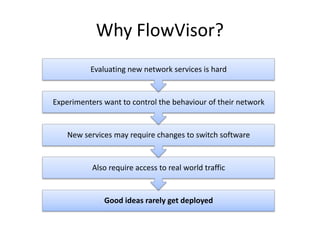
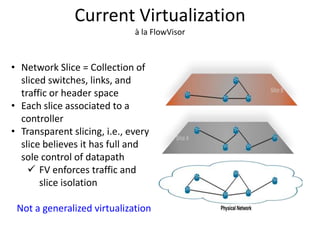
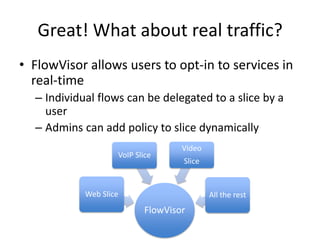
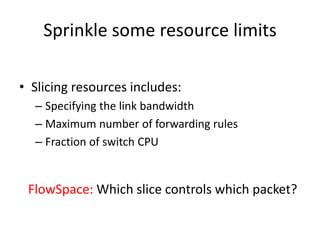
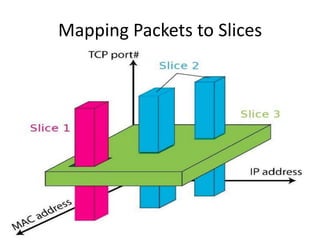
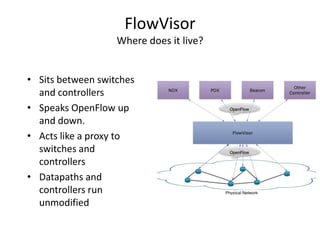
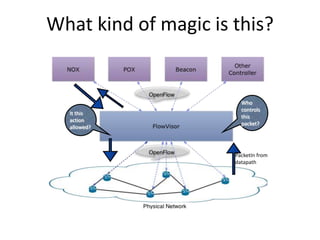
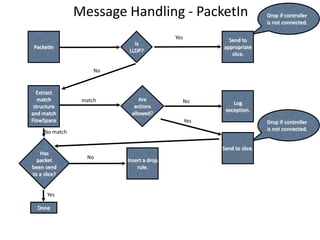
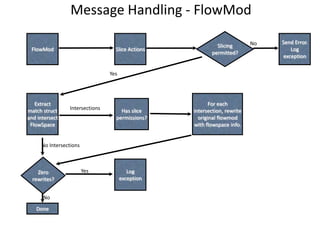
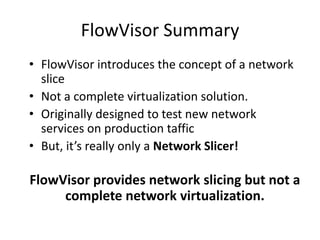
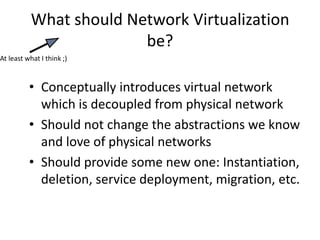
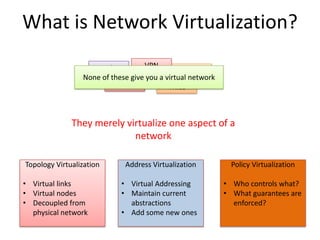
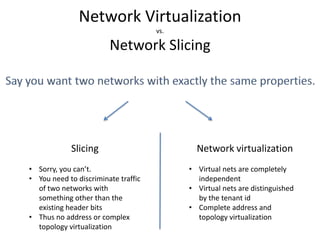
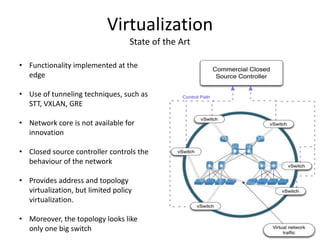
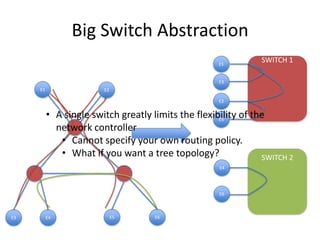
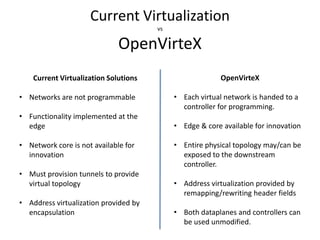
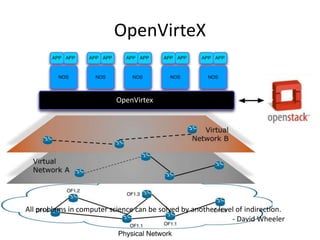
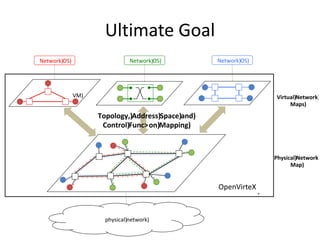
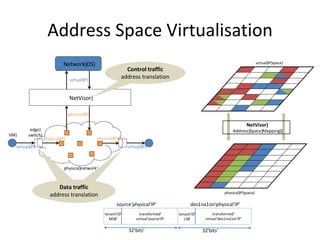
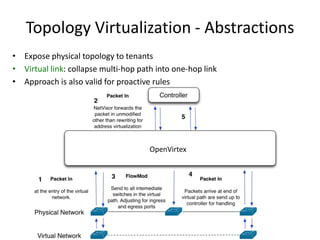
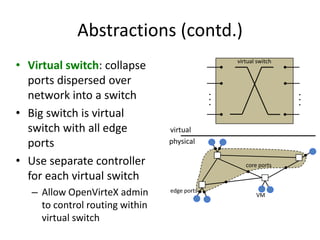
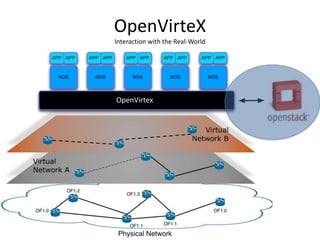
