Embed presentation
Download as PDF, PPTX


























































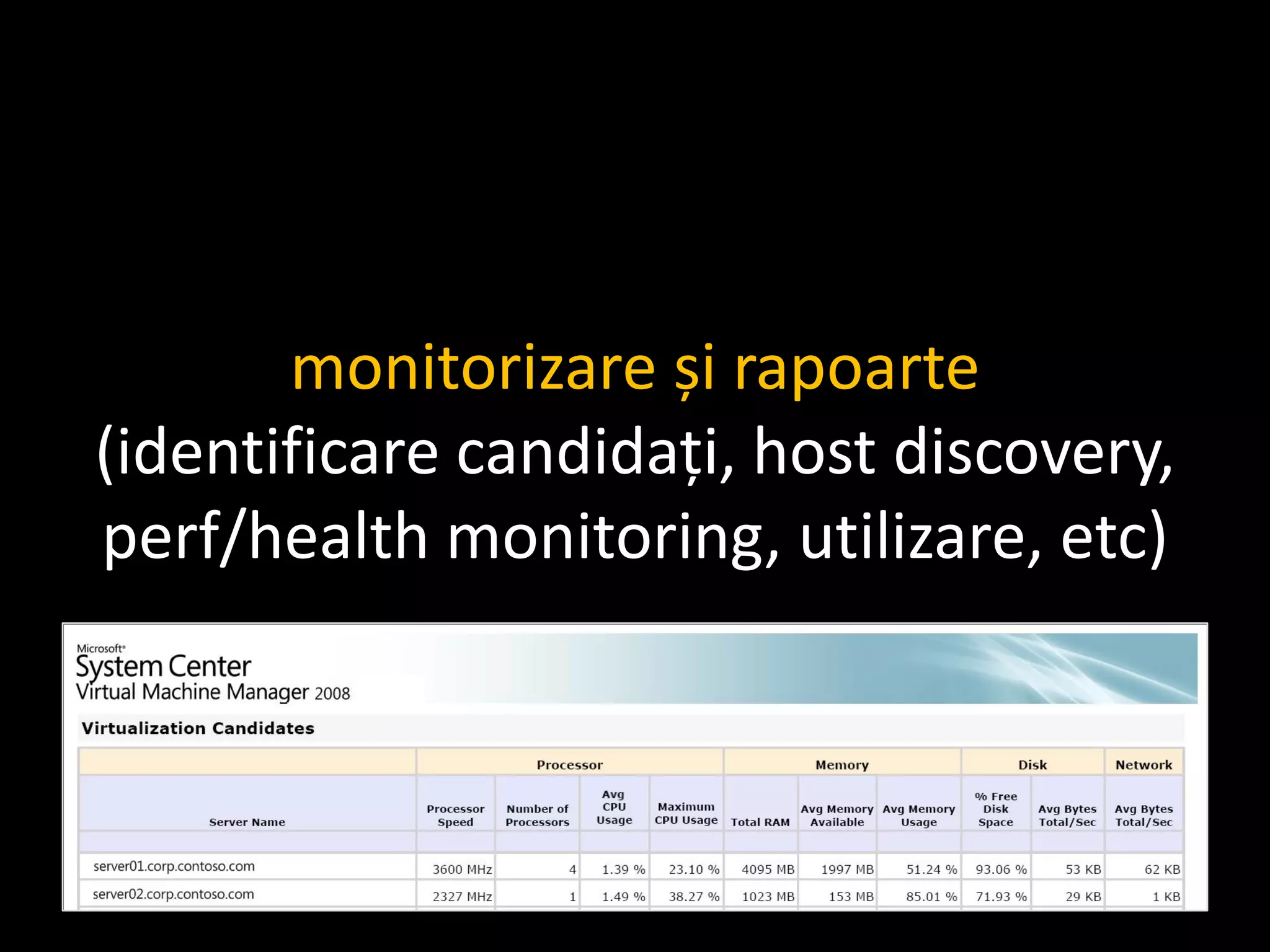
