The document describes key concepts related to web services and Service Oriented Architecture (SOA). It defines web services, SOAP, WSDL, UDDI, service roles, and message exchange patterns. It provides examples of how these concepts apply when an invoice submission service sends an electronic invoice to an accounts payable service. It also includes a sample WSDL document for an arithmetic calculator web service to illustrate how abstract and concrete descriptions are defined.
![9
4.2.1.4 Service Contract
• A service contract comprised of a collection of service descriptions(WSDL) and
additional documents(XSD schema, policy, SLA)
4.2.1.5 Semantic descriptions
• A semantic description is a supplementary documentation published along with service
descriptions (WSDL) to provide sufficient semantic information in a structured manner so
that, service requestors can evaluate and choose suitable service providers independently.
• Service policies can be designed to express the semantic descriptions of service behavior.
4.2.1.6 Service description advertisement and discovery
– Advertising and discovering service descriptions may become necessary for
amount of services increases within and outside of organizations.
– Universal Description, Discovery, and Integration (UDDI) provides a registry
model worth describing.
• Private and public registries
– UDDI is a accepted standard for structuring registries that keep track of service
descriptions These registries can be searched manually and accessed
programmatically.
– Public registries accept registrations from any organizations. Once signed up,
organizations acting as service provider can register their web services.
– Private registries can be implemented within organization boundaries to provide a
central repository for descriptions of all services the organization develops, leases,
or purchases.
Ex: Arithmetic web service in .NET
public class WebService : System.Web.Services.WebService {
public WebService () {
//InitializeComponent();
}
[WebMethod]
public string HelloWorld() {
return "Hello World";](https://image.slidesharecdn.com/soa-unitiv-webservices-notes-191010114450/75/Web-services-Notes-9-2048.jpg)
![10
}
[WebMethod]
public int add(int a, int b)
{
return (a+b);
}
[WebMethod]
public int sub(int a, int b)
{
return (a - b);
}
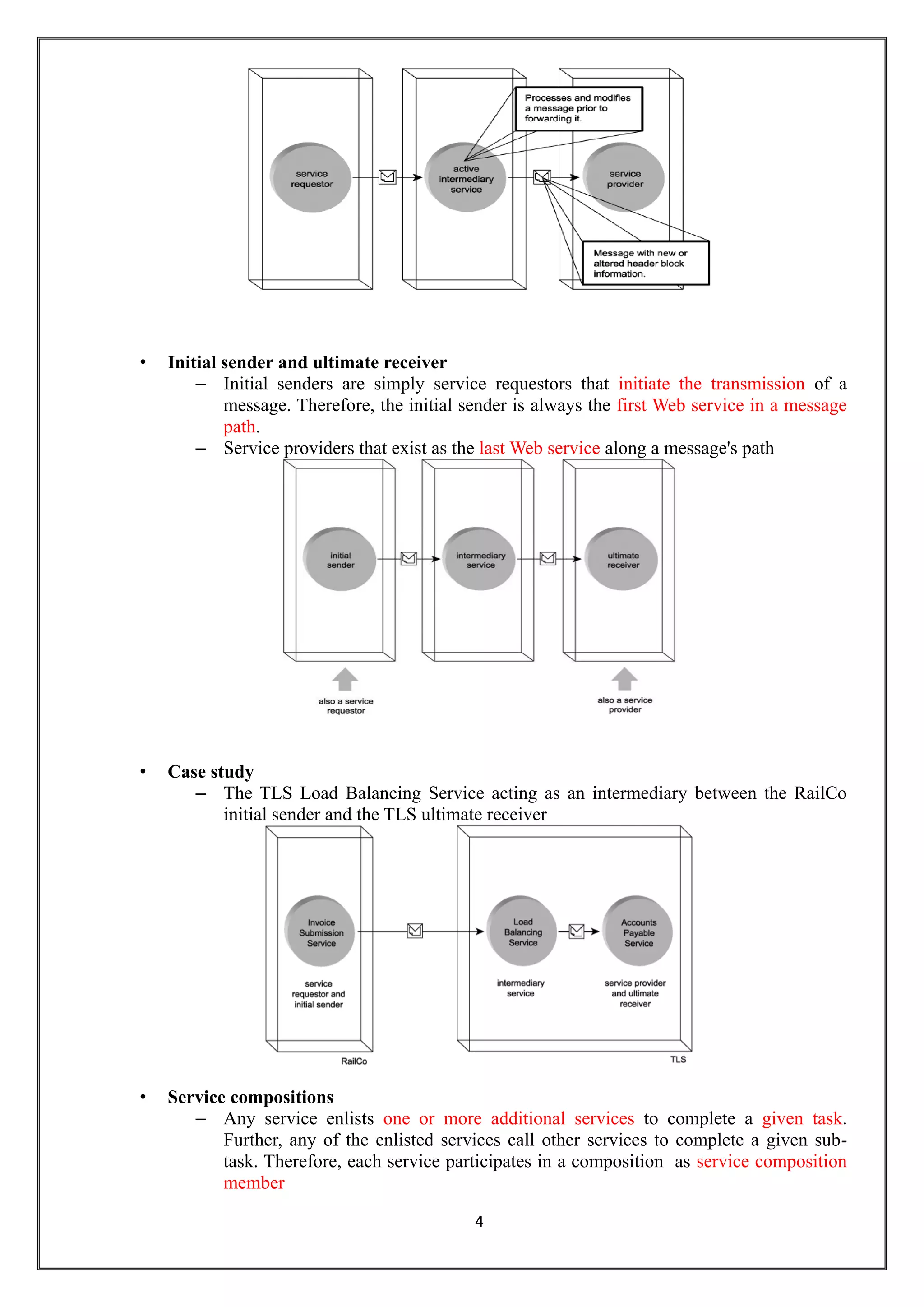
4.2.2 WSDL document for Arithmetic calculator web service (16 marks)
<wsdl:portType name="WebServiceSoap">
<wsdl:operation name="add">
<wsdl:input message="tns:addSoapIn"/>
<wsdl:output message="tns:addSoapOut"/>
</wsdl:operation>
<wsdl:operation name="sub">
<wsdl:input message="tns:subSoapIn"/>
<wsdl:output message="tns:subSoapOut"/>
</wsdl:operation>
</wsdl:portType>
<wsdl:binding name="WebServiceSoap" type="tns:WebServiceSoap">
<soap:binding transport="http://schemas.xmlsoap.org/soap/http"/>
<wsdl:operation name="add">
<soap:operation soapAction="http://tempuri.org/add" style="document"/>
<wsdl:input>
<soap:body use="literal"/>
</wsdl:input>
<wsdl:output>
<soap:body use="literal"/>
</wsdl:output>
</wsdl:operation>
</wsdl:binding>
SOAP input message (Service requestor)
<?xml version="1.0" encoding="utf-8"?>
<soap:Envelope xmlns:xsi="http://www.w3.org"
<soap:Body>
<add xmlns="http://tempuri.org/">](https://image.slidesharecdn.com/soa-unitiv-webservices-notes-191010114450/75/Web-services-Notes-10-2048.jpg)