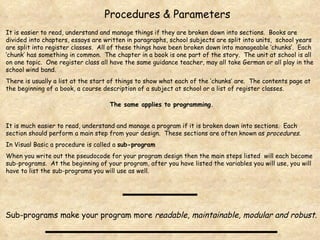
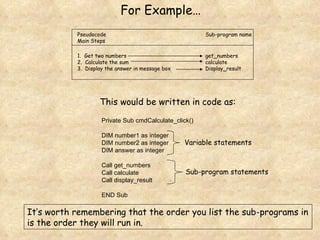
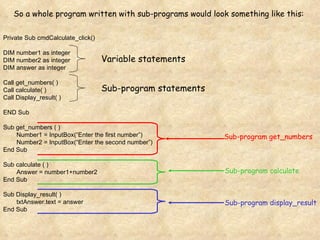
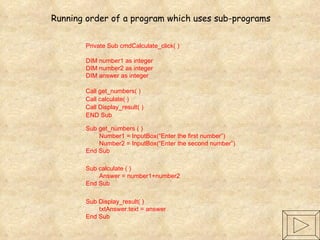
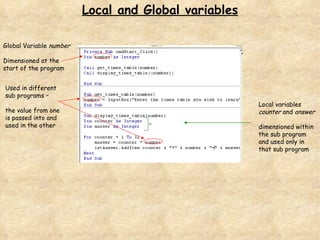
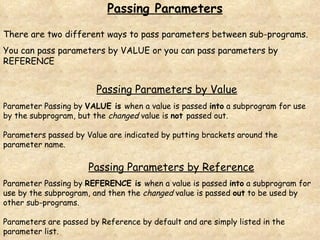
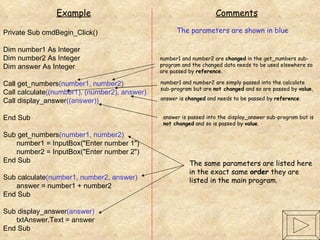
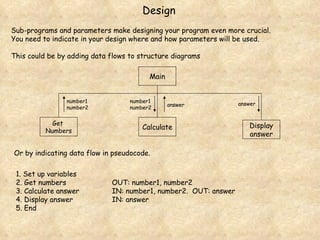
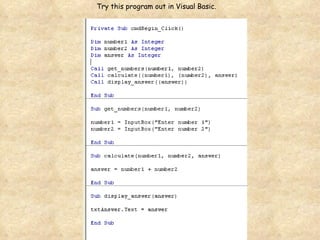
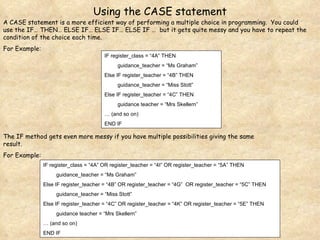
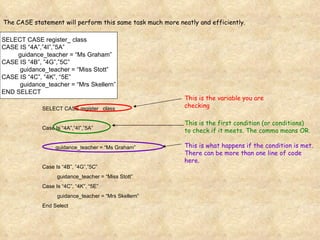
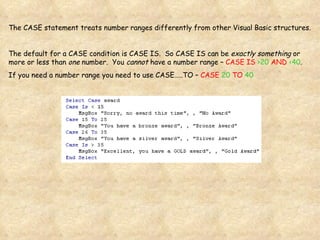
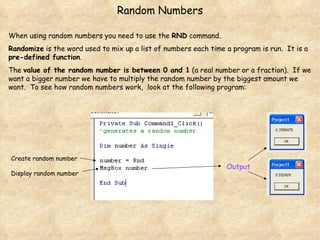
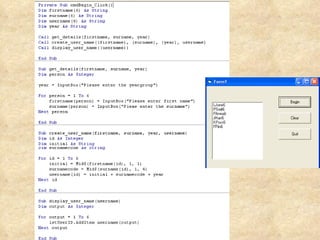
The document discusses how breaking programs down into sections or subprograms makes them easier to read, understand and manage. It provides examples of how to structure a program using subprograms and parameters to pass information between the subprograms. Key aspects covered include declaring global and local variables, using subprograms to perform main steps, and using parameters and CASE statements to control program flow and data passing between subprograms.