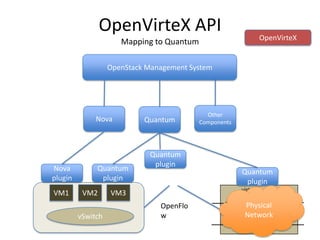
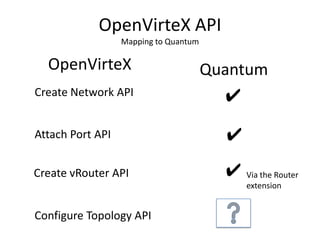
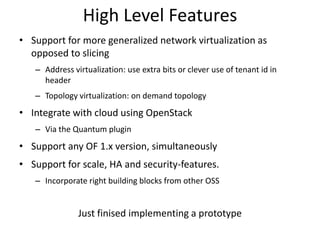
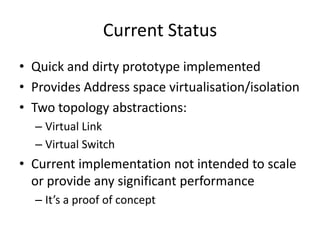
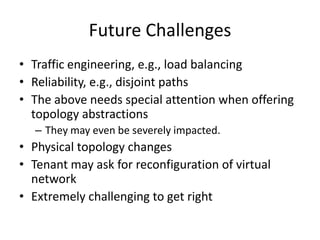
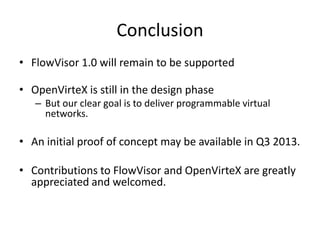
This document introduces programmable virtual networks and discusses their advantages over traditional network slicing. It describes FlowVisor, an early network slicing tool, and its limitations in providing full network virtualization. The document then introduces OpenVirteX, a new system that aims to provide complete programmable virtual networks through topology, address, and policy virtualization. OpenVirteX maps virtual and physical network elements and allows independent control of virtual networks. While still in development, OpenVirteX has the potential to enable more flexible and innovative virtualized networks than previous solutions.