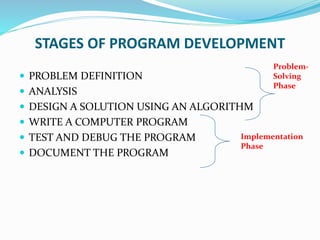
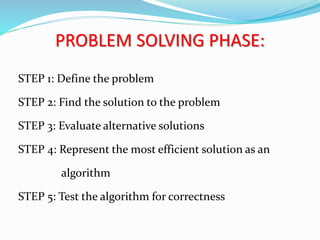
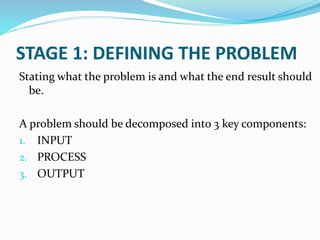
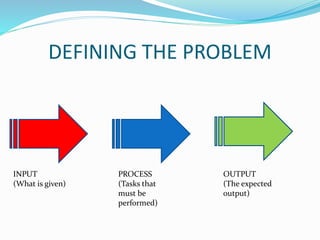
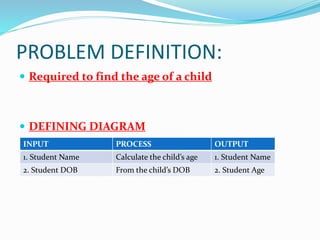
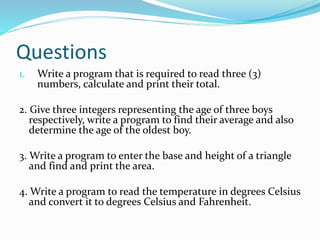
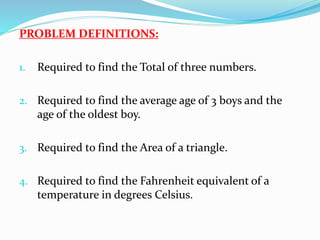
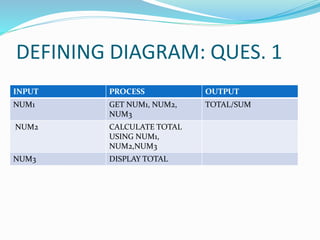
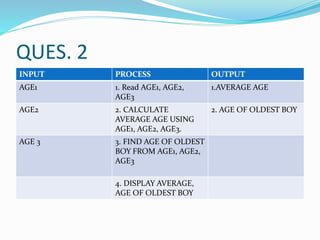
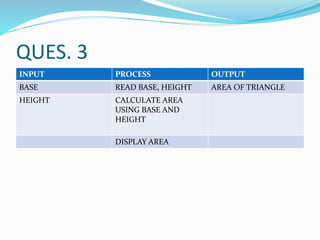
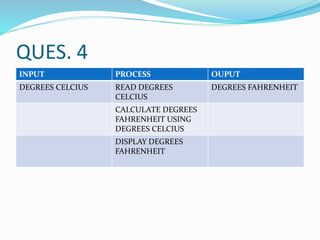
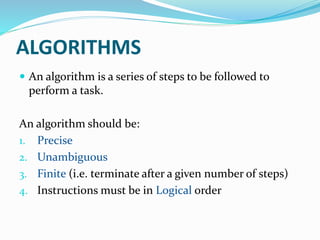
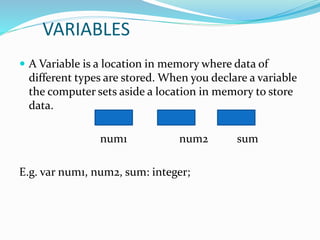
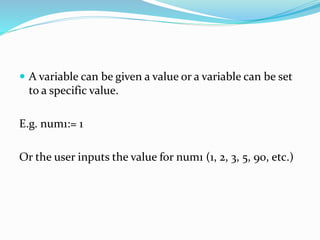
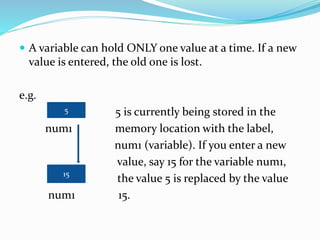
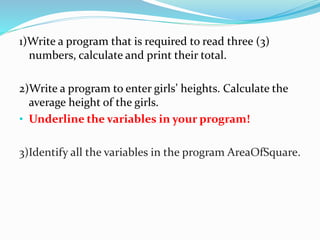
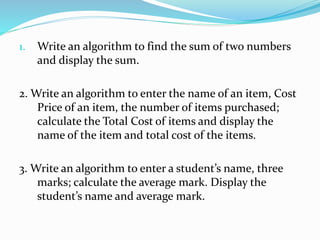
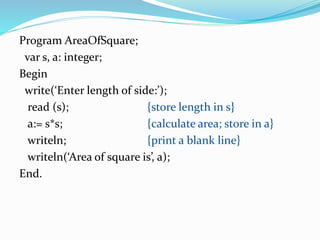
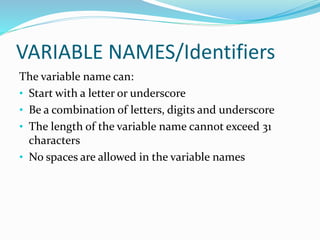
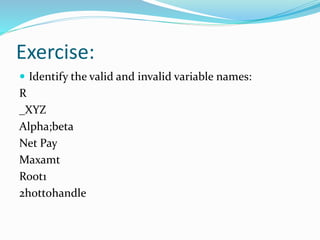
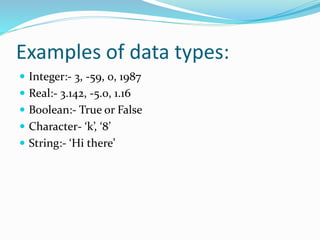
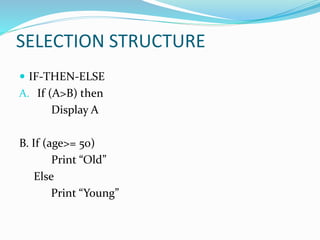
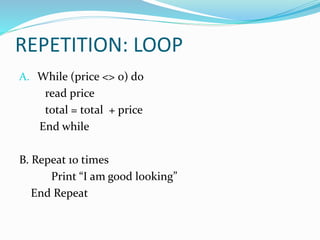
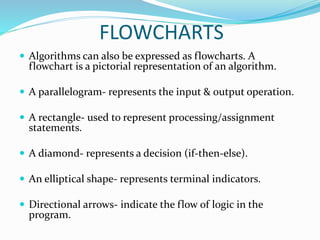
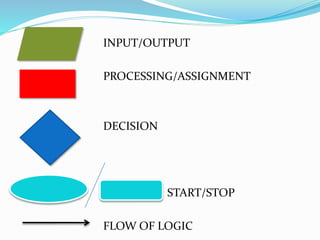
