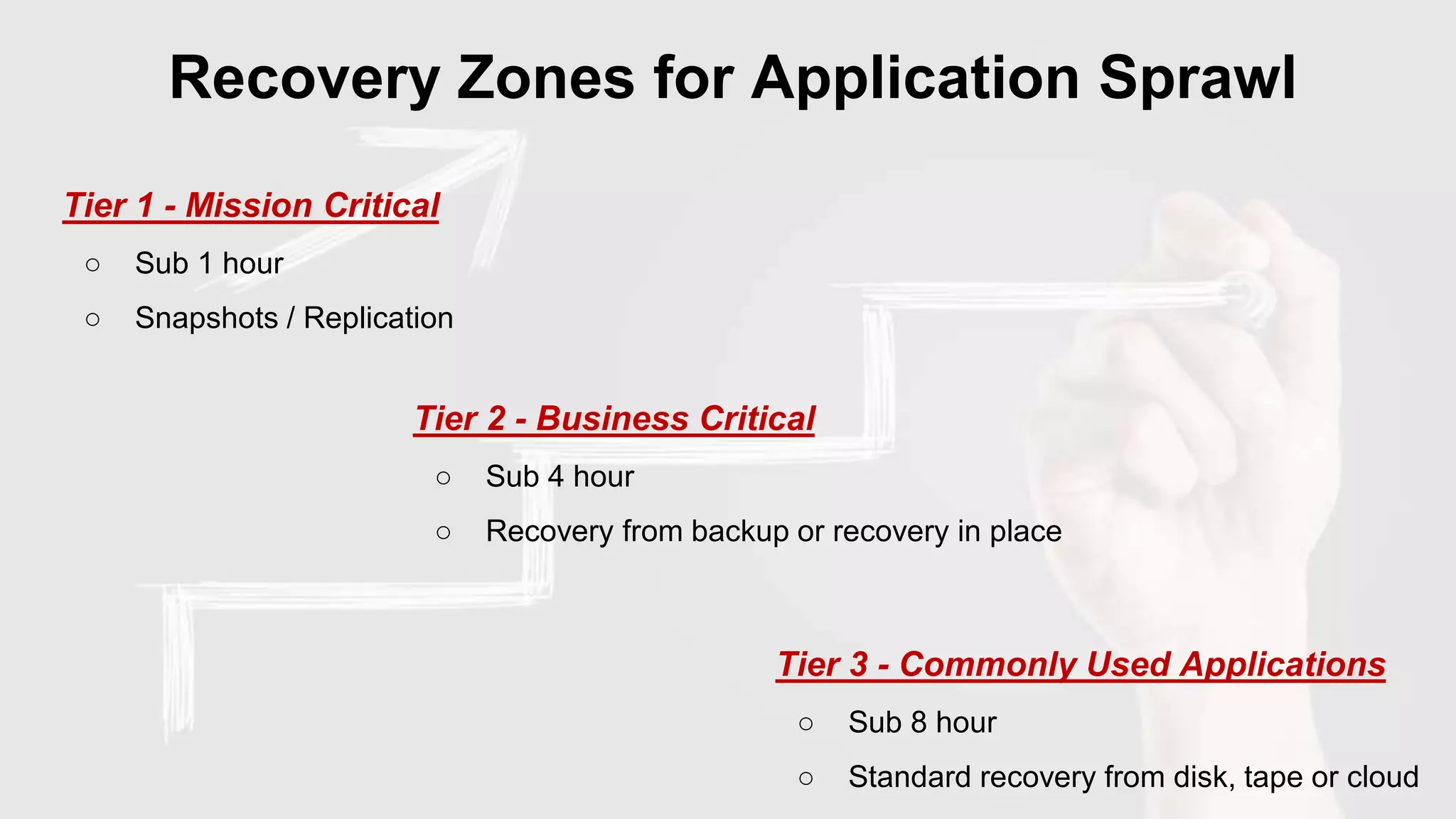
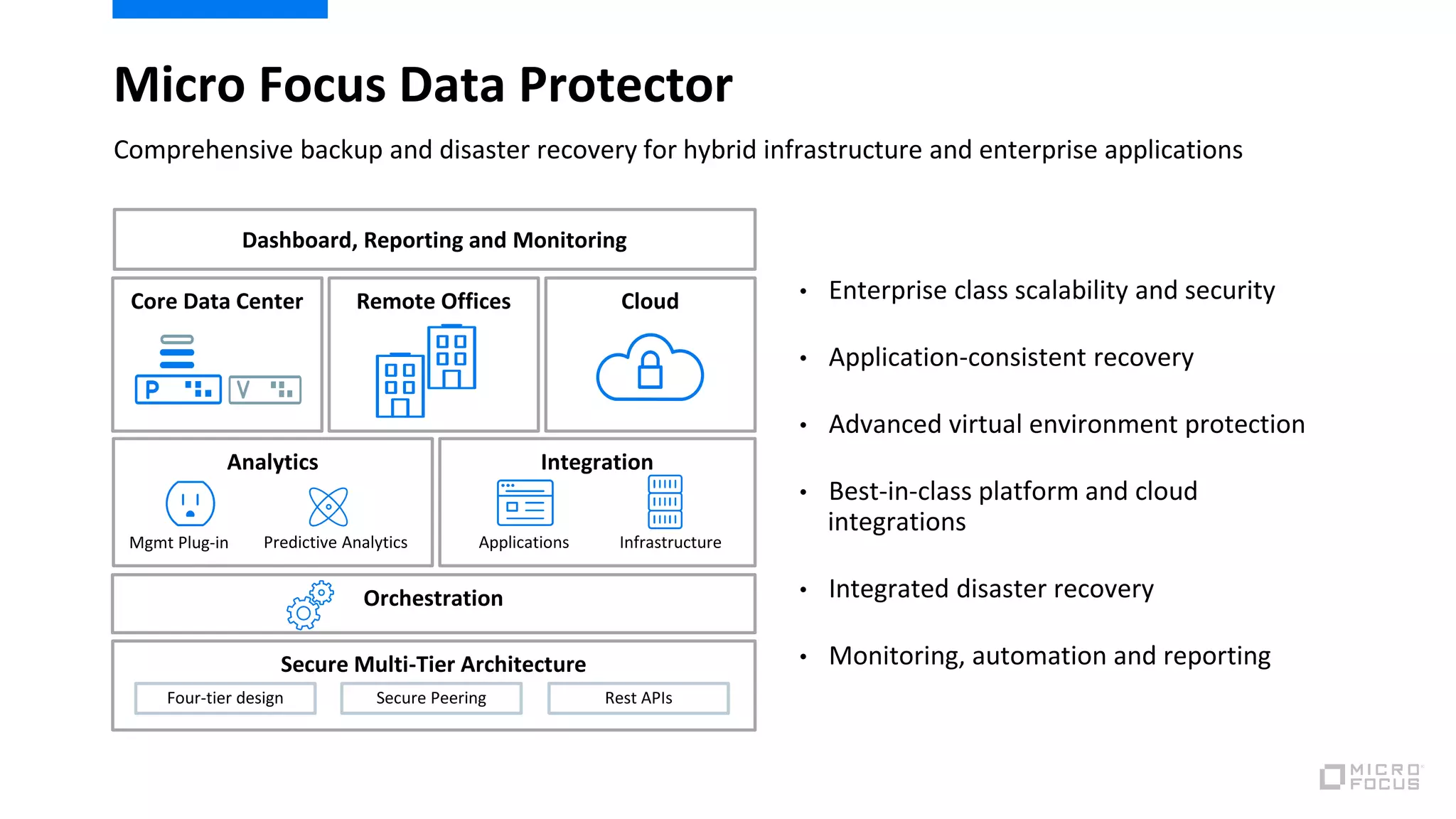
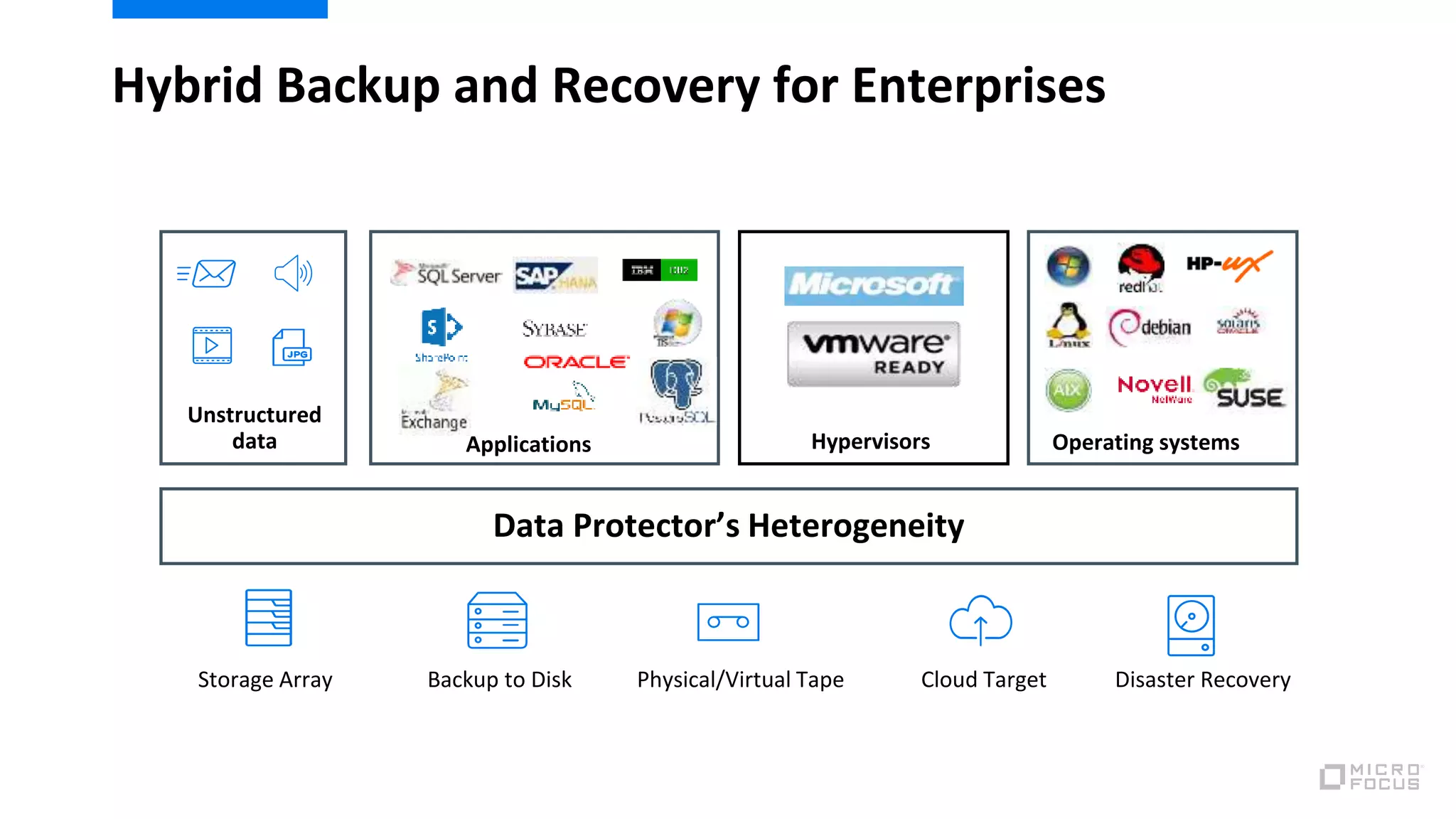