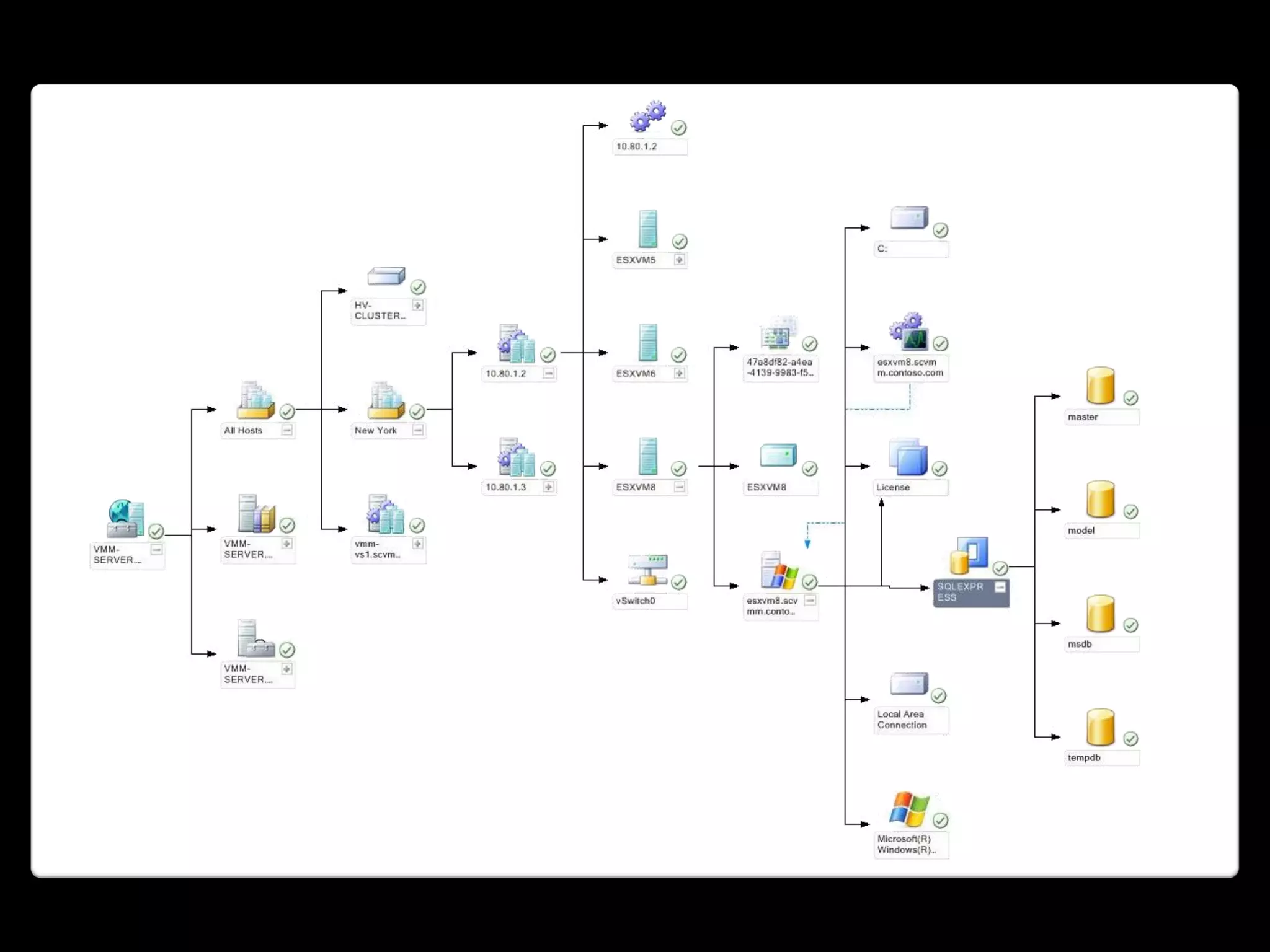

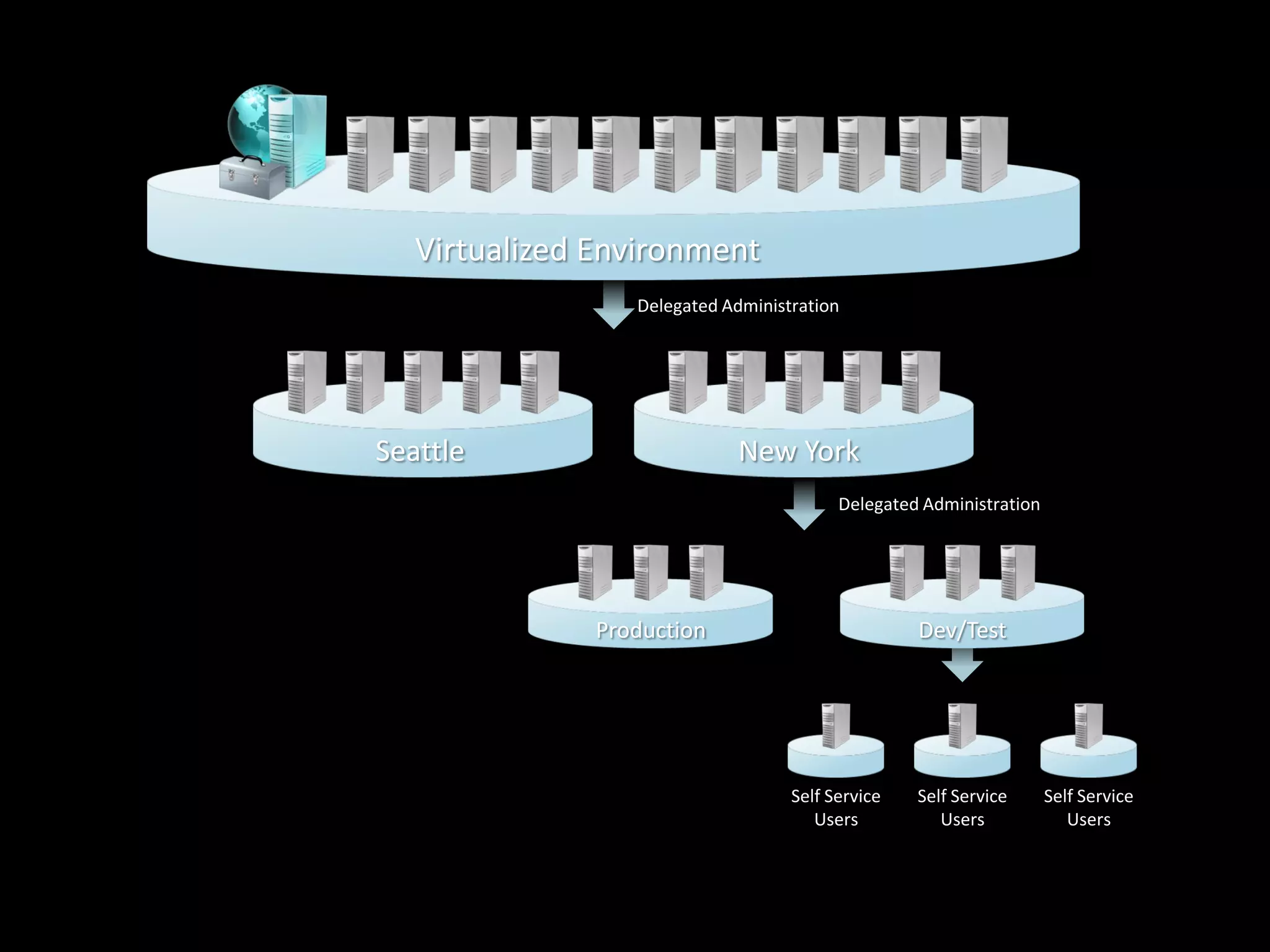








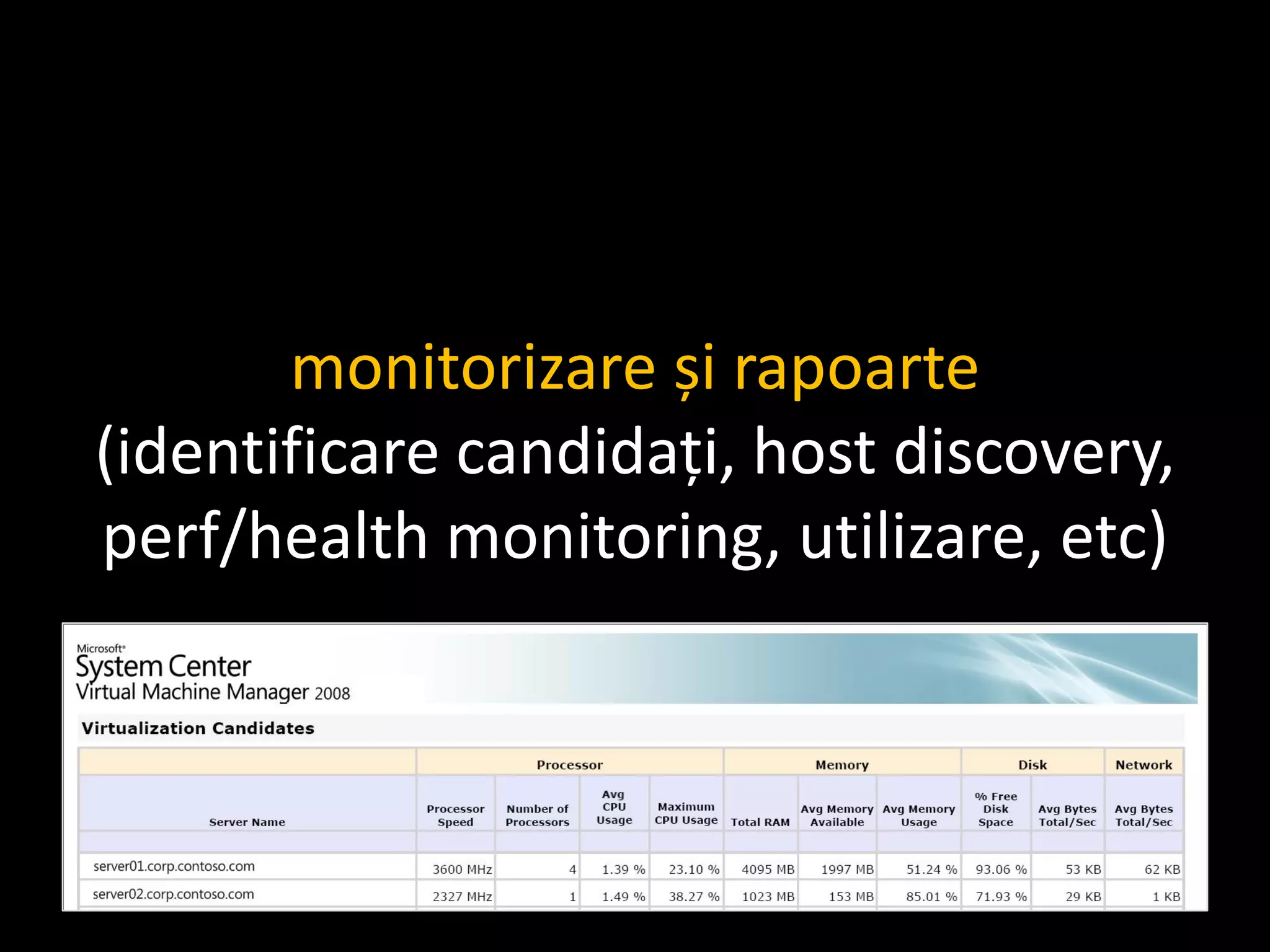
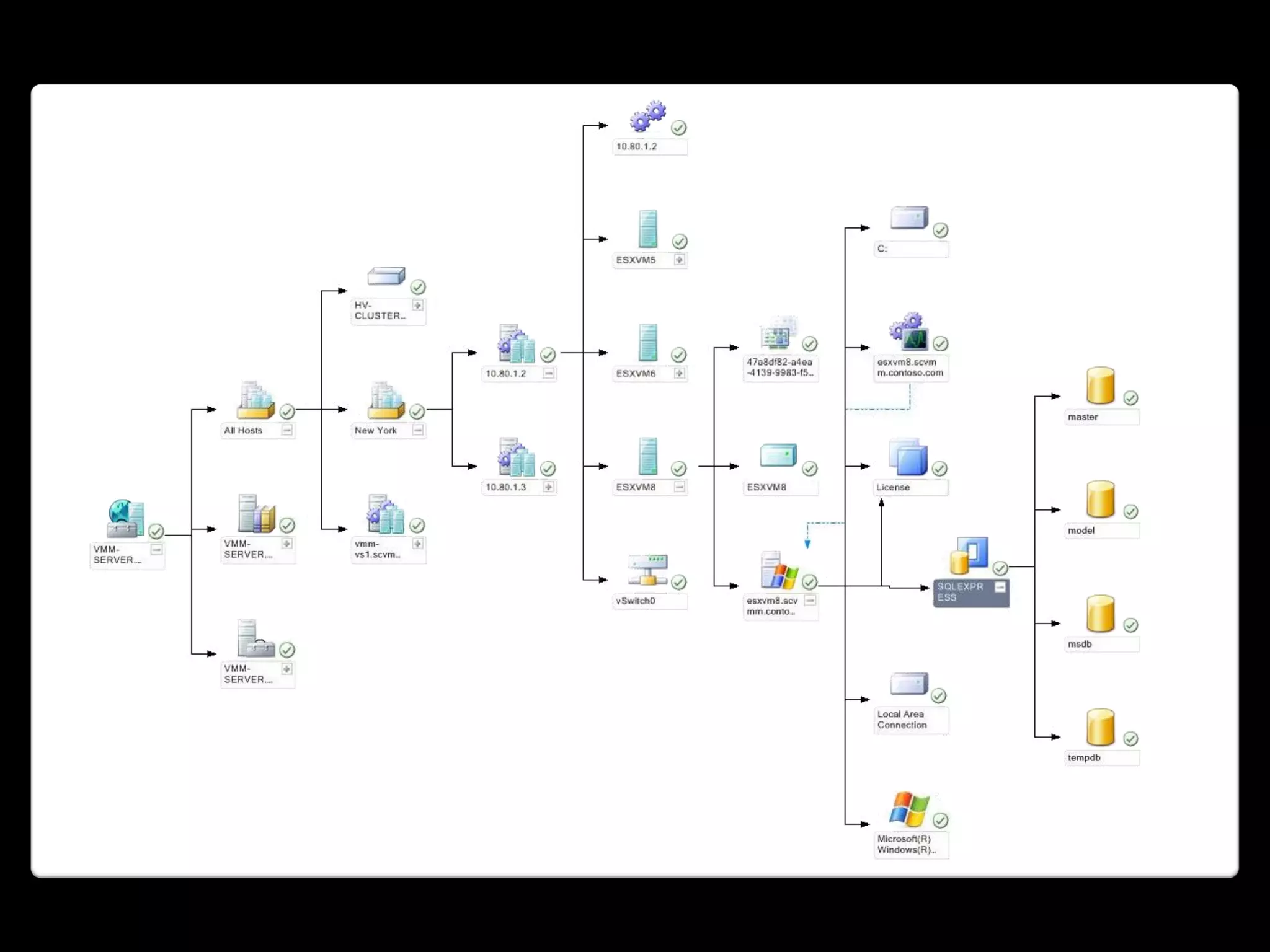
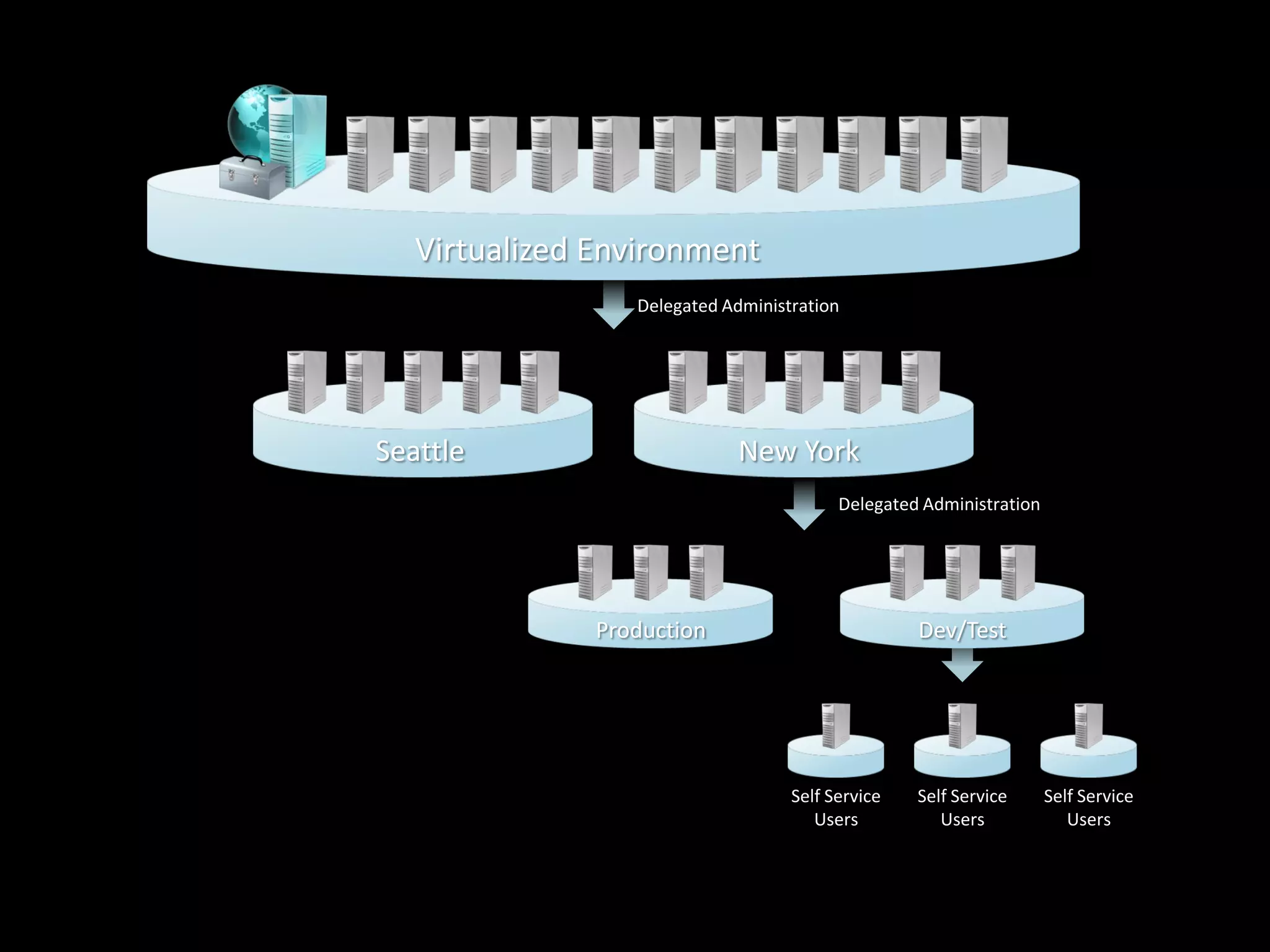
Hyper-V and SCVMM 2008 provide virtualization capabilities for Microsoft. SCVMM 2008 allows for managing virtual machines across VMware and Hyper-V environments. It provides features like intelligent placement of VMs, conversion of physical to virtual machines, and delegated administration. SCVMM 2008 integrates with other System Center products and uses PowerShell for administration and monitoring of the virtualized environment.