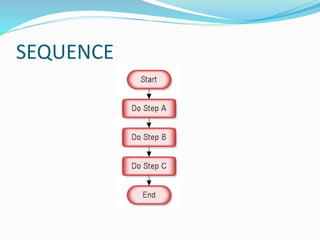
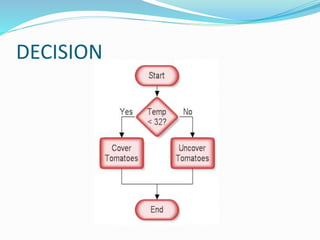
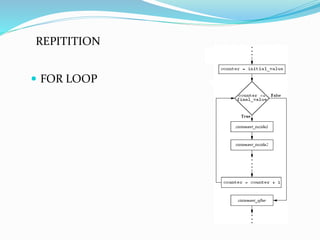
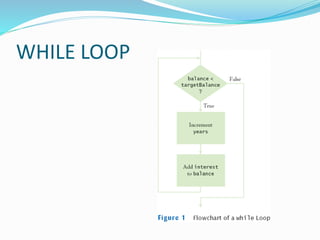
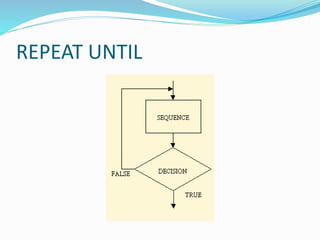
The document outlines the stages of program development, which include problem definition, analysis, design, implementation, testing, and documentation. It emphasizes the importance of defining problems through inputs, processes, and outputs, and introduces algorithms as precise steps to solve these problems. Additionally, it explains concepts such as variables, data types, control structures, and arrays in programming.

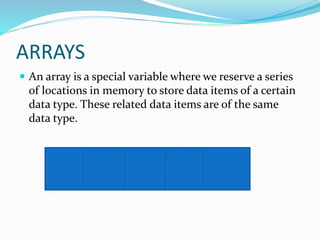
![DECLARING AN ARRAY
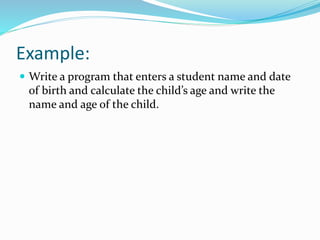
Example:
var MARKS: Array[1..35] of integer;
Reserved
word
Variable
Name
Group of
35 Data type
MARKS is the name of the entire array. In order to access one data item the
subscript is used.
MARKS
1 2 3 4 5](https://image.slidesharecdn.com/problemsolvinganddesign-161101143635/85/Problem-solving-and-design-42-320.jpg)