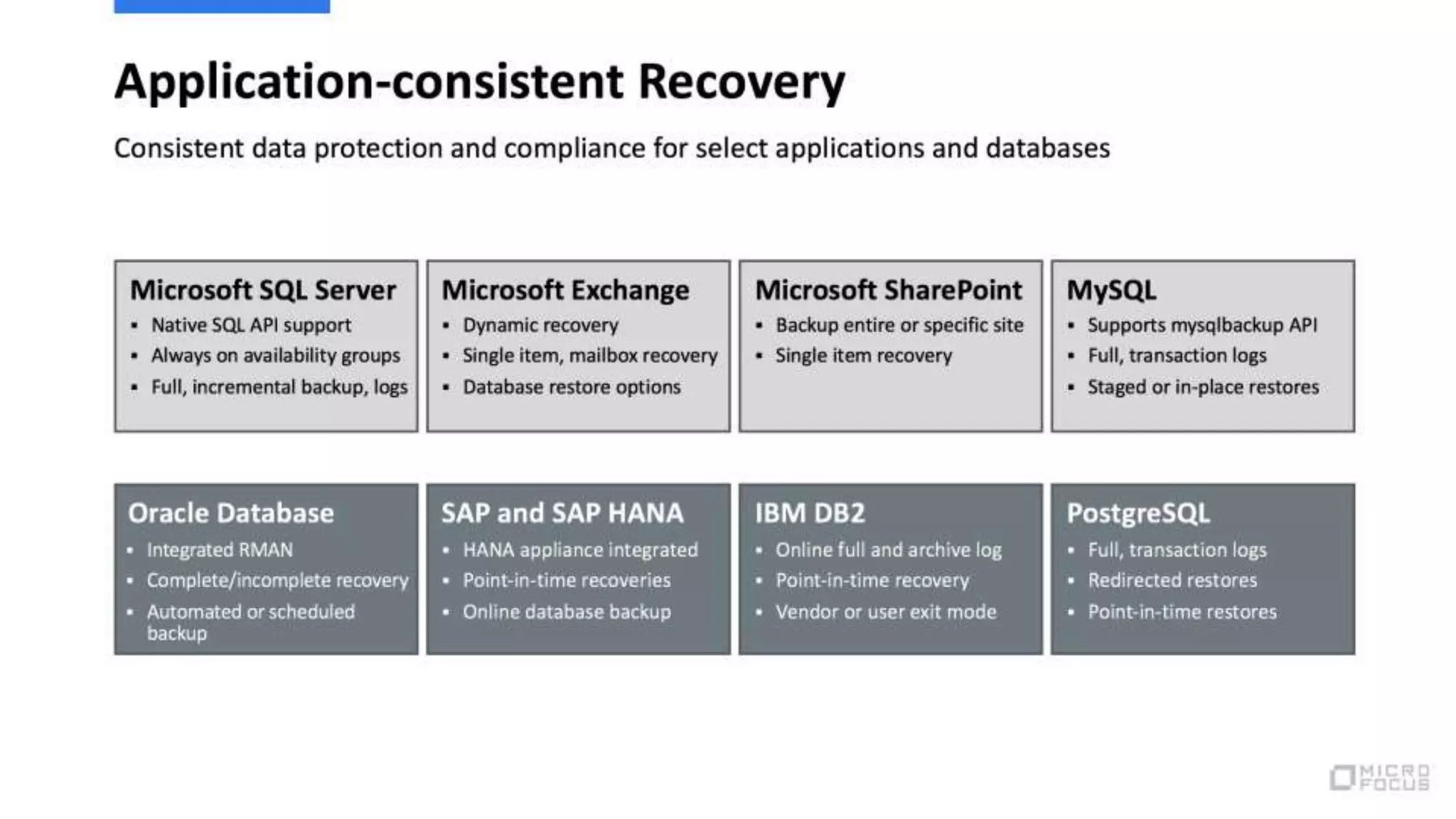
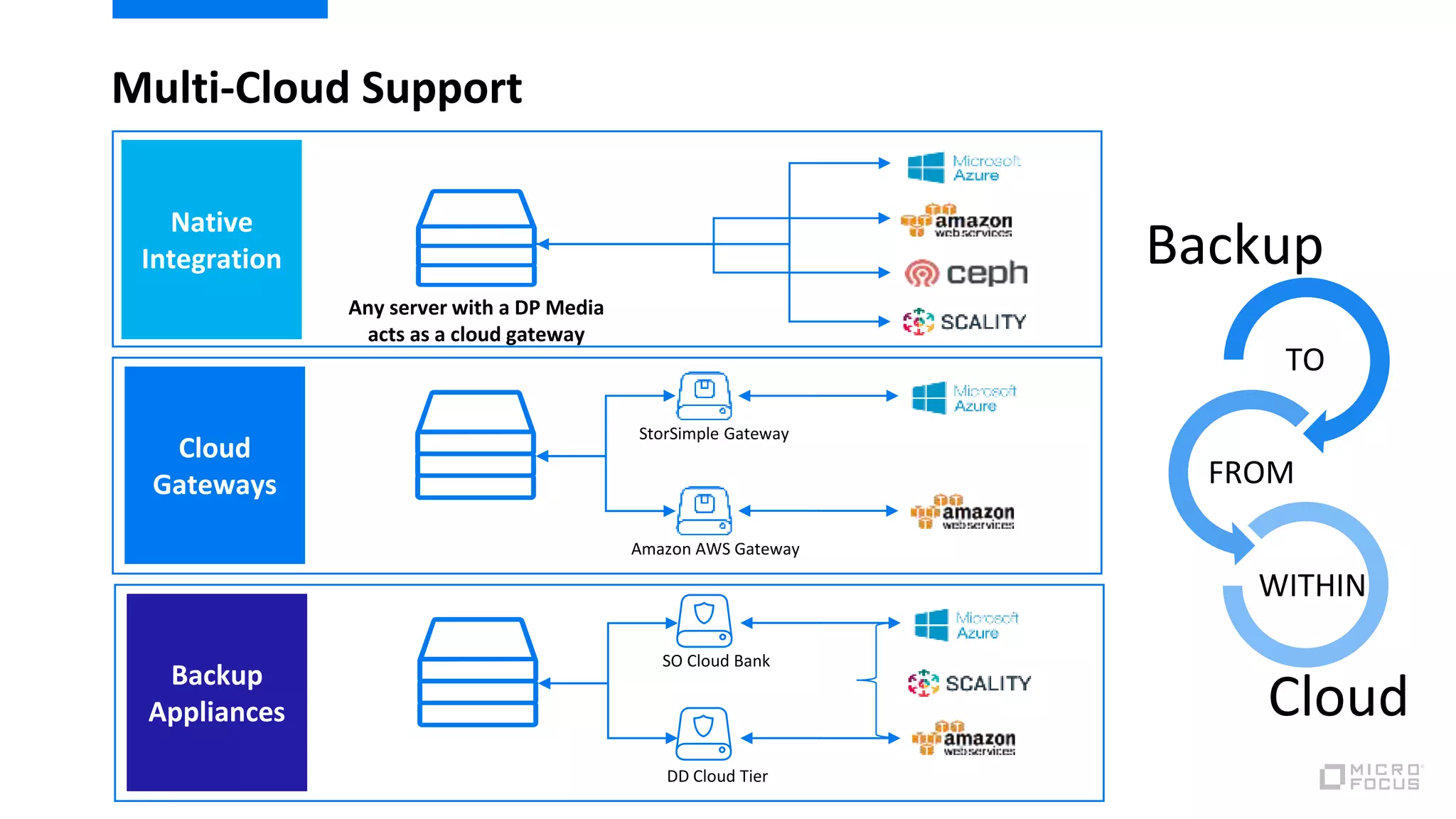
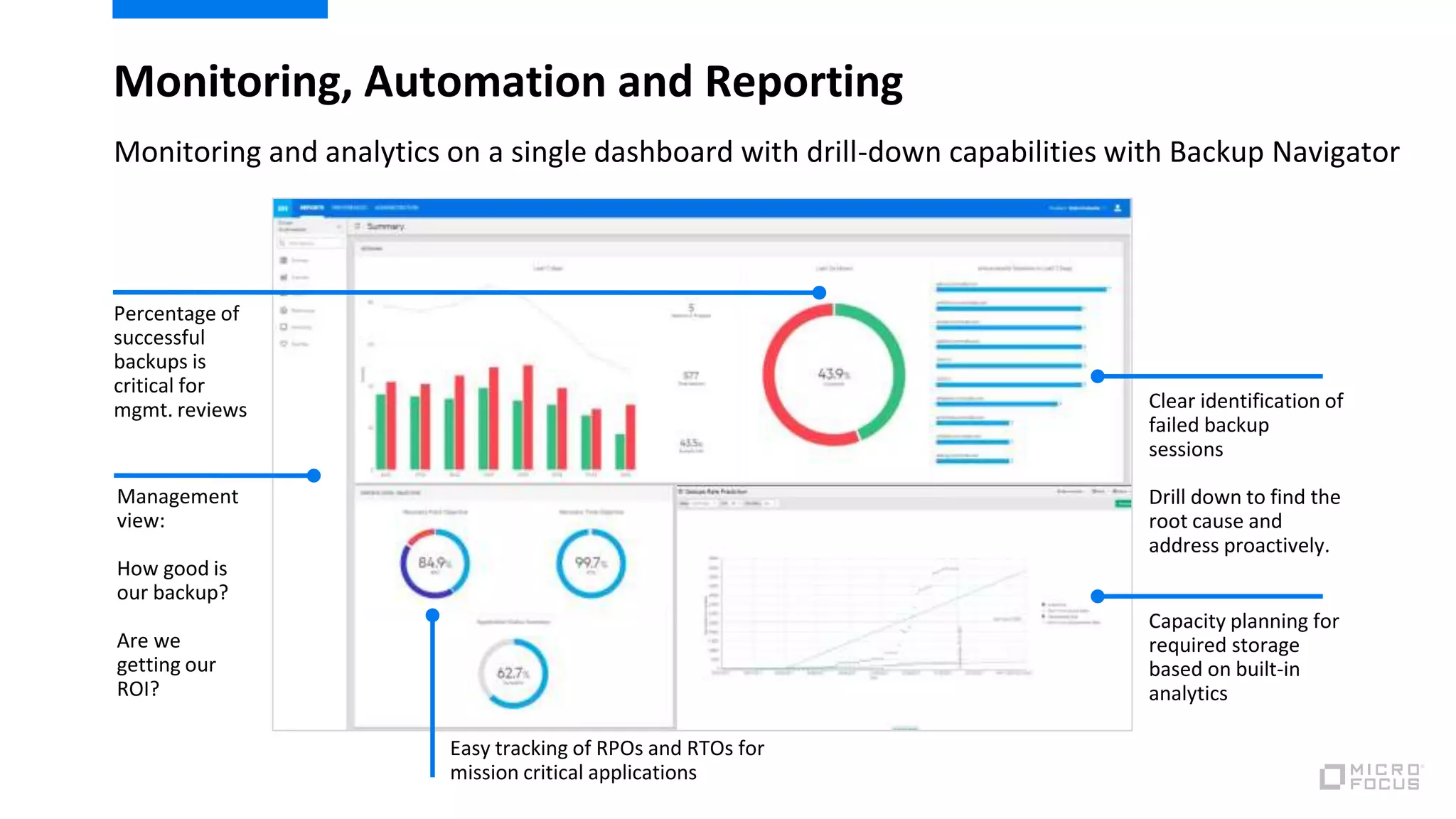
