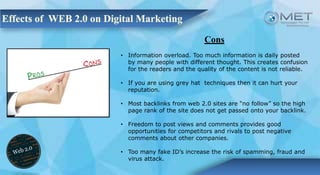
Web 2.0 represents the second generation of the World Wide Web, characterized by enhanced user interaction and the creation of online communities. It marks a shift from static web pages (Web 1.0) to more dynamic, participatory platforms that promote content sharing and collaboration. While it offers benefits such as high-quality content creation and traffic generation, it also presents challenges like information overload and potential reputation risks.