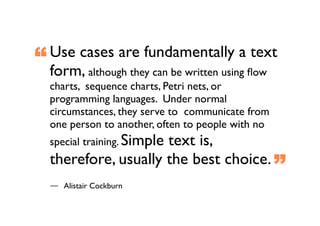
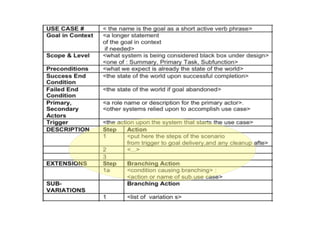
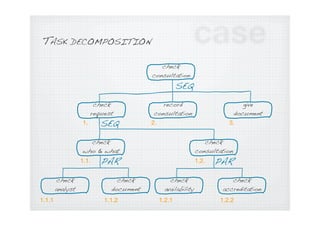
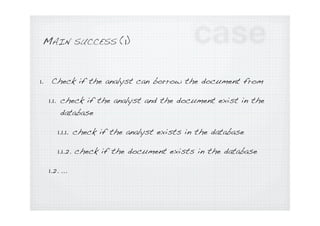
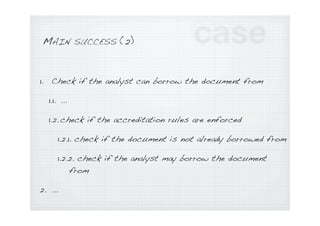
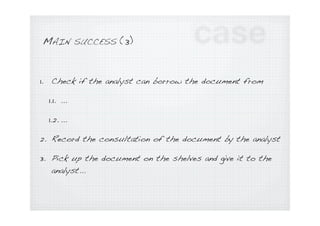
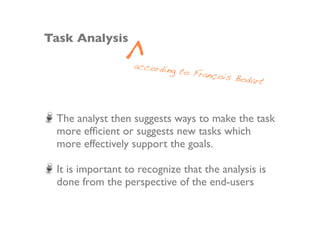
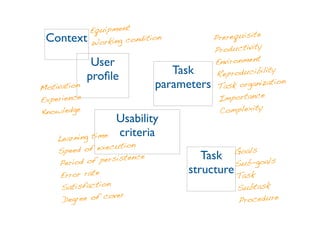
The document provides an overview of tasks for analyzing e-business services, including task analysis, user observation, goal definition, scenario development, and hierarchical task decomposition. Key aspects covered include defining goals, preconditions and postconditions, identifying actors and their roles, describing scenarios as sequences of actions, and breaking down tasks into hierarchical sub-tasks.