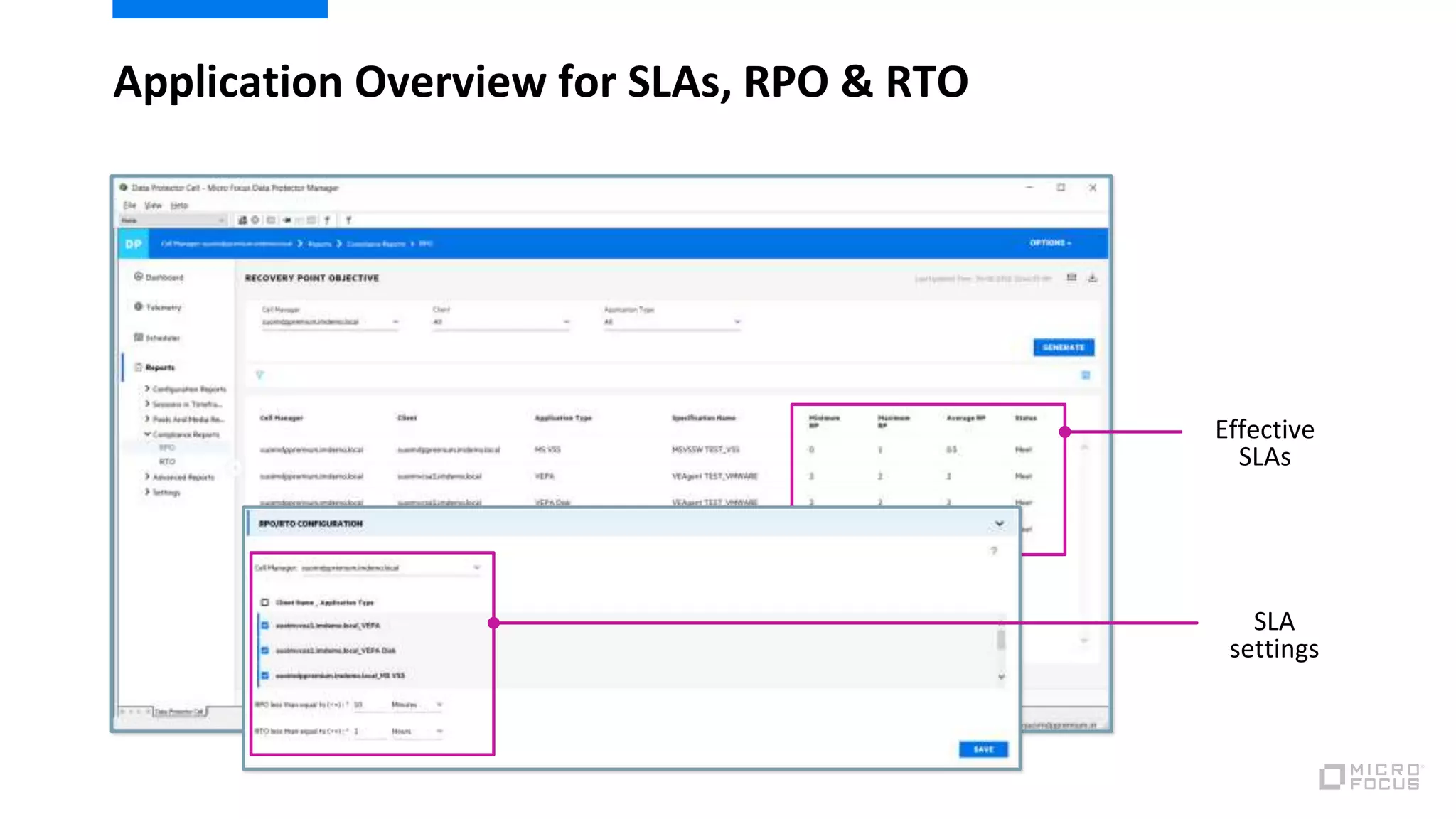
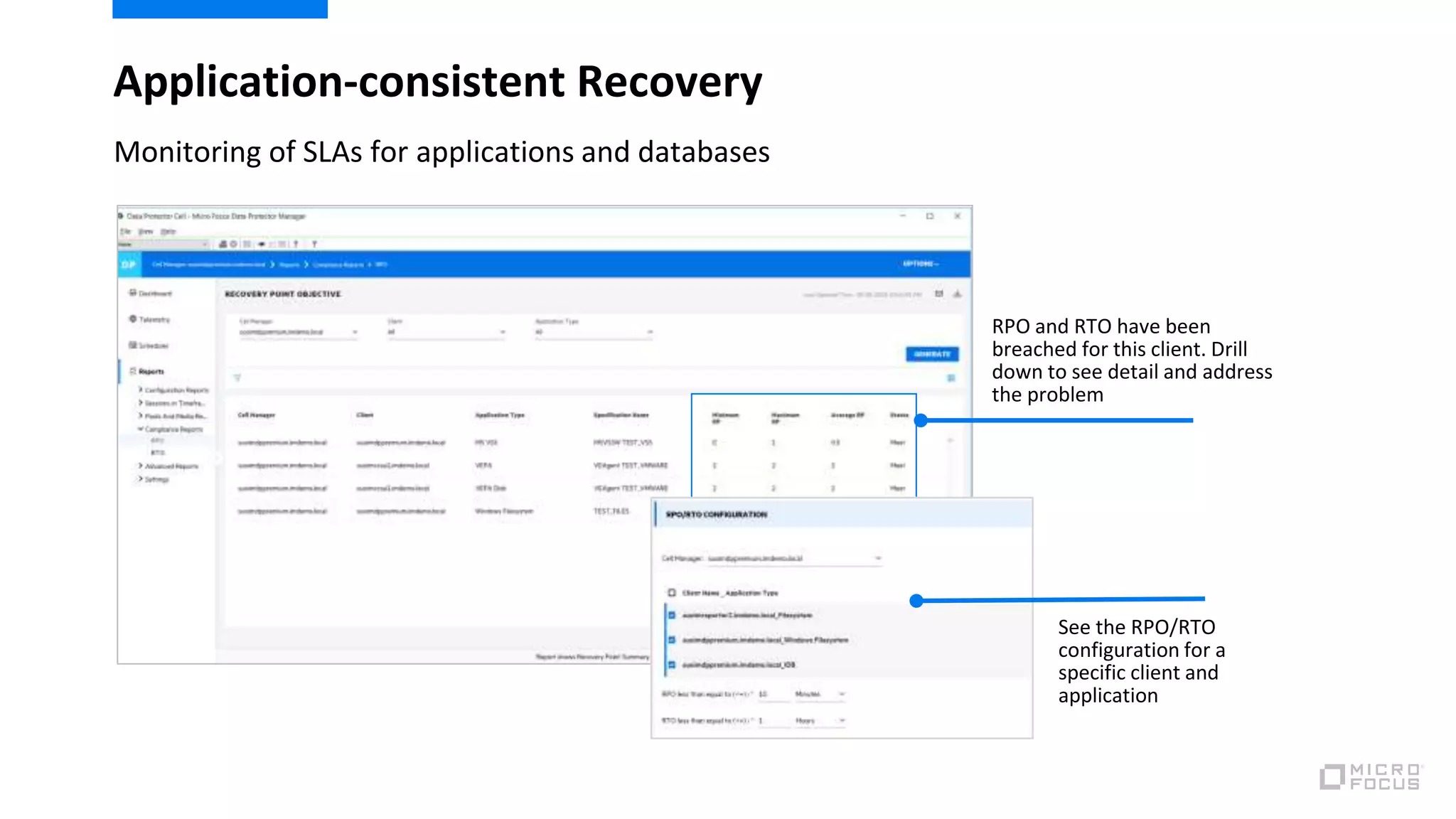
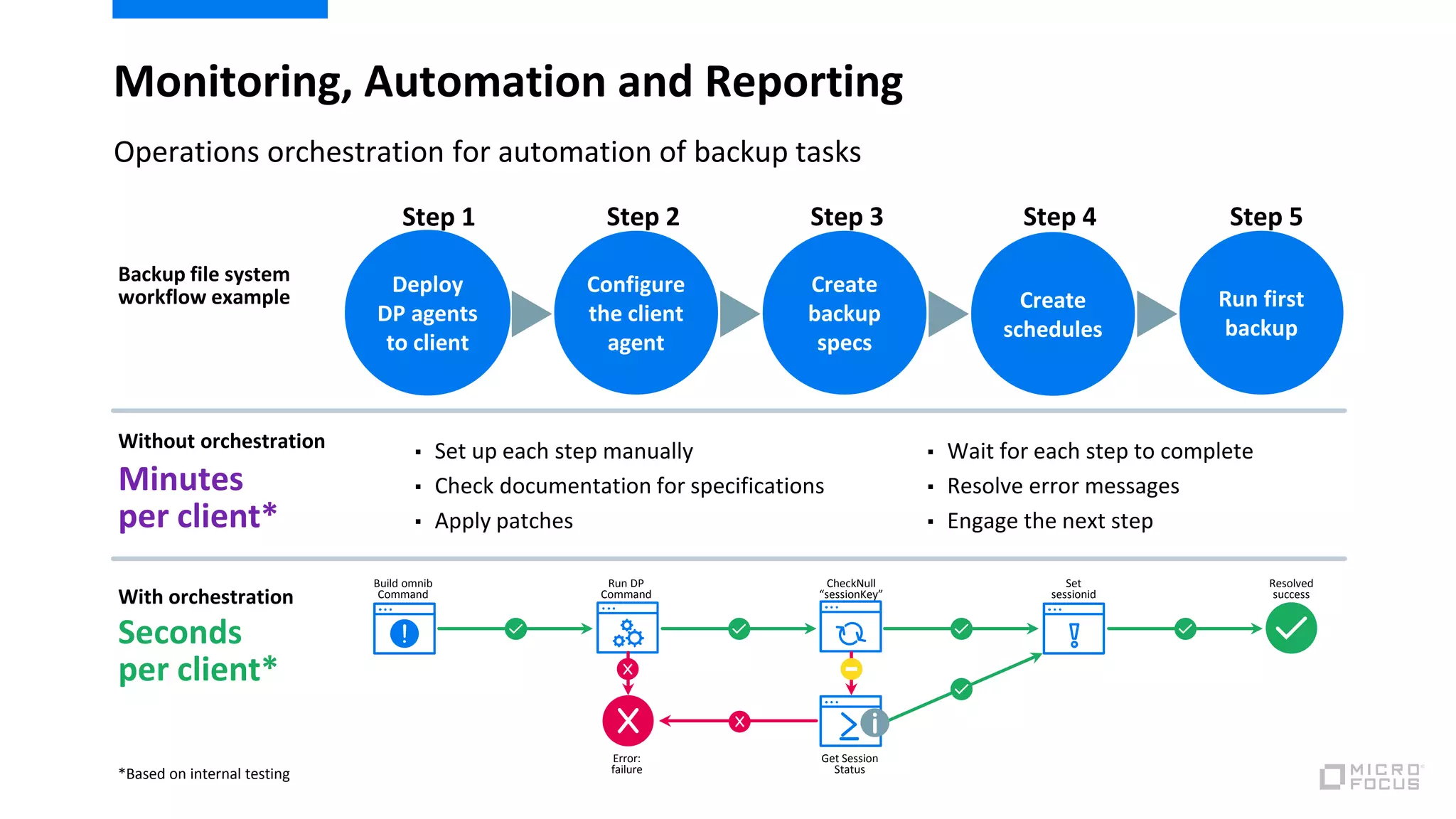
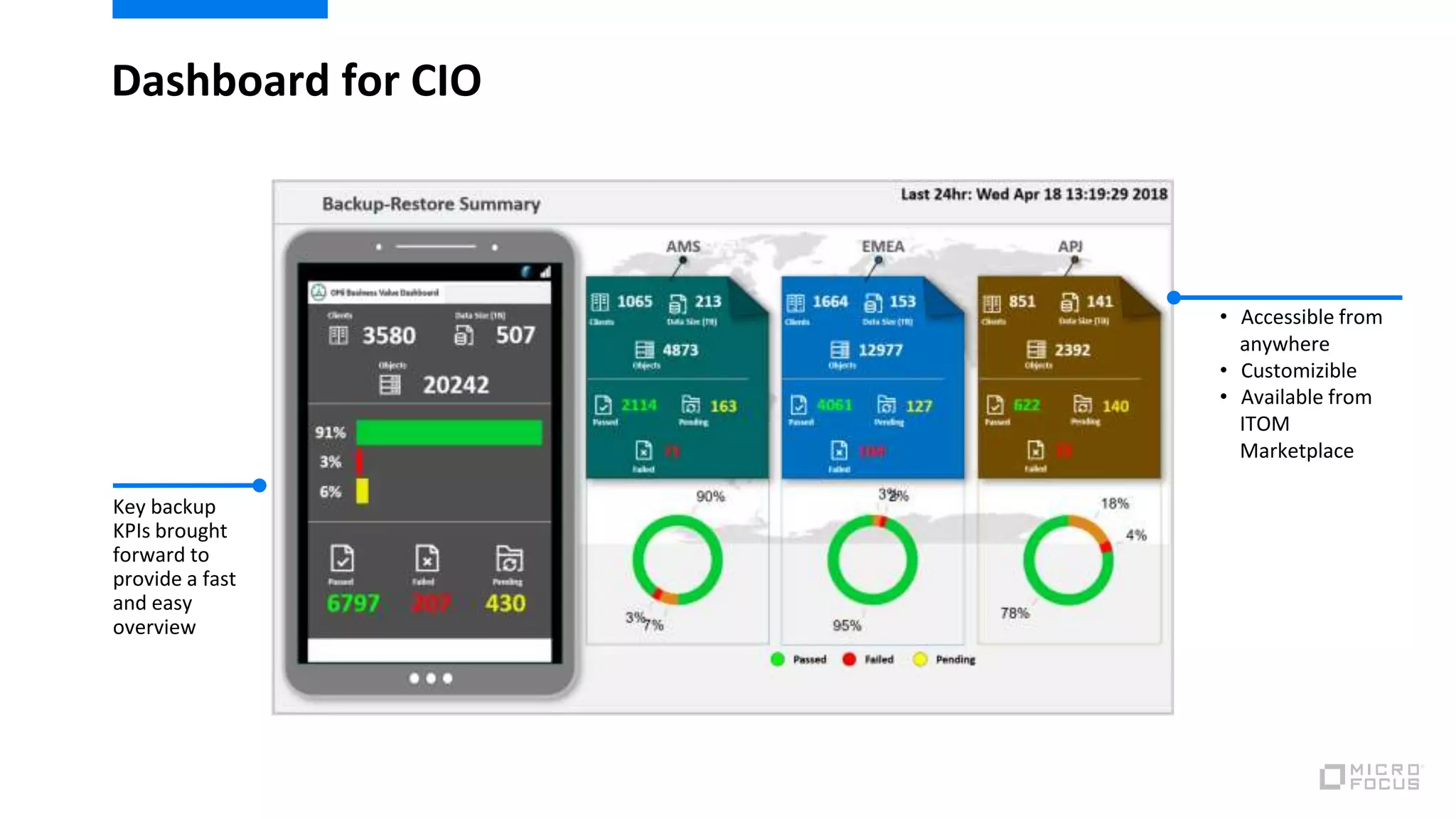
The document discusses the importance of service-level-driven data protection in the context of increasing application complexity and the need to ensure recovery objectives like RPO and RTO are met. It emphasizes establishing specific service levels for different applications, including mission-critical, business-critical, and commonly used applications, and outlines the necessary protocols for backups and recovery. Additionally, it highlights features of Micro Focus Data Protector as a comprehensive solution for hybrid infrastructure backup and disaster recovery, with monitoring and analytics capabilities.