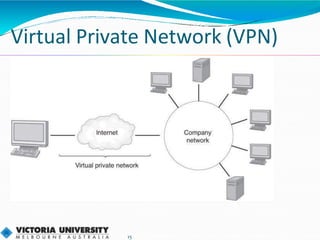
Virtualisation uses hardware and software to create virtual versions of servers, desktops, networks, storage and memory. This allows one physical server to appear as many servers, or one desktop to run multiple operating systems simultaneously. Server virtualisation improves resource utilisation and reduces costs. Popular virtualisation platforms include VMware ESXi and Microsoft Hyper-V. While virtualisation offers advantages like increased flexibility and scalability, it requires new skills and adds some